Join Tech Prescient at ET CISO IDAM Summit 2026 | 8 May, Mumbai.
The Next Gen AI-DrivenIdentity Security and Governance Platform
See every identity. Control every permission. Automate governance. All from one intelligent platform.

Trusted By
If You Can’t
See, You Can’t Control
Hidden access
quietly increases risk
Unmanaged NHIs create
blind spots in governance

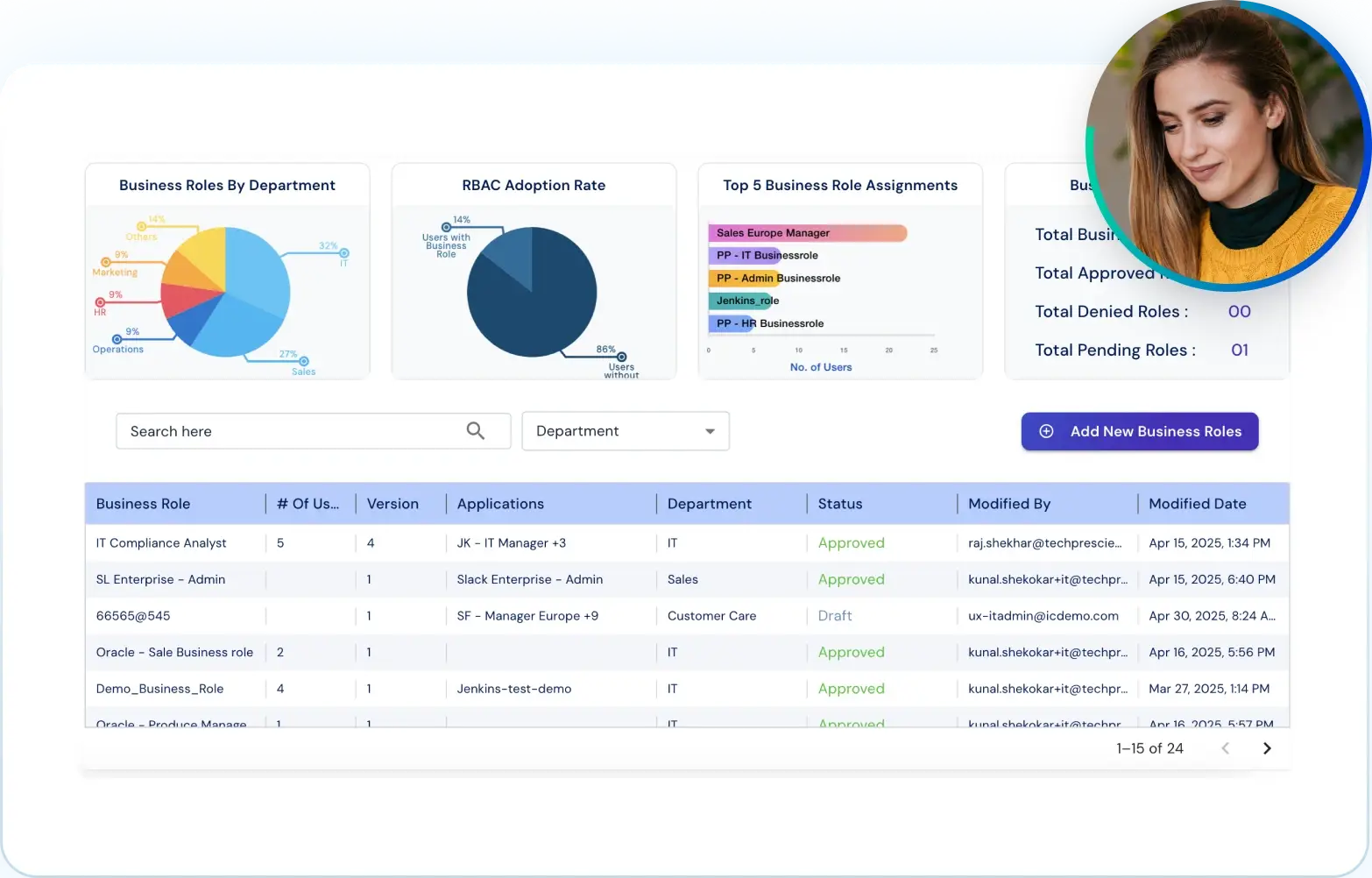
Everything You Need. To Govern Every Identity.
Make access reviews faster and easier
Use AI-driven risk scoring & contextual recommendations to simplify access reviews and accelerate decision-making.
Learn More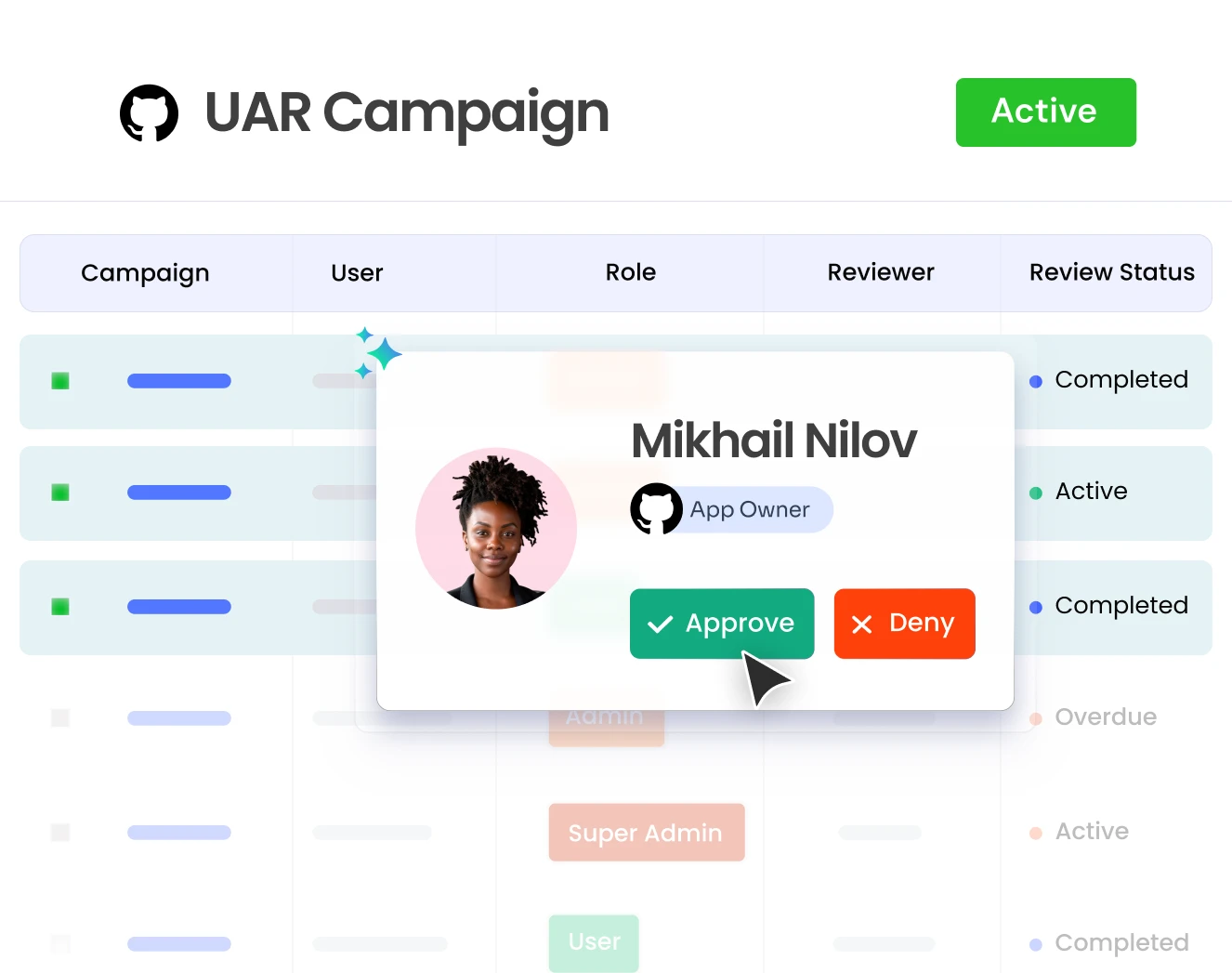
Keep Access In Sync As Roles Change
Automate joiner, mover and leaver processes with policy-based workflows to ensure timely and accurate access changes
Learn More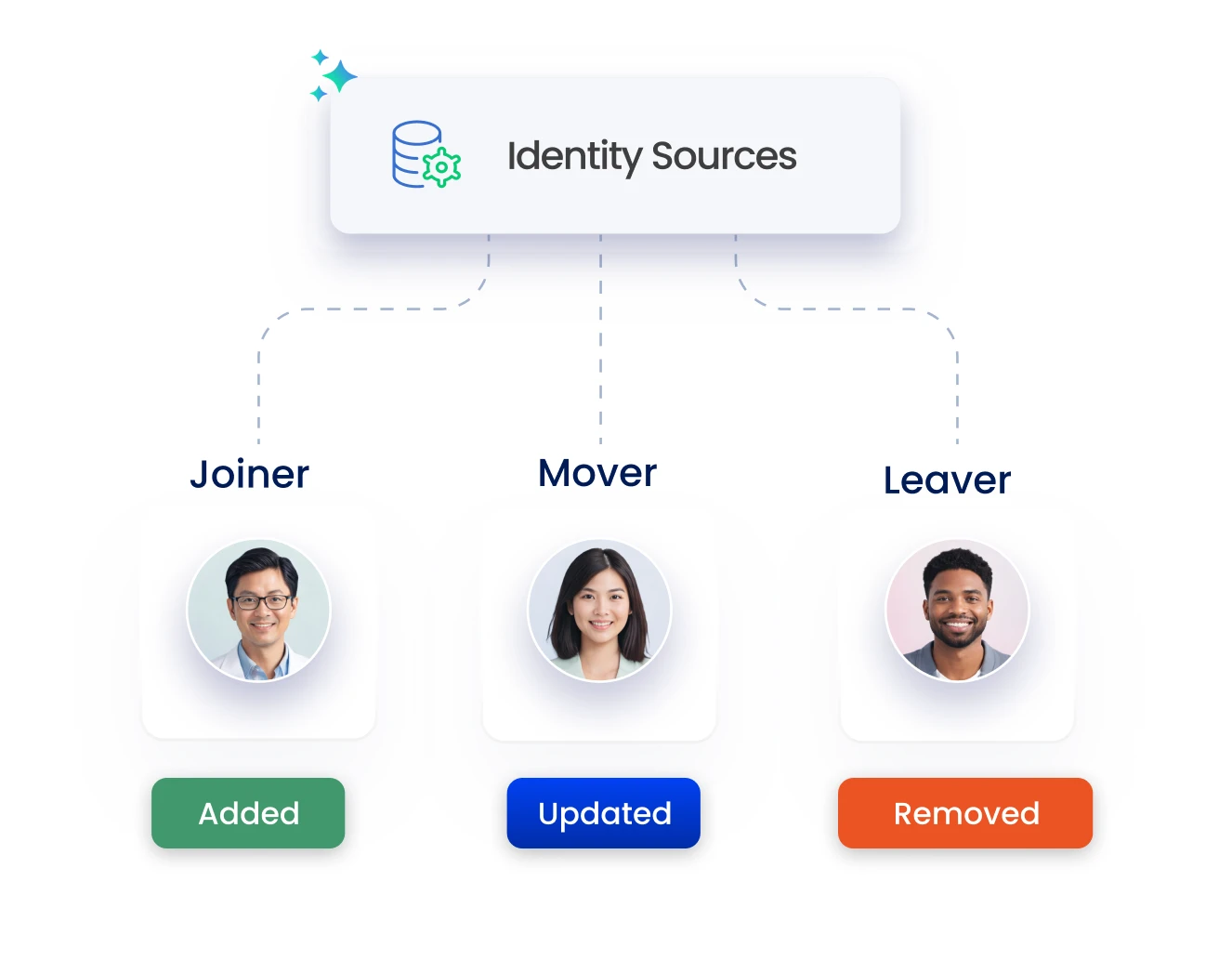
Track and manage non-human access easily
Discover, classify, and assign ownership to non-human identities for better visibility and control.
Learn More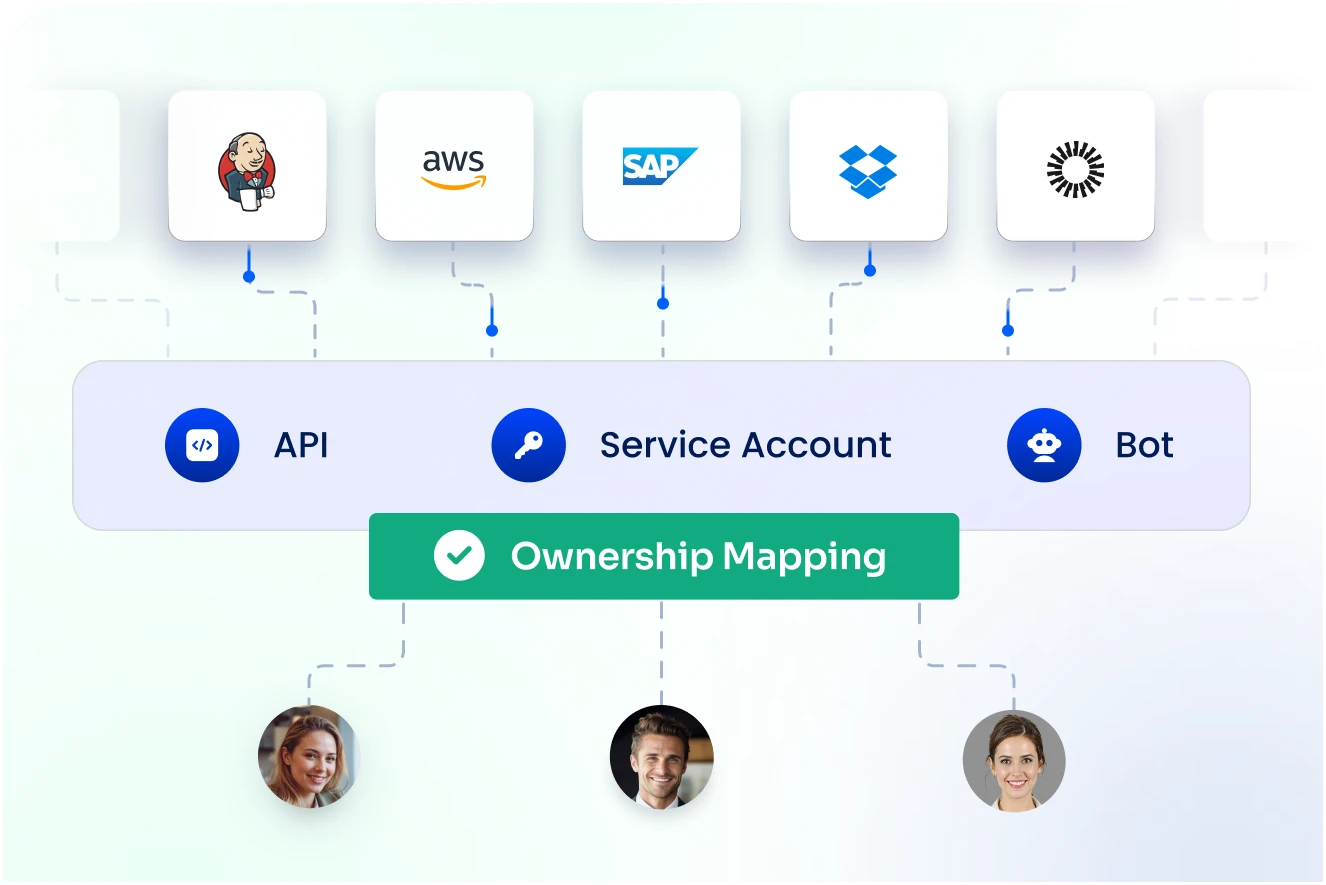
See where your identity risks really are
Continuously assess identity risks across users, roles, entitlements, and non-human identities.
Learn MoreDetect and act on threats in real time
Get actionable insights and prioritized alerts to respond to identity threats in real time.
Learn More
Bring AI into every identity decision
Use AI to detect risks, guide access decisions, automate reviews, streamline workflows, and manage AI agents with continuous visibility.
Learn More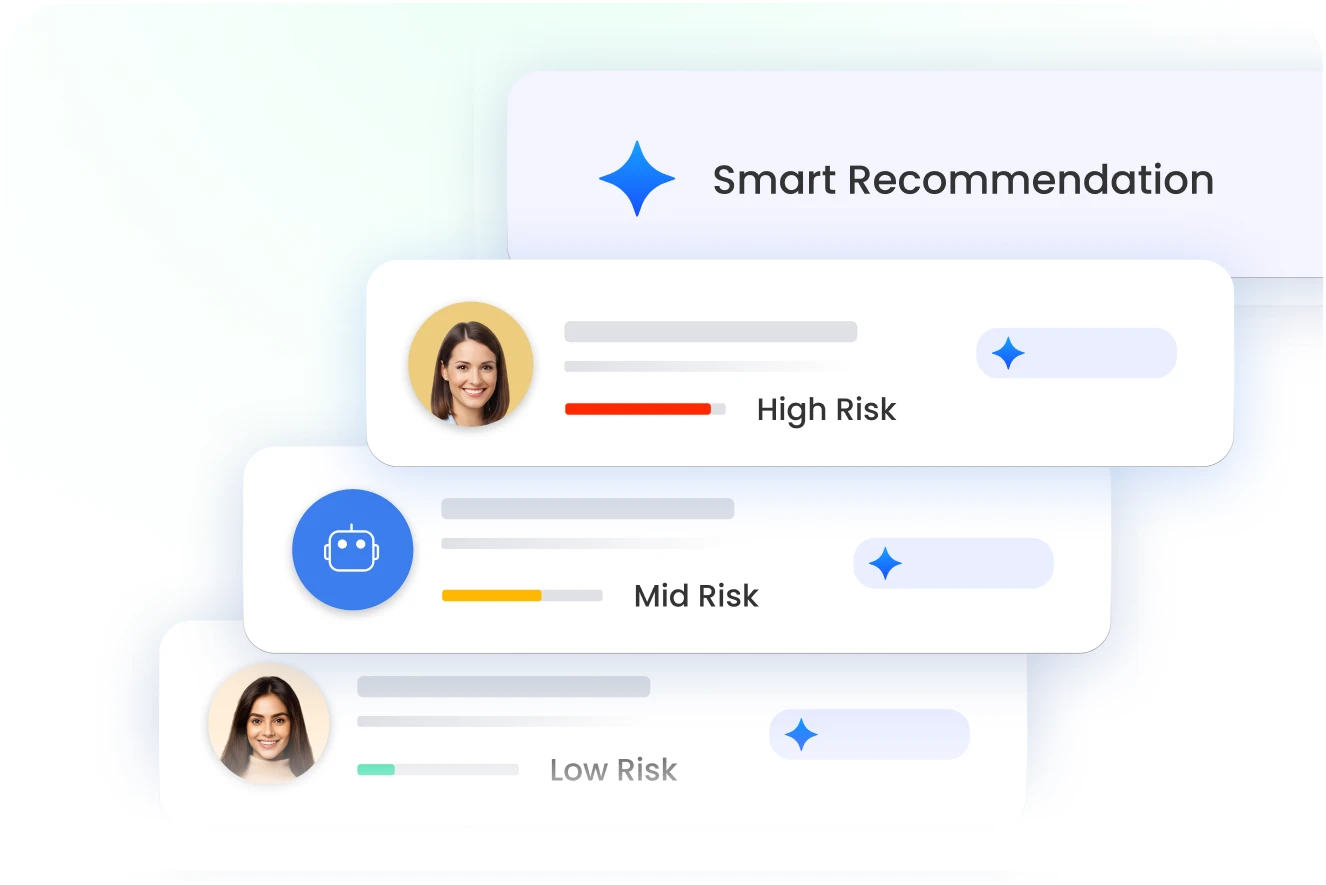
Workflows that run processes for you
Design drag-and-drop workflows to handle access changes, approvals, and identity events without manual steps.
Learn More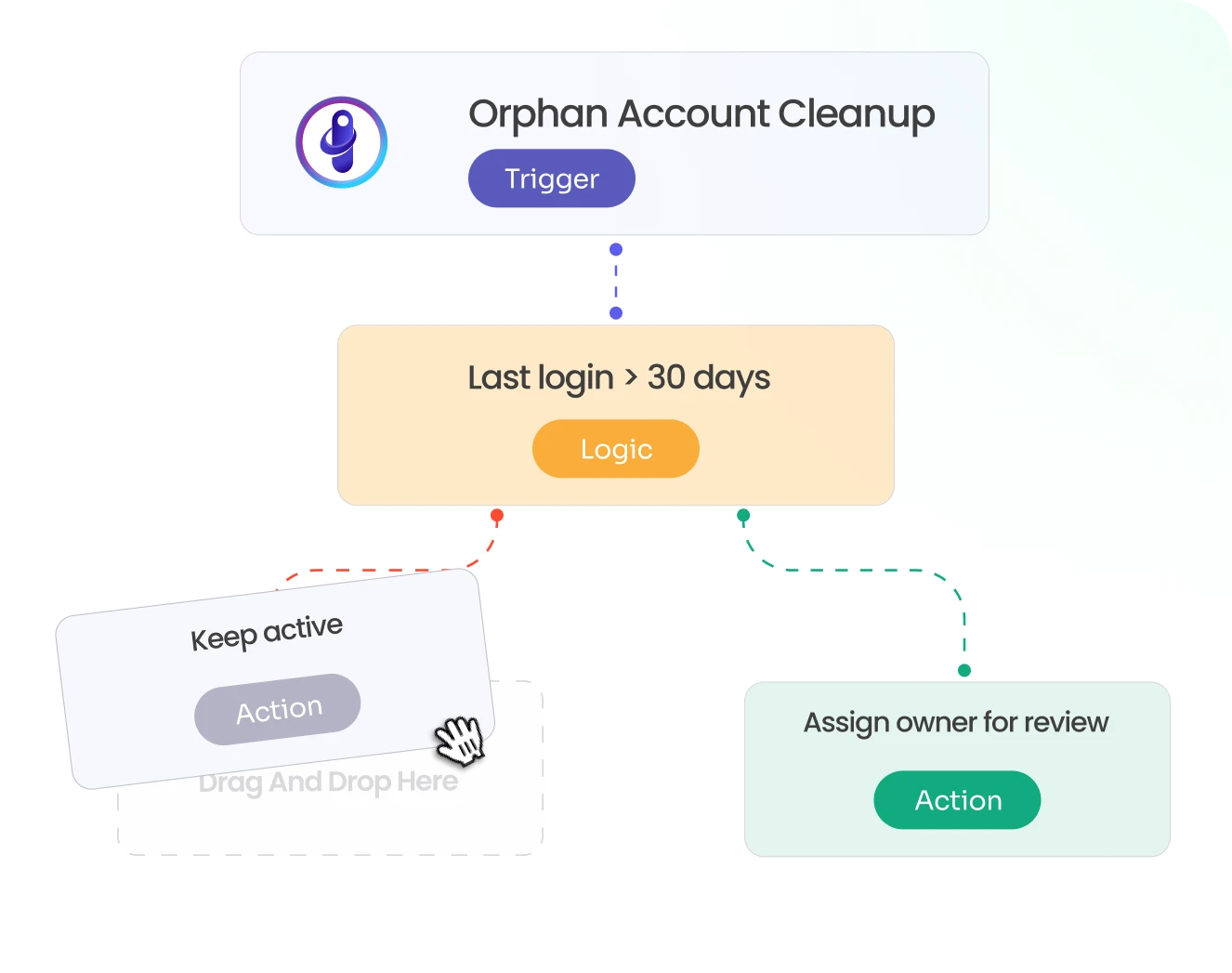
Always Audit-Ready with Evidence Center
One place for all audit and compliance evidence
Prebuilt reports mapped to requirements
Create Custom reports and export in one-click




GET A PERSONALIZED DEMO
Schedule a call with our experts
Drive measurable value with Identity Confluence
Calculate Your ROI
85%
reduction
in manual identity tasks
90%
automated access
lifecycle workflows
3-5x
ROI
in first 12 months

250+ Integrations to all systems
See all app integrations