
What is User Lifecycle Management (ULM)? Process, Tools, and Best Practices (2026 Guide)

Annually, companies lose millions to breaches stemming from something shockingly avoidable - idle or over-privileged accounts. Whether it is an ex-employee who has not had their access revoked or a contractor still retaining admin rights, these mistakes in managing user accounts can allow attackers to take advantage of them.
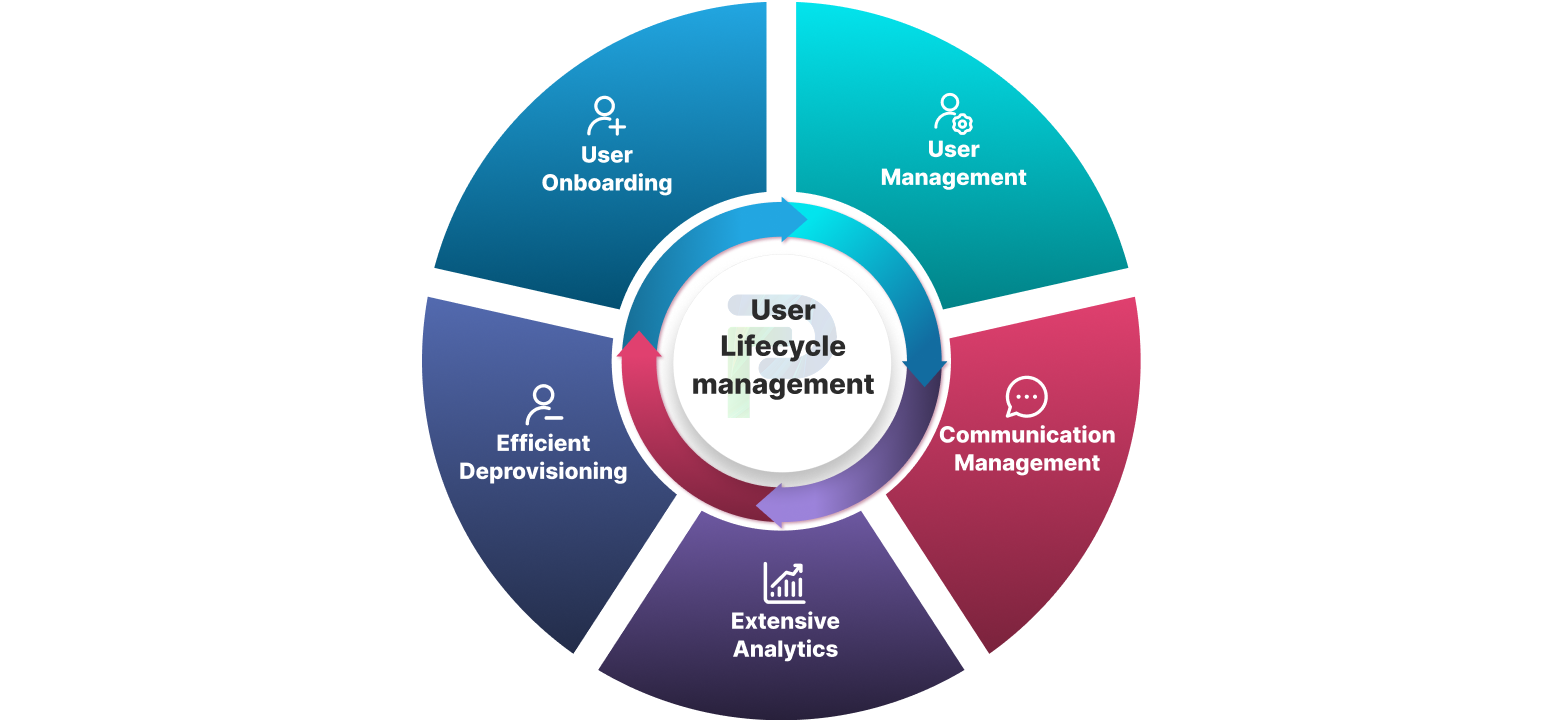
User Lifecycle Management (ULM) closes the gaps. ULM incorporates everything associated with the life of a user in your organization’s IT ecosystem — from their onboarding until their access is revoked. It covers an individual’s digital identity, access rights, and permissions as long as a user is active, providing the right amount of access, reducing security risk, and aiding in compliance. When handled fully, ULM can reduce the potential for insider threat and non-compliance, whilst also enabling the orchestration of IT processes, improving onboarding, and improving the overall state of audit readiness for organizations.
We’ve helped enterprises in finance, healthcare, and technology build a fully layered ULM practice that eliminates orphaned accounts, enforces least privileges, and achieves continuous compliance while still performing business.
In this blog, we will break down what ULM is, how it works, and how you can make it work for your organization.
Key Takeaways
- Universal Lifecycle Management is essential for risk reduction. It ensures that only the right people have the right access at the right time, and access is revoked immediately when it is no longer needed.
- A strong ULM prevents common security gaps like orphaned accounts, privilege creep, and inconsistent access policies.
- When ULM tools are integrated with IT and HR workflows, they eliminate unnecessary errors, delays, and manual overhead.
- Compliance is simplified with ULM tools, as they provide continuous monitoring and audit trails, as well as the structure and enforcement of policies.
- Future-ready ULM leverages AI to enhance predictive provisioning, role mapping, and non-human identity management across hybrid environments.
What is User Lifecycle Management?
User lifecycle management (ULM) is the formal practice of establishing, maintaining, and ultimately retiring a user’s digital identity and access privileges throughout their entire relationship with an organization. The user lifecycle starts the moment a user is onboarded starting with the provision of accounts, assignment of derivative permissions based on role or function, and continues throughout every access change or requirement, from promotions to departmental moves to project-based need, to when they are securely offboarded, in immediate fashion, ensuring there is no remaining access to cause potential harm.
In contrast with ad-hoc account administration, ULM guides a structured, consistent, policy-based control around who has access, what they can access, and when that access should end to protect an organization's cyber interests and compliance obligations.
Based on our work with ULM implementations in enterprises with over 10,000 employees and contractors, we have learned that the potential difference between a secure cyber environment and a high-risk environment lies in how well the user lifecycle is governed. Organizations without a defined ULM framework are susceptible to privilege creep, orphaned accounts, and compliance gaps that bad actors will take advantage of or may get flagged during audits.
Why User & Account Lifecycle Management Matters for Security and Compliance
The modern business no longer just has a secure office network to operate on. Hybrid and remote workforces have users logging in from home devices all over the world at all hours. Additionally, cloud adoption is bursting at the seams with business-critical data and applications spread amongst SaaS platforms, IaaS environments, and on-premises environments.
This change has exponentially enlarged the attack surface. Every user account, be it employee, contractor, or even third-party vendor, is now a potential entry point. And inconsistent or manual access processes have opened up perilous gaps, such as:
- Orphaned accounts that remain active after a user has left
- Privilege creep (users maintaining old permissions as their jobs change)
- Accounts that are spread out across various disconnected systems make centralized control almost impossible
Attackers know these weaknesses deeply. Unrevoked accounts of former employees or vendors make an easy backdoor into sensitive systems, and in cloud environments, may have a large blast radius impacting customer data, intellectual property, and regulatory standing.
The stakes are also high from a compliance perspective. Major regulations, including ISO 27001, SOC 2, HIPAA, and GDPR, all require organizations to demonstrate who had access to what, when, and why that access occurred. Without automated User Lifecycle Management in a hybrid/cloud environment, compiling the necessary audit trail is not only labor-intensive but potentially very expensive if lapses occur.
We have seen this play out in several industries:
- Finance: A remote contractor (cloud credentials remaining active for several months) had access to sensitive transaction records.
- Healthcare: A cloud-based electronic health record (EHR) system with over-privileged accounts resulted in unauthorized access to patient records, representing a HIPAA violation.
- Technology: Fragmented identity systems created delays in onboarding that pushed critical project milestones into the red.
User Lifecycle Management closes the gaps by provisioning access immediately, maintaining statuses as roles change, and revoking access as soon as it is not needed, while maintaining a consistent, auditable record to satisfy regulators and reduce risk from a cyber threat perspective.
User Lifecycle Management Process Flow (ULM Step-by-Step)
An effective ULM strategy has a repeatable, automated process that controls access from the point of hire (or engagement) until offboarding, with oversight all along the way.
Step 1- Onboarding & Provisioning
The process begins with integrating a new user into the organization’s systems and workflows. This includes setting up accounts, granting appropriate access permissions, and providing necessary resources so they can start working productively on day one. Provisioning ensures that users only receive access aligned with their role and responsibilities, reducing the risk of overexposure. For example, when a cloud engineer joins, ULM automatically creates their Azure AD account, grants GitHub repo access, provisions AWS IAM roles, and delivers all necessary tools without requiring IT intervention.
Step 2- Modification and Updates
As users move between teams, projects, or roles, their access must be adjusted accordingly. This involves granting new permissions when needed and revoking outdated ones to prevent privilege creep—where users accumulate more access than required over time. For instance, when a sales lead transitions to the marketing department, ULM instantly removes CRM admin rights and assigns access to marketing automation tools, triggered directly by HR system updates.
Step 3- Usage Monitoring & Governance
Throughout the user’s journey, ULM continuously monitors account activity, login behavior, and access requests to identify anomalies and potential risks. By tracking logins, unused accounts, and permissions outside policy, the system helps maintain compliance and detect insider threats early. A common case would be flagging a developer’s login from an unrecognized country and temporarily suspending access until verified, ensuring threats are stopped before escalation.
Step 4- Offboarding & Deprovisioning
When a user exits the organization, ULM enforces a secure and immediate deactivation of all accounts. This step revokes credentials, removes access to cloud and on-prem systems, and eliminates the risk of orphaned accounts—a leading cause of data breaches. For example, when a contractor completes their project, ULM automatically disables Microsoft 365, Jira, AWS, and VPN access within seconds of HR marking their departure.
Benefits of User Lifecycle Management
User Lifecycle Management is much more than an account manager; if done right, it provides tangible security, compliance, and operational benefits that the business can take advantage of. The benefits of effective ULM include the following:
1. Enhanced Security
ULM reduces the risk of insider threats and abuse of privilege by providing users only the access they need, and when no longer needed, removing it immediately. ULM can also reduce external threats that take advantage of orphaned accounts. With continuous monitoring, ULM can identify anomalies much earlier than ad-hoc reviews, which can greatly improve the overall security posture of the organization.
2. Regulatory Compliance
Whether it is an iso or industry standard, regulations such as HIPAA, SOC 2, ISO 27001, and GDPR require strict access controls and valid audit readiness at all times. ULM enforces policy compliance, provides detailed audit logs, and allows for quick revocation of access. These steps not only make it easier to achieve compliance, but they also ease the burden of managing compliance in audits.
3. Operational Efficiency
Manual provisioning and deprovisioning waste IT Resources and slow productivity. Automating the provisioning and deprovisioning provides users the right access from the day they start and prevents unnecessary delays in role changes or offboarding. More importantly, it allows IT and Security teams to focus their time on more strategic or value-add tasks compared to legacy repetitive and mundane tasks of providing access.
4. Enhanced User Experience
When employees, contractors, and partners have the right tools at the right time, they can begin contributing more quickly. ULM eliminates the frustration of waiting for access requests to be fulfilled and allows for a smooth transition during a role change with no security compromises.
5. Cost Savings
Idle or unused accounts are not just security risks, but they also incur needless licensing and infrastructure expenses. ULM identifies and removes idle or unused accounts continuously, ensuring that organizations optimize their resources and reduce ancillary costs.
Key Challenges in Managing the User Lifecycle
Even with modern IAM tools, many organizations continue to face challenges in securely and effectively managing identities. In our audits of many firms, we found that many enterprises lack a process to identify or disable orphaned accounts, showcasing a glaring compliance and security deficiency. These deficiencies not only create challenges for audits but also result in opportunities for insiders and ransomware attacks, or other forms of data exfiltration.
Following are the major challenges organizations face:
1. Privilege Creep
Privilege creep takes place when a user gradually accumulates more privileges than their current role requires because access is granted for new projects and then typically not removed. Over time, these excessive privileges exponentially increase the risks associated with a compromised account. And now, with hybrid and cloud environments, users engage with multiple systems daily, all with different access policies, and privilege creep is exacerbated.
Example: A marketing manager takes the time to help finance with a project and is granted access to the payroll application. Months later, when they return to marketing, they still retain their payroll access, putting the sensitive employee data at unnecessary risk.
2. Orphaned Accounts:
An orphaned account is a user account that remains active without its user. Orphan accounts are especially urgent in cloud and SaaS, as they are easily lost during the offboarding process. Attackers rely on orphan accounts because they receive no visibility and bypass usual onboarding security controls.
Example: A former developer's GitHub account remains active for months after leaving the organization, allowing code changes to go undetected and without plate approval.
3. Fragmented Systems:
At many enterprises, identity-related data exists in multiple unsynchronized systems such as Active Directory, cloud IAMs, SaaS admin consoles, and legacy on-prem applications. Without a single source of truth, provisioning and de-provisioning are slow, painful, and incomplete. Compliance teams have trouble putting together timely and accurate access reports.
Example: When a contractor leaves the organization, their access needs to be removed from five separate admin dashboards. Unless IT thoroughly vetted all five, they could have unknowingly left the door open for months.
4. Manual processes:
Users manually managed in spreadsheets, email approvals, and ticket-based provisioning have their risks and are very time-consuming. Steps can easily be missed or delayed, especially when managing role changes in bulk or urgent terminations. Every delay increases the exposure to possible security breaches. Example: A vendor finishes their engagement on Friday, but their VPN access isn’t removed until the following week because the IT team is waiting for approval through the manual process.
Compliance in the ULM Journey
In regulated industries, User Lifecycle Management isn’t just a best practice; it’s a requirement for compliance. If you're compliant with things like HIPAA in health care, SOC 2 in SaaS, ISO 27001 for information security, or GDPR for data privacy, regulators expect you to know who has access to what, why, and how long. A strong ULM strategy cannot only secure your environment, but it also puts you in the position of documenting every step of the user's journey in a way that is auditable and compliant with your governance policies.
1. Keeping Detailed Audit Trails
There should be logs and timestamps for any activity in the user lifecycle from onboarding to role changes to final deprovisioning. Audit trails will demonstrate to auditors that you followed policies, which is important for compliance, during audits or investigations. An audit trail can also provide aid to security officers conducting forensic analysis. For example, in a SOC 2 audit, an auditor may ask for proof of who accessed the production database in the past 90 days. ULM creates a full report in minutes, showing user identities, timestamps, and approvals related to the access request.
2. Enforcing Role-based Access Control
Oftentimes, regulatory frameworks require users to have the minimum access necessary for employees to perform their job functions. Role-Based Access Control (RBAC) ensures permissions are assigned to job roles, rather than individuals, limiting privilege creep and over-provisioning. In combination with periodic reviews, RBAC helps with maintaining continuous compliance. In reporting requirements, for example, a GDPR audit, user access is not tied to individual employees, but only the customer support role has read access to customer PII. Any deviation from that baseline would generate an automatic alert for review.
3. Ensuring Quick Revocation Upon Employee Exit
Most compliance issues are a result of insufficient or incomplete offboarding. Most frameworks, such as HIPAA and ISO 27001, state that access must be instantly removed for terminated users. User lifecycle management will automate your deprovisioning so no account is live beyond the employee's last working moment. For example, a hospital that is HIPAA-regulated can prove that a nurse who resigned on March 15 had their access revoked to the EHR on the same day. ULM logs show that the revocation took place within 30 seconds of the HR record being updated.
4. Meeting Standards like HIPAA, SOC2, ISO 27001, GDPR
Each compliance framework has its own access control requirements. User Lifecycle Management offers the ability to create a single operational model to meet all of those compliance requirements. The same operational model, which is built on automated provisioning, role-based access, continuous monitoring, and instant deprovisioning, can be applied consistently across multiple compliance standards. This lowers the audit fatigue and no longer requires separate workflows for each oversight body. For example, a fintech company that is required to comply with both SOC 2, ISO 27001 is leveraging ULM to automatically map its access policies to both frameworks, reducing audit readiness preparation by 50%.
Best Practices for Effective User Lifecycle Management
Successful implementation of User Life Cycle Management goes beyond just having the right tools; it involves consistent, disciplined best practices that reduce security risk and make operations more efficient. In our experience, the most mature organizations centralize identity control, enforce strict access principles, automate repetitive tasks, and monitor continuously with the help of intelligent analytics. These practices not only reduce the likelihood of breaches but also ensure compliance is baked into every stage of the user journey.
Here are some best practices you can follow:
1. Centralize Identity and Access
With a fragmented identity landscape, you can never confidently know who has access to what. Centralizing identity and access management into a single IAM or IGA platform allows full visibility across on-premises, cloud, and hybrid environments. The security and compliance teams can see all accounts, permissions, and activity in one environment, therefore creating a complete account view for easier anomaly detection and consistent policy enforcement.
2. Enforce Least Privilege & JIT Access
The principle of least privilege limits what users can do (the permissions they have) to only what they require for their tasks. Now, when you combine least privilege with Just-in-Time (JIT) access, which allows users higher permissions for a short time period, you can greatly decrease the attack surface you are dealing with. When a user no longer needs the access, it expires automatically, and there is no risk that the user is using high-risk permissions after the fact.
3. Automate Provisioning & Deprovisioning
Onboarding or offboarding individuals manually is just too slow and ineffective, and often leads to missing accounts or wrong permissions assignments. Once automated provisioning occurs, there is immediate instant user accounts with correct access, and once automated deprovisioning occurs, entitlements will be removed immediately once the user exits an organization & organization can address security gaps, push users faster toward readiness, and revoke access with zero lag for compliance purposes.
4. Monitor Continuously
Monitoring continuously is necessary to catch privilege creep, unused accounts, and policy violations before they become breaches. Scheduled access reviews at least quarterly provide a way to verify that each user is approved for the access granted.
5. Leverage AI-Driven Governance
Modern user lifecycle management platforms can use machine learning to detect unusual access behavior, predict risky permission assignments, and flag violations before they escalate. By integrating AI-driven governance, security teams can proactively manage access rather than react after an incident, strengthening both security and compliance posture.
Tools & Software for User Lifecycle Management
If you're implementing User Lifecycle Management across your organization, then it stands to reason that the correct tools and software will impact the success of your strategy. Organizations today manage dozens and often hundreds of applications that reside in hybrid and multi-cloud environments, where manual processes will often no longer scale securely. User lifecycle management (ULM) software automates provisioning, deprovisioning, and access governance, giving IT and security teams one identity truth.
Some examples and categories include:
- Identity and Access Management (IAM) Platforms – These are the likes of Okta, Microsoft Entra ID, and Passkey, which bring together authentication, role assignments, and access policies across all applications and systems in the cloud.
- Identity Governance and Administration (IGA) Tools – These are the likes of identity confluence by Tech Prescient, which provide capabilities for governance, compliance reporting, and automated access certification.
- Provisioning Tools with HRIS integrations – If an organization has Workday or SAP SuccessFactors, these tools connect to the HR system to automatically create and remove user access when employment status changes.
- Privileged Access Management (PAM) Solutions – These include tools like CyberArk and BeyondTrust, whose purpose is to control high-risk, elevated accounts by providing capabilities such as Just-In-Time provisioning and session recording.
When assessing tools, consider:
- Integration capability with existing HR, IT Service Management, and cloud environments.
- Scalability to handle identity volumes of today and tomorrow.
- Automation capabilities for provisioning and compliance workflows.
- Security capabilities such as AI-fueled anomaly detection and real-time policy enforcement. The right ULM software stack should fit your current needs and also accommodate workforce changes, compliance obligations, and technology evolution.
The Future of Identity & User Lifecycle Automation
As organizations increasingly expand their digital ecosystems, the next phase of User Lifecycle Management will be defined by intelligent automation, proactive security, and broader identity management, including every identity, human or otherwise. These developments will reduce manual oversight, promote compliance, and react to varying business needs in real-time.
AI-Based Role Mapping
AI systems will offer access levels and permissions by evaluating user behavior, access history, and peer group activity, rather than from defined role templates. This will speed up onboarding and provide ongoing access management aligned to the access actually needed by the users, which reduces privilege creep.
Predictive Provisioning
User Lifecycle Management platforms will use predictive analytics to identify your access needs before the demands are made. For instance, if you have an employee who is starting a new project next week, your system will be able to get the employee provisioned with the right tools and access ahead of time, resulting in zero downtime when the employee shifts projects.
Non-Human Identity Management
The workforce of the future is more than just people. Machine identities like service accounts, RPA bots, APIs, and IoT endpoints require the same lifecycle management as employees. Advanced User Lifecycle Management tools will track, govern, and automatically rotate credentials to these non-human identities to prevent the potential for misuse.
Support for Hybrid Workforces
With hybrid work establishing itself as the norm, User Lifecycle Management has to efficiently manage access to office systems, cloud environments, and, in some cases, to an actual physical space like smart buildings. IT will need to use location-aware policies, contextual MFA, and unified identity governance to ensure security wherever the user works.
Final Thoughts
User Lifecycle Management is not only an IT function; it is also a key security and compliance function. As workforces become increasingly hybrid, cloud adoption accelerates, and identities (human and machine) multiply, the room for error in managing access gets smaller and smaller. An orphaned account or unchecked privilege can be the difference between running a secure operation and suffering a breach that comes with significant costs.
By automating the entire identity lifecycle, adhering to least privilege, and incorporating monitoring into everyday operations, you can not only secure sensitive data but also improve efficiencies for IT and security teams. The organizations that practice ULM well now will be in a much better position to react to identity-based challenges in the future.
- Learn how Identity Confluence streamlines ULM
- See Identity Confluence in action.
Frequently Asked Questions (FAQs)
1. What is user lifecycle management?
User Lifecycle Management (ULM) refers to the process of provisioning, modifying, and deprovisioning user accounts and permissions as people enter, move within, and leave your company or organization. ULM ensures that any user, be it employee, contractor, or partner, has the right access at the right time and that this access is removed when it is no longer required. This helps enforce policy to protect sensitive data, mitigate security risks, and maintain compliance.2. Why use ULM software?
ULM software streamlines user identity-related manual processes to mitigate human and manual errors. In an erratic, multi-faceted environment, organizations need to keep up with placement, disengagement, position changes, and level changes to mitigate privilege creep and immediately deactivate associated user access to mitigate orphaned user accounts. ULM software helps organizations maintain compliance with industry standards such as GDPR, HIPAA, and ISO 27001 through audit trails and consistent access policies, removing manual effort altogether.3. How to automate user provisioning and deprovisioning?
Most automation is a simple matter of interfacing your ULM (User Lifecycle Management) or IAM (Identity Access Management) with a source of truth system, such as HR software like Workday or SAP SuccessFactors, or with a vendor management tool. Once you connect them, when a user is created, updated, or removed, they trigger provisioning or revoking access, or deprovisioning across all connected applications, without needing an IT ticket or manual action.4. What are the best practices in ULM?
Utilize a centralized IAM platform for everybody to see everything, apply privileges in a least privilege and Just-in-time (JIT) manner to limit wasted permissions, and automate provisioning and deprovisioning processes to eliminate human choke points. Utilize periodic access reviews, as well as anomaly detection with AI, to proactively manage risk, and log actions to address compliance audits.5. What should be the steps to implement ULM?
Begin by mapping the range of user types and their access needs, defining role-based policies with least privilege, and integrating your IAM or ULM platform with HR and IT systems to automate lifecycle steps, including onboarding, access changes, monitoring, and deprovisioning. Then, pilot your processes with a small group before you roll out to the full population. And as you evolve your practices based on the results of regular auditing.With Identity Confluence, these are pre-built and configurable, so that organizations can deploy a secure, compliant ULM framework sooner rather than later, usually in weeks rather than months.