
Access control is a cybersecurity mechanism that determines who can access systems, data, or applications, what they can do with them, and under what conditions. It combines authentication, authorization, and enforcement to prevent unauthorized access and misuse. As organizations operate across remote, hybrid, and cloud environments, controlling access to sensitive data and applications has become a baseline security requirement. This blog will unpack access control, how it works, and why it is central to both a secure and compliant business and still an agile one, through platforms like Tech Prescient’s Identity Confluence.
Key Takeaways
- Access control determines who can access what, when, and how
- Core pillars include authentication, authorization, and enforcement
- Popular models: RBAC (role-based), ABAC (attribute-based), DAC, and MAC
- Identity Governance (IGA) turns access control into a manageable, auditable process
- Least privilege enforcement and MFA are essential controls

What Is Access Control?
Access control is a fundamental security mechanism that ensures only authorized users, devices, or systems can access designated resources, be it files, databases, applications, or physical spaces. It governs how identities interact with systems, making sure sensitive information stays out of the wrong hands. Modern access control also accounts for context, such as time, location, or device, to make real-time, dynamic access decisions.
Access control is the process of restricting access to resources so that only authorized users, systems, or devices can interact with them. In cybersecurity, access control protects sensitive systems and data by enforcing rules around identity, permissions, and context.
Why Access Control Matters in 2026
As digital infrastructures become more distributed, the importance of access control becomes exponentially more important. In 2026, access control is not just a technical specification; it is a strategic protection against modern threats and a foundation of enterprise resilience.
Breaches happen due to a lack of controlled access:
Industry threat reports consistently show that a significant majority of breaches involve compromised credentials or excessive privileges. Without an established access control system, organizations operate with a broad attack surface for attackers to traverse laterally through their internal systems.
The expanding cloud attack surface:
Cloud platforms and SaaS are widespread, and the use of remote work has blurred the true perimeter boundaries. Access control creates borders in their hybrid ecosystems and establishes clear boundaries so that identity, not location on a network, is a new identity security perimeter.
Compliance pressures and audit requirements:
Modern IGA-enabled access control requires role-based provisioning, access reviews, and audit logs for audits as part of compliance, which can ensure organizations have controls in place for who can access sensitive data across frameworks such as HIPAA, SOX, or ISO 27001.
Mitigating Insider Threats and Over-Provisioning:
Excess or stale access from current, former (or prospective) employees, contractors or users poses a serious insider risk. When organizations do not consistently enforce least privilege or conduct access reviews, they open themselves up to the risk of data exfiltration, sabotage or regulatory violations.
Access control, especially if managed through modern IGA platforms, is a continuous control. It provides the organization with proactive oversight, automates and reduces human error, and responds to the rapidly evolving business and threat environments.
Is Your Access Control Built for Governance?
Fragmented governance breaks access control. Test your strategy against modern IGA standards.
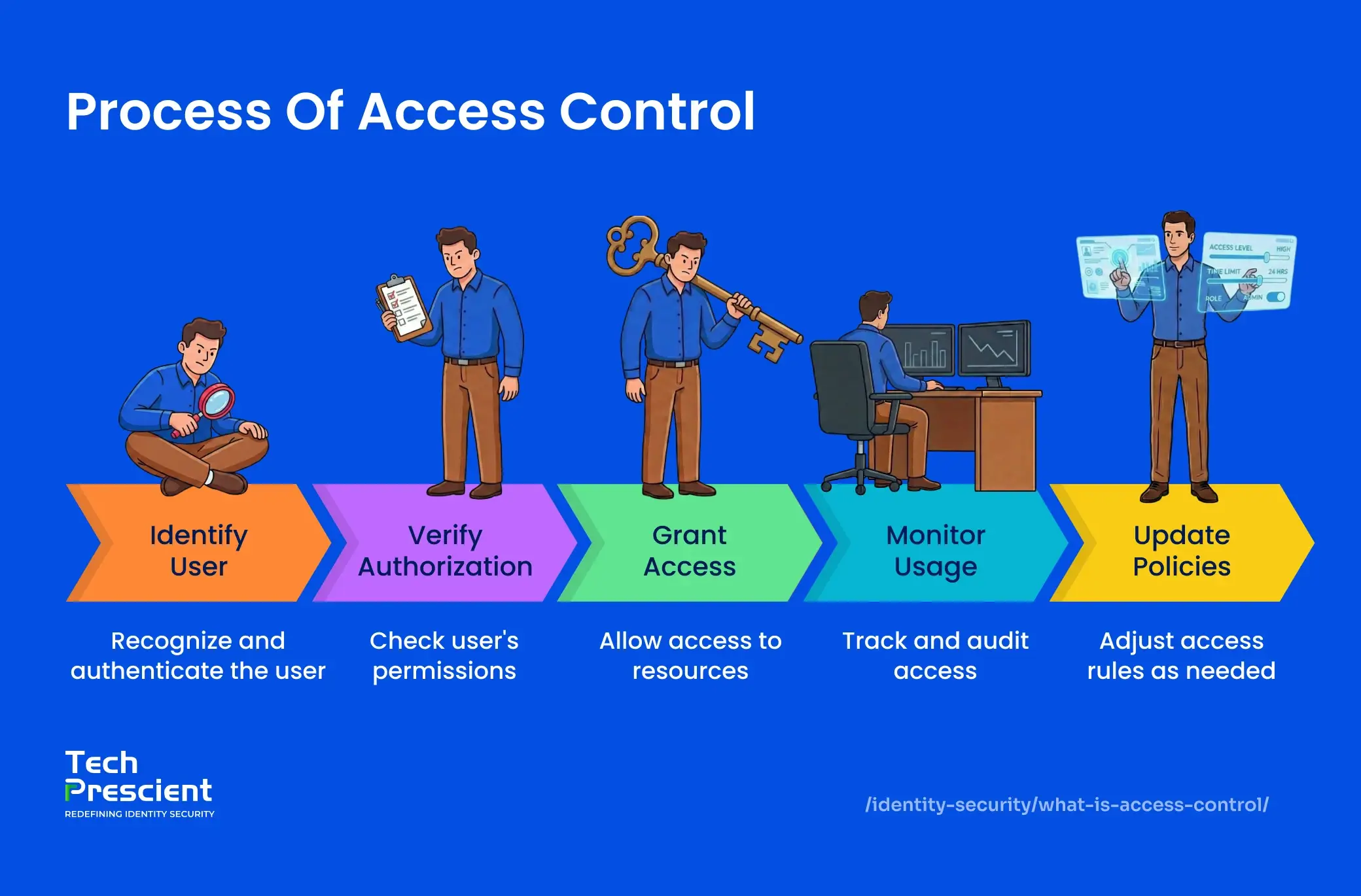
Key Components of Access Control
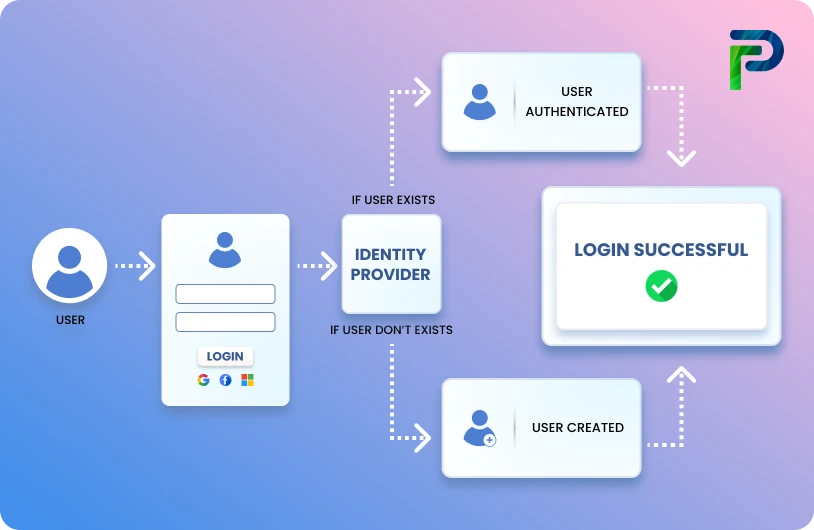
Authentication
Authentication verifies that the requester actually is who they say they are. Today, strong identity assurance offers passwordless authentication, biometrics (such as fingerprint or facial recognition), OTPs (One-Time Passwords), hardware tokens, and behavioral biometrics. MFA is being adopted more frequently because it combines something you know (password), something you have (device), and something you are (biometric), all of which substantially decrease your chances of identity spoofing.
Authorization
Authorization limits access to actions that authenticated users can take. Policies can be based on job functions (RBAC), risk, contextual input signals (device, location) (ABAC), or hybrids. Strong authorization protections limit the attack surface area by allowing only the minimum access required to perform a task.
Enforcement
Enforcement ensures that the access policy is implemented and maintained at all times. Enforcement engines integrate with applications, APIs, and network-level enforcement entities to provide real-time decisions. Enforcement engines can track an individual user and spot anomalous activity, such as anomalous login times or unexpected geographic access patterns, and dynamically limit or revoke that user's access.
| Component | Description |
|---|---|
| Authentication | Validates identity (e.g., SSO, MFA) |
| Authorization | Determines access levels (read, write, admin) |
| Enforcement | Applies policy logic in real time |
Types of Access Control in Security (With Examples)
Various access control models provide different flexibility, security, and administrative overhead. The access control model you select ultimately depends on your organization, its structure, its compliance needs, and its appetite for risk.
Role-Based Access Control (RBAC) assumes access control based on roles defined by the organization. Each role is associated with a defined set of permissions, and it enables large-scale access management. For example, the HR manager can view employee records but cannot edit anything related to finance. Generally, RBAC works well in precise, structured environments where job functions align closely to access requirements.
RBAC example: An HR manager can view employee records but cannot access payroll systems.
Attribute-Based Access Control (ABAC) does not use static roles and focuses on a multitude of contextual factors, for example, user location, device type, and time of access to inform access decisions in real-time. ABAC provides more explicit decisions, for example, granting access during business hours from a company-managed device or application. ABAC is an appropriate approach for organizations that are in flexible, cloud-first environments, where any situation can arise.
ABAC example: Access is allowed only when a user logs in from a corporate device during business hours.
Discretionary Access Control (DAC) provides flexibility for data owners by allowing them to decide who can or cannot access resources. This is often seen in collaborative tools, such as common file-sharing platforms, which allow a user to share a document or folder at their discretion. While this is convenient for access control, it may create challenges for consistent policy enforcement and auditing at scale.
Mandatory Access Control (MAC) is the strictest model of the remaining three and is enforced regardless of the discretion of the user (i.e., the data owner). Policies are enforced based on the classification and clearances of a user. This is typically enforced in government and military settings. The least privileged user and system administrator are unable to override policies. It is a great option if you desire high security and strict access controls. However, MAC is often too restrictive for general commercial uses.
| Model | Description | Example |
|---|---|---|
| RBAC | Access by role | HR can access employee records |
| ABAC | Access by attributes | Allow access only from corporate IP |
| DAC | User-controlled access | Shared Google Drive folders |
| MAC | System-enforced | Government/military environments |
Challenges of Traditional Access Control
- Manual Provisioning Errors: Relying on manual access requests results in incorrect permission assignments, delays in decisions, and workload increases on IT teams.
- Orphaned Accounts: When employees or vendors leave the organization, their credentials may remain active and be reused, deliberately or unintentionally exposing your systems.
- Poor Visibility: Access rights that are spread across various disparate systems, and without centralized governance, cannot be audited or risk-assessed.
- Inconsistent Enforcement of Policy: Without consistent tools, security policies might be enforced inconsistently, resulting in critical gaps in coverage or duplication across cloud, on-prem, and third-party services.
At this stage, most organizations recognize that access control failures aren’t caused by missing tools but by fragmented governance and manual enforcement.
Is Your Access Control Built for Governance?
Fragmented governance breaks access control. Test your strategy against modern IGA standards.
How Identity Governance (IGA) Enhances Access Control
IGA augments and scales access control by automating lifecycle management of identity and enforcing policies and governance. Identity Confluence by Tech Prescient helps enterprises through
Automated joiner/mover/leaver workflows: Automatically modify access as the employee moves or leaves the enterprise without delays or post-change updates, based on role and status determined by the enterprise.
Centralized policies: Define once and apply everywhere. IGA ensures that access control polices are applied consistently in cloud, SaaS, and legacy systems.
Continuous access reviews and access certifications: Ongoing access policy assessments or access reviews based on events or calendar triggers with the application owner for current access that is still applicable.
Role mining and SoD policy management: Evaluate access based upon actual usage patterns to identify access roles, and enforce separation of duties to avoid conflicting roles like dual-role fraud.
Dashboards and audit logging: Provide current data on access history to enable security and compliance teams so they are always audit-ready.
Benefits of Access Control with IGA
- Less human error and admin overhead: Automated workflows replace manual ticketing, removing configuration errors and streamlining processes.
- Faster onboarding and offboarding: Users who are offboarded lose immediate access, while new hires get specific access on day 1 based on department and role.
- Total visibility: Centralized dashboards show who has what access across cloud, on-premise, and third-party systems.
- Audit readiness: Automatic logs and certification workflows help organizations stay compliant with GDPR, HIPAA, and SOX, providing ready-to-export proof of evidence.
- Enforced Least Privilege and Zero Trust at Scale: Dynamic, attribute-based policies ensure users only have access to what they need when they need it in lockstep with modern Zero Trust frameworks.

Ready to Evolve Your Access Governance?
Tech Prescient’s Identity Confluence combines intelligent access models, seamless automation, and enterprise-ready governance into a single platform. If you're ready to bring together your fragmented controls and move towards intelligent identity management:
Book a Demo with our team to evaluate your access strategy for 2026 and beyond.
Access Control vs Access Management vs IAM vs IGA
To build a resilient identity security strategy, it’s essential to distinguish between Identity and Access Management (IAM), Access Control, and Identity Governance and Administration (IGA). While the three areas are interconnected, each area serves an important, independent purpose as the following provides an overview.
IAM (Identity and Access Management) identifies the identity lifecycle, from account creation and password resets to user authentication, and IAM answers the question "who are you?" It is the basis that allows entry for only verified identities.
Access Control takes IAM further by answering "what can you do once you're in?" Access Control identifies authorization: What systems or data can the user access; and the conditions in-place that permit access. This supports organizational policies like least privilege and Zero Trust.
IGA (Identity Governance & Administration) sits above IAM and Access Control with the objective of review, compliance, and alignment with internal policies and external requirements. IGA enables workflows (e.g., onboarding/offboarding), manages/automates access review, and has specific audit trails.
You may think of it as a three-tier system:
- IAM identifies or authenticates identities.
- Access Control governs access decisions for authorized identities.
- IGA governs the organizational whole for compliance and visibility.
Best Practices for Access Control in 2026
It is important to understand the distinctions between IAM, Access Control, and IGA when creating a comprehensive identity security architecture. IAM (Identity and Access Management) primarily relies on identity lifecycle management. This includes creating user accounts, authenticating users with credentials or with multi-factor authentication (MFA), and allowing for self-service functions such as password changes or resets. IAM provides an initial construction for how users can access data and applications securely.
Access Control extended from IAM to then enforce the “rules” of what authenticated users can do in a system, specifically authorization management, who can access what data, applications, or systems, and under what conditions. Access Control is primarily what tells the user which resources they can see or interact with based on their Job or Risk Profile.
Identity governance and administration (IGA) provides the policy and oversight structure that governs IAM and Access Control. The goal of IGA is to ensure that access is correct technically and is compliant with internal governance and external laws. IGA tools allow the organization to operate efficiently and maintain compliance by allowing for policies that govern and automate the provisioning/deprovisioning workflows, posing periodic access reviews, and generating audit-ready reports.
Here is what our expert suggests
We asked our Chief Architect at Tech Prescient what truly makes access control work in the real world, and here’s what they had to say:
“Our recommendation is simple: make access governance continuous. Don’t just assign roles, review them regularly. Don’t just enforce policies; monitor and validate them against real-world behavior. And wherever possible, automate. Automation doesn’t just save time; it removes the human error attackers depend on.”

Mukesh Rathod
,Chief Architect
This expert insight aligns with what we’ve built into Identity Confluence: a dynamic, policy-driven, and constantly monitored access framework that’s built for scale, compliance, and rapid change.
Conclusion
Access control has evolved from a simple gatekeeper function to become the cornerstone of modern identity security. In 2026's distributed, cloud-first landscape, organizations can no longer rely on manual processes or siloed systems to manage who has access to what. The combination of sophisticated access control models like RBAC and ABAC, strengthened by comprehensive IGA platforms, provides the automation, visibility, and governance enterprises need to stay secure and compliant. As threats continue to evolve and regulatory requirements tighten, the organizations that thrive will be those that treat access control as a continuous, adaptive process rather than a one-time configuration.
Implementing the strategies outlined in this guide, from enforcing least privilege to automating identity lifecycle management, can transform access control from a security burden into a strategic enabler. The journey to mature access governance doesn't happen overnight, but with the right foundation and tools like Identity Confluence, enterprises can build an identity security framework that scales with their growth while maintaining the agility to respond to tomorrow's challenges.
Is Your Access Control Built for Governance?
Fragmented governance breaks access control. Test your strategy against modern IGA standards.
FAQs
Access control in cybersecurity controls who can access systems, data, or networks, and what actions they are allowed to perform. It ensures that only authenticated and authorized people can access sensitive resources and eliminates the risk of unauthorized exposure or misuse.
IGA enhances access control by automating identity lifecycle tasks such as provisioning, enforcing access policies through RBAC and ABAC, conducting periodic access reviews, and providing compliance-ready audit trails from a central platform.
IAM manages identities and authentication processes of users such as login and password resets, while IGA is transforming governance to establish policies, reviewing access, and ensuring compliance with internal and external regulations.
The two most popular styles of access control are Role-Based Access Control (RBAC), which assigns permissions based on user roles, and Discretionary Access Control (DAC), which allows resource owners to decide who can access their resources.
The principle of least privilege provides the minimum access levels that users need to perform their tasks. This reduces insider threats, prevents data exfiltration, and limits damage if an account is compromised.
Examples include: RBAC - where HR can access employee records but not financial data; ABAC - where access is granted based on conditions like device or time; DAC - where users can share access like in Google Drive; and MAC - where access is restricted based on security clearance in government systems.
Multi-Factor Authentication (MFA) strengthens access control by requiring two or more verification factors, such as a password and a fingerprint, reducing the risk of unauthorized access even if credentials are compromised.
Brinda Bhatt
Digital Marketing Strategist
She focuses on translating complex concepts, particularly identity governance, into clear, actionable insights for business and technical audiences. She is led by a logical, data-driven approach to content creation and explores optimal and constructive storytelling.
Most Popular Blogs
Identity Security· 19 min read
Just-in-Time (JIT) Provisioning Explained: How It Works & Why It Matters
Learn how Just-in-Time (JIT) provisioning automates user onboarding via SSO and SAML, saving admin time while improving access security.
Rashmi Ogennavar· December 22, 2025

