Segregation of Duties: The Ultimate Guide to Implementation, Examples, and Compliance
Learn segregation of duties (SoD), meaning, examples, checklist & tools. Prevent fraud, ensure compliance, and enforce secure access with IAM/IGA.
Last Updated date: March 18, 2026
What is Segregation of Duties?
Segregation of Duties (SoD) is a critical internal control mechanism used to minimize the risk of fraud, errors, and unauthorized access by ensuring that no single individual is responsible for all aspects of a critical process. This means that responsibilities are split among different individuals to establish checks and balances in daily operations.
Overall, SoD involves dividing tasks related to authorization, custody, record-keeping, and reconciliation. This control is applicable in accounting, cybersecurity, & auditing functions in order to ensure regulatory compliance with standards like the Sarbanes-Oxley Act (SOX) and the General Data Protection Regulation (GDPR). For example, one employee may be responsible for approving any payment, another for processing it, and a third for reconciling the accounts afterward.
Why is Segregation of Duties Important?
Segregation of Duties (SoD) is no longer just a finance or audit control, it is a critical cybersecurity safeguard. As organizations rely more heavily on digital systems, cloud platforms, and privileged access, SoD plays a direct role in preventing insider threats, privilege misuse, and unauthorized access. In modern IT environments, a single individual having unchecked control over provisioning, approval, and monitoring creates a serious security blind spot. SoD reduces this risk by enforcing checks and balances across identity, access, and operational workflows. From a compliance perspective, regulatory frameworks such as SOX, GDPR, HIPAA, and PCI-DSS explicitly require SoD controls to prevent fraud, enforce accountability, and demonstrate governance during audits. Organizations that fail to implement effective SoD often struggle with audit findings, access violations, and compliance penalties. In short, Segregation of Duties strengthens security posture, improves operational accountability, and ensures regulatory alignment, making it a foundational control for both cybersecurity and governance teams.
Segregation of Duties in Cybersecurity
In cybersecurity, Segregation of Duties is essential for preventing misuse of privileged access and reducing insider risk. IT environments involve sensitive actions such as provisioning users, approving access, modifying systems, and auditing activity. When these responsibilities are concentrated within a single role, the risk of abuse or error increases significantly.
A strong SoD model in cybersecurity ensures that:
- No single user can both grant and approve access
- The team that provisions accounts is different from the team that audits access
- Security monitoring is separated from system administration
For example:
- One team provisions user access
- Another team reviews access logs and entitlement changes
- A third team handles compliance reporting and audits
Modern Identity and Access Management (IAM) and Identity Governance and Administration (IGA) platforms are commonly used to enforce SoD in IT. These tools automate access controls, detect SoD conflicts, and continuously monitor role assignments to ensure policy compliance. Implementing SoD in cybersecurity directly supports Zero Trust principles by limiting implicit trust and enforcing least-privilege access across systems.
Segregation of Duties Examples
Real-world examples help clarify the practical value of Segregation of Duties.
Payroll Process
- Employee A enters work hours
- Employee B approves timesheets
- Employee C processes payroll
- Employee D reconciles payroll reports
Procurement Process
- Employee A creates a purchase request
- Employee B approves the request
- Employee C receives goods
- Employee D issues payment
IT Access Management
- IT Admin provisions user accounts
- Security team reviews access permissions
- Compliance team audits access logs
By dividing responsibilities across multiple roles, organizations reduce the risk of fraud, accidental errors, and unauthorized activity.
Segregation of Duties in Auditing
Auditors rely on Segregation of Duties to ensure organizations maintain strong internal controls and minimal risk of exposure. SoD enhances transparency and objectivity in financial and operational processes.
Audit practices include:
- Reviewing role assignments and permissions.
- Identifying conflicts in user access or workflow.
- Recommending corrective measures to mitigate risk.
Segregation of Duties is also a crucial element in SOX audits, which require companies to prove that financial activities are not controlled by a single individual without oversight.
Core Components of Segregation of Duties
The following four functions form the foundation of Segregation of Duties:
Authorization
Authorization is the process of approving specific actions and transactions. Only authorized personnel can approve activities like payments or contract signings, ensuring that all transactions are legitimate and policy-compliant.
Custody
Custody is a process that involves the responsibility of managing assets or even holding them, whether they are physical (such as cash or inventory) or digital (like data or credentials). An individual with custody safeguards these assets but does not have the authority to approve their use or movement.
Record-Keeping
Record-keeping primarily means accurately documenting all transactions and maintaining up-to-date records. Individuals in this role document and track activities, but do not have access to the assets themselves. Neither do they have the authority to approve any type of transactions. This ensures transparency and accountability.
Reconciliation
Reconciliation is the independent review and comparison of records with actual assets or external data. This step verifies that recorded transactions align with actual assets or external records, helping to identify errors or fraud, if any. The person reconciling should not be involved in authorization, custody, or record-keeping.
Example:
Let us understand the above concepts with the help of an example:
In a payroll process, an employee enters work hours (that is record-keeping), another individual approves them (authorization), a third person may disburse payments (custody), and a fourth checks the records against bank statements (reconciliation). This separation of duties reduces the risk of mistakes or any kind of fraud.
Segregation of Duties vs. Separation of Duties: What's the Difference?
Although these terms are often used interchangeably, Segregation of Duties and Separation of Duties have distinct contexts.
| Feature | Segregation of Duties (SoD) | Separation of Duties |
|---|---|---|
| Definition | Divides tasks across roles for fraud prevention | Splits access/control in IT/security systems |
| Primary Use | Finance, auditing, compliance | Cybersecurity, IAM |
| Example | Separate roles for approving and processing pay | One team provisions users; another audits |
While SoD is typically used in financial and operational controls, separation of duties is more commonly referenced in IT and security environments.
How to Implement Segregation of Duties in Practice
Segregation of Duties Matrix
A Segregation of Duties matrix is a practical tool used to identify and eliminate conflicting responsibilities across roles. It visually maps which roles can perform which actions, helping organizations spot risk before it introduces operational or compliance risk
How to build a SoD matrix:
- Identify critical business or IT processes
- List all roles involved
- Map each role against actions such as prepare, approve, execute, and audit
- Identify overlaps that create conflicts
- Resolve conflicts through reassignment or automated controls
Example SoD Matrix:
| Role | Prepare | Approve | Reconcile |
|---|---|---|---|
| Accountant | ✔ | ||
| Manager | ✔ | ||
| Auditor | ✔ |
SoD matrices are widely used during audits and are often required to demonstrate compliance with SOX and internal control frameworks.
Need a ready-to-use SoD matrix?
Download an audit-ready Segregation of Duties conflict matrix to identify risky access combinations across IT and identity systems.

Segregation of Duties Checklist
Use this checklist to ensure your SoD framework is effective and audit-ready:
- Identify all critical business and IT processes
- Document roles and responsibilities
- Prevent conflicting duties through access controls
- Enforce least-privilege access
- Deploy IAM or IGA tools to monitor access
- Conduct regular access reviews
- Maintain documentation for audits
- Train employees on SoD policies
This checklist helps organizations maintain continuous compliance and reduce operational risk.
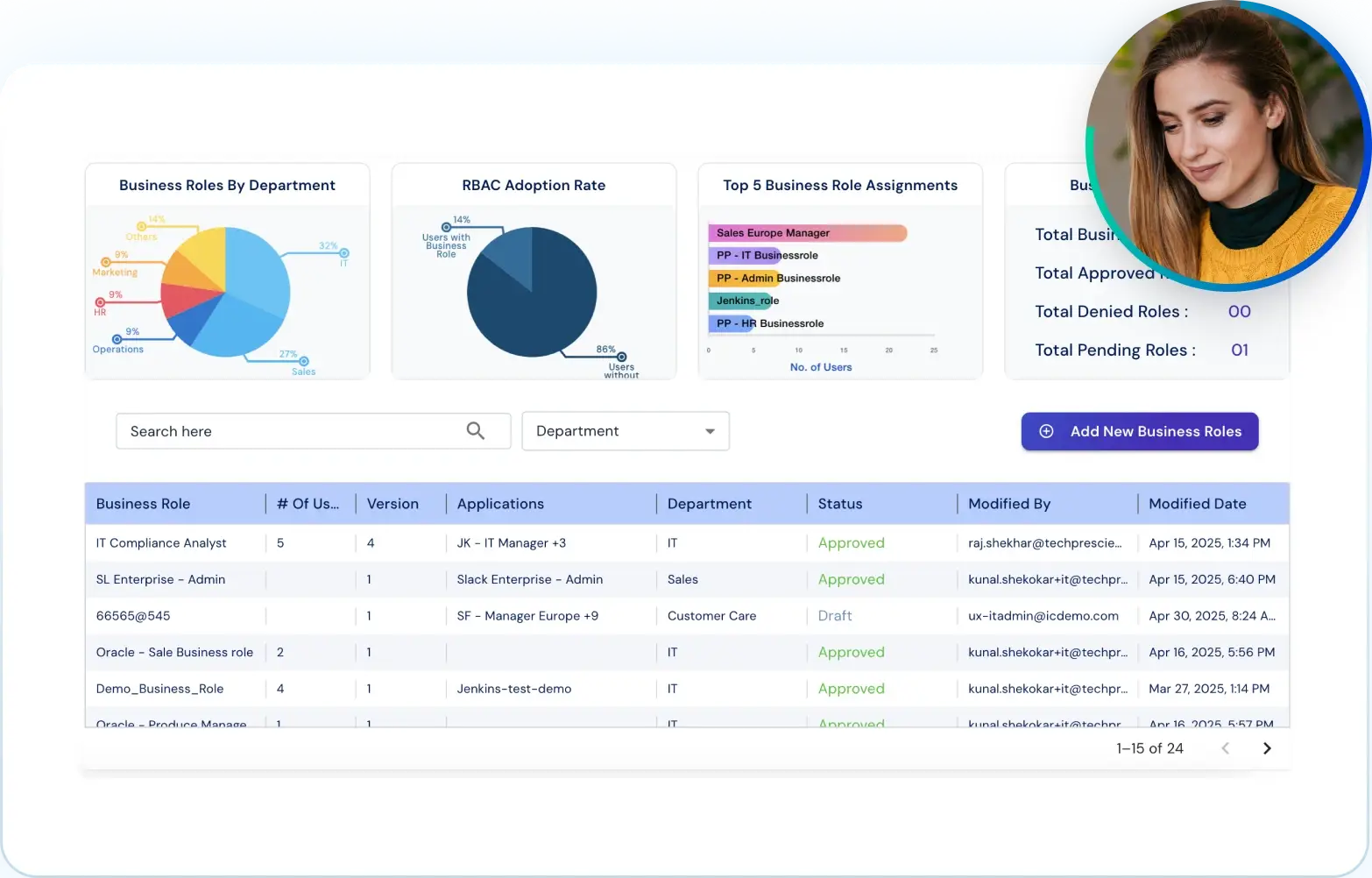
Enforcing Segregation of Duties with IAM / IGA Tools
Manual enforcement of Segregation of Duties does not scale. As environments grow, organizations increasingly rely on IAM and IGA platforms to automate SoD enforcement. These tools help by:
- Detecting SoD conflicts automatically
- Preventing unauthorized role combinations
- Automating access reviews and certifications
- Generating audit-ready reports
- Providing continuous monitoring of access changes Automating SoD through IGA platforms significantly reduces human error and ensures policies remain enforced as users, roles, and systems change.
Best Practices for Segregation of Duties Implementation
Implementing SoD successfully requires a blend of people, processes, and technology. Follow these best practices:
Clearly define roles and responsibilities across departments
The foundation of effective SoD must be communicated organization-wide. This can be done by ensuring that every employee knows their specific duties and how they align with broader processes. Job descriptions should explicitly outline tasks and limitations of authority to avoid overlap.
Automate access controls and approval workflows using IGA solutions
Manual processes can lead to errors or overlooked conflicts. Implementing IAM and IGA tools allows organizations to automatically enforce policies, flag violations, and restrict access based on predefined roles. Automation not only increases accuracy but also enhances scalability.
Conduct periodic internal audits to validate SoD policies
Regular audits help ensure that existing SoD frameworks remain effective as teams evolve and processes change. Audits should examine user access rights, identify conflicting roles, and verify whether controls are functioning as intended.
Train employees on their specific duties and the importance of compliance
Awareness and education are crucial. Provide mandatory training sessions for all new employees and conduct refresher courses periodically to reinforce the importance of maintaining SoD and avoiding conflicts of interest.
Maintain proper documentation to demonstrate audit readiness
Documentation is essential for internal governance and external compliance. Keep records of role assignments, access control reviews, training logs, and audit findings. Proper documentation not only improves operational clarity but also simplifies regulatory reporting.
By following these best practices, organizations can establish a robust and sustainable SoD framework that mitigates risk, supports compliance, and fosters a culture of accountability.
Conclusion
Segregation of Duties is not just an internal control, it is a security and compliance necessity. Without proper SoD enforcement, organizations expose themselves to fraud, insider threats, audit failures, and regulatory penalties.
Modern enterprises cannot rely on manual processes alone. As access environments become more complex, automating Segregation of Duties through identity governance tools becomes essential for maintaining control, visibility, and compliance at scale.
At Tech Prescient, we help organizations implement and automate Segregation of Duties using intelligent Identity Governance solutions. From SoD conflict detection to continuous access monitoring, we enable teams to enforce security policies without slowing down operations.
Automate Segregation of Duties Enforcement
Detect SoD conflicts in real time and enforce least-privilege access without manual effort.

FAQs
Segregation of Duties (SoD) is a security and internal control practice that prevents a single individual from controlling all stages of a critical process. By dividing responsibilities such as approval, execution, and auditing, organizations reduce the risk of fraud, errors, and unauthorized access.
Segregation of Duties is important because it reduces fraud risk, prevents insider threats, and ensures regulatory compliance. Without SoD, a single user could exploit access privileges without detection, increasing the likelihood of financial loss, data breaches, and audit failures.
A common segregation of duties example is payroll processing, where one employee enters hours, another approves them, a third processes payments, and a fourth reconciles records. In IT, one team provisions access while another audits permissions to prevent misuse.
The four core components of segregation of duties are authorization, custody, record-keeping, and reconciliation. These functions must be handled by separate roles to ensure accountability, prevent conflicts of interest, and detect fraud or errors early.
In cybersecurity, segregation of duties ensures that no single user can provision access, approve permissions, and audit activity. This separation reduces insider threats, limits privilege abuse, and supports Zero Trust and least-privilege security models.
A segregation of duties matrix is a visual tool that maps roles against critical tasks to identify conflicts. It helps organizations detect risky role combinations and is commonly used during audits to demonstrate compliance with internal controls and regulations like SOX.
IAM and IGA tools enforce segregation of duties by detecting access conflicts, preventing unauthorized role combinations, automating access reviews, and generating audit logs. These tools enable continuous SoD enforcement at scale without relying on manual controls.