User Access Review Policy: Process, Audit & Best Practices

A user access review policy is a crucial framework for IT managers to proactively manage access privileges in response to the growing threat of data breaches and regulatory requirements. Far more than just a compliance checkbox, it serves as an effective governance tool that helps in the evaluation and management of user privileges, ensuring that only authorized individuals can access critical resources. By regularly checking who has access to what and updating permissions when employees leave or change roles, a user access review policy helps organizations strengthen security, uphold compliance, and minimize risk.
But over time, access tends to "drift." Employees change teams, leave the organization, or are promoted, yet their former permissions remain with them. When roles and responsibilities change, access permissions may become outdated or excessively permissive. This increases the risk of security breaches, data leaks, and compliance violations within the organization. Before you realize it, some accounts end up with more access than they should, and no one’s keeping an eye on them. That’s exactly the kind of gap attackers look for. Not managing access properly not only raises the risk of data breaches but can also cause issues during compliance audits.
According to recent data by Secureframe, cyberattacks using stolen or compromised credentials increased by 71% in only one year. Even more concerning, 74% of all breaches currently include human intervention. In other words, most breaches are the result of poor access control, insecure credentials, and ignored entitlements.
That is why user access reviews are so impactful. By routinely certifying, altering, or removing rights, companies close one of the most common attack vectors while demonstrating to auditors that governance is under control. Next, we’ll look at how to set up a solid user access review policy, build processes that are always audit-ready, and follow best practices to lower insider risks.
Key Takeaways:
- Understand how a user access review policy helps enforce the principle of least privilege and role-based access control.
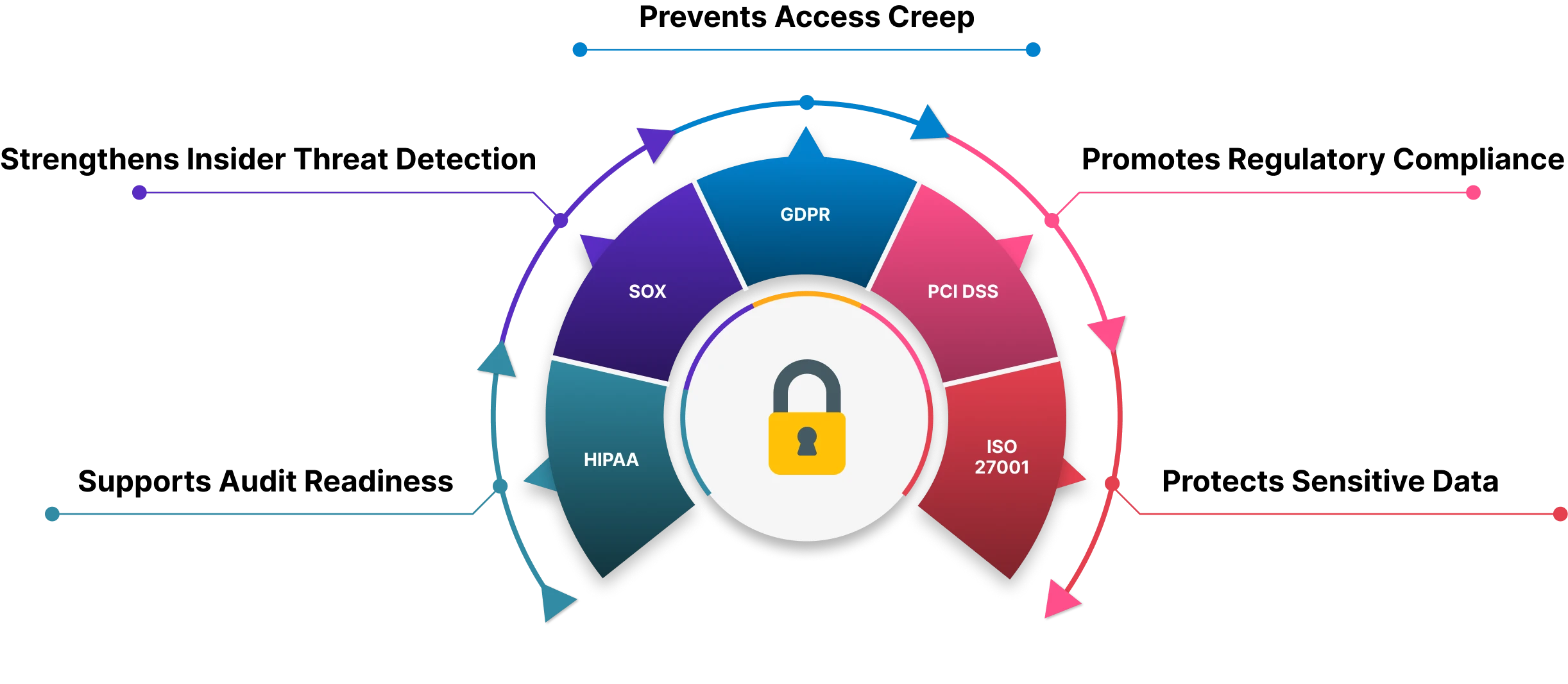
- Learn why access reviews are required by compliance frameworks such as GDPR, SOX, and HIPAA.
- See how regular reviews prevent privilege creep and reduce insider threats.
- Discover how structured reviews support audit readiness and strong governance.
- Follow best practices to make access reviews efficient, scalable, and compliant.
What Is a User Access Review Policy?
A user access review policy is a vital component of an organization’s cybersecurity strategy. It defines the guidelines and procedures for regularly reviewing, monitoring, and managing user accounts and their associated access rights across the digital environment. As part of a broader user account management and access control process, it ensures that the access rights of employees and third-party users are periodically reviewed to prevent unauthorized access.
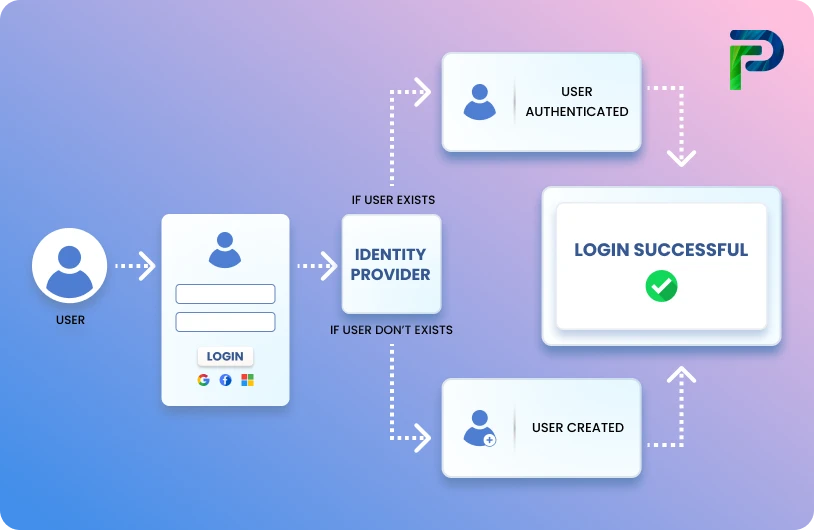
A user access review also serves as an essential pillar of a strong identity and access management (IAM) strategy, where the focus lies on evaluating who has access to critical systems, applications, and data. Based on these assessments, organizations can adjust permissions when necessary, ensuring that users retain only the level of access they require to perform their roles effectively and securely.
Through such a policy, organizations can continuously validate and adjust access privileges, preventing unauthorized access by former employees, contractors, or individuals who have changed roles. This proactive approach reduces the likelihood of insider threats, data breaches, and cyberattacks.
Beyond security, a well-designed user access review policy also supports regulatory compliance, helping organizations avoid fines and reputational damage. Regular reviews further optimize IT operations by ensuring that employees consistently have the appropriate level of access required to perform their responsibilities effectively.
Additionally, the policy provides a framework to address discrepancies uncovered during access audits. For instance, if an audit identifies that a former employee still retains active access to critical systems, immediate remediation is required to revoke access and investigate the oversight, thereby preventing recurrence of similar risks.
Why User Access Reviews Matter for Compliance & Security?
At its core, user access reviews enables organizations to reassess user roles, access privileges, and entitlements. The primary objective is to minimize the risk of security breaches by restricting access to critical data and resources only to authorized users. Regularly refining access rights not only strengthens security but also reduces system clutter, streamlines IT operations, and improves the overall user experience by granting employees access strictly to what they need to perform their roles effectively. Here’s a closer look at the key ways user access reviews strengthen security and compliance within an organization.
- Unauthorized Access
As employees’ roles evolve, they often retain unnecessary access rights, creating risks such as privilege creep. User Access Reviews (UARs) help identify and revoke such excess privileges, thereby reducing the organization’s overall attack surface. This proactive approach strengthens security by preventing unauthorized access and mitigating insider threats like privilege misuse, abuse, and escalation.
- Privilege creep happens when employees accumulate more access rights to critical systems and sensitive data than their job roles require. This usually occurs as they take on new responsibilities or projects, while outdated permissions are left in place instead of being revoked.
- Privilege misuse occurs when individuals use their granted privileges in ways that differ from the intended purpose. Such misuse may be accidental, careless, or deliberate, but regardless of intent, it often results in cybersecurity breaches.
- Privilege abuse refers to the deliberate exploitation of privileges to steal, compromise, or damage an organization’s sensitive information. Both malicious insiders and external attackers who compromise privileged accounts may engage in such abuse.
- Privilege escalation arises when users unlawfully obtain higher levels of access than authorized, typically through malicious techniques. Once elevated, these privileges can be exploited to move laterally across systems, access confidential resources, and target critical infrastructure.
-
Strengthens insider threat detection
As employees transition into new roles or take on different responsibilities, they often retain access rights that are no longer relevant to their current positions. User access reviews (UARs) help detect these discrepancies and remove unnecessary privileges, thereby reducing the overall attack surface available to malicious actors. By revoking redundant access, organizations can prevent unauthorized activity and mitigate risks associated with insider threats. -
Supports regulatory compliance
Many industries operate under strict regulatory standards such as Europe’s GDPR for data protection, HIPAA for healthcare, and SOX for financial reporting. These frameworks often require organizations to perform regular user access reviews to ensure sensitive information is protected against misuse or unauthorized access.
Conducting these reviews creates a detailed audit trail, documenting who has access to specific systems, when changes occurred, and how access rights are managed. Such documentation becomes essential during compliance audits, for example, SOX assessments demand a thorough review of access to financial systems to verify that only authorized personnel can handle sensitive financial data. Failure to maintain this level of oversight can result in regulatory violations, which may carry heavy fines, legal liabilities, and severe reputational harm.
Core Elements of a User Access Review Policy
To build an effective user access review policy, organizations must define their scope, determine how frequently reviews occur, assign clear stakeholder responsibilities, and establish strong documentation protocols. Each of these elements works together to ensure that access reviews are not only consistent and accurate but also aligned with compliance requirements. The following sections break down these core components in detail.
Scope of Access Reviews – What systems and users are included?
A robust User Access Review (UAR) policy depends on having a clear objective and scope, as these elements together determine the effectiveness of the review process. For IT managers, defining them well ensures that reviews are purposeful, aligned with organizational security goals, and capable of addressing real risks. The objective gives the policy its direction by establishing why reviews are necessary, while the scope sets the boundaries of who and what will be included in those reviews. A strong objective should be concise, easy to understand, and directly relevant to the security and compliance challenges faced by the organization.
For example, one could state: “To regularly review and assess user access rights to sensitive data, minimizing the risk of unauthorized data exposure and ensuring compliance with industry regulations.”
The scope, on the other hand, outlines the specific users, systems, applications, and data that fall under review. It essentially answers the question: Who and what will be included in our access reviews? When defining this, organizations often take into account the different types of users (employees, contractors, or external partners), the systems and applications they access (databases, networks, or business-critical platforms), and the sensitivity of the data involved (confidential, sensitive, or public). Practical considerations like the frequency of reviews and role-based exceptions also form part of the scope, ensuring the policy is both comprehensive and realistic.
For instance, a scope statement could read: “This policy covers all employees and contractors with access to sensitive customer data within the CRM system. Reviews will be conducted quarterly, with exceptions for IT administrators, who will be reviewed annually.”
Review Frequency – Monthly, quarterly, annually
The review frequency in a user access review policy defines how often user access rights are assessed and validated. Finding the right balance is essential; reviews conducted too rarely may leave obsolete or unauthorized access undetected, while overly frequent reviews can overwhelm IT teams with unnecessary administrative work. Ideally, the frequency should reflect the pace of organizational changes, such as employee onboarding, role transitions, or project-specific needs. This approach ensures an accurate, up-to-date view of user privileges and helps confirm that only authorized individuals maintain access to critical systems and data.
Alongside periodic checks, triggers play an equally important role by signaling when an access review is required outside the regular cycle. These triggers are tied to significant events, like an employee leaving the organization, receiving a promotion, or changing responsibilities. They may also include unexpected developments such as a security breach or shifts in compliance requirements. By integrating these triggers into the policy, organizations can promptly reassess access rights when circumstances change, reducing the risk of unauthorized access and closing potential security gaps.
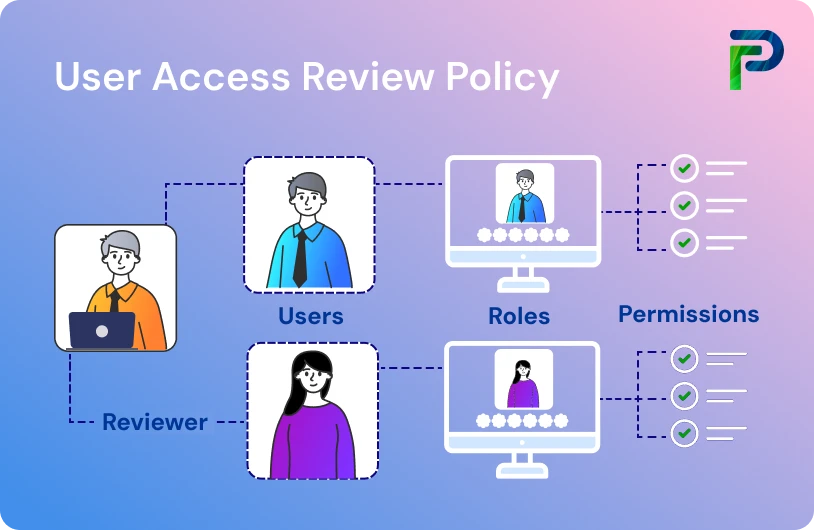
Stakeholder Roles – HR, managers, IT, auditors
Defining stakeholder roles is central to an effective user access review policy. When responsibilities are allocated across teams, reviews become more structured, risks are reduced, and accountability is strengthened. Each group, HR, managers, IT, and auditors, plays a unique part in ensuring that access privileges remain accurate, relevant, and compliant.
- HR Teams
HR serves as the starting point for provisioning and deprovisioning users. By maintaining accurate employee records and promptly notifying IT of new hires, role changes, or departures, HR ensures that access rights stay aligned with an individual’s employment status. Their involvement minimizes the risk of lingering or unnecessary accounts. - Managers
Line managers or business unit leaders act as access reviewers and approvers. Since they best understand the operational needs of their teams, they are responsible for verifying whether employees still require certain permissions. This oversight ensures that access aligns with business needs and helps prevent privilege creep. - IT Administrators
IT teams manage the technical side of access control, granting, modifying, and revoking permissions across systems. Their role is to implement manager and HR inputs in real time, enforce the principle of least privilege, and maintain secure configurations. By serving as the custodians of system access, IT administrators reduce the chances of unauthorized entry. - Auditors and Compliance Officers
Finally, auditors and compliance officers provide independent oversight. They evaluate whether access reviews are carried out effectively and verify that processes align with regulatory requirements. Their assessments help identify gaps, enforce accountability, and strengthen overall governance.
When these stakeholders work in coordination, the user access review process functions as a closed loop: HR triggers changes, managers validate necessity, IT executes updates, and auditors ensure compliance. This collaboration not only safeguards sensitive information but also embeds security awareness into day-to-day operations.
Documentation Protocols – Audit trail, certifications
Robust documentation protocols are the backbone of a strong user access review policy. They establish a clear audit trail, capturing who had access, what changes were made, when they occurred, and why they were approved. This not only enforces accountability but also provides solid evidence during audits and certification reviews.
A reliable audit trail should cover:
-
User Profiles and Roles: Detailed records of user responsibilities and associated access permissions, creating a structured view of access levels.
-
Access Change Logs: A comprehensive log of all modifications, including who initiated the change, the time of change, and the justification behind it.
-
Access Approval Workflow: Documentation of the entire process for granting access, from request to authorization, ensuring clarity and transparency.
-
Access Removal Process: A defined protocol for revoking access promptly when employees leave or transition to new roles, preventing privilege creep.
Beyond tracking, documentation also supports certifications and compliance. This is where reporting frequency becomes critical. Specifying how often reports are generated and reviewed ensures continuous oversight of access patterns, highlights unusual activity, and provides proof of proactive governance.
Together, audit trails and certification protocols elevate documentation from simple recordkeeping to an active safeguard, strengthening security, ensuring regulatory alignment, and reinforcing organizational trust.
Step-by-Step User Access Review Process
An effective user access review requires a structured approach. The following steps outline how to gather access data, involve the right stakeholders, flag anomalies, and take corrective action, while keeping documentation audit-ready.
Step 1. Generate access reports/Extract access data
The first step in reviewing user access is to generate accurate and comprehensive access reports. This process involves compiling information from all organizational assets, servers, workstations, network devices, cloud platforms, databases, and other systems where sensitive data is stored or processed. These reports form the foundation for assessing whether access rights are appropriate and compliant.
There are two primary approaches to extracting access data:
-
Automated Tools and Scripts: Whenever possible, rely on automation to pull access information directly from systems. Automated extraction reduces manual effort, eliminates human error, and ensures consistency. Key details to capture include user names, assigned roles, access levels, and last access timestamps.
-
Manual Processes: In environments where automation is not feasible, due to system limitations or tool incompatibility, manual collection is required. Here, system administrators compile access rights lists from applications and platforms to provide the necessary visibility into user privileges.
By combining both automated and manual methods, organizations can generate access reports that are complete, accurate, and tailored to their unique IT landscape.
Step 2. Review with department heads
Involving department heads is a critical component of the user access review process. Since managers and business leaders have direct visibility into their teams’ responsibilities, they are best positioned to verify whether access rights align with actual job requirements. Their involvement not only reinforces accountability but also ensures that access reviews are rooted in the operational context rather than being a purely technical exercise.
Department heads should:
- Validate User Permissions: Confirm that employees under their supervision retain only the access necessary for their roles, preventing privilege creep.
- Review Documentation: Cross-check access records against job functions to ensure accuracy during onboarding, role changes, or offboarding.
- Identify Outliers: Flag unnecessary or outdated permissions that IT teams may overlook without business context.
- Collaborate with IT: Work alongside administrators to approve, modify, or revoke access rights, ensuring changes are both technically feasible and business-relevant.
By integrating department heads into the review process, organizations strengthen accountability and create a closed feedback loop where access decisions are informed by both technical oversight and business needs.
Step 3. Flag anomalies or unnecessary privileges
One of the primary objectives of an access review is to detect anomalies, instances where users, applications, or processes hold permissions that exceed what is truly required. Left unchecked, these unnecessary privileges can create opportunities for insider threats, privilege misuse, or accidental data exposure.
The Principle of Least Privilege (PoLP)
At the core of this process lies the Principle of Least Privilege (PoLP). It dictates that every user, system, or application should have only the minimum level of access required to perform its function, no more, no less. By limiting access rights in this way, organizations reduce their attack surface and ensure that if an account is compromised, the potential damage is restricted.
For example:
- User Accounts: Regular employees operate with standard access, while elevated or administrative privileges are tightly controlled.
- Applications and Systems: System processes run with narrowly defined permissions, preventing them from interacting with unrelated data or networks.
- Temporary Privileges: Elevated access is granted only for specific tasks and automatically revoked once the activity is complete.
Steps to Flag and Address Excess Privileges:
- Identify Anomalies: Scrutinize access reports to spot accounts with privileges beyond role requirements, such as admin rights for non-IT staff.
- Reduce Unnecessary Access: Downgrade or revoke excess permissions promptly, aligning them with PoLP.
- Cross-Check with Departments: Collaborate with department heads to validate complex or cross-functional access needs that may appear excessive at first glance.
- Document and Approve Exceptions: Any deviation from the principle of least privilege should be justified, recorded, and approved by the relevant stakeholders.
By embedding the principle of least privilege into access reviews, organizations turn it into a practical filter: any access beyond the principle’s limits is flagged as an anomaly. This makes it easier to spot unnecessary privileges, close gaps proactively, and maintain stronger security and compliance.
Step 4. Revoke, adjust, or approve access
Once anomalies are flagged, corrective action must follow swiftly to maintain security and compliance. The goal is to ensure only legitimate and necessary access rights remain active, minimizing risks from outdated or unauthorized privileges.
- Revoke Unauthorized Access: Establish a systematic process to immediately remove outdated, unnecessary, or suspicious privileges. Coordinate with IT security to prevent disruption, scheduling revocations carefully, or granting supervised temporary access when critical operations are at stake.
- Adjust Roles and Permissions: Review and refine user roles to align with actual responsibilities. This may involve redefining job functions, updating group memberships, or creating new role profiles to reflect business needs accurately.
- Approve and Document Exceptions: For cases requiring special or cross-functional access, formally approve them through department heads, with clear documentation to ensure accountability and transparency.
By revoking excess rights, adjusting roles appropriately, and approving only justified exceptions, organizations maintain a strong balance between security and operational efficiency.
Step 5. Document all changes
Accurate documentation is critical to ensure accountability, compliance, and audit readiness. Every step of the user access review, including findings, corrective actions, and follow-up measures, should be captured in detail.
-
Report the Review Process: Maintain a comprehensive record of the review’s scope, data collection methods, identified discrepancies, corrective actions, and rationale behind revocations or adjustments. Specific instances of unauthorized or inappropriate access must be logged.
-
Create an Action Plan: Outline recommendations for strengthening access control policies and procedures. Include follow-up tasks, assigned responsibilities, deadlines, and measurable outcomes to track effectiveness.
-
Communicate with Stakeholders: Share reports with management, IT security, department heads, and auditors to ensure transparency. Gather feedback to improve future reviews.
-
Maintain Compliance Records: Securely store reports, supporting documents, and logs for regulatory or audit purposes, ensuring they are well-organized and easily retrievable.
By thoroughly documenting every change, organizations not only strengthen accountability but also demonstrate compliance with security and regulatory requirements.

Best Practices for Efficient & Scalable Access Reviews
A user access review becomes more efficient and less burdensome when supported by well-defined access control policies and adherence to recognized security standards. To help strengthen your process, we’ve outlined four best practices that can significantly enhance your organization’s user access reviews.
- Leverage RBAC and policy automation
Role-Based Access Control (RBAC) streamlines access management by assigning permissions to roles rather than to individual user accounts. Each role represents the access required for specific job functions, and users inherit permissions based on their assigned role. This not only reduces complexity but also accelerates user access reviews, allowing organizations to validate roles instead of checking individual profiles.
To implement effectively:
- Map user access rights to job functions by reviewing job descriptions and responsibilities.
- Define roles that reflect these functions and assign appropriate permissions.
- Use policy automation tools to ensure roles remain updated as responsibilities evolve.
-
Involve business unit leaders
Department heads and business unit leaders play a critical role in validating employee access rights. Since they have direct insight into daily operations and job requirements, they are best positioned to assess what level of access is truly necessary. Their involvement not only enforces the Principle of Least Privilege (PoLP) but also helps prevent unnecessary or excessive access that could introduce security risks. Collaborating with these leaders ensures access rights are aligned with actual responsibilities, strengthening both operational efficiency and security. -
Schedule periodic access reviews
Keeping access reviews consistent and timely is essential for maintaining strong security standards. As part of your access management policy, establish a formalized user access review (UAR) procedure that:
- Defines a clear review schedule
- Assigns security officers responsible for conducting reviews
- Outlines how and when employees will be notified
- Specifies reporting timelines and required report details
In addition, align UARs with your organization’s operational calendar. For example, reviews can be scheduled after major business cycles (such as year-end financial closures) when systems are more stable and staff availability is higher. At the same time, avoid peak activity periods, like end-of-quarter sales or holiday seasons, to minimize disruption. Formalizing both the schedule and timing ensures UARs remain efficient, consistent, and non-intrusive.
- Integrate access tools with HR systems
To streamline user access reviews, organizations should adopt automation tools that not only collect and analyze access data but also integrate seamlessly with existing infrastructure, such as HR systems, Active Directory/LDAP, and cloud services. These integrations allow user roles and permissions to be automatically updated in response to HR events like onboarding, promotions, role changes, or terminations.
An effective platform should:
- Support end-to-end management of the user access lifecycle, covering provisioning, review, modification, and documentation
- Scale with organizational growth and adapt to increasing complexity in access rights
- Ensure accuracy by minimizing manual intervention and reducing the risk of outdated or unnecessary privileges
This alignment between HR systems and access management tools ensures that access rights remain consistent with real-time organizational changes, enhancing both efficiency and security.
Overcoming Common Access Review Challenges
User access reviews often stumble on hidden roadblocks, manual delays, complex IT environments, and weak HR integrations. Tackling these challenges head-on is essential to keep reviews accurate, efficient, and audit-ready.
Manual review delays
Conducting user access reviews manually is often time-consuming and resource-intensive. The process typically starts with gathering and consolidating access data from multiple systems and applications, each with its tools, interfaces, and complexities. Beyond data collection, reviewers must also have a deep understanding of organizational workflows and the security implications tied to each permission. This makes verifying whether access rights are appropriate for every user a painstaking and error-prone task.
How to address this challenge:
- Leverage automation tools to accelerate data collection, analysis, and reporting
- Adopt access management platforms that provide real-time visibility into permissions across systems
- Implement role-based access control (RBAC) to align access rights with job roles and reduce complexity
- Automate policy enforcement to eliminate bottlenecks and minimize human error
By reducing reliance on manual checks, organizations can shorten review cycles, improve accuracy, and strengthen overall security posture.
Complex IT environments
Most organizations today operate across a hybrid landscape of cloud services, on-premise infrastructure, and third-party applications. While this flexibility supports business needs, it creates major challenges for user access reviews. Each platform comes with its management interface, security protocol, and integration requirements, making it difficult to maintain a single, consistent view of user access rights. The situation becomes even more complex when dealing with custom-built applications, which often require specialized expertise to manage permissions effectively.
How to overcome these challenges:
- Adopt a centralized access management platform that unifies visibility across cloud, on-premise, and third-party systems
- Implement Identity and Access Management (IAM) solutions with automation to streamline user identity and permission management
- Leverage Security Information and Event Management (SIEM) tools to monitor access patterns, detect anomalies, and strengthen oversight
By consolidating access oversight in complex IT environments, organizations can reduce blind spots, simplify reviews, and enhance overall security posture.
Poor integration with HR systems
Without seamless integration between access review tools and HR platforms, organizations struggle to maintain accurate and current user access data. HR systems often manage the true source of identity like onboarding, role changes, and terminations, yet if these changes aren't synchronized, access controls quickly become outdated and risk-prone. For instance, manual data consolidation from HR to access review processes leads to time-consuming spreadsheet work and increased chances for error or delay.
Compliance Frameworks That Require Access Reviews
User access reviews are not only a cybersecurity best practice but also a mandatory requirement under several international compliance frameworks. These standards emphasize periodic reviews to enforce the principle of least privilege, protect sensitive data, and maintain audit readiness. Failure to comply can lead to heavy penalties, reputational damage, or loss of customer trust.
- NIST (SP 800-53, AC-1 & AC-2):
Requires organizations to perform periodic reviews of access rights and policies. Companies may define their review schedules, but must ensure access aligns with organizational policies. - PCI DSS (Requirement 7):
Applies to all entities that store, process, or transmit cardholder data, Requirement 7 mandates that access to cardholder data and related systems be restricted strictly to individuals whose job responsibilities require it. It further calls for granular access control, enforcement of the principle of least privilege, and periodic review of user roles. To meet this requirement effectively, organizations handling cardholder data must also adopt compliance tools that ensure ongoing monitoring and enforcement. - HIPAA (§164.308):
In the United States, this requirement applies to covered entities and business associates in the healthcare sector that handle citizens’ healthcare data. It mandates that access be granted only to authorized individuals or software programs with approved rights. Healthcare organizations must also periodically review, document, and update access rights, supported by regular audits of access records to ensure compliance with the HIPAA Privacy Rule, which safeguards medical records and other personal health information. Non-compliance may result in violations and audits by the US Department of Health and Human Services (HHS). - GDPR (Article 32):
The regulation applies to all organizations processing the personal data of EU residents, regardless of the organization’s location. It obligates such entities to regularly audit data access, covering both employees and third-party vendors. Access to personal data must also be limited to authorized personnel whose job responsibilities require it, in line with the principle of least privilege. Failure to comply with these requirements can expose organizations to significant penalties and steep fines. - ISO/IEC 27001 (Annex A.5):
Calls for scheduled access reviews as part of an ISMS framework, with privileged accounts requiring more frequent reviews than standard users. - SOX (Section 404):
The Sarbanes-Oxley Act (SOX) applies to all public companies in the United States, as well as international companies with registered equity or debt securities under the Securities and Exchange Commission (SEC). It requires financial organizations to enforce strict access control procedures and undergo annual audits by independent auditors. SOX further mandates that both management and auditors establish and verify controls over access to financial systems and data privacy. To support the integrity of financial reporting, organizations rely on regular User Access Reviews (UARs) to ensure that only authorized individuals can access sensitive financial information. Specialized compliance software is often adopted to help meet these standards effectively. - SOC 2 (CC 6):
SOC 2 (Common Criteria 6) is designed to protect the confidentiality and integrity of data handled by service organizations, particularly those managing sensitive customer information. It applies broadly to organizations across the globe that provide cloud-based services, IT systems, or data processing for clients. The framework mandates strong access control mechanisms, regular monitoring, and periodic user access reviews (UARs) to ensure that only authorized personnel can access critical systems. By enforcing the principle of least privilege and strict accountability measures, SOC 2 (CC 6) helps organizations maintain compliance and build trust with clients worldwide.
By aligning with these frameworks, organizations can strengthen security, streamline compliance efforts, and reduce the risks of financial or reputational losses.
Final Thoughts
A user access review policy is no longer optional; it’s a critical safeguard against privilege creep, insider threats, and compliance failures. By embedding structured reviews into your identity governance strategy, you not only reduce risks but also build a culture of accountability, audit readiness, and proactive security.
At Tech Prescient, we partner with organizations to design and implement scalable access review processes that align with regulatory frameworks, business operations, and Zero Trust principles. From automating review cycles to integrating with HR and IAM systems, we help ensure that only the right people have the right access, at the right time.
Take control of access before it controls you. See how Tech Prescient can help streamline your user access reviews:
Frequently Asked Questions (FAQs)
1. What is the user access review process?
The user access review process is a structured procedure that verifies whether each user’s access rights align with their current job responsibilities. By comparing permissions against role requirements, organizations can spot excessive or outdated privileges and adjust them accordingly. This ensures both security and compliance remain intact.2. How often should user access reviews be conducted?
The frequency of reviews often depends on the sensitivity of systems. Critical systems are usually reviewed quarterly to minimize risk, while less sensitive applications may be reviewed annually. Regular scheduling helps maintain least privilege and prevents privilege creep over time.3. What regulations require access reviews?
Several compliance frameworks mandate user access reviews to safeguard sensitive data. Regulations such as GDPR, HIPAA, SOX, ISO 27001, and PCI DSS all require organizations to periodically verify access rights. Meeting these requirements not only protects data but also helps ensure audit readiness.4. How do you automate a user access review?
Automation is typically achieved through Identity Governance and Administration (IGA) or Identity and Access Management (IAM) tools. These platforms streamline reporting, automate certification workflows, and provide dashboards to track approvals and revocations. This reduces manual effort and makes reviews more scalable.5. What is the principle of least privilege?
The principle of least privilege means granting users only the minimum level of access required to perform their job functions. By limiting permissions in this way, organizations reduce the attack surface and minimize the risk of insider threats or accidental misuse of data.