What Is Identity Governance and Administration (IGA)? Definition, Features & Examples
Identity Governance and Administration (IGA) helps in managing digital identities and their access rights across systems.
Last Updated date: April 6, 2026
Identity Governance and Administration (IGA) is a cybersecurity framework that ensures the right users have the right level of access to the right systems, applications, and data, at the right time and for the right reasons. It governs how digital identities are created, managed, reviewed, and removed across an organization to maintain security, compliance, and least-privilege access.
IGA provides centralized visibility into user identities and access rights, enabling organizations to define access policies, automate provisioning and deprovisioning, conduct access reviews, and meet regulatory requirements. By continuously governing access, IGA reduces security risk, prevents misuse, and simplifies audits while supporting day-to-day business operations.

Why Organizations Need IGA
Modern organizations manage thousands of users, applications, cloud services, and data repositories. Without proper identity governance, this complexity leads to access sprawl, security gaps, audit failures, and unmanaged risk. Identity Governance and Administration provides the structure needed to control access at scale.
By implementing IGA, organizations gain centralized oversight of identities, automate access decisions, and enforce consistent security and compliance policies across on-premises and cloud environments. This ensures access remains secure, auditable, and aligned with business needs as the organization grows.
Identity Governance and Administration (IGA) provides this level of control and oversight
- Enhances Security & Reduces Risk
IGA identifies and removes excessive, unused, or unauthorized access before it can be exploited. By continuously monitoring identity behaviour and access patterns, it reduces the risk of insider threats, credential misuse, and privilege creep. - Regulatory Compliances
IGA enforces access policies and maintains detailed audit trails required for regulations such as GDPR, HIPAA, SOX, and ISO standards. Automated access certifications and reporting simplify audits and help organizations meet compliance requirements consistently. - Improves Operational Efficiency
By automating provisioning, deprovisioning, and access requests, IGA reduces manual IT effort while ensuring access remains policy-driven. This improves efficiency without compromising security or governance. - Enabling Business Productivity
IGA delivers fast, role-based access to critical systems while maintaining governance controls. Users get timely access to what they need, helping them stay productive without increasing security risk. - Reduces insider threats
With real-time visibility, risk analytics, and orphaned account detection, IGA proactively reduces insider threats by identifying and revoking unnecessary or risky access before it leads to a breach.

Features of an Efficient IGA Solution
A modern Identity Governance and Administration solution combines visibility, automation, and policy enforcement to govern identities across their entire lifecycle. Below are the core capabilities organizations should expect from an enterprise-grade IGA platform.
-
Integration of Connectors for Identity Management
IGA platforms use pre-built connectors to integrate with directories, HR systems, and applications across on-premises and cloud environments. These integrations unify identity data, keep access permissions synchronized, and ensure access decisions are based on accurate, up-to-date information. -
Automated Access Request Workflows
With the help of automated workflows, users can request access to any resource or application, and managers have the right to approve or deny access based on pre-defined roles and policies. All of this streamlines the identity administration processes while ensuring enforcement of access management rules. -
Provisioning and De-Provisioning
IGA automates access provisioning and deprovisioning across the user lifecycle, from onboarding through role changes to offboarding. Access is updated in real time as roles change, and all activity is logged to support governance and compliance. -
Entitlement Management
Entitlement management defines what actions users can perform within systems and applications. IGA ensures these permissions are aligned with role, policy, and risk, helping organizations enforce least-privilege access and reduce exposure. -
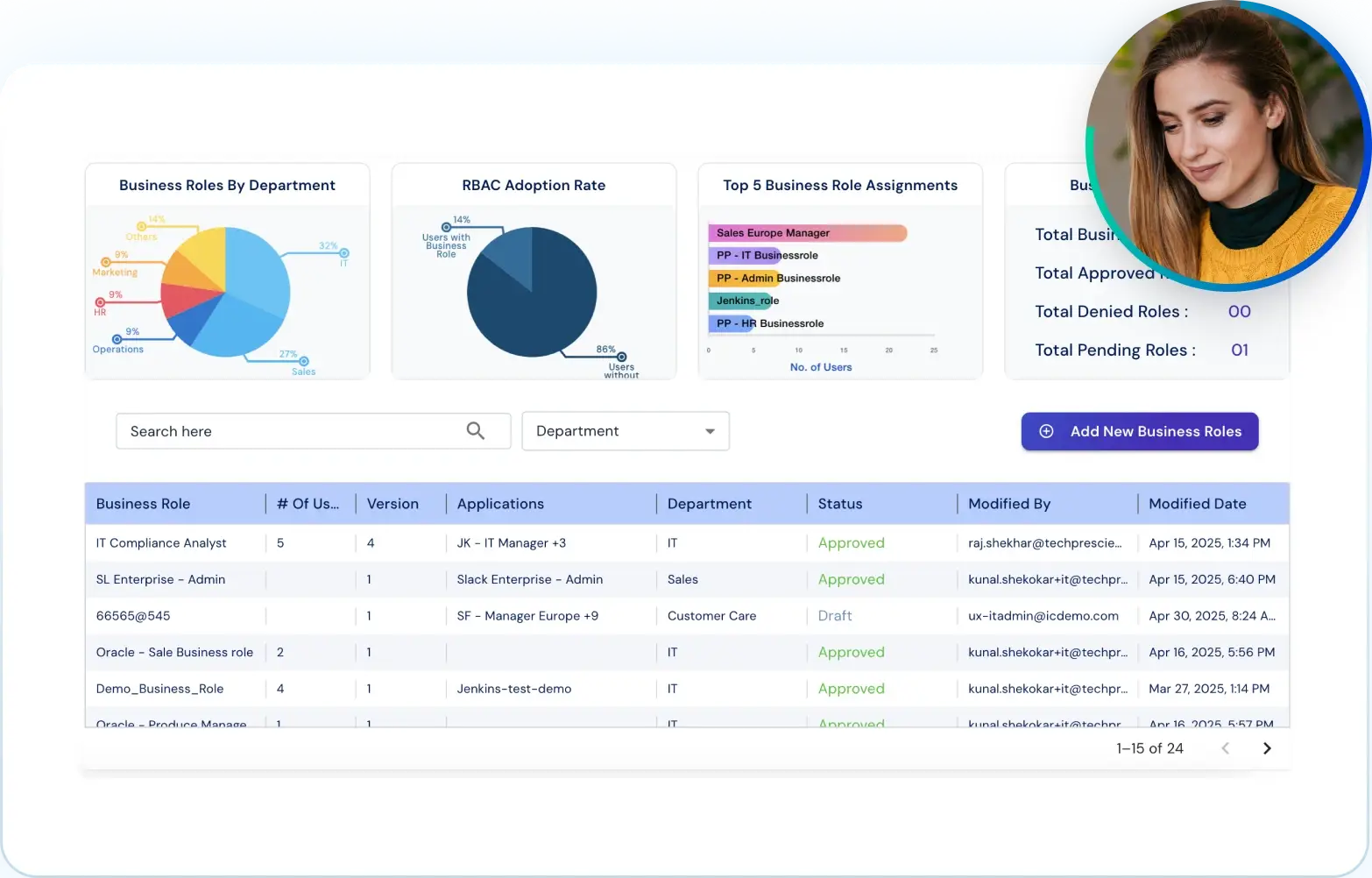
Role-Based Access Control (RBAC)
In Role-Based Access Control, the user access is restricted based on job responsibilities or job roles and only has access to the permissions attached to the same. During onboarding, IGA automatically assigns access based on the user’s role and responsibilities. This ensures least privilege access and enhances security. -
Access Review and Certification
IGA platforms provide regular access reviews and access certification campaigns, enabling organizations to validate whether users still require access to particular resources. This supports both regulatory compliance efforts and internal policy enforcement. -
Segregation of Duties (SoD) Controls
To reduce risk and prevent fraud, Identity Governance enforces Segregation of Duties by ensuring that no single user has conflicting access rights, such as the ability to initiate and approve transactions. SoD policies are critical for maintaining compliance and strengthening internal security controls. -
Analytics and Reporting
Real-time analytics and reporting capabilities allow security teams to monitor user identity activities, detect anomalies, and generate detailed audit logs. These insights support risk detection, investigation, and audit requirements.
Planning to implement IGA?
This checklist helps you move from pilot to production without access sprawl or audit gaps.
How Identity Governance and Administration (IGA) Integrates with Existing Security Systems
Identity Governance and Administration does not replace existing security tools; it strengthens them. IGA acts as the governance layer that connects authentication systems, directories, applications, and security platforms to ensure access is controlled, monitored, and compliant across the entire IT ecosystem.
Step 1: Authentication Systems
IGA works hand-in-hand with tools like:
- Single Sign-On (SSO) – so users log in once and access many systems
- Multi-Factor Authentication (MFA) - for extra identity checks
- Identity Providers (IdPs) – like Okta or Azure AD that handle login credentials
This connection ensures access isn’t just fast, but secure and policy-driven.
Step 2: Directory Services (e.g., Active Directory)
IGA connects with directory services like LDAP, Active Directory, and Azure AD to:
- Sync user accounts and groups
- Manage access rights centrally
- Keep permissions updated in real time
This helps keep user data and access consistent across all systems.
Step 3: Applications and Cloud Services
IGA platforms integrate with:
- SaaS apps like Salesforce, Google Workspace
- Cloud platforms like AWS, Azure (IaaS)
- Legacy systems via connectors (SCIM, APIs)
This enables centralized access management across both modern and legacy systems.
Step 4: IT Service Management (ITSM) Tools
IGA works with platforms like ServiceNow or Jira to:
- Automate access requests and approvals
- Trigger identity workflows (onboarding, offboarding)
- Track issues and incidents tied to identity access
This makes access part of the same process your IT team already uses.
Step 5: Mobile Device Management (MDM) & Endpoint Security
IGA checks if a user’s device is secure before granting access. For example:
- Is the phone encrypted?
- Does the laptop have an antivirus?
Access is granted only if both the user and the device are trusted.
Step 6: Privileged Access Management (PAM)
IGA teams up with PAM tools to handle high-risk access (like admin or root users). It helps:
- Approve and monitor privileged account usage
- Ensure such access is temporary and reviewed regularly
This keeps your most sensitive data and systems extra secure.
Step 7: SIEM (Security Information and Event Management)
IGA sends access logs and user activity data to SIEM platforms like Splunk or IBM QRadar. This helps:
- Detect risky behaviour in real-time
- Investigate unusual access patterns
- Prove compliance with audit logs
This provides deeper visibility and context into identity-related security events.
What’s the cost of manual identity governance?
Estimate the operational effort, audit impact, and savings of automating IGA across provisioning, reviews, and compliance.
IGA vs IAM: A Strategic Comparison
While Identity and Access Management (IAM) focuses on authentication and access, Identity Governance and Administration (IGA) ensures that access is appropriate, justified, and continuously governed over time.
| Aspect | Identity Governance and Administration (IGA) | Identity and Access Management (IAM) |
|---|---|---|
| 1 | Delivers end-to-end control over the identity lifecycle, from onboarding to deprovisioning, with governance at its core. | Focuses on basic identity creation and access control, primarily for authentication and authorization. |
| 2 | Ensures that access is appropriate, auditable, and aligned with business policies through access reviews, policy enforcement, and risk-based controls. | Authenticates users and grants access based on predefined roles or credentials, without ongoing governance. |
| 3 | Provides automation for provisioning, deprovisioning, access reviews, and compliance reporting, reducing manual workload and audit effort. | Automates login and access permissions, but lacks full lifecycle oversight and compliance tooling. |
| 4 | Built to meet compliance and regulatory requirements by maintaining detailed access logs, SoD policies, and certification workflows. | Helps meet basic access control needs, but relies on external tools for audit and compliance support. |
| 5 | Integrates across your IT ecosystem, unifying HR systems, apps, directories, cloud platforms, and security tools for contextual access governance. | Primarily integrates with authentication systems, focusing on validating identity at the point of access. |
| 6 | Reduces insider threats and policy violations by enforcing least-privilege access and continuously monitoring user access behavior. | Lacks deep governance visibility, often unable to track or revoke outdated or risky permissions. |
Discover Enterprise-Grade Identity Governance with Tech Prescient
As identity becomes the new security perimeter, organizations need automated and policy-driven governance. Tech Prescient helps enterprises reduce access risk, simplify compliance, and scale Identity Governance and Administration across cloud and hybrid environments.
FAQs
Identity Governance and Administration is a framework that manages digital identities and governs access to systems, applications, and data to ensure security, compliance, and least-privilege access.
IGA stands for Identity Governance and Administration. In cybersecurity, it ensures access is appropriate, auditable, and aligned with business and regulatory requirements.
IGA complements IAM by adding governance controls such as access reviews, policy enforcement, and compliance reporting on top of authentication and access management.
IGA supports compliance by enforcing access policies, maintaining audit trails, and enabling access certifications required by regulations such as GDPR, HIPAA, and SOX.
Provisioning assigns access based on roles or policies, while deprovisioning removes access when it is no longer required. Both processes are automated in IGA to reduce risk and errors.