Identity Confluence
Identity Lifecycle Management
Identity Lifecycle Management Built for Unified Identity Security
Automatically manage access through HR-driven lifecycle workflows, granting precise access when needed and removing it immediately upon exit.
Trusted by



Access Drift Causes Over-Provisioning & Compliance Gaps
Manual identity lifecycle processes cause delays and a lack of visibility, resulting in access drift, over-provisioning, and orphaned accounts that increase audit deficiencies and security risk.
See It in Action →
From Lifecycle Automation to Intelligent Identity Governance
Trigger identity changes from authoritative HR systems in real time.
Deliver precise birthright access aligned to role-based policies.
Ensure entitlements stay accurate as user roles and attributes change.
Automatically revoke access when employment ends or role changes occur.
Maintain continuous alignment between identities, permissions, and policy.
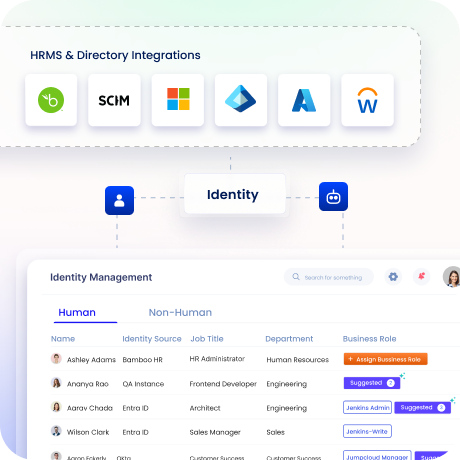
End-to-End Identity Lifecycle Governance
Streamline the Entire JML Lifecycle
Manage identity lifecycle events from a centralized dashboard connected to HR & directories.
Administer role changes for Human Identities & provision/de-provision of Non-Human Identities.
Continuously validate access with automated certifications to keep permissions aligned to roles.
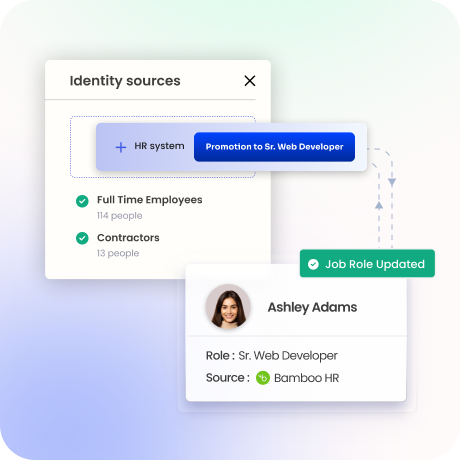
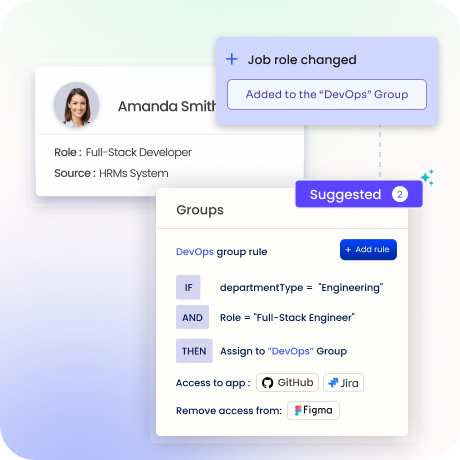
Keep Access in Sync with Every HR Change
Trigger real-time access updates from integrated HR systems in a centralized framework.
Automation of permissions that are aligned for role updates & organizational changes.
Align HR attributes with identity and system accounts for consistent control.
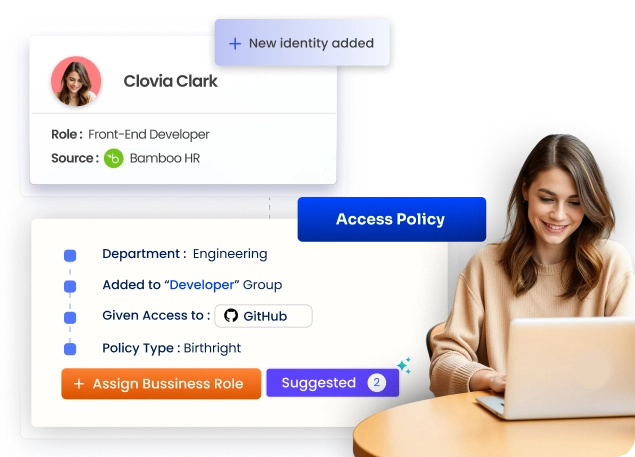
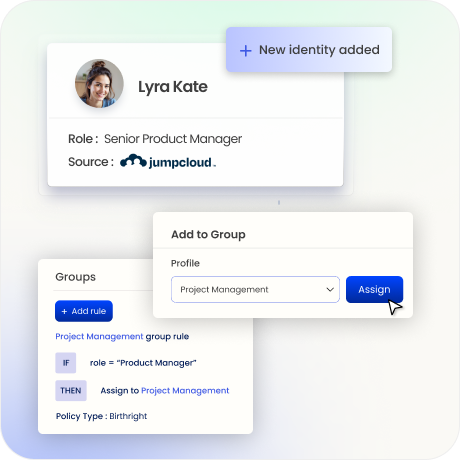
Grant the Right Access from Day One
Establish baseline access using role, department & policy rules in a unified framework.
Grant appropriate permissions at onboarding, supported by built-in controls such as MFA and SSO.
Prevent SoD conflicts and sensitive access risks before access is provisioned.
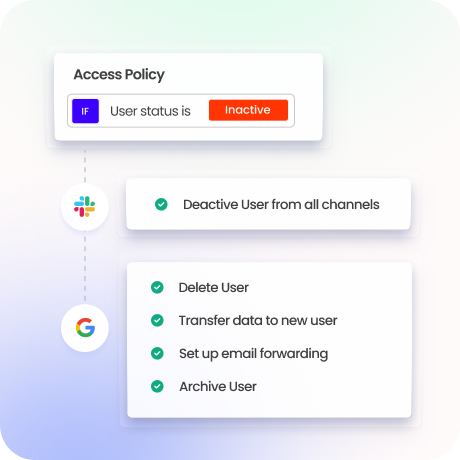
Remove Access the Moment Risk Appears
Revoke access across systems from a unified control layer when roles change or end.
Remove residual permissions to eliminate orphaned accounts and reduce exposure risk.
Track and verify every revocation with closed-loop remediation for full auditability.
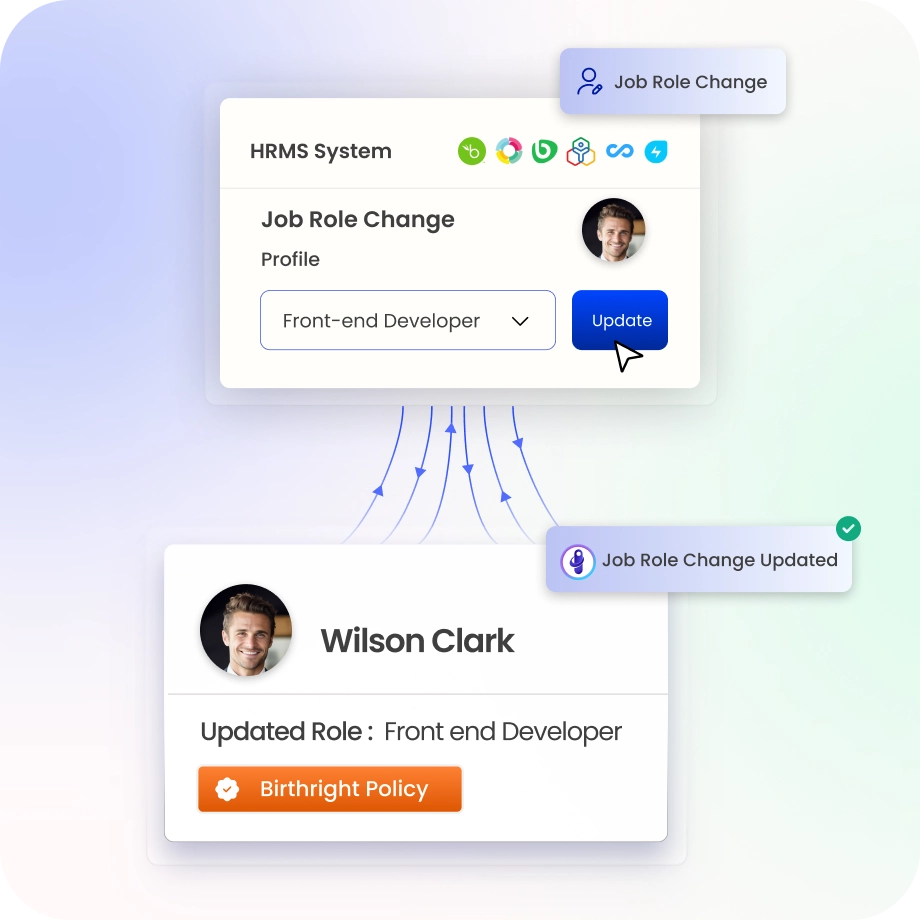
Adapt Access as Roles and Risks Evolve
Continuously adjust access by role and policy conditions in a centralized AI-powered platform.
Adapt permissions as users move across teams and responsibilities without operational friction.
Apply risk-aware intelligence to prioritize high-risk entitlements and privileged access.
Stay Audit-Ready with Continuous Visibility
Maintain centralized visibility across SaaS, cloud, and on-prem systems.
Identify access drift, entitlement mismatch and dormant accounts in real time.
Create audit-ready reports aligned with SOX, SOC 2, ISO 27001, HIPAA through Identity Confluence’s Evidence Center.

Drive measurable value with Identity Confluence
Calculate Your ROI
100%
Reduction in identity risk
90%
Faster access to investigations
3-5x
ROI
within 12 months
Why Teams Choose Identity Confluence
1.
Continuous Identity Governance
Enforce Zero Trust continuously, not periodically. Lifecycle controls, reviews, and policy enforcement run in real time.

2.
Unified Human and Machine Coverage
Govern workforce, contractor, and non-human identities on one platform, closing machine identity gaps in Zero Trust.

3.
No Bolt-Ons Required
Deliver least privilege, SoD enforcement, lifecycle automation, and NHI governance natively without multiple tools or add-ons.




