Maintain Audit-Ready Identity Governance Every Day
Most teams prepare for audits. The ones that pass them consistently never stopped being ready. Continuously enforce policy, certify access, and generate evidence automatically.
Trusted by



Periodic Reviews Leave Gaps Auditors Find First
Quarterly reviews burn weeks, produce rubber-stamp approvals, and miss privilege creep between cycles. By the time the next audit starts, the gaps have already been there for months.
See How We Fix This →

Compliance That Runs Continuously, Not Quarterly
Run automated certifications on event and schedule-based triggers.
Detect SoD violations and access drift through continuous policy evaluation.
Generate audit-ready evidence aligned to SOX, SOC 2, ISO 27001, HIPAA, GDPR, DPDPA, and NIST.
Govern employees, contractors, and non-human identities under unified policies.
Map every certification outcome to multiple compliance requirements at once.
Automate Every Layer of Identity Compliance
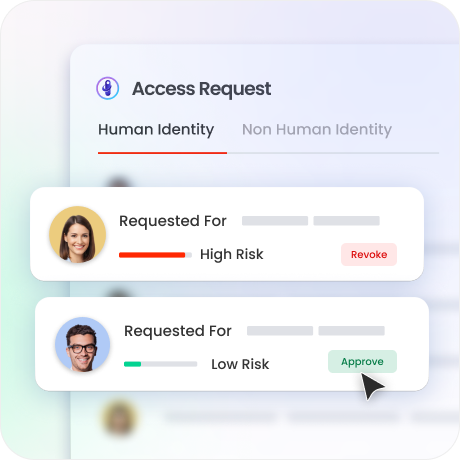
Risk-Based Access Certification
Launch recurring and event-driven certification campaigns across identities and apps.
Auto-approve low-risk access so reviewers focus on what actually matters.
Give managers risk scores, access source, and last-used dates per decision.
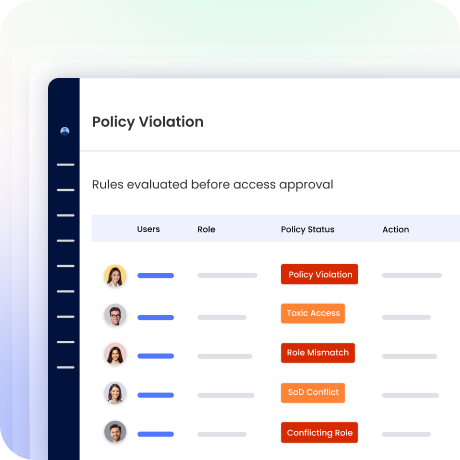
Policy Enforcement and SoD Controls
Evaluate SoD conflicts with pre-built and custom toxic access policy rules.
Detect privilege creep continuously through periodic and event-driven identity reconciliation.
Enforce birthright and compliance policies across cloud, on-prem, and hybrid environments.
Evidence Center and Audit Reporting
Generate pre-configured compliance reports with one-click export for auditors.
Maintain continuous audit trails for every access decision and lifecycle event, automatically maintained.
Centralise access logs, review records, and certification evidence in one place.

Identity Lifecycle Governance
Provision birthright access automatically the moment HR triggers onboarding.
Adjust entitlements instantly on role changes with policy-based rules.
Revoke all access on termination automatically. Zero orphaned accounts.

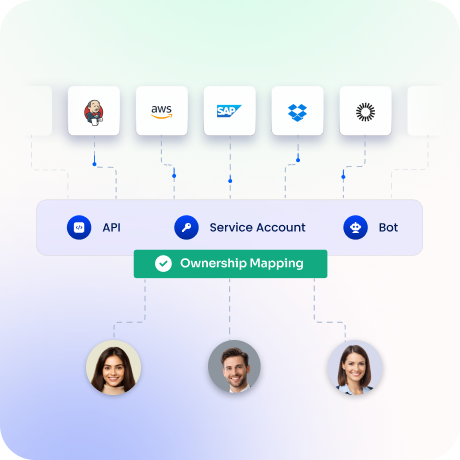
Non-Human Identity Governance
Auto-discover non-human identity from AWS, Azure, and GCP environments.
Map every NHI to an accountable owner and enforce credential rotation.
Run access reviews and governance workflows via JIRA, Zoho or any ticketing integration.
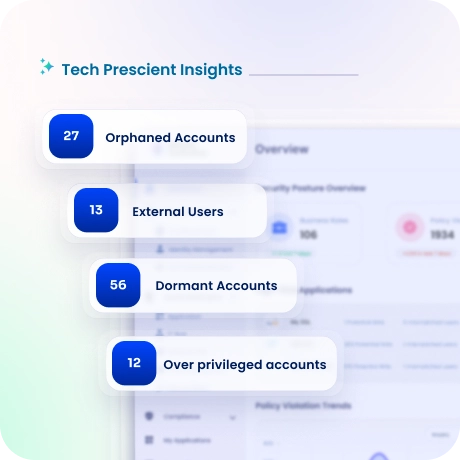
Identity Risk Intelligence
Score every identity using configurable risk models per application and environment.
Detect anomalous access patterns through near real-time analysis.
Stale and over-privileged access is flagged and routed for remediation.
Drive measurable value with Identity Confluence
Calculate Your ROI
24/7
Compliance Monitoring
90%
Faster Audit Readiness
3-5x
ROI
within 12 months
Why Teams Choose Identity Confluence
1.
Simplify compliance
One certification campaign maps to SOC 2, ISO 27001, SOX, HIPAA, GDPR, DPDPA, NIST, and more.

2.
Stay audit-ready
Policy enforcement, identity reconciliation, and evidence generation run continuously, so your compliance posture stays current between audits.

3.
Seamless integration
API-first architecture and 250+ pre-built connectors integrate Identity Confluence into your existing identity ecosystem without ripping out what works.



