Identity Confluence
SOD Enforcement
Eliminate Access Risks with Intelligent SoD Enforcement
SoD violations don't announce themselves. They accumulate quietly role by role, system by system, until an auditor or an attacker finds them first. Stop them before they form.
Trusted by



Conflicting Access Creates Unseen Compliance Gaps
Most SoD violations aren't the result of bad intent, they're the result of no visibility. Roles accumulate across siloed systems until someone holds access they should never have had simultaneously.
See It in Action →
Enforce SoD with Intelligent, Policy-Driven Controls
Enforce Segregation of Duties policies across every system and role
Detect and block conflicting access combinations before they're granted
Automate SoD checks across every identity lifecycle event automatically
Maintain continuous visibility into SoD risks and active violations
Remediate faster with intelligent workflows and contextual risk insights
Core SoD Enforcement Capabilities for Modern Identity Governance
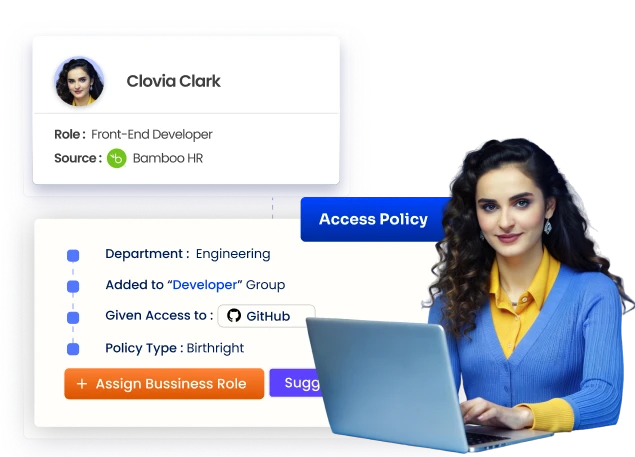
Prevent and Block Conflicting Access
Define SoD policies to identify incompatible roles and entitlements.
Block risky access combinations at provisioning, before they're granted.
Enforce preventive controls stop violations at the source.
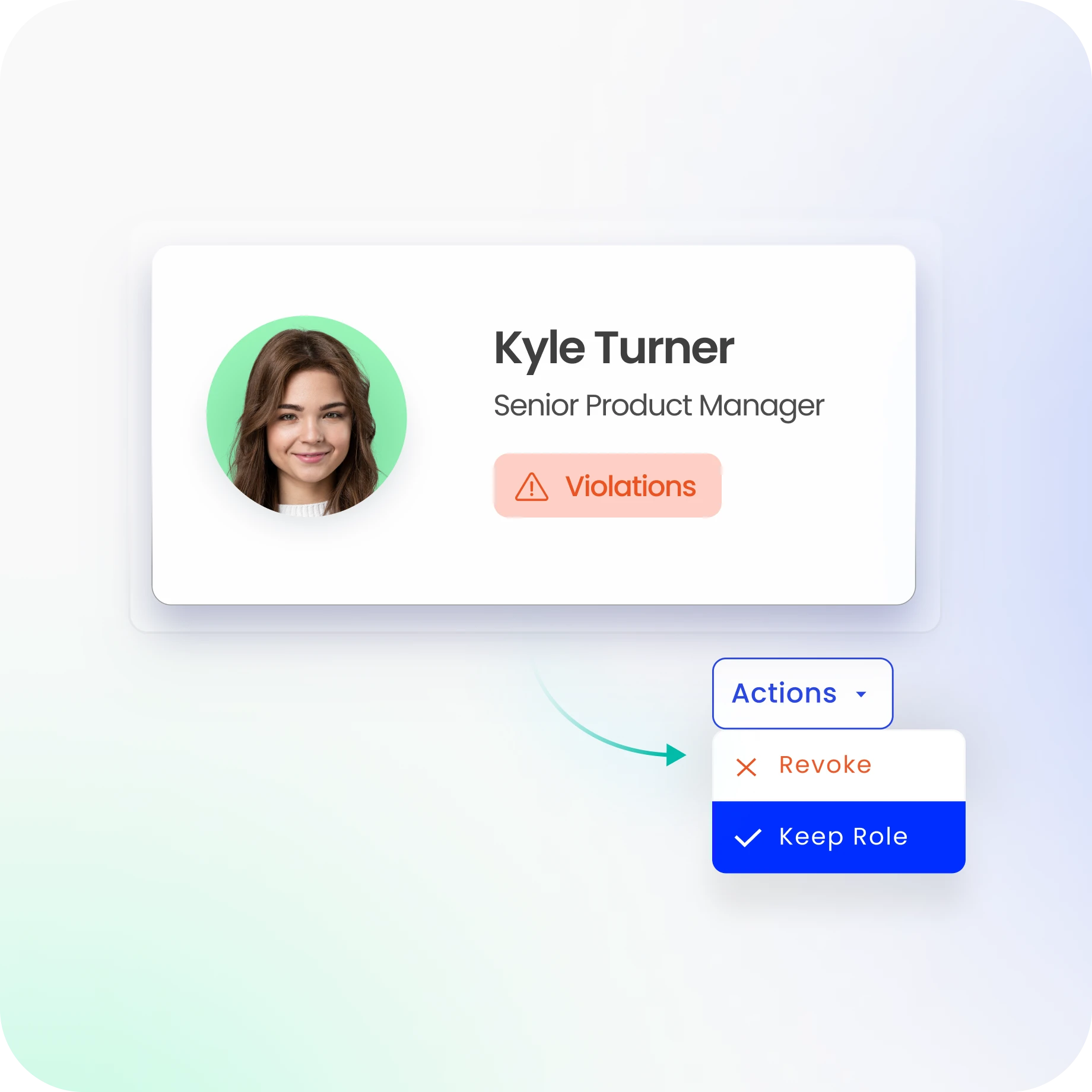
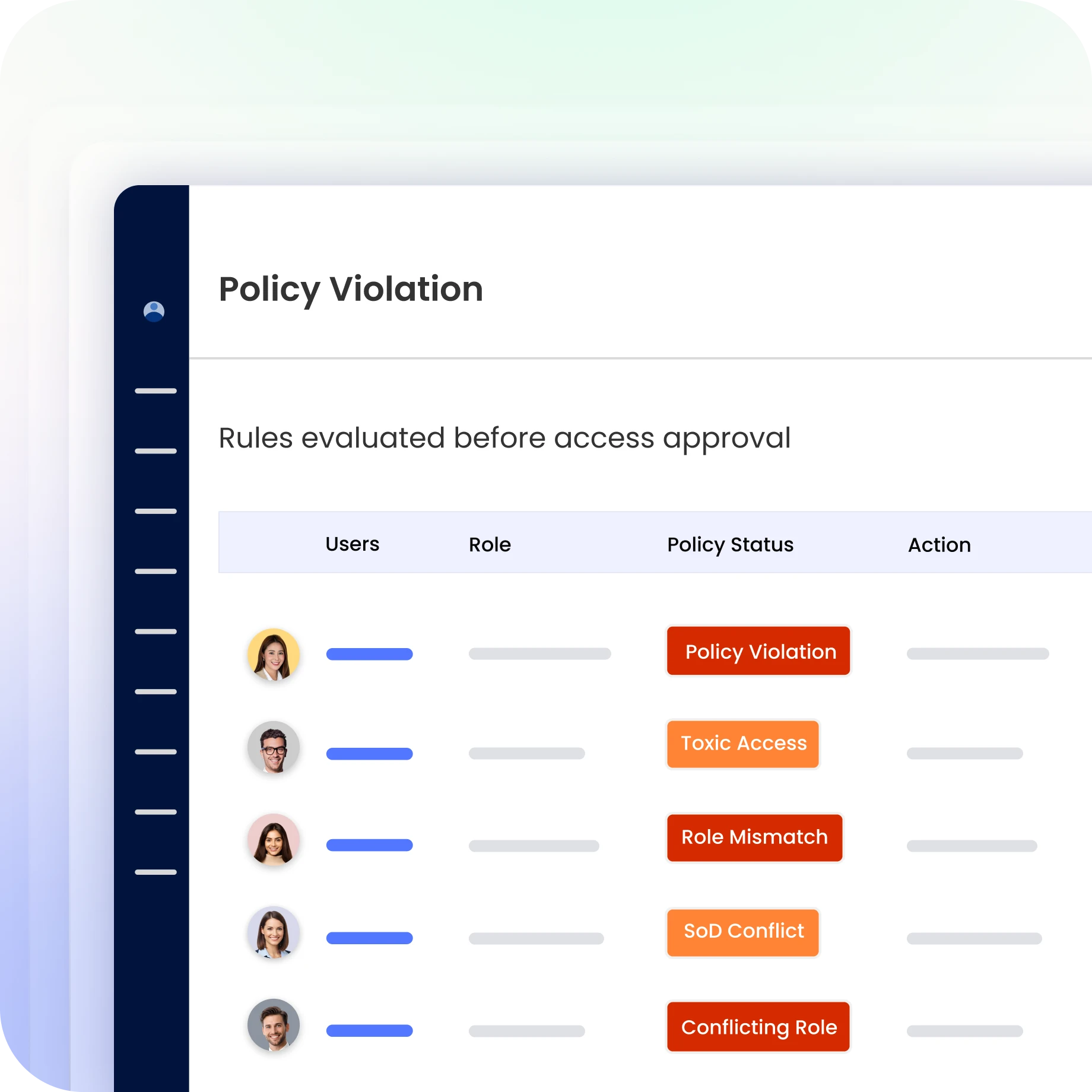
Detect, Prioritize, and Remediate Violations
Continuously monitor access across every connected system for SoD conflicts.
Identify and prioritise violations in real time using contextual risk insights.
Automated remediation workflows trigger the moment a conflict is confirmed.

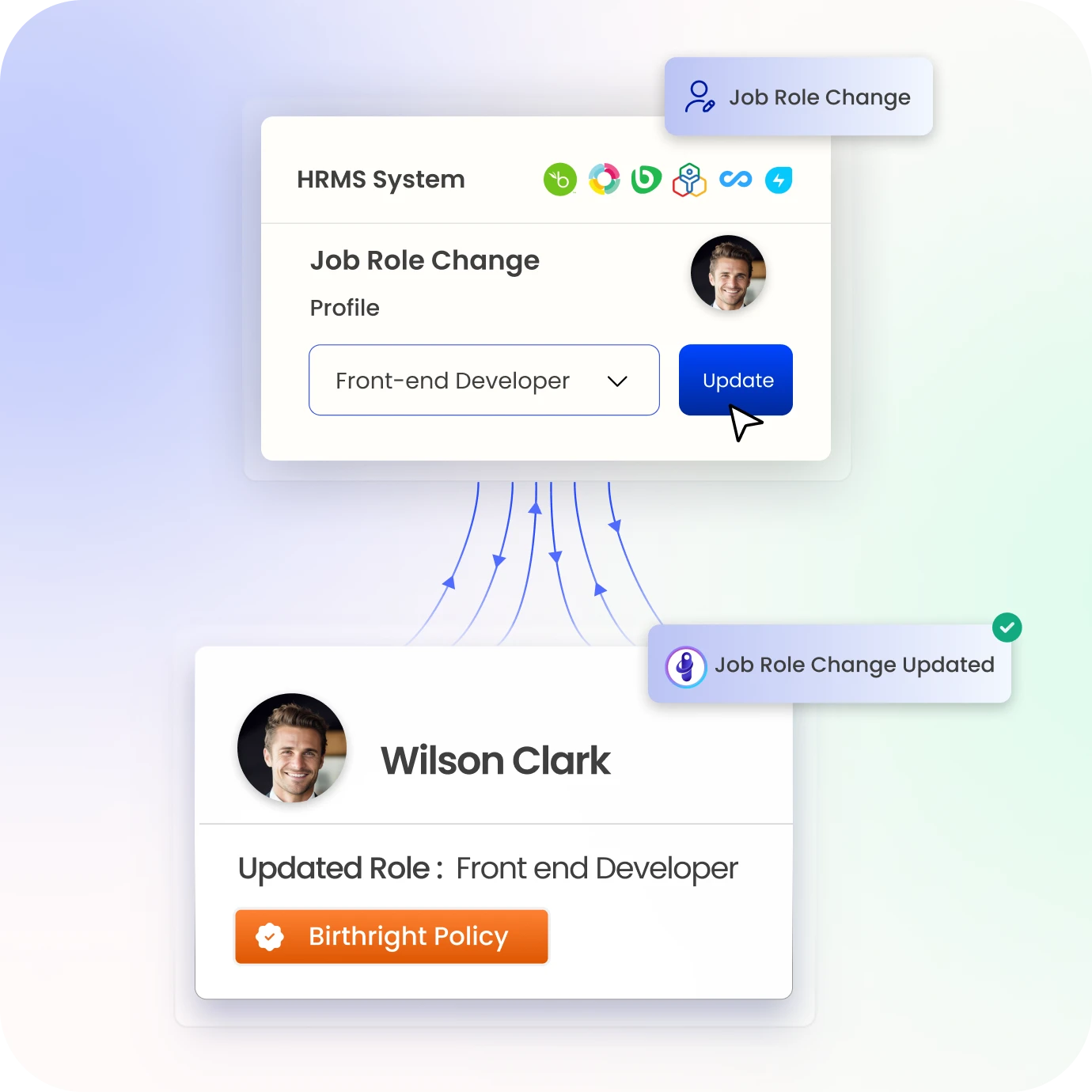
Embed SoD Across Identity Lifecycle
SoD checks run at onboarding, role changes, and offboarding.
Ensure access remains compliant as roles and entitlements evolve.
Integrate SoD enforcement seamlessly within lifecycle processes.
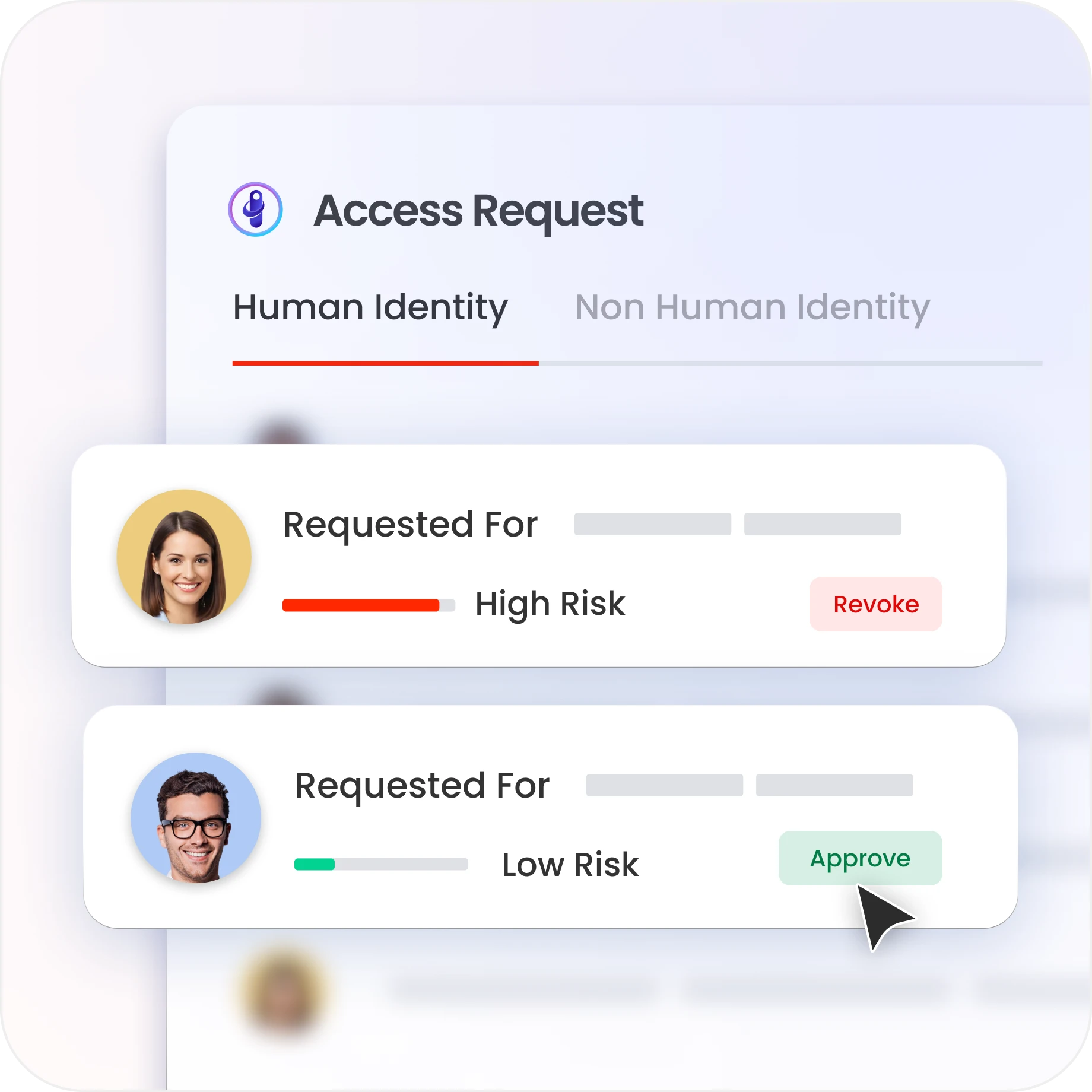
Govern Access Requests with SoD Controls
Every access request is validated against SoD policies before approval.
Prevent violations through automated approval workflows.
Embed policy-based approvals within access request workflows to enforce SoD in real time.
Strengthen Reviews and Audit Readiness
Highlight SoD conflicts during access reviews and certifications.
High-risk access combinations rise to the top of every review queue.
The Evidence Center centralises policy enforcement history, violation records, and remediation outcomes.

Centralize SoD Governance and Resolution
The Reconciliation Board surfaces active SoD conflicts, remediation status, and policy enforcement across every connected system in one view.
Consolidated insights across systems mean better governance decisions.

Drive measurable value with Identity Confluence
Download the ROI Report
90%
Fewer access violations
85%
Faster compliance reviews
3-5x
ROI
within 12 months
Why Teams Choose Identity Confluence
1.
Built for Proactive Risk Prevention
Most SoD tools detect violations after they've been active for months. Identity Confluence blocks them at provisioning, before a conflict is ever granted.

2.
Context-Aware Decision Intelligence
Pre-built toxic access combinations cover common SoD rules. Configurable policies cover the ones specific to your environment. Risk scoring and contextual insights prioritise what matters

3.
One platform across every system
SoD that covers only some apps isn’t real control, it leaves gaps. Identity Confluence enforces consistent policy across cloud, SaaS, on-prem, and hybrid from one layer.



