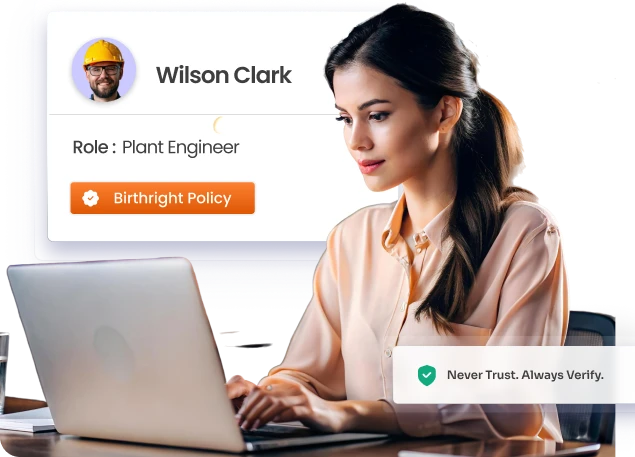
Enforce Zero Trust Across Every Identity in Your Enterpriset
Govern human & machine identities with continuous lifecycle controls, least privilege enforcement & risk-based access across cloud & on-prem systems.
Trusted by



Zero Trust Fails Without Identity Governance
Authentication gets you to the door. Identity governance controls what happens inside. Without it, verified users carry excessive access, machine identities go unreviewed, and blind spots become breach vectors.
See It in Action →
Make Identity Governance the Foundation of Zero Trust
Discover every human and machine identity and map their access
Enforce least privilege and remove excessive entitlements continuously
Automate identity lifecycle to eliminate standing access risk
Detect policy violations and high-risk access combinations in real time
Maintain continuous compliance with audit-ready evidence on demand
Six Controls That Make Zero Trust Actually Work
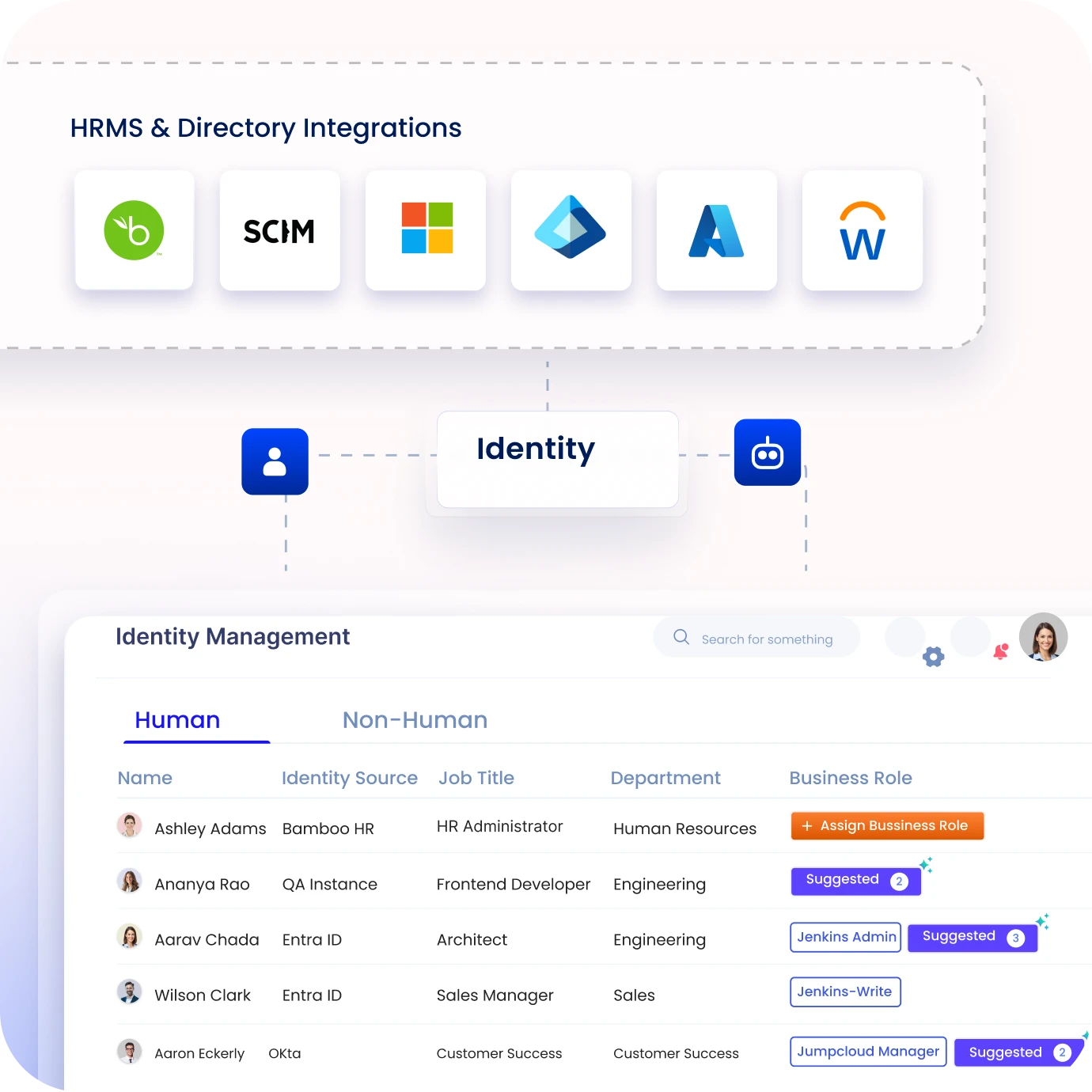
Unify Visibility Across Identities and Access
Build a complete inventory of human & machine identities across systems.
Map entitlements and privileges to surface hidden access risks early.
Correlate identity data via a universal sync framework to eliminate silos.
Enforce Least Privilege Across All Identities
Remove excessive access using role-based and policy-driven controls.
Enforce policies across cloud, SaaS, and on-prem environments.
Enable policy-based access requests with automated approvals to prevent risk.
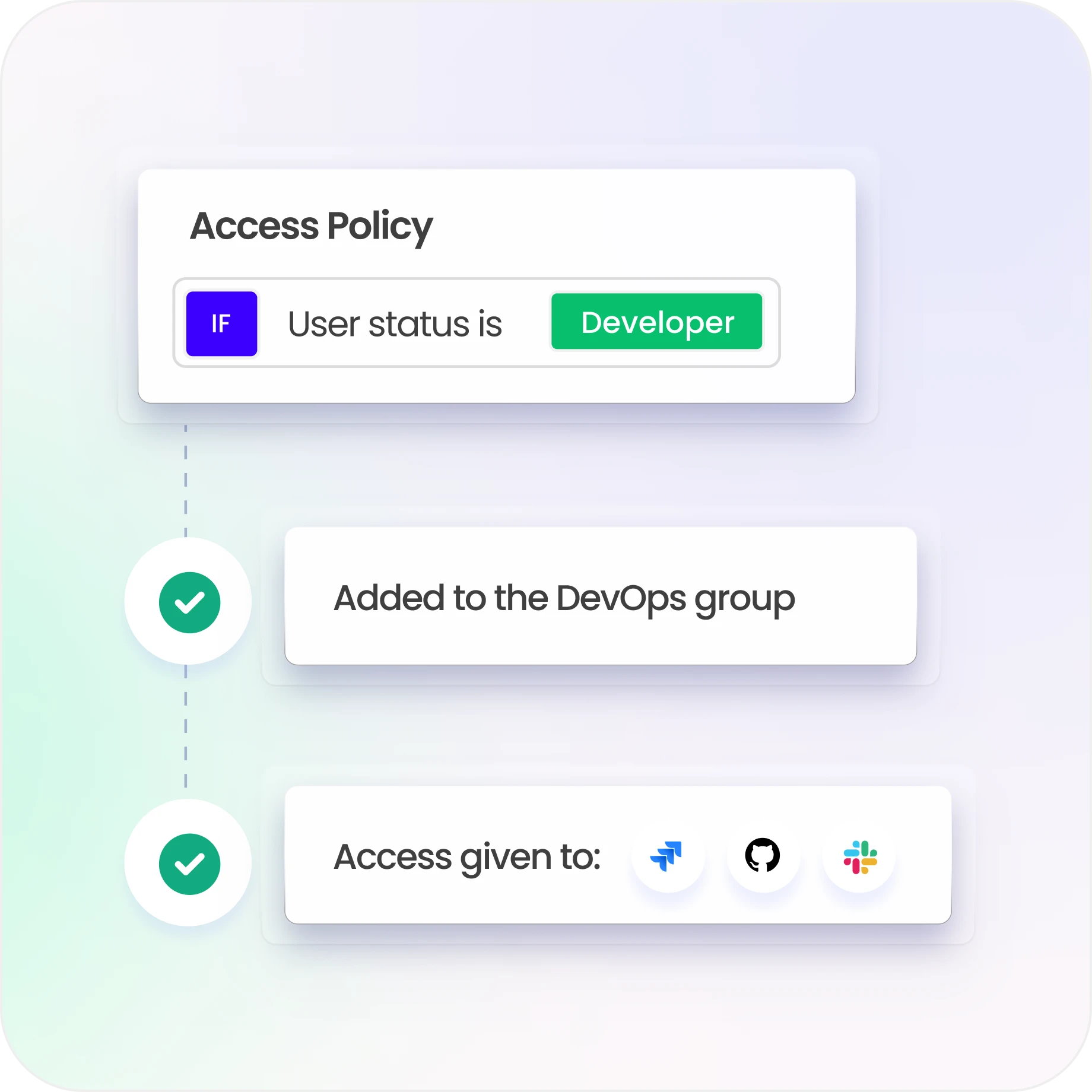
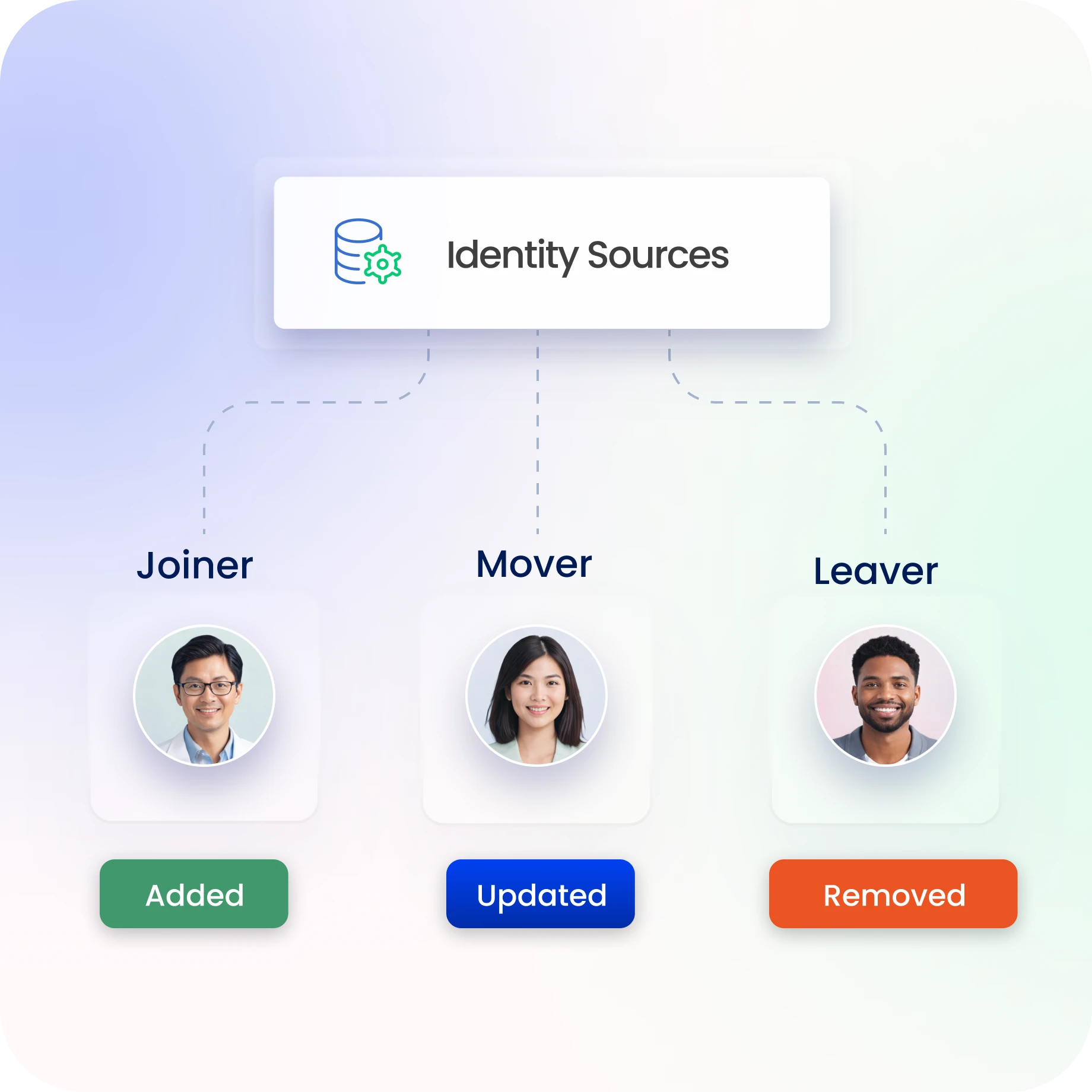
Automate Identity Lifecycle and Access Changes
Automate joiner, mover, and leaver workflows across all systems.
Revoke and update access instantly as roles change or users exit.
Use smart workflows and role models to standardize provisioning.
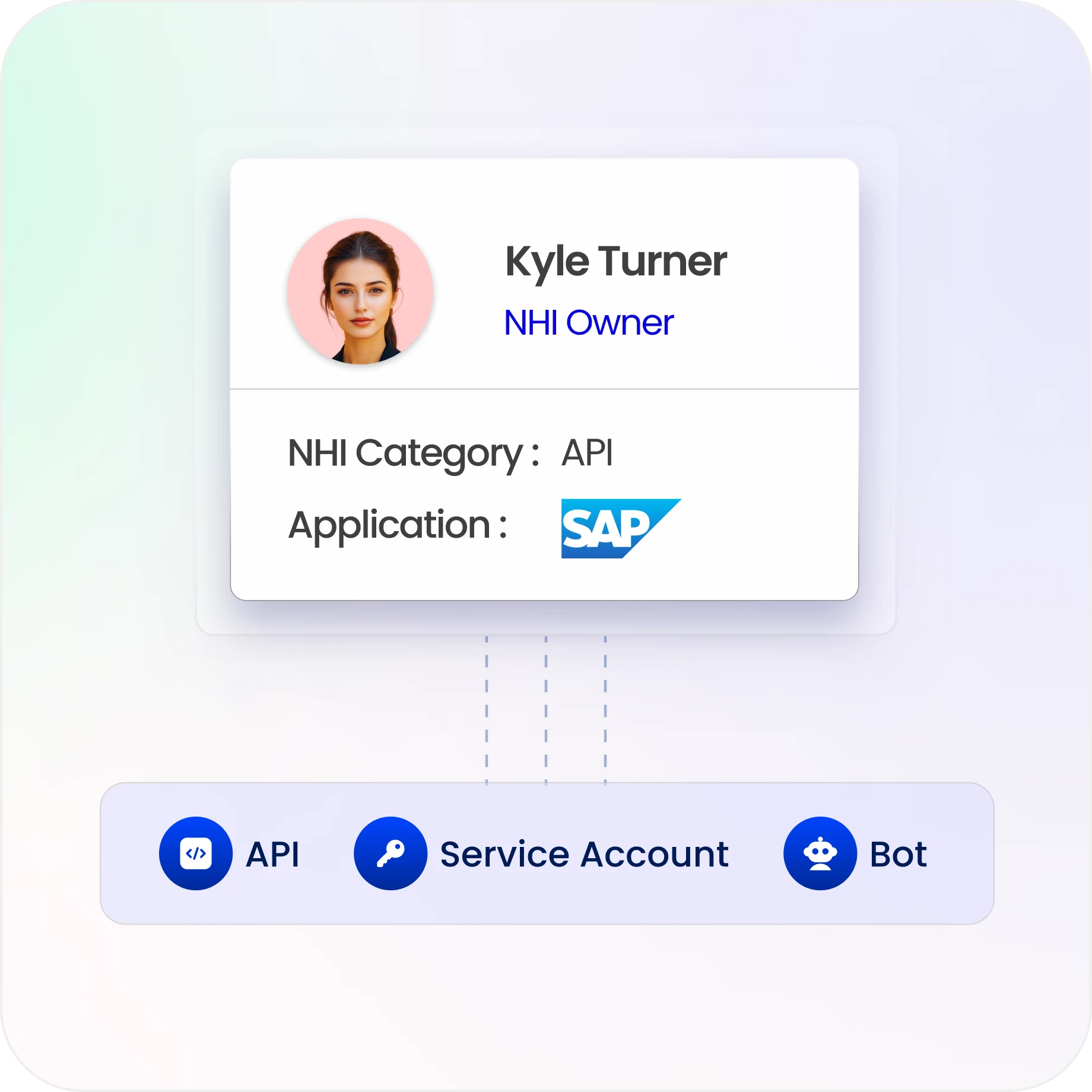
Govern and Secure Machine Identity Access
Discover and classify service accounts, APIs, bots, and credentials.
Assign ownership and enforce least privilege for non-human identities.
Apply lifecycle controls and policies to secure all machine identities.
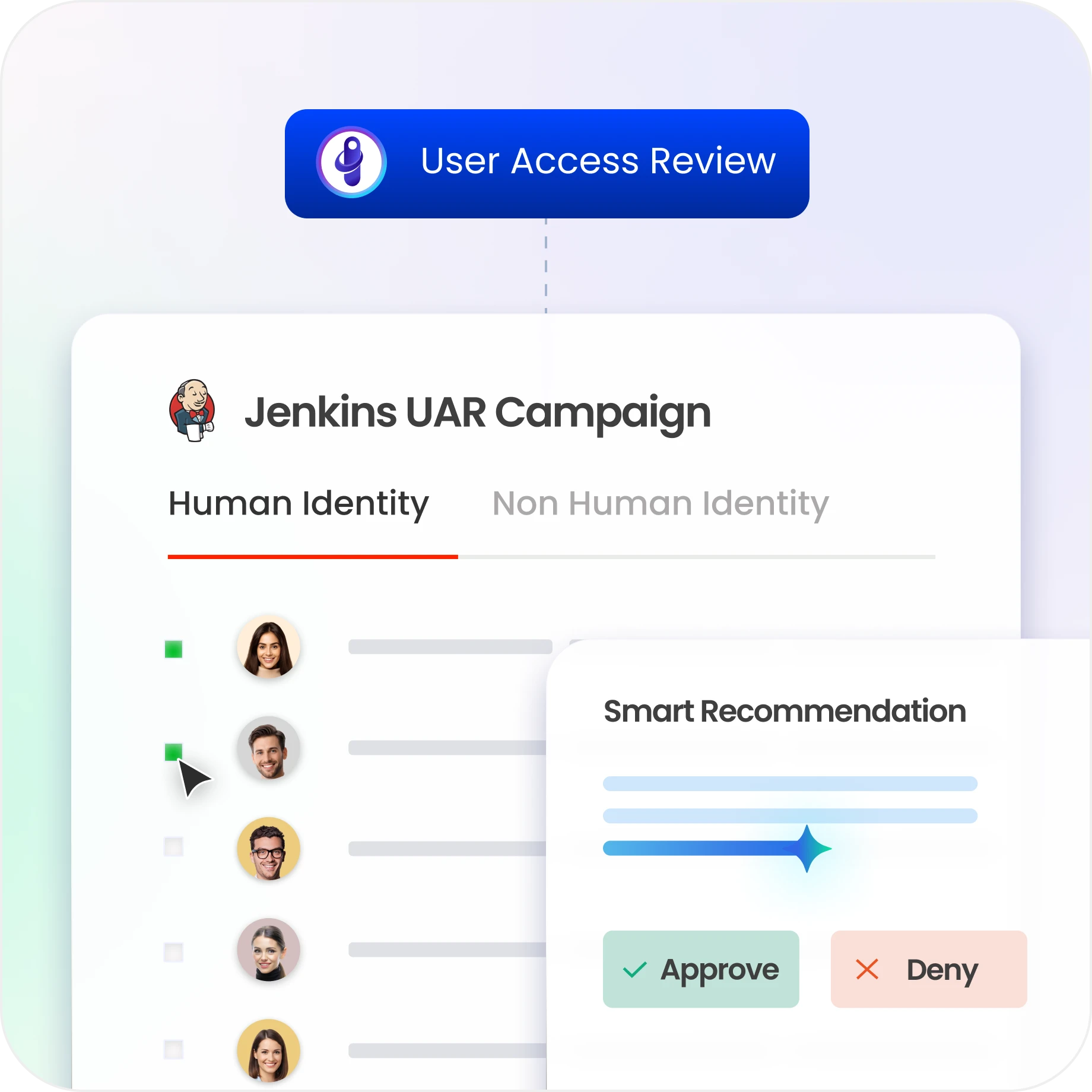
Enable Risk-Based Access Reviews and Certifications
Run reviews focused on high-risk access and toxic combinations.
Detect SoD violations and anomalous access patterns quickly.
Centralize reviews, reconciliation, and evidence for audit readiness.

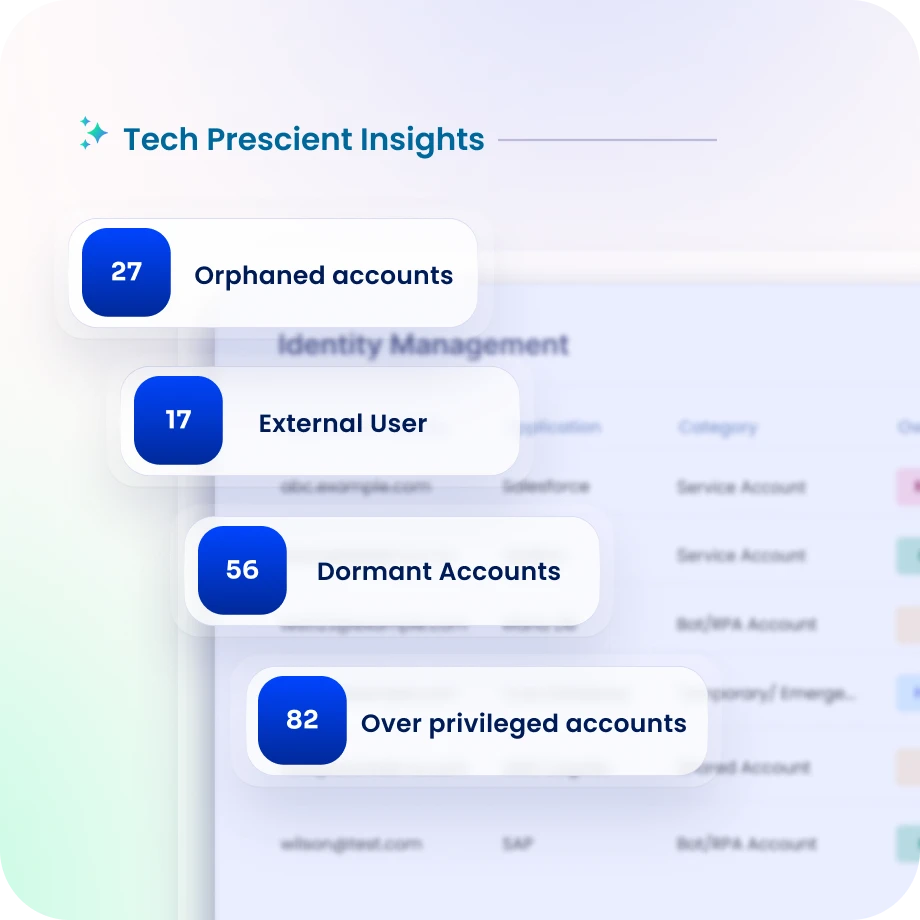
Continuously Monitor Identity Security Posturee
Assess identity risk across users, roles, and entitlements in real time.
Detect violations, misconfigurations, and abnormal access proactively.
Use ISPM with risk scoring to reduce identity attack surface continuously.
Drive measurable value with Identity Confluence
Download the ROI Report
96%
reduction in excess access risk
90%
faster access decisions
3-5x
ROI
within 12 months
Why Teams Choose Identity Confluence
1.
Continuous Identity Governance
Enforce Zero Trust continuously, not periodically. Lifecycle controls, reviews, and policy enforcement run in real time.

2.
Unified Human and Machine Coverage
Govern workforce, contractor, and non-human identities on one platform, closing machine identity gaps in Zero Trust.

3.
No Bolt-Ons Required
Deliver least privilege, SoD enforcement, lifecycle automation, and NHI governance natively without multiple tools or add-ons.



