Identity Confluence
Identity Security Posture Management
Identity Security Posture Management For Zero Blind Spots
One platform to continuously score, surface, and fix identity risk across IAM, IGA, PAM, cloud, SaaS, and every human and non-human identity in between.
Trusted by



Your Identity Tools Do Not Talk to Each Other
AM sees users. PAM sees privileges. IGA sees roles. None of them see your full posture, which means toxic access, MFA gaps, and orphaned accounts stay hidden until it is too late.
See It in Action →
50+ Identity Security Signals. One Continuously Scored Posture
Eliminate identity blind spots every environment.
Score risk in real time for every human and non-human identity.
Detect toxic access and privilege risks early, before they escalate.
Prioritize remediation based on actual breach impact, not alert noise.
Automate fixes directly into IAM, ITSM, and security workflows.
Identify, manage, and fix every identity security posture gap
Unified Identity Security Posture Graph
Map identity sprawl from IAM, IGA, PAM, cloud, on-prem, and hybrid into a unified view.
Detect shadow admin accounts, hidden entitlements, and risky access paths in real time.
Enforce Zero Trust with continuous identity verification across every system.

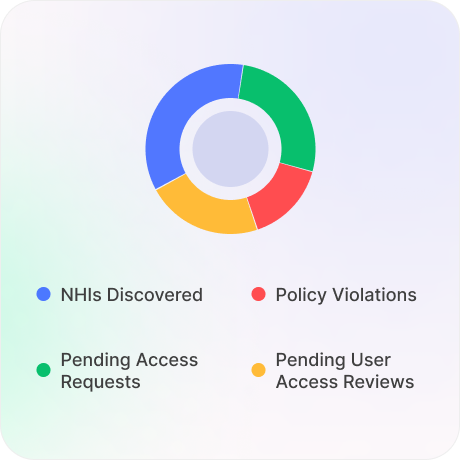
AI-Powered Identity Risk Scoring and NHI Governance
Score every human and non-human identity - service accounts, API keys, AI agents.
Track posture drift and prioritize by real exposure, not alert volume.
Enforce least privilege. Automate credential rotation across your NHI estate.
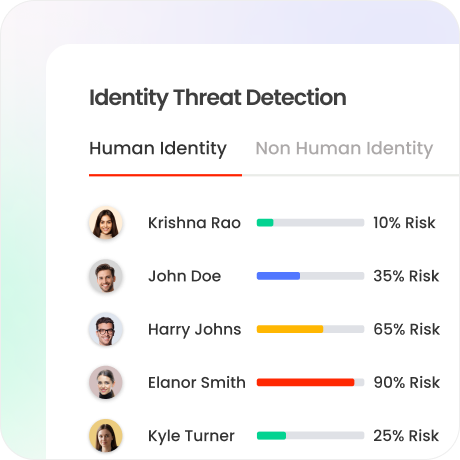
Toxic Access and Attack Path Detection
Surface excess privilege, privilege creep, and toxic access combinations across your full environment.
Visualise the exact attack paths that enable lateral movement, and insights to close them before they're used.
Trace any risk signal back to its source identity, entitlement, and system in a single click.

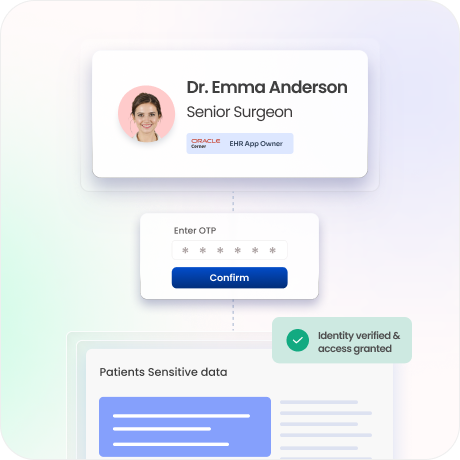
MFA Coverage and Gap Analysis
Find every identity without MFA, with bypassed controls, or still running legacy authentication.
Each gap widget is interactive, see the affected identities, and act immediately.
Close coverage gaps before an auditor, or an attacker.
Stale and Orphaned Identity Detection
Surface stale accounts, orphaned identities, and inactive NHIs still with access.
Validate offboarding completion across every system and identity type.
Reduce audit exposure by eliminating ungoverned dormant accounts.
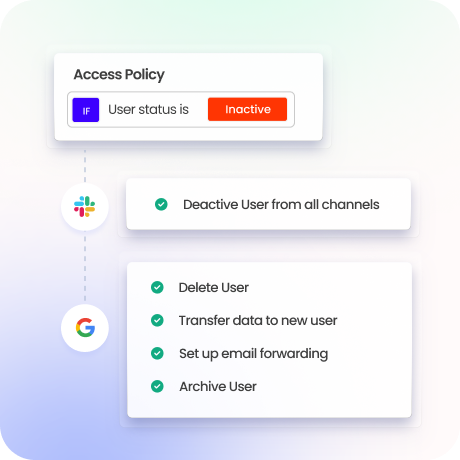
Automated Remediation, Reviews and Compliance
Route risk-prioritized tickets to ITSM, IAM, and security tools automatically.
Pre-built playbooks: revoke, restrict, rotate, review. Track every fix.
Streamline access certifications. Generate SOX, HIPAA, GDPR, and ISO 27001 evidence.

Drive measurable value with Identity Confluence
Calculate Your ROI
50%
Identity Security Signals
90%
faster investigations
3-5x
ROI
within the first year
Why Teams Choose Identity Confluence
1.
Unified Security Overview with 50+ signals
See every risk in one place, continuously tracked and scored, from toxic access and MFA gaps to privilege drift, dormant NHIs, and orphaned credentials.

2.
Every widget drives action
From risk found to ticket closed without a single manual handoff. Drill into any signal, trace it to its source, and remediate.

3.
Built for complex environments
No matter your environment, hybrid, multi-cloud, legacy, or ERP, you can deploy your way and start seeing posture insights right away, not months later.



