
Secure Federal Systems with Modern Identity Security
Federal agencies govern thousands of identities across hybrid environments where a single access gap can compromise mission-critical systems. Close every gap. Continuously.
Trusted by



Fragmented Identity Access Weakens Federal Security
Federal agencies manage thousands of users, contractors, & systems across hybrid environments. Without centralized Identity Governance, access becomes difficult to track, and harder to secure.
See It in Action →
Bring Federal Identity Access Under Unified Control
Govern workforce and contractor identities from a single platform
Enforce least privilege across every federal system and application
Automate onboarding, transfers, and access revocation end to end
Secure contractor and inter-agency access with time-bound controls
Maintain continuous compliance with ICAM, NIST 800-63, and Zero Trust
Identity Governance Built for Federal Mission Security
See Every Identity Across Agency System
Discover and maintain a centralised view workforce, contractor, and machine identities across agency environments.
Maintain centralized visibility across cloud and on-prem environments.
Shadow accounts, unowned credentials, and access anomalies surface before they become security incidents.

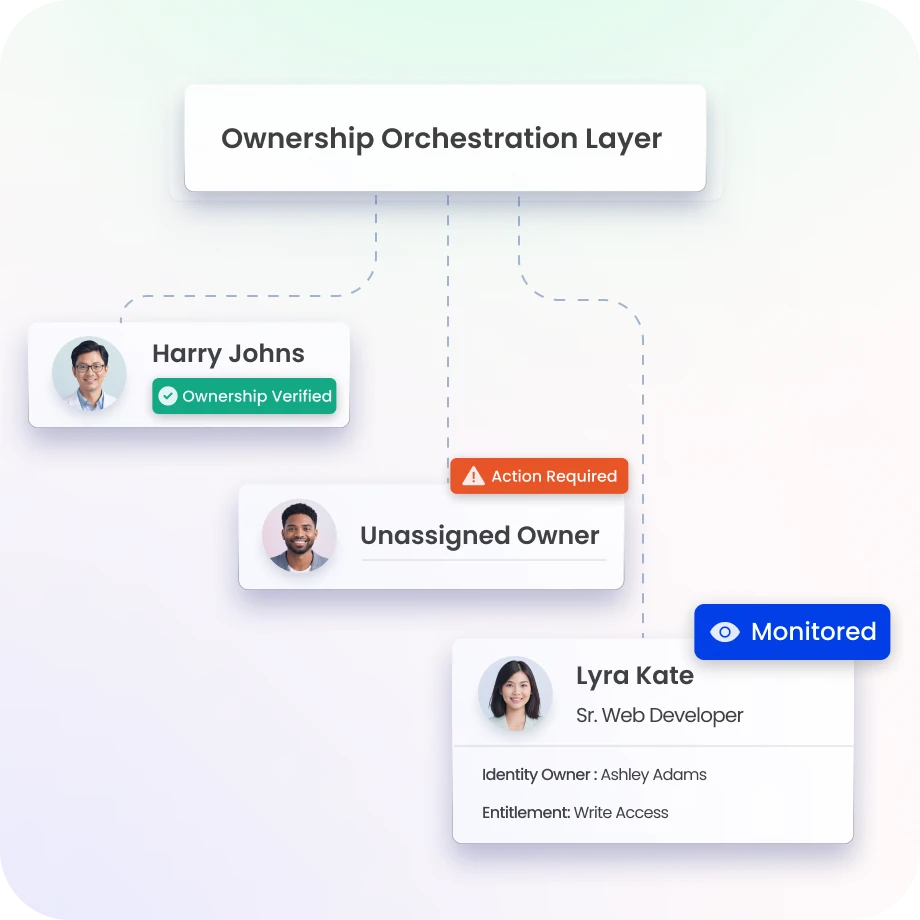
Ensure Every Identity Has Clear Ownership
Every identity, human or machine links to a responsible owner and agency role.
Ownership changes and unassigned identities trigger automatic alerts
Maintain accountability across programs, departments, and partners.
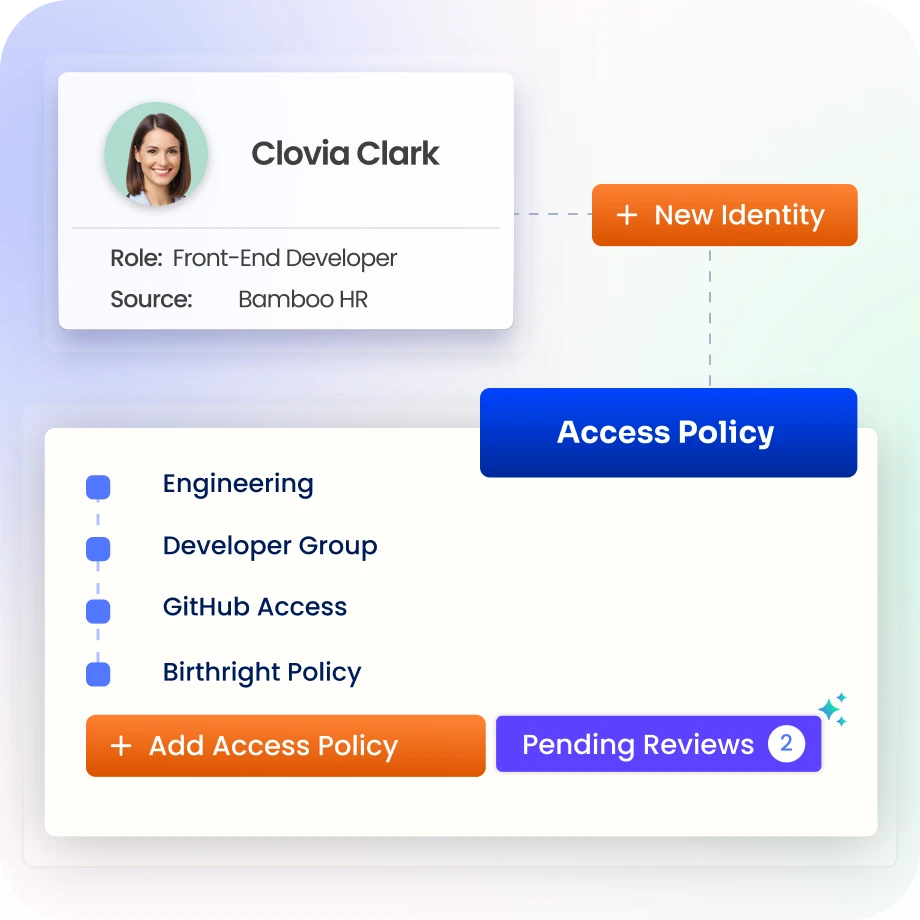
Enforce Least Privilege Across Government Systems
Enforce least privilege aligned to agency roles and responsibilities.
Excessive permissions are identified and removed across applications and infrastructure.
Reduce risk of insider misuse and credential compromise.
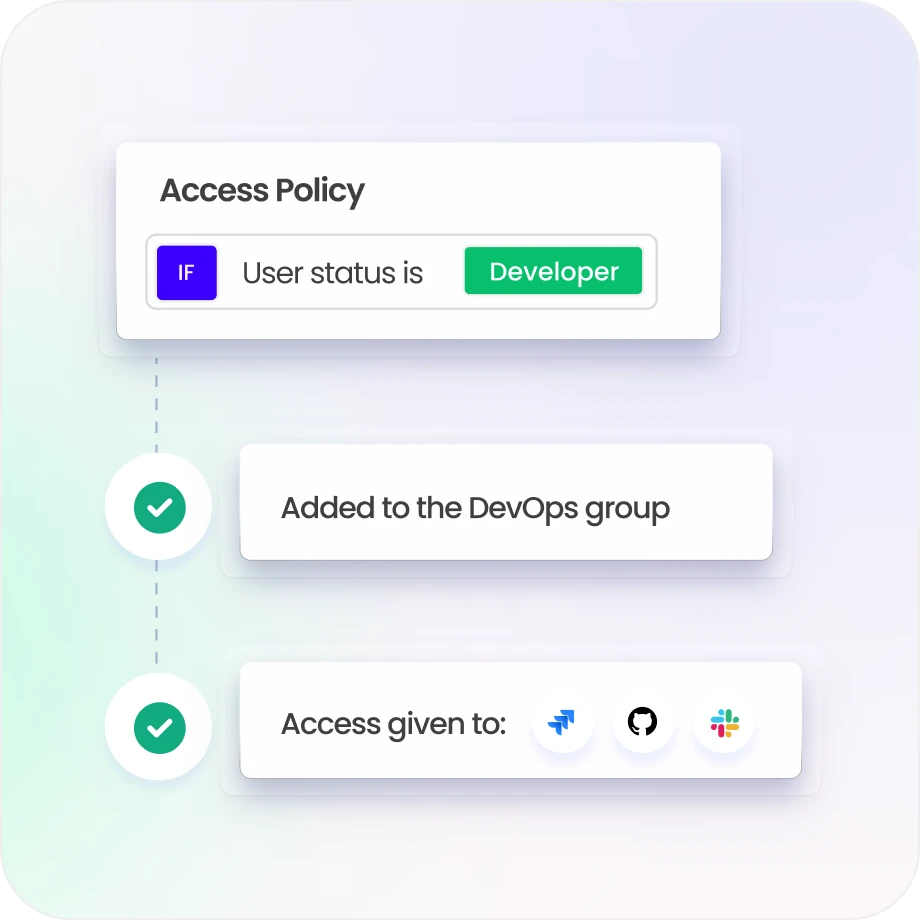
Govern Contractor and Inter-Agency Access
Provide controlled, time-bound access to contractors, partners, and external agencies.
Maintain full visibility into every third-party permissions.
Reduce risk across inter-agency and vendor collaboration.

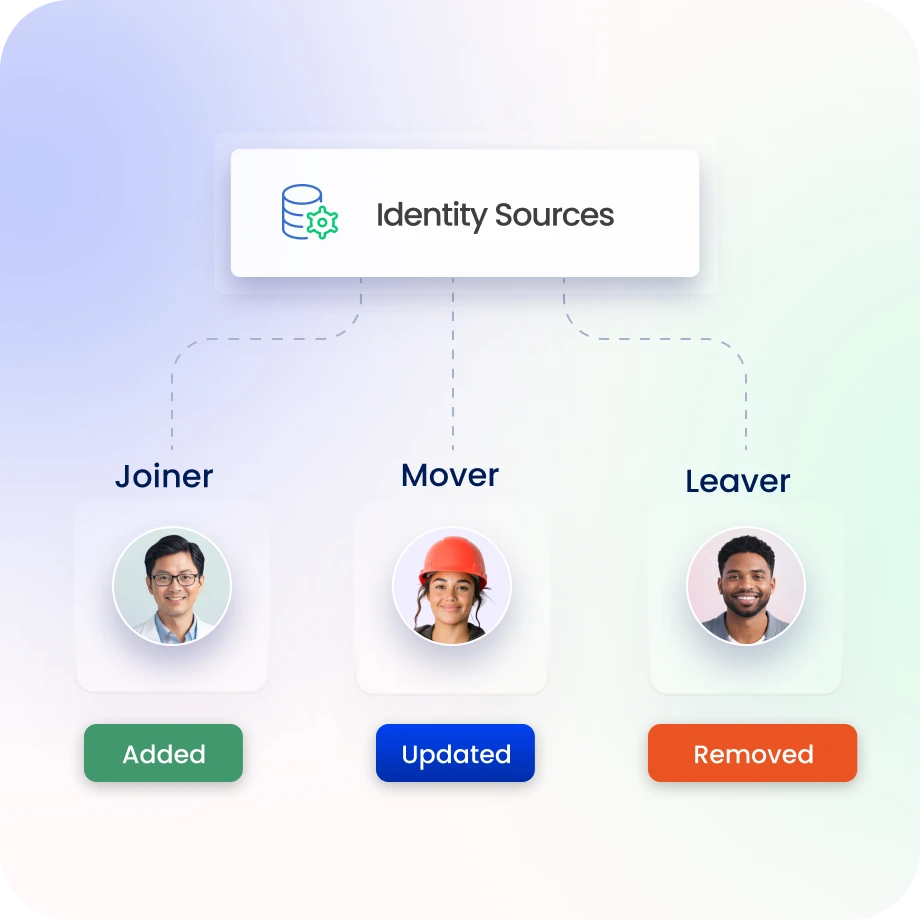
Automate Identity Lifecycle Across Agencies
Identity Confluence automates onboarding, transfers, and terminations.
Adjust permissions automatically when roles change.
Reduce manual provisioning and operational delays.
Maintain Continuous Federal Compliance
Track access certifications, policy enforcement, and SoD controls centrally.
Support ICAM, NIST, FedRAMP, and other federal standards.
Maintain audit evidence without manual preparation.

Drive measurable value with Identity Confluence
Download the ROI Report
80%
fewer identity security incidents
85%
faster contractor access provisioning
3-5x
ROI
within 12 months
Why Teams Choose Identity Confluence
1.
Unified Identity Visibility
Govern workforce, contractor, and machine identities across federal systems from one platform, ensuring security.

2.
Policy-Driven Zero Trust
Enforce least privilege and identity verification aligned with ICAM and NIST standards.

3.
Continuous Compliance Readiness
Maintain audit-ready identity governance for federal regulations and security mandates.



