Secure Telecom Networks With Intelligent Identity Governance
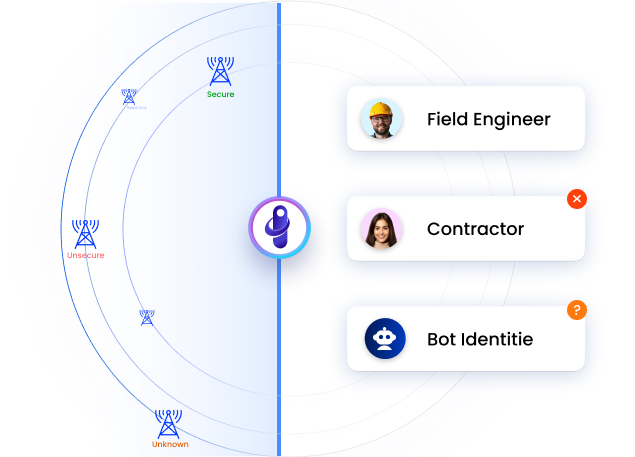
Field engineers, contractors, and network automation identities multiply fast and govern slowly. Automate the lifecycle, close access gaps, and stay compliant continuously.
Trusted by



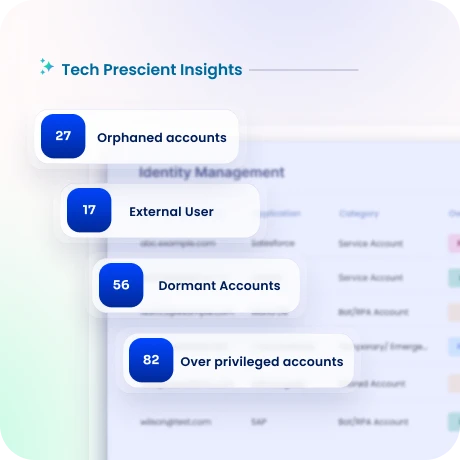
Uncontrolled Identity Access Puts Networks at Risk
Telecom operators manage workforce, contractor, and machine identities across networks that cannot afford downtime. Manual provisioning, fragmented controls, and poor visibility create gaps attackers find first.
See It in Action →
Turn Identity Governance into a Network Security Control Layer
See every workforce, contractor, and network identity in one place.
Automate identity lifecycle from onboarding through access revocation.
Govern machine identities across network infrastructure and APIs.
Enforce least privilege, policy based access and rotate secrets.
Maintain continuous compliance with NIS2, GDPR, ISO 27001, and more.
Identity Governance Features for Telecom Environments
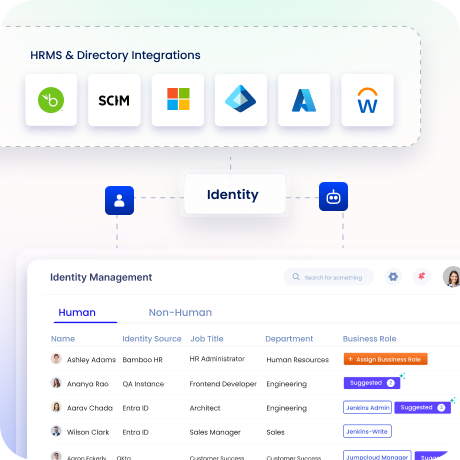
See Every Identity Across Your Network
One centralized view of workforce, contractors, field operations, and network automation identities across BSS, OSS, cloud, and on-prem systems.
Shadow accounts, orphaned credentials, and access gaps surface before they become incidents.
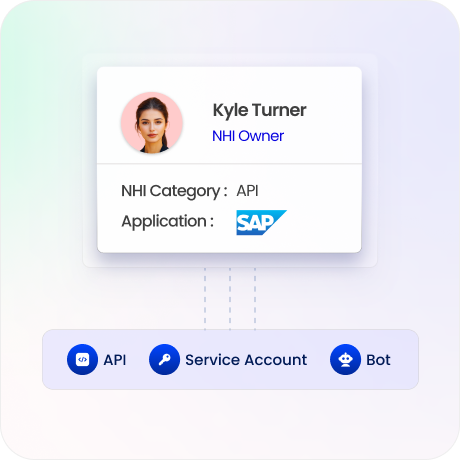
Govern Machine and Network Identities
Discover and classify service accounts, APIs, and network automation identities at scale.
Map clear ownership to every machine identity across your network infrastructure.
Enforce credential rotation and least-privilege controls for all non-human access.
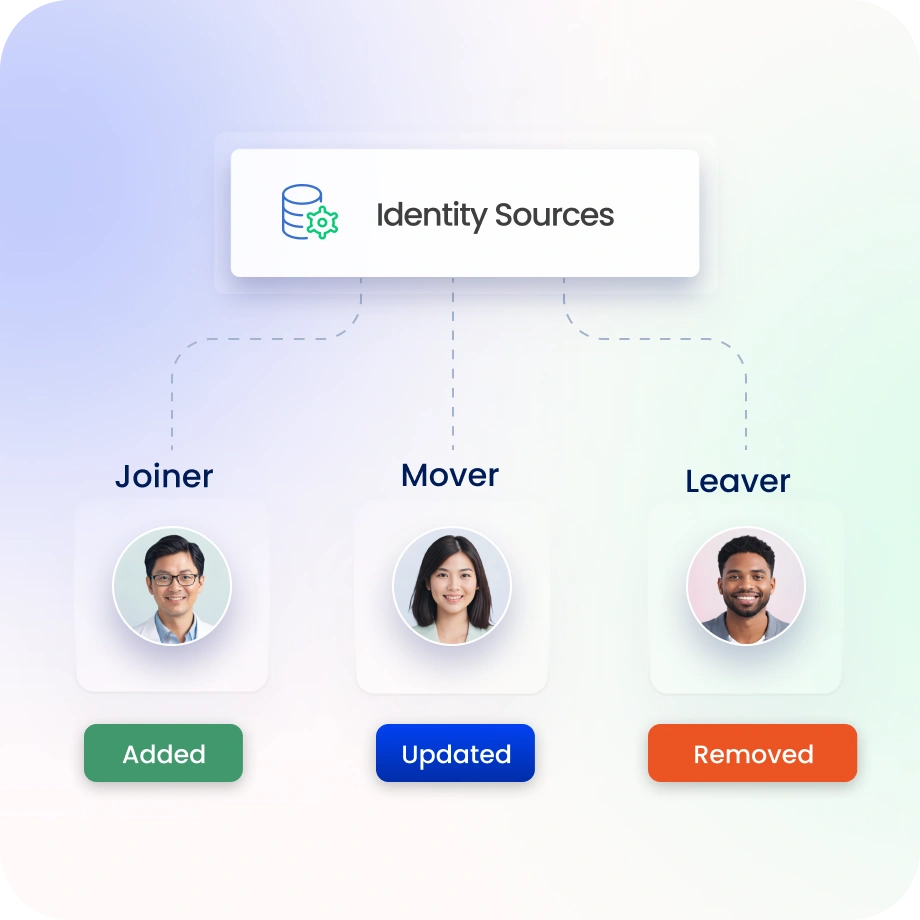
Automate the Full Identity Lifecycle
HRMS-driven provisioning and deprovisioning triggers automatically when engineers join, transfer, or leave.
Eliminate orphaned accounts and reduce residual access risk across network operations.
Control Every External Identity
Field engineers, vendors, and third-party partners get the access they need only when they need it.
Time-bound, governed, and automatically revoked when engagements close.
No manual tracking of who has access to what across your partner ecosystem.

Continuous Compliance and Audit Readiness
Centralize access certifications, and policy enforcement in one place.
Pre-built template for NIS2, GDPR, DPDPA, ISO 27001, SOC 2, NIST, and more.
Reduce audit preparation time and demonstrate continuous compliance to regulators.

Drive measurable value with Identity Confluence
Calculate Your ROI
90%
automated workflows
85%
faster onboarding
3-5x
ROI
within the first year
Why Teams Choose Identity Confluence
1.
Unified Identity Visibility
Centralized view of workforce, contractor, and network identities across legacy, cloud, and hybrid telecom systems.

2.
Automation-Driven Operations
Automate lifecycle workflows, access reviews, and credential rotation to reduce effort and keep access controlled.

3.
Deployment Without Compromise
Support SaaS, on prem, hybrid, and Kubernetes identity deployments while meeting data and regulatory requirements.



