Identity Governance Powered by AI, Not Spreadsheets
Static rules miss what changes between reviews. Machine learning continuously scores risk, mines roles, detects anomalies, and recommends access decisions, before a human has to ask.
Trusted by



Rule-Based Governance Cannot Keep Up
Static policies miss what changes between reviews. Managers rubber-stamp entitlements with no context. Role engineering takes months and drifts the moment it ships.
See How We Fix This →

AI That Scores, Mines, Detects, and Recommends
Score every identity with ML-powered risk formulas per app, per tenant.
Mine and optimize roles using AI that finds natural groupings automatically.
Detect anomalies through behavioral baselines before they escalate.
Recommend access decisions with context so reviewers act on insight, not instinct.
Surface SoD violations, orphaned accounts, and over-privileged access in real time.
Intelligence Built Into Every Governance Decision
AI-Powered Role Mining and Optimization
Discover natural role groupings by analyzing access patterns across users, systems, and departments.
Consolidate entitlements into Business and Application Roles so approvers certify job functions, not cryptic technical names.
Continuously revise roles as business structures evolve through an automated feedback loop.
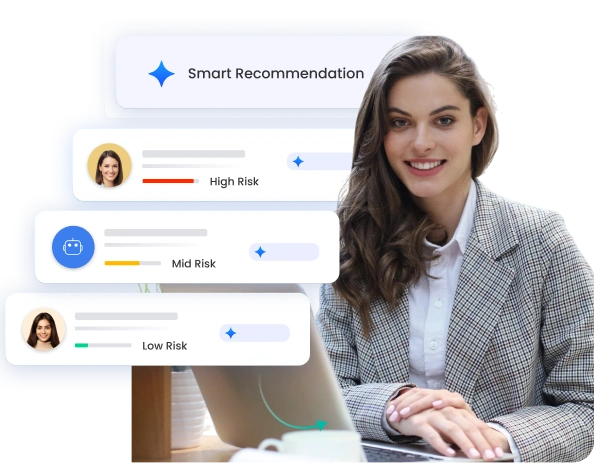
Configurable Identity Risk Scoring
Score every user-application combination using formulas configurable at the tenant and per-application level.
Evaluate risk based on role sensitivity, data sensitivity, and behavioral history.
Surface over-privileged accounts with automated right-sizing recommendations.
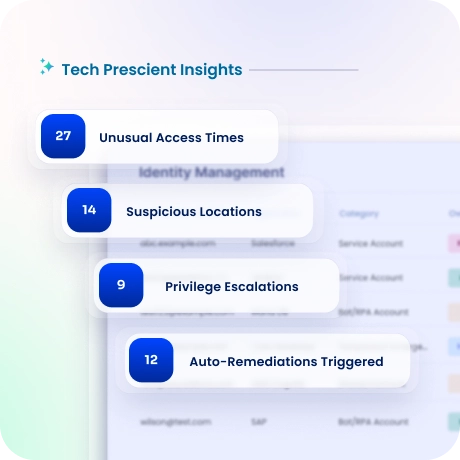
Anomaly Detection and Behavioral Analytics
Establish behavioral baselines using machine learning and alert on deviations in near real time.
Flag unusual access times, unexpected locations, privilege escalation, and dormant credentials suddenly activating.
Integrate alerts with SIEM tools and trigger automated remediation or recertification workflows so detection leads to action.
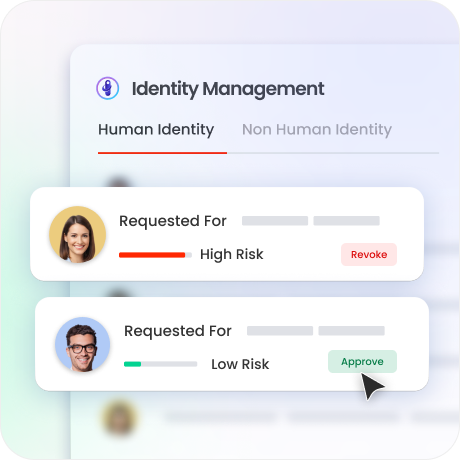
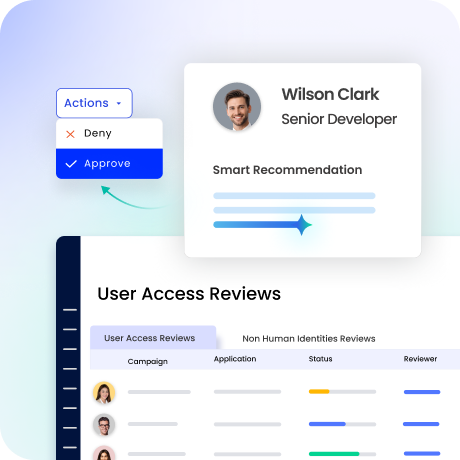
Intelligent Access Certification
Give reviewers risk scores, access sources, last-used dates, and peer-based recommendations per entitlement.
Automate low-risk access so managers focus only on high-risk decisions that need human judgment.
Support bulk and offline certifications at scale with a complete audit trail per decision.
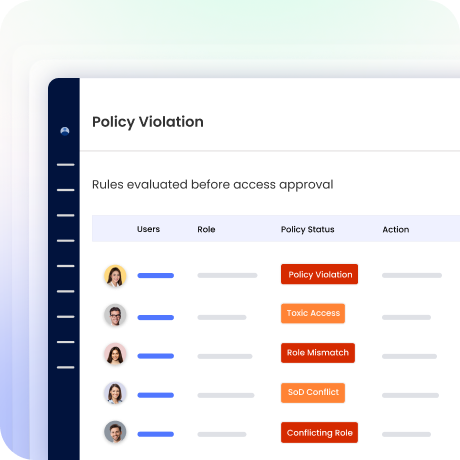
Smart SoD Detection and Enforcement
Detect toxic access combinations across systems using pre-built and custom policy rules.
Block conflicts at provisioning with preventive controls and flag emerging violations with detective controls.
Track exceptions with business justification and generate audit-ready SoD evidence automatically.
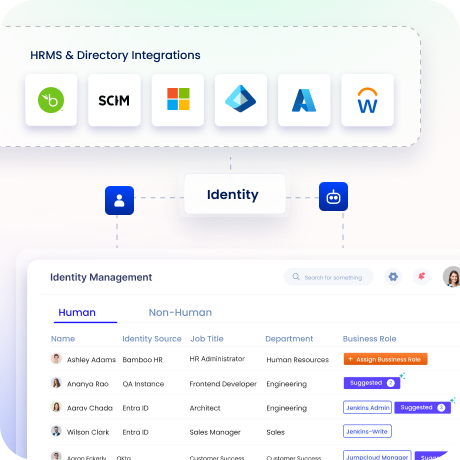
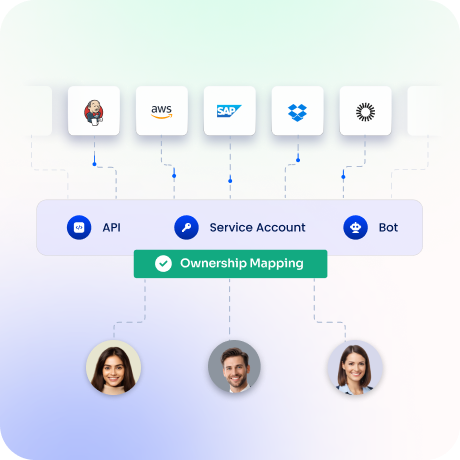
Non-Human Identity Discovery
Automatically discover and classify service accounts, IAM roles, secrets, and API tokens from cloud platforms.
Map every NHI to an accountable human owner with privilege and sensitive access visibility.
Enforce reminder-driven rotation at intervals without forced revocation that risks breaking live integrations.
Drive measurable value with Identity Confluence
Calculate Your ROI
90%
Reduction in role count
85%
Less access review effort
3-5x
ROI
within 12 months
Why Teams Choose Identity Confluence
1.
AI embedded, not bolted on
Native embedding in governance for risk scoring, role mining, anomaly detection, and certifications, not a bolt-on analytics export.

2.
Every identity under the same AI
Workforce, contractor, and non-human identities governed on one platform with consistent models and evidence.

3.
Connects to what you already run
API-first architecture and 250+ pre-built connectors integrate Identity Confluence into your existing identity ecosystem without ripping out what works.



