Identity Confluence
Non-Human Identity Governance
Secure Every Non-Human Identity Across Your Ecosystem
Establish ownership, restrict access, and reduce exposure for machine identities across cloud and on-prem environments.
Trusted by



Unmanaged Non-Human Identities Create Unseen Risk
Non-human identities multiply silently. Without ownership, access controls, or lifecycle governance, they accumulate privileges, bypass audits, & expose sensitive data, creating security & compliance blind spots.
Try for Free →
From Invisible Access to Governed Identity Control
Discover all non-human identities across environments
Map clear ownership and accountability instantly
Restrict access based on context and risk
Detect unusual activity early and respond quickly
Maintain continuous audit readiness automatically
Complete Governance for Non-Human Identities
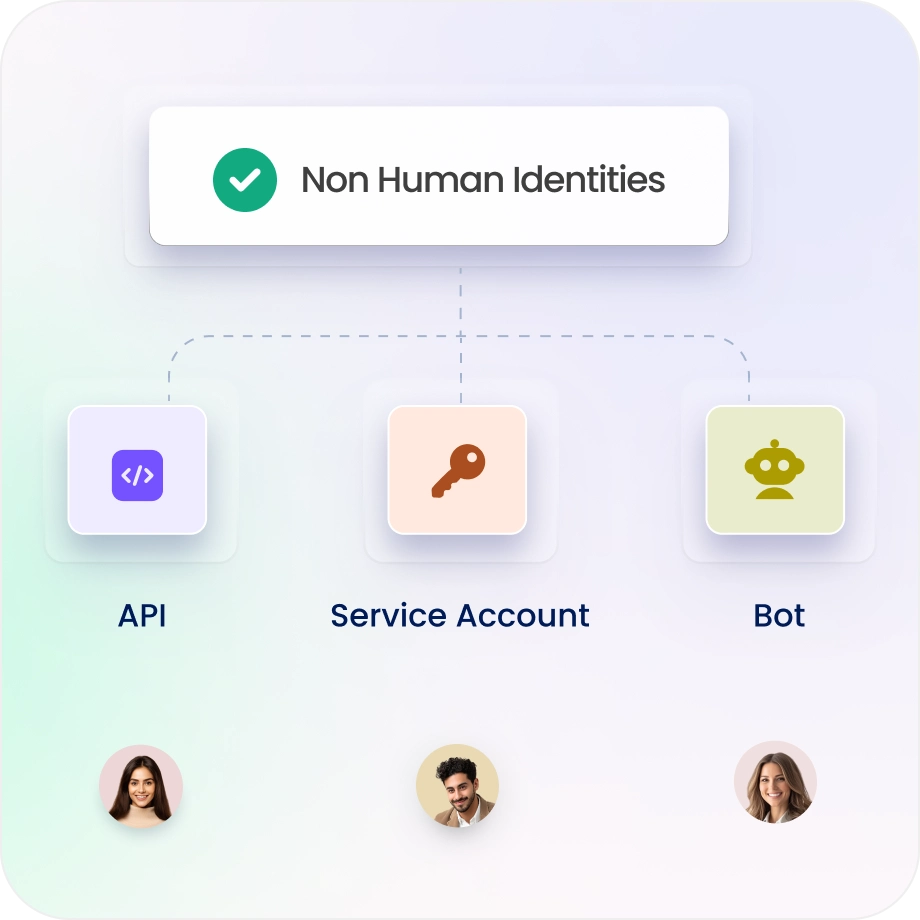
Maintain Complete Visibility of NHIs
Automatically discover service accounts, bots, and workloads.
Classify identities by risk, ownership, and usage to eliminate blind spots.
Establish normal behavior patterns and detect new or anomalous machine identities in real time.
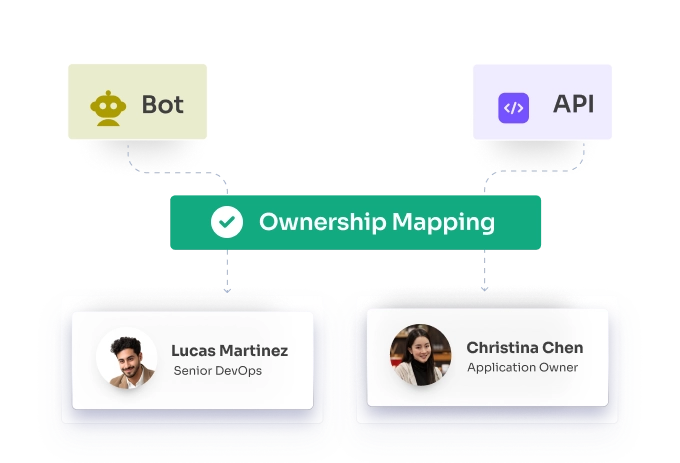
Every identity has a clear owner
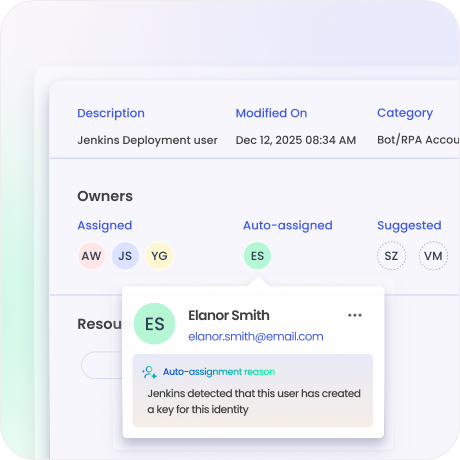
Map each NHI to a responsible human owner.
Get notified when ownership changes, becomes unassigned or when activity deviates from normal usage patterns.
Identify and Reduce High-Risk Access
See exactly what each NHI can access and which sensitive data is exposed.
Identify excessive permissions and risky access paths before they are misused.

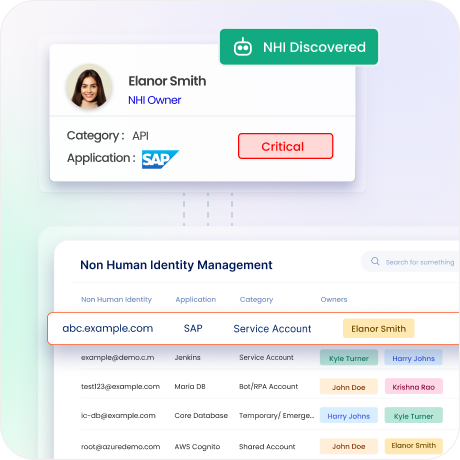
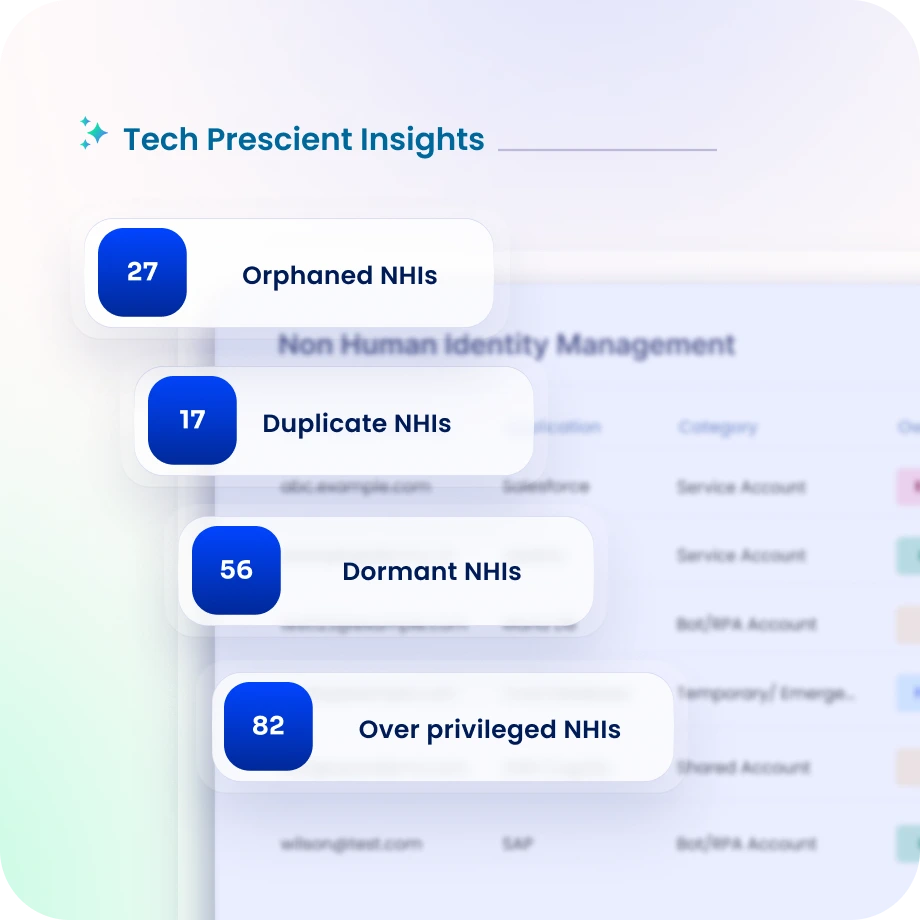
Eliminate Orphaned and Unused Identities
Reconcile, merge, and remove orphaned or duplicated NHIs.
Maintain a centralized, trusted identity inventory as a single source of truth.
Continuously detect unused credentials, inactive tokens, and abandoned integrations.
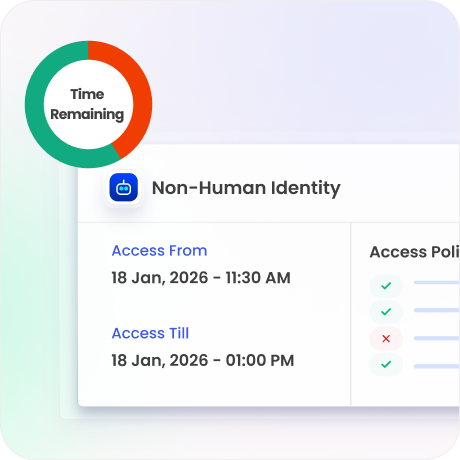
Enforce Access Only When Required
Grant access only when needed, and revoke automatically.
Eliminate standing privileges and reduce attack surface.
Adapt access dynamically based on risk level, behavior, and contextual signals.
Continuous Audit Readiness
Generate audit-ready evidence with complete trails of access, ownership, and changes.
Support SOX, HIPAA, ISO, SOC 2, and internal policies with Evidence Center.
Maintain a complete timeline of activity and access changes for investigations.

Drive measurable value with Identity Confluence
Download the ROI Report
20:1
ratio of NHIs to human identities uncovered
80%
reduction in orphaned identities
3-5x
ROI
within 12 months
Why TechPrescient Is Different
1.
Ownership-First Model
Every non-human identity is mapped to a real owner for accountability and traceable access decisions.

2.
Lifecycle Controls
Access is granted only when needed and revoked automatically, reducing standing privileges and attack surface.

3.
Business Context
Prioritize risk based on privileges, data access, and business impact, so security teams act on what truly matters.



