
Secure Access for Healthcare with Intelligent Identity Governance
Secure clinician, partner, and patient identities while automating access governance across EHR systems, cloud platforms, and healthcare applications.
Trusted by



Broken Identity Governance Creates Security & Compliance Risks
Manual access reviews, delayed joiner-mover-leaver processes, and no automated certifications or SoD checks increase risk and reduce visibility.
See It in Action →
Identity Governance Built for Healthcare Ecosystems
Automate identity lifecycle for clinicians, staff, partners, machines
Self-service access requests with intelligent approval workflows
Automated access certifications and reviews to enforce least privilege
Role mining, role management, and SoD enforcement for healthcare
Centralized entitlement visibility across EHR, SaaS, cloud, on-prem
Continuous policy enforcement, risk scoring, and audit-ready reports
End-to-End Healthcare Identity Governance Features
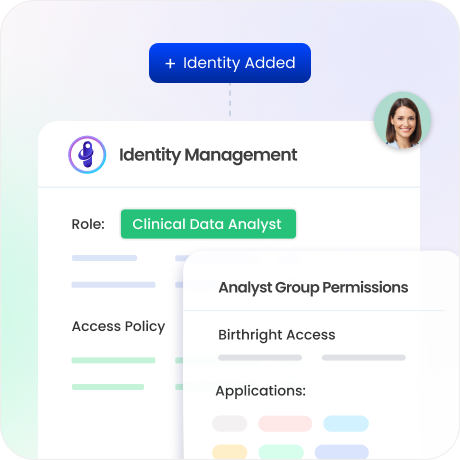
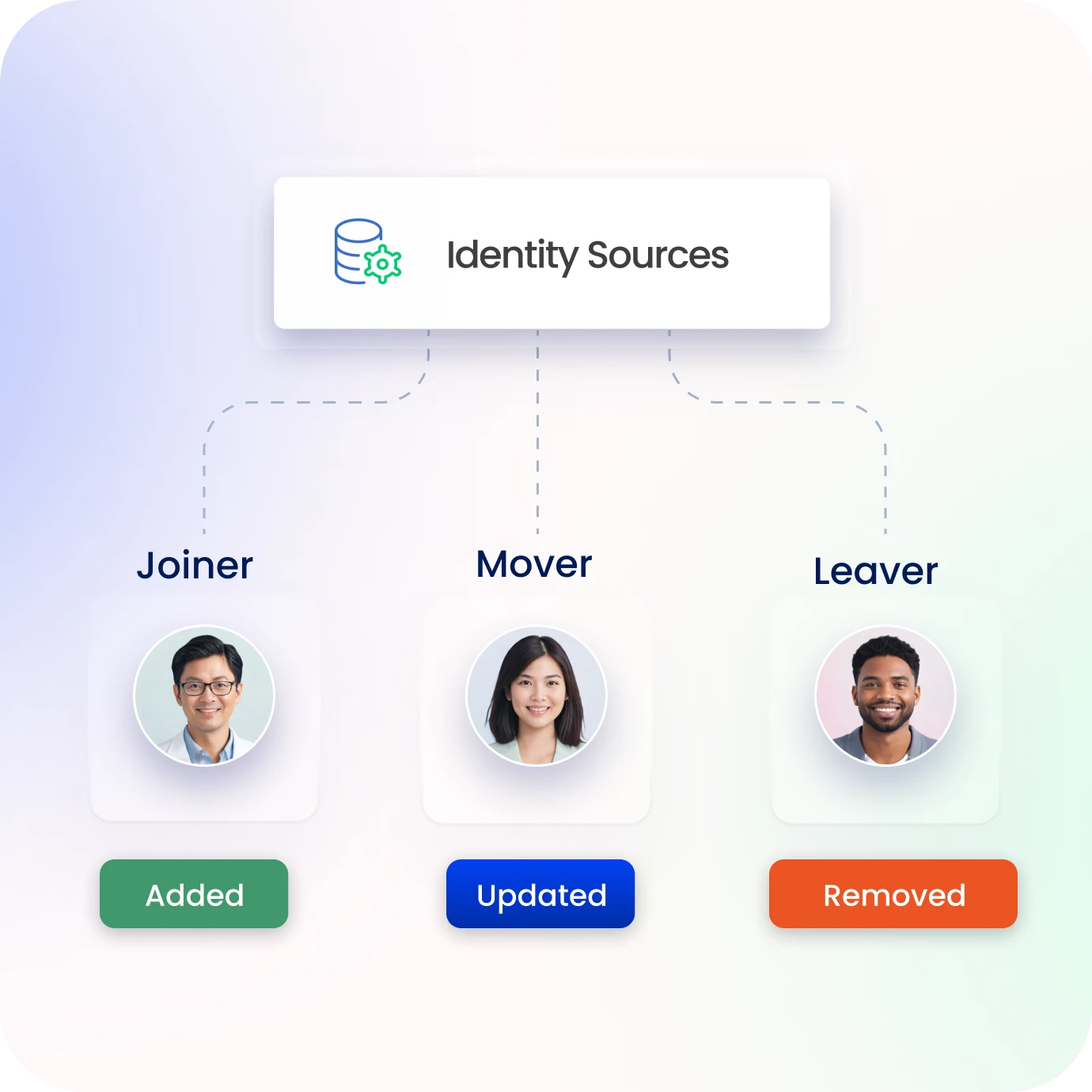
Automate the Healthcare Identity Lifecycle
Automate onboarding, role changes, and offboarding across healthcare systems.
Ensure clinicians receive day-one access to EHR and clinical application.
Instant revocation on role change or termination.
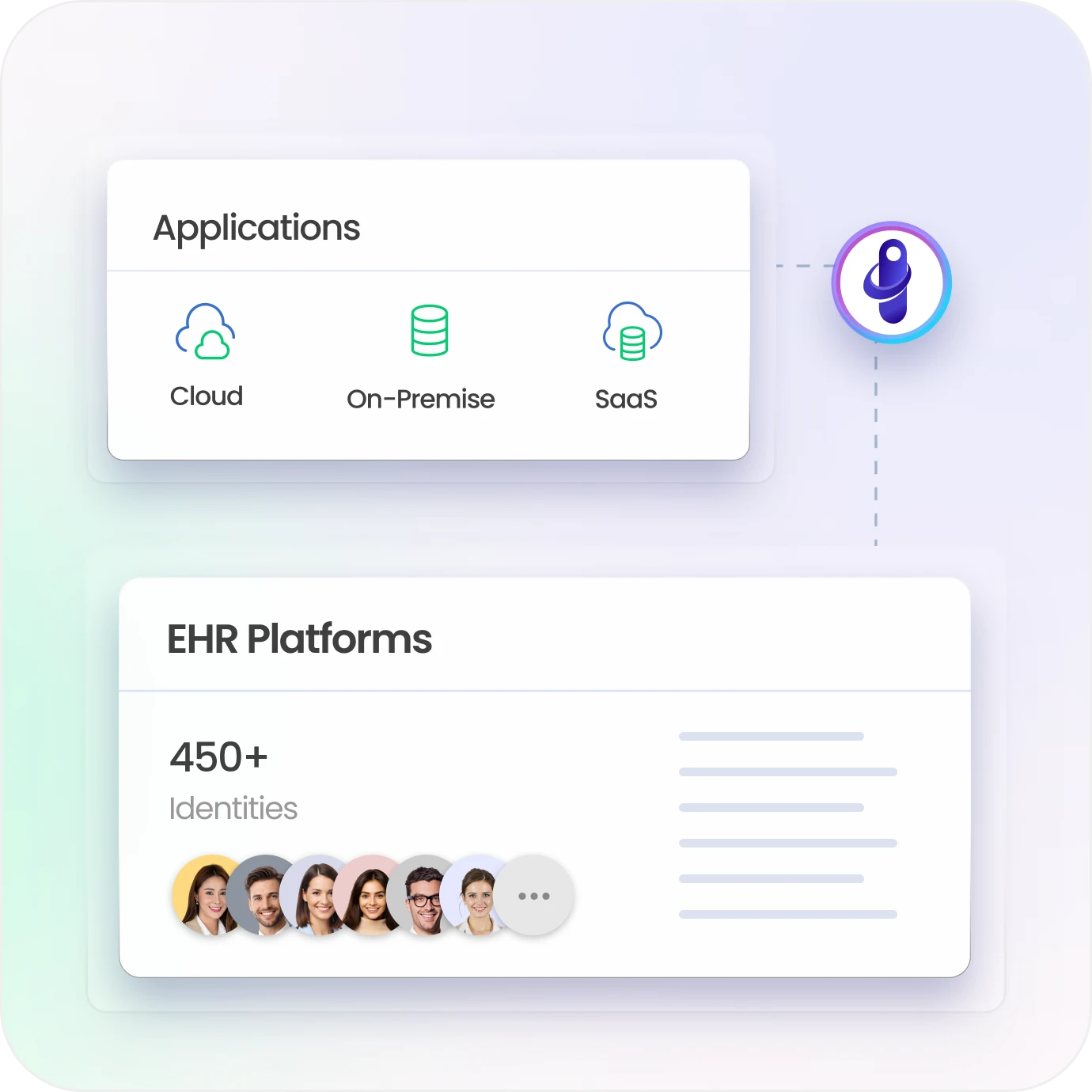
Deliver Secure Access to Clinical Applications
Integrate Identity Governance with EHR and healthcare platforms.
Centralize access governance across cloud, SaaS, and on-prem systems.
Enforce consistent security policies across healthcare infrastructure.
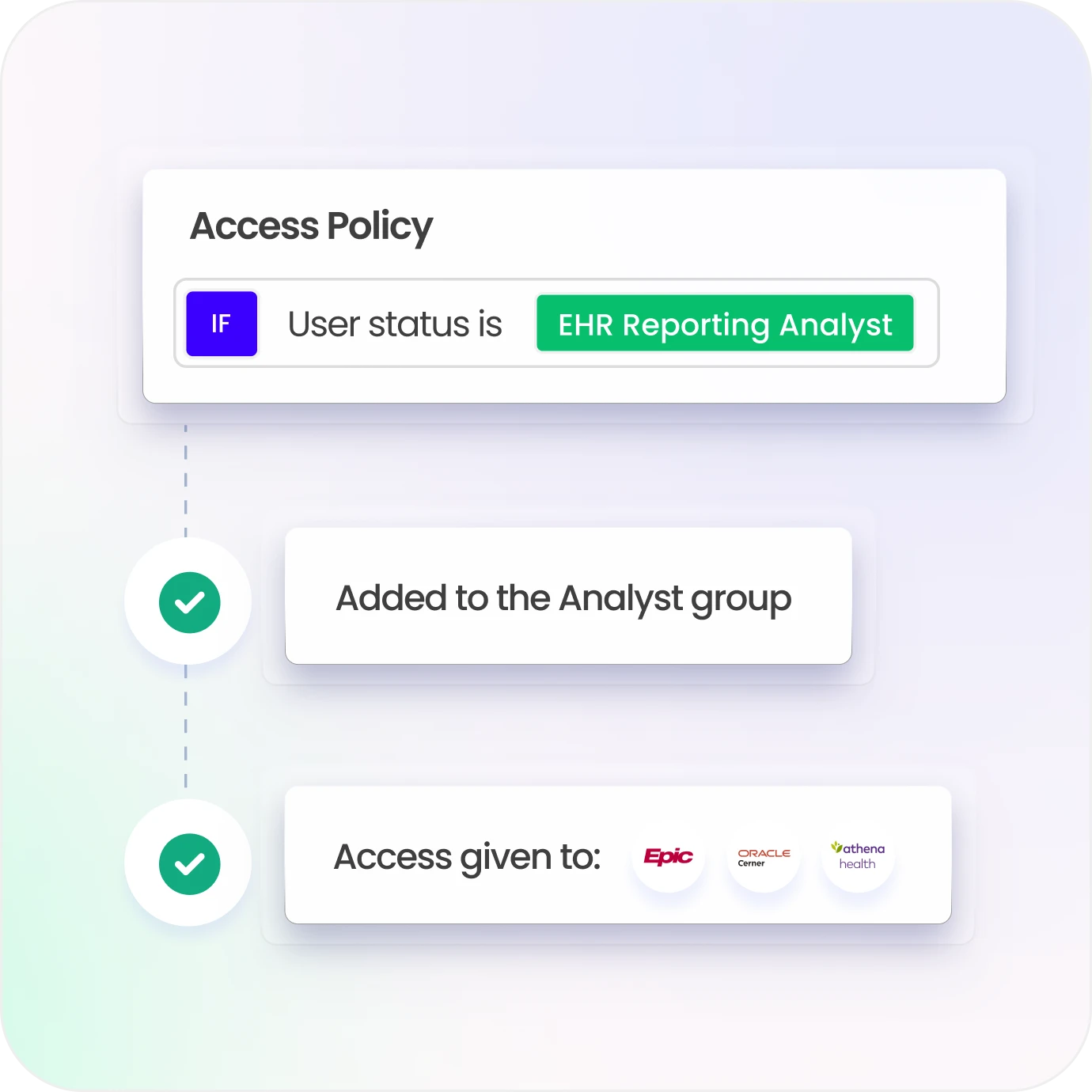
Enforce Least-Privilege & Policy Governance
Advanced RBAC, PBAC, and entitlement management.
Automated SoD conflict detection and remediation.
Validate permissions continuously with intelligent access reviews.
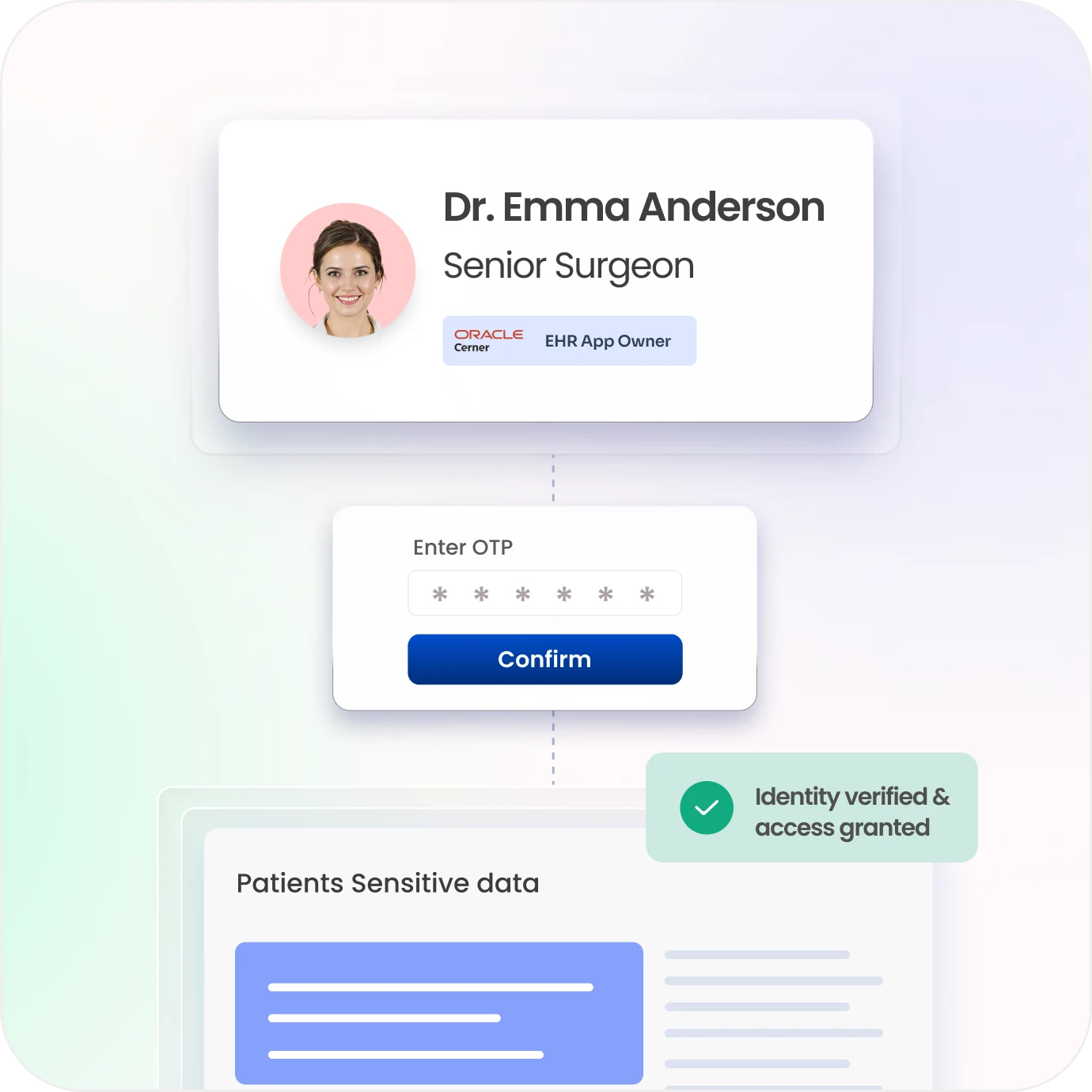
Protect Patient Data with Strong Authentication
Govern access with least-privilege and policy-based controls.
Detect anomalous access and compromised credentials across identities.
Secure patient portals and healthcare apps with seamless MFA/SSO integration.
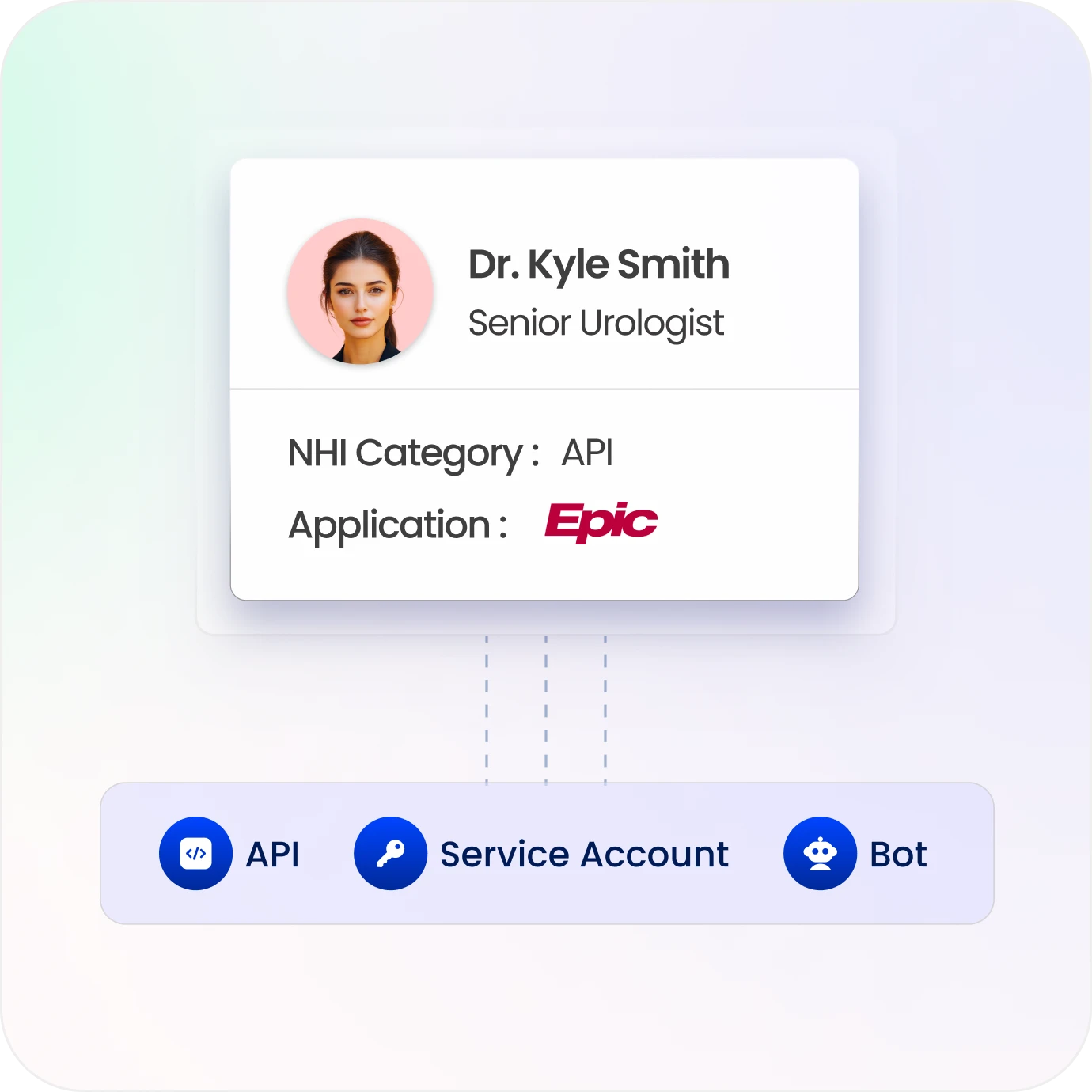
Govern All Healthcare Identities
Secure clinicians, staff, contractors, partners, and patient identities.
Govern service accounts, bots, and machine identities.
Apply consistent identity security policies across all identity types.
Maintain Continuous Healthcare Compliance
Track identity activity with detailed audit trails.
Generate compliance evidence aligned with HIPAA, HITRUST, ISO 27001, and SOC 2.
Detect policy violations before audits and compliance reviews.

Drive measurable value with Identity Confluence
Calculate Your ROI
90%
Faster provisioning
85%
Fewer identity risks
3-5x
ROI
within 1st year
Why Teams Choose Identity Confluence
1.
Unified Healthcare Identity Governance
Centralize identities, access, and entitlements to improve visibility and reduce risk.

2.
Automation-Driven Access Control
Automate lifecycle and access workflows to eliminate manual effort and speed operations.

3.
Scalable & Compliant Architecture
Enforce consistent policies and maintain compliance across EHR, cloud, and healthcare systems.

GET A PERSONALIZED DEMO


