Identity Confluence
Just In Time Access
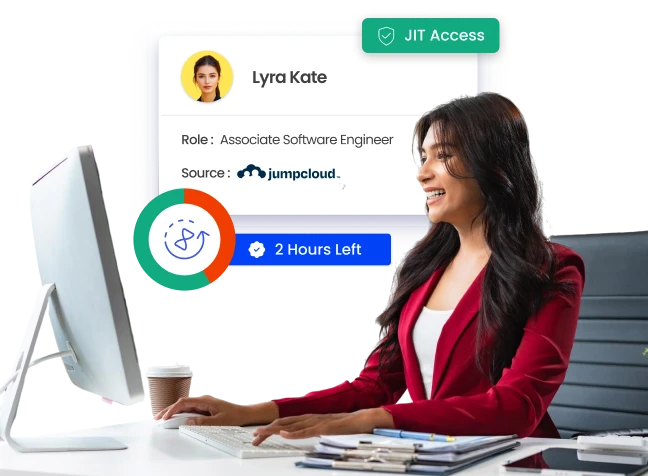
Eliminate Standing Privileges. Enforce Least Privilege
Elevated access that exists indefinitely is elevated risk that exists indefinitely. Grant it when it is needed, scope it to the task, and revoke it automatically when it is done.
Trusted by



Standing Privileges Are Your Largest Unmanaged Risk
Most elevated access is granted once and never reviewed again. It sits active, unused, and invisible until an attacker finds it and moves through your environment before anyone notices.
See How We Fix This →
Access That Exists Only When It Needs To
Grant time-bound, scoped access via request, approval, or automated workflow.
Enforce least privilege at the task level, not just the role level.
Revoke elevated access automatically the moment the window expires.
Route every request through configurable, risk-aware approval workflows.
Validate every request with AI-driven risk scoring before access is granted.
Every Layer of JIT Access. Governed and Automated
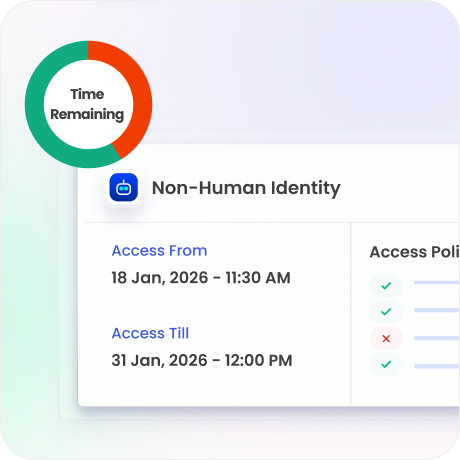
Time-Bound Access, Zero Residual Risk
Define exact start, end times and scope set at approval enforced automatically.
Access expires automatically when the window closes or the task completes.
No manual cleanup. No forgotten accounts. No residual risk.

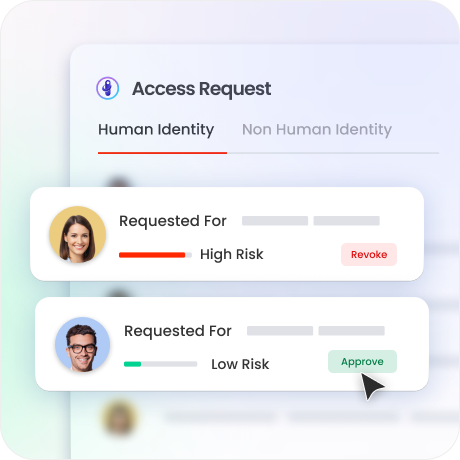
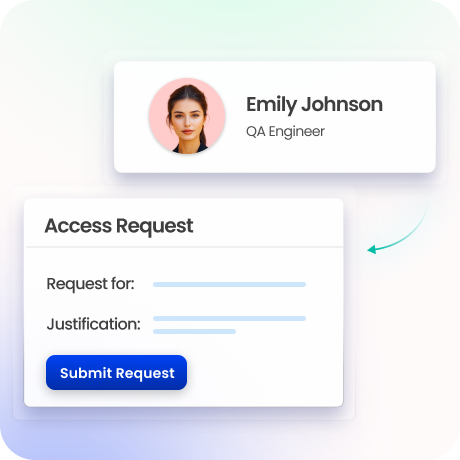
Policy-Driven Approval Workflows
Users request elevated access with a defined justification and scope.
Low-risk requests auto-approve with defined justification, role, and risk score.
High-risk requests escalate through configurable multi-level approval chains.
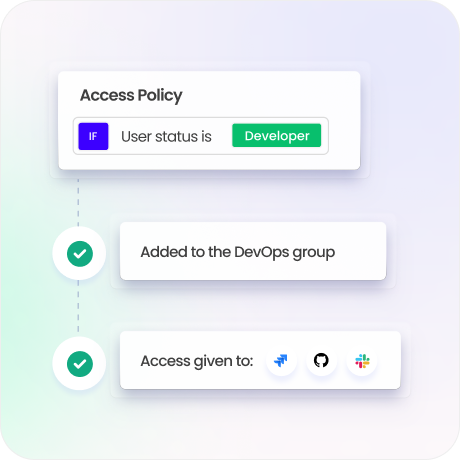
Just-Enough Privilege, Nothing More
Every access grant scopes to the specific permissions required for the task.
RBAC and ABAC policies define the exact systems, resources, and commands accessible.
Prevent lateral movement by scoping every privilege granted at the task level.
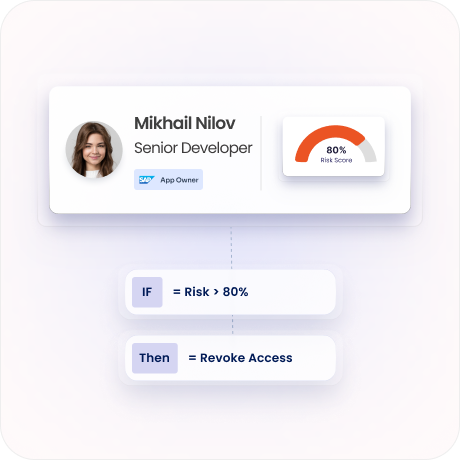
AI-Driven Risk Scoring Before Every Grant
Configurable risk formulas score every access request before it reaches an approver.
Active sessions are continuously evaluated and behavioural anomalies flagged in real time.
Over-privileged accounts surface automatically with right-sizing recommendations.
Emergency Access That Is Still Governed
Break-glass procedures allow rapid elevated access during critical incidents.
Every emergency session is policy-controlled, fully monitored, and audit-logged in real time.
Mandatory post-incident review ensures every break-glass grant is accounted for.
Complete Session Monitoring and Audit Trails
Log every request, approval, action, and revocation in a complete, immutable record.
Generate pre-configured compliance reports for SOX, HIPAA, PCI DSS, GDPR, and ISO 27001.
Fewer standing accounts means less to certify and review.

Drive measurable value with Identity Confluence
Calculate Your ROI
100%
ownership mapping across all NHIs
95%
Access grants automated
3-5x
ROI
within 12 months
Why Teams Choose Identity Confluence
1.
One engine for governance and enforcement
Most JIT tools bolt onto an existing IAM layer and create a new gap between where access is governed and where it's enforced. Identity Confluence unifies IAM and IGA in one platform.

2.
Risk scored before access is granted, not after
AI-driven risk scoring validates every request before a single permission is granted, not after an incident surfaces that a session was anomalous.

3.
Connects to everything already in your stack
API-first architecture and 250+ pre-built connectors mean JIT access governance extends to every system your privileged users touch.



