
Govern Every Identity. Automate Every Access Decision.
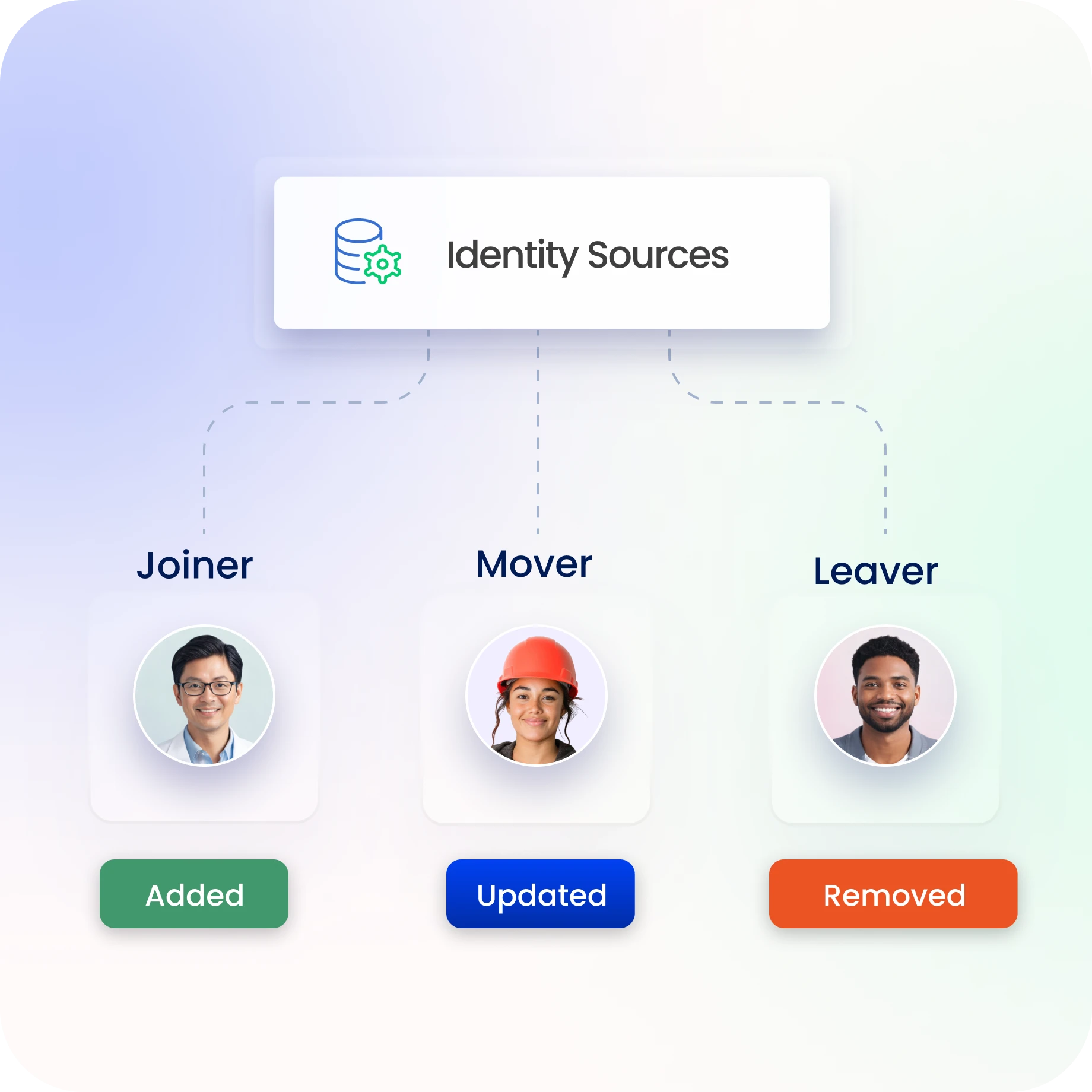
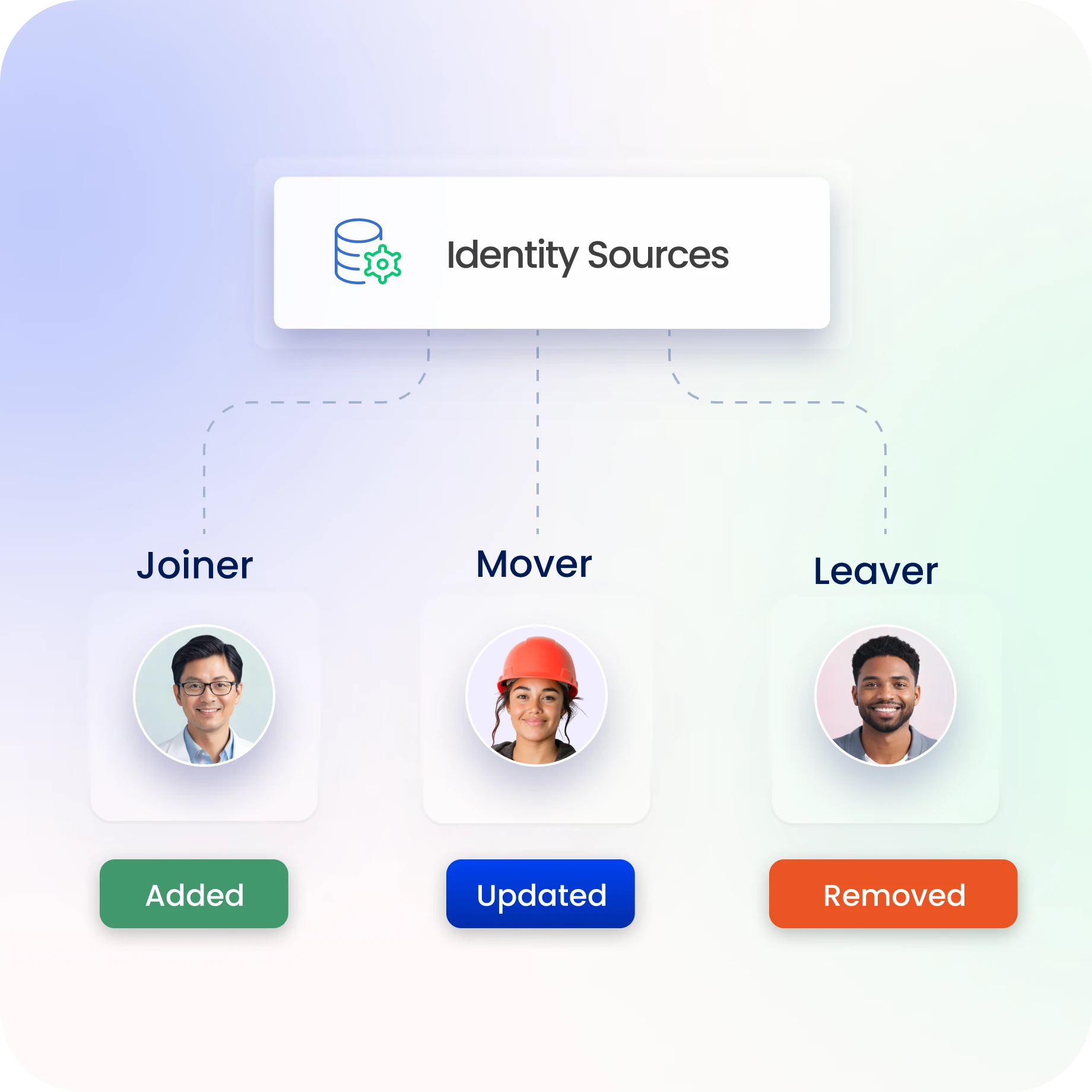
Identity Confluence enforces policy-driven access across joiner, mover, and leaver events with full audit traceability across enterprise systems.
Trusted by



Uncontrolled Identity Access Disrupts Manufacturing
As factories digitize and supply chains expand, identities multiply across IT and OT systems. Without centralized governance, access becomes fragmented, excessive, and difficult to audit, increasing the risk of downtime, IP exposure, and compliance gaps.
See It in Action →
Simplify Workforce Identity Lifecycle and Access Governance
Manage joiner, mover, leaver lifecycle across HR systems and directories
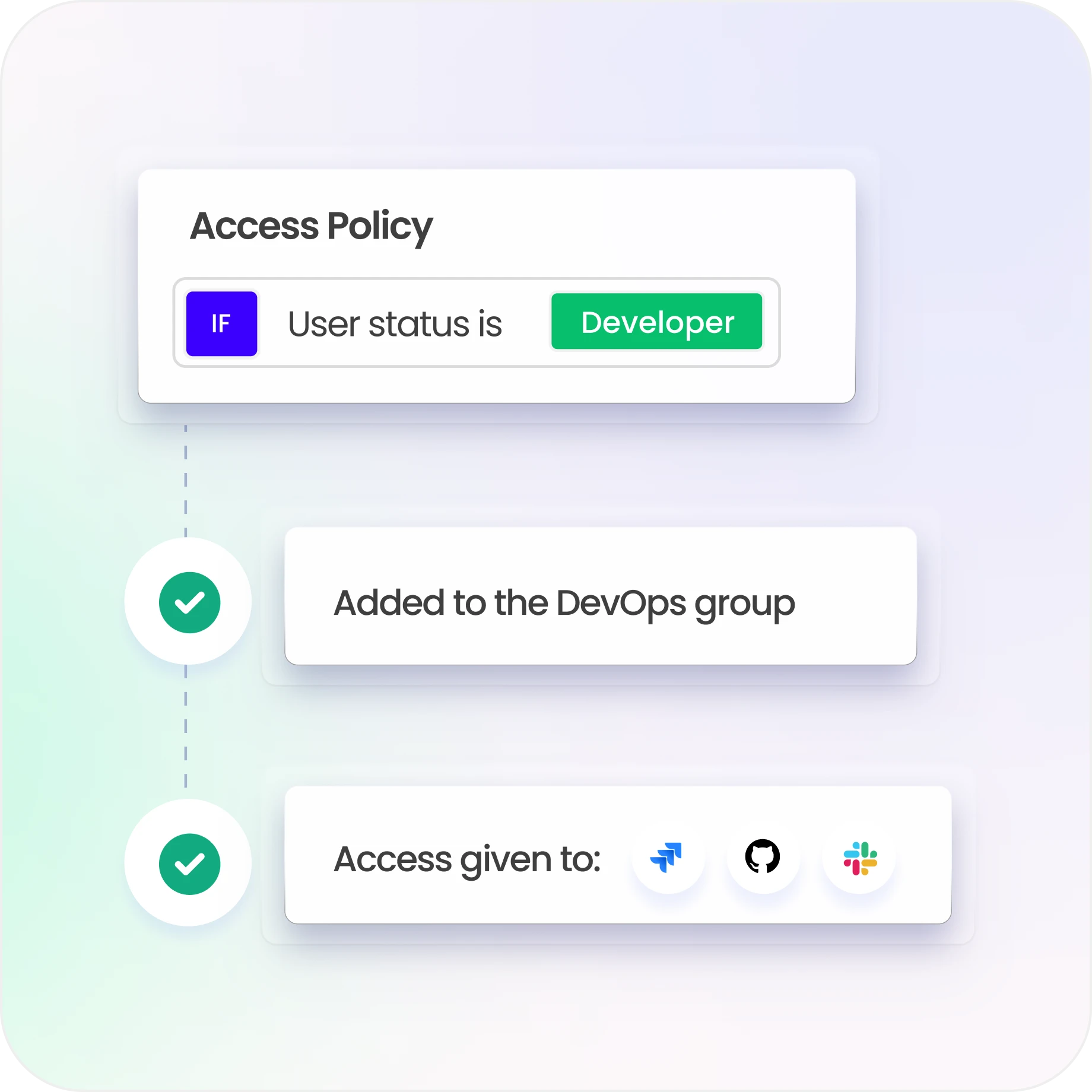
Provision and revoke access via API and connector-based integrations
Deliver real-time visibility into identities and entitlements across apps
Enforce least-privilege using RBAC with attribute-driven policies
Continuously monitor access across enterprise systems for compliance
Identity Governance Built for Modern Manufacturing
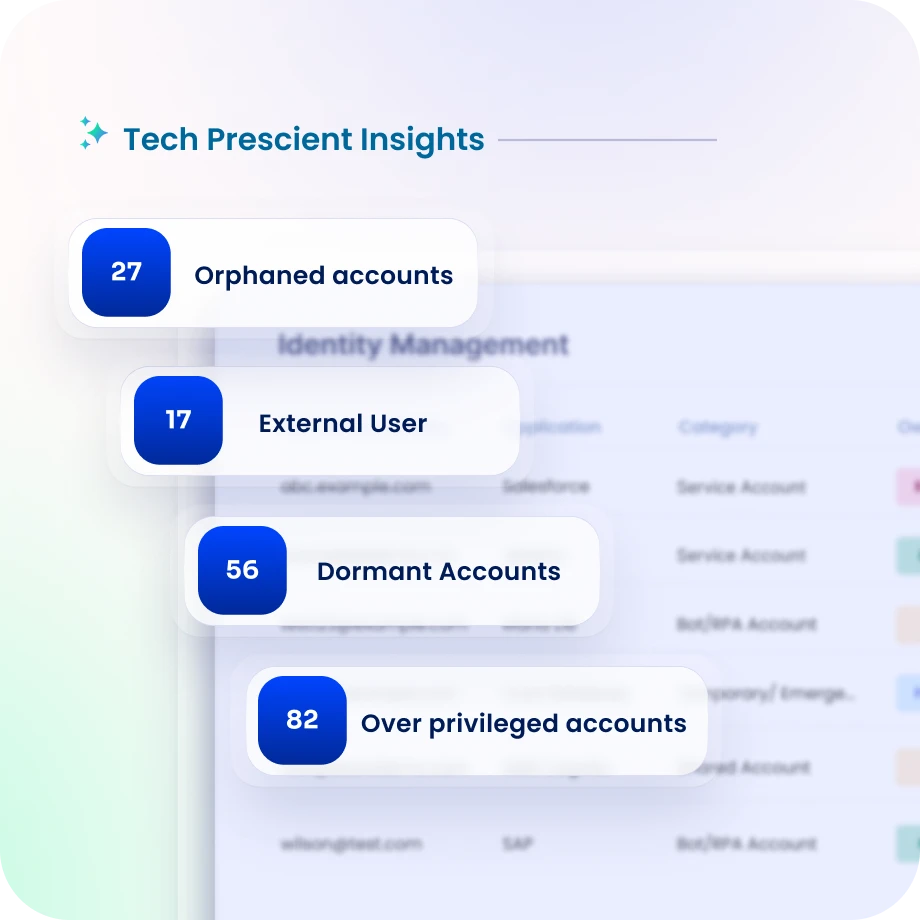
Access Visibility Across Manufacturing Systems
Discover workforce, contractor, and machine identities across IT and OT systems.
Maintain a centralized view of access across plants, ERP, and cloud environments.
Detecting unusual or unauthorized access patterns early.
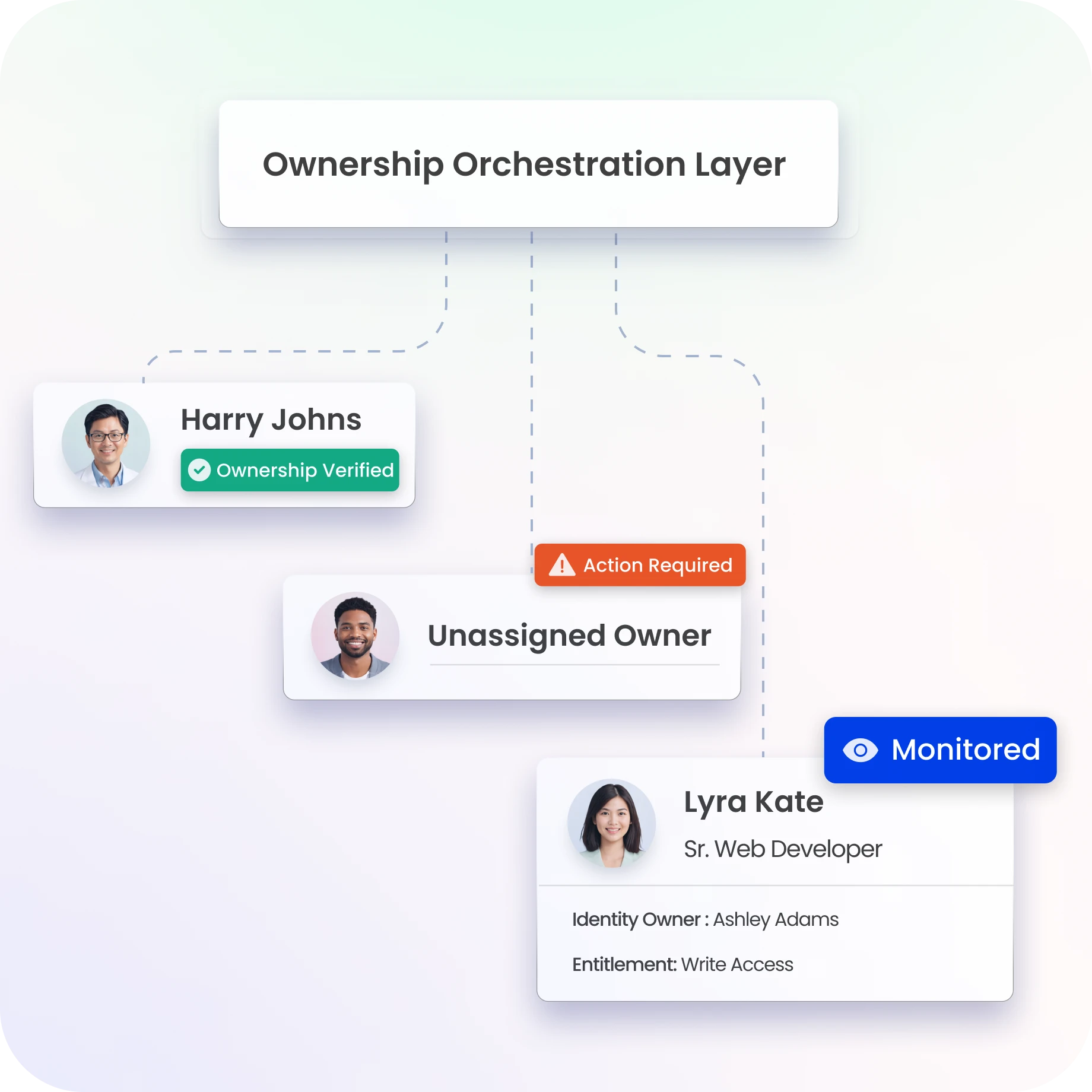
Clear Identity Ownership Across Manufacturing Operations
Link each identity to a responsible owner across departments and facilities.
Receive alerts when ownership changes or becomes unassigned.
Ensure accountability across global manufacturing operations.
Least Privilege Access Across Production Systems
Enforce least-privilege policies aligned with production roles and plant functions.
Identity Confluence removes unnecessary permissions across systems and facilities.
Reduce exposure to ransomware and credential misuse.
Secure Third-Party and Supplier Access
Provide controlled, time-bound access to vendors and contractors.
Maintain visibility into external access across the supply chain.
Reduce third-party risk without slowing collaboration.

Automate Identity Lifecycle Across Facilities
Automate onboarding, transfers, and terminations across HR and plant systems.
Update or revoke access immediately when roles change or contracts end.
Identity Confluence reduces manual workload and operational delays.
Stay Audit-Ready at All Times
Track access certifications, policy enforcement, and SoD controls centrally.
Support SOX, ISO 27001, SOC 2, NIST, and global regulatory requirements.
Maintain audit evidence without manual preparation.

Drive measurable value with Identity Confluence
Download the ROI Report
85%
Fewerorphan accounts
80%
Faster access reviews
90%
Reduced audit findings
Why Teams Choose Identity Confluence
1.
Unified IT and OT Visibility
Govern human and machine identities across production systems, ERP, and cloud systems from one platform.

2.
Policy-Driven Control
Enforce least privilege access consistently across plants, partners, and distributed operations.

3.
Continuous Risk Reduction
Monitor access posture proactively to protect production uptime and sensitive data.



