
Eliminate Identity Risk Across Financial Systems, Stay Audit-Ready
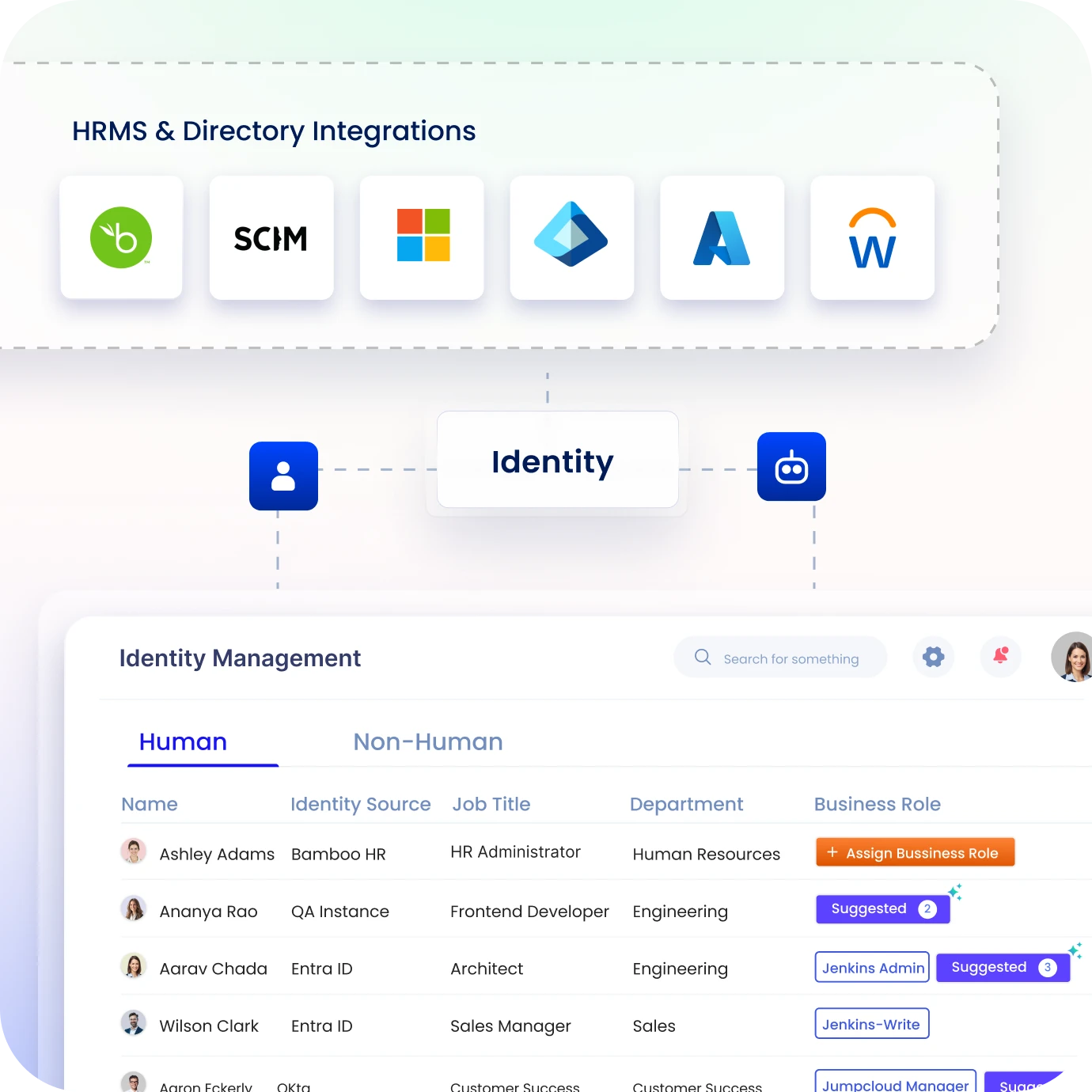
Gain real-time visibility, automate access governance, and enforce least-privilege controls across employees, vendors, and non-human identities, all in one platform.
Trusted by



Your Biggest Compliance Risk Is Not External, It Is Identity Access
Lack of visibility into identity access across financial systems creates excess permissions, orphaned accounts, and audit gaps, increasing the risk of misuse and regulatory non-compliance.
See it in Action →
Secure Financial Systems with Intelligent Identity Governance
Reduce audit preparation time with automated evidence collection.
Eliminate orphaned accounts instantly with lifecycle automation.
Prevent policy violations before they happen with policy enforcement.
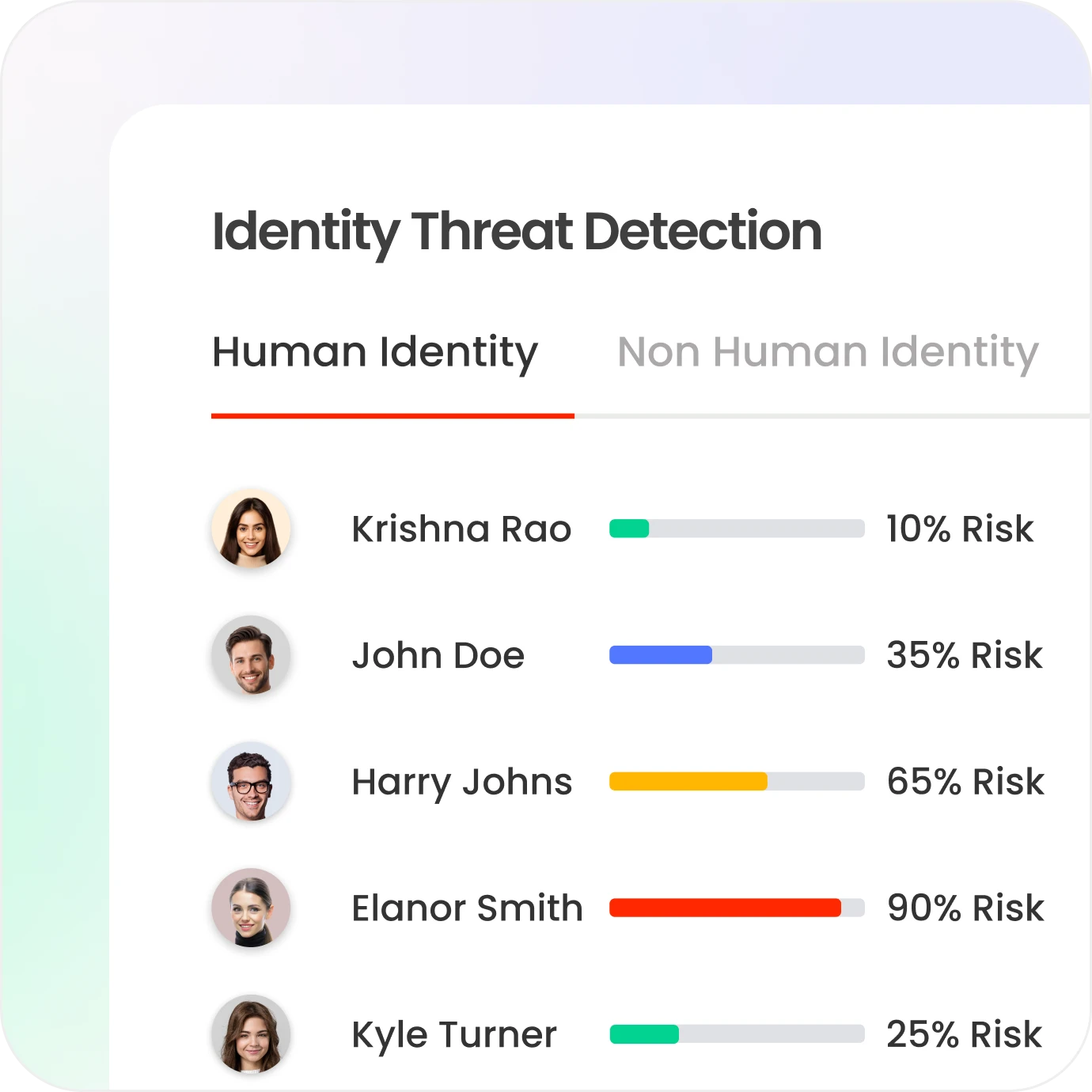
Gain complete visibility across human and non-human identities in one view.
Enforce least privilege at every access point without manual review cycles.
End-to-End Identity Governance for Financial Services
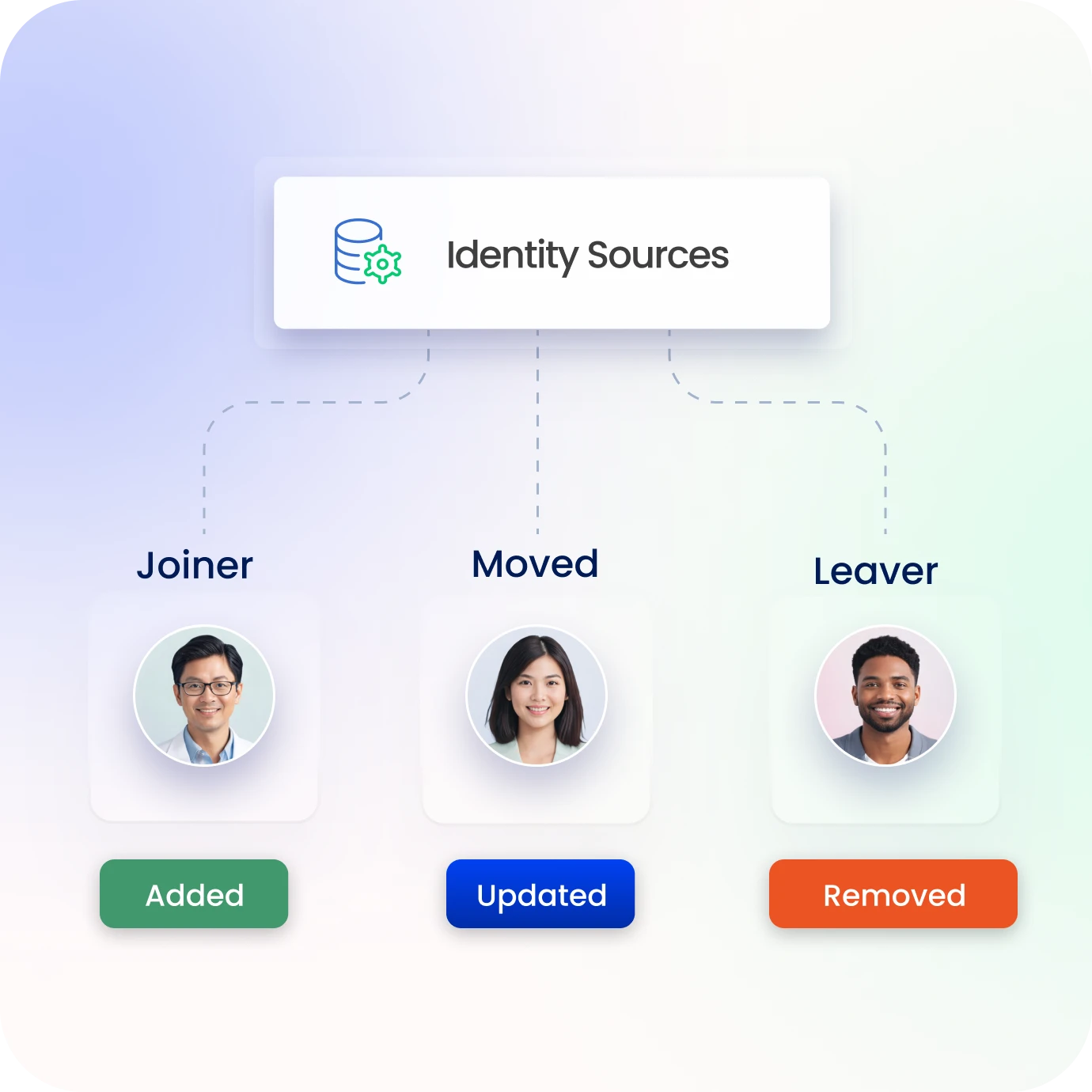
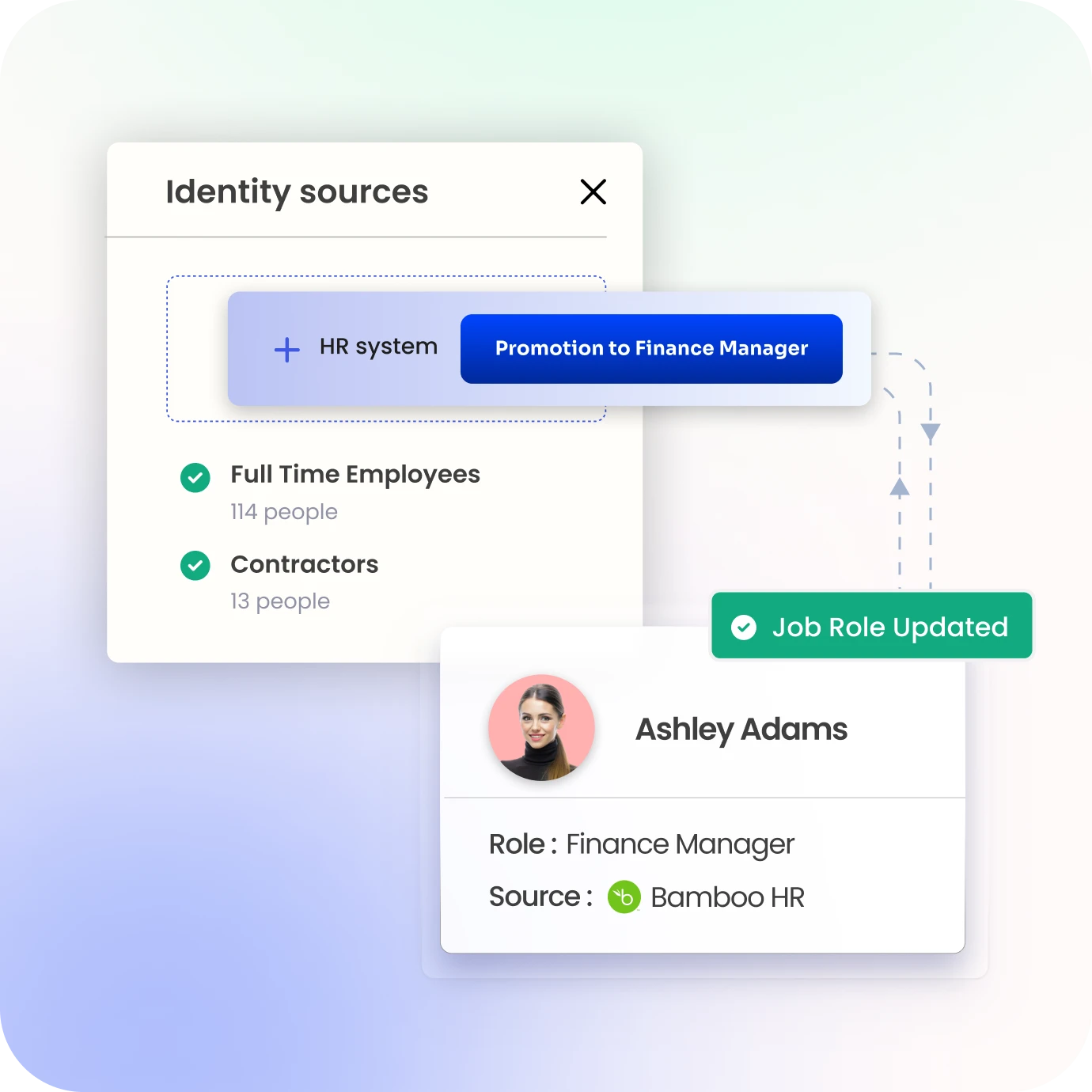
Automate Identity Lifecycle Across Financial Systems
Automate onboarding, role changes, and offboarding with predefined policies.
Ensure least privilege using roles, policies, and regulatory requirements at every stage.
Remove access instantly for leavers, role shifts, or policy violations to reduce risk.
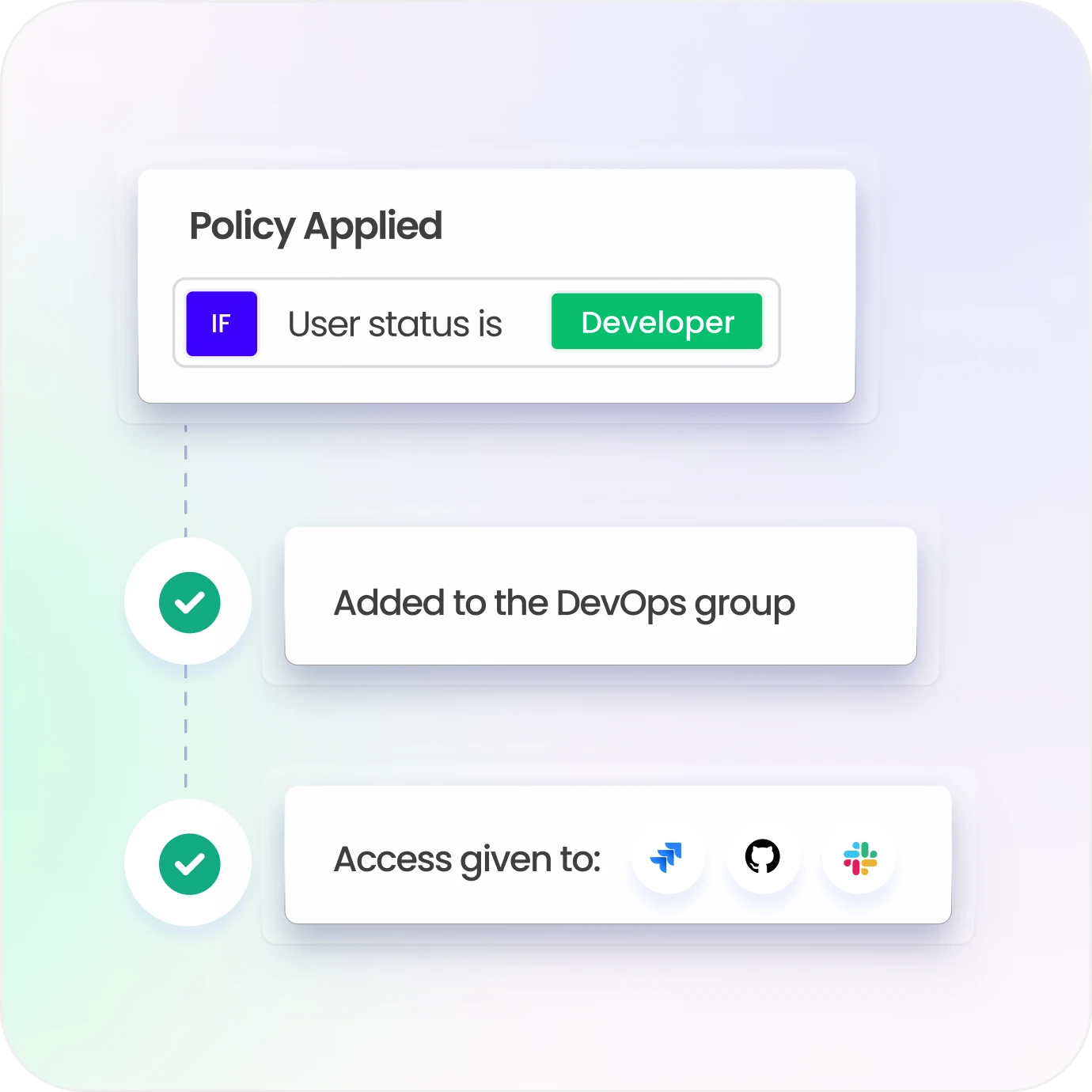
Automate Provisioning with Policy-Based Governance
Provision and deprovision access across systems using predefined governance policies.
Enforce least privilege using role- and attribute-based access models across platforms.
Continuously validate access against policies before granting or updating permissions.
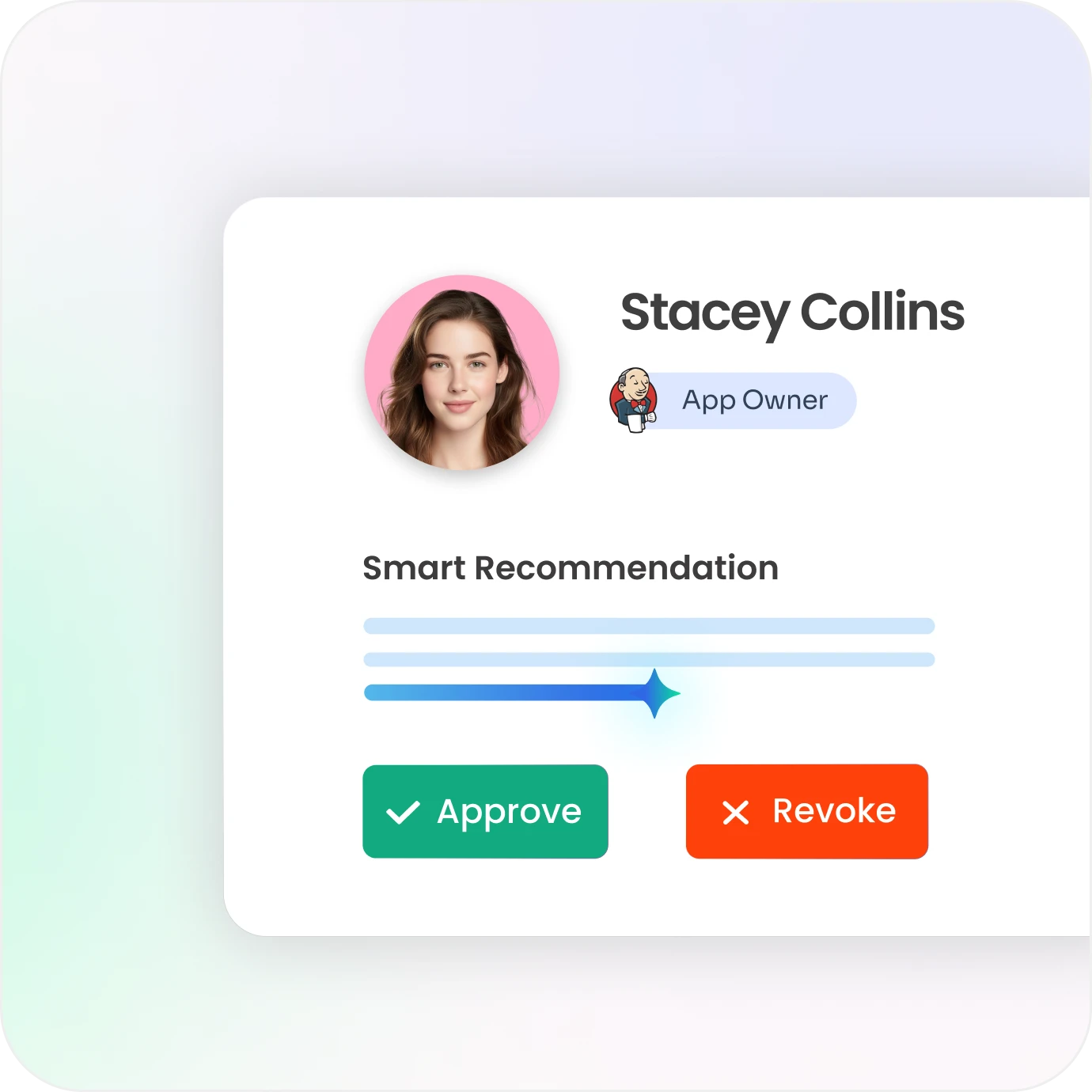
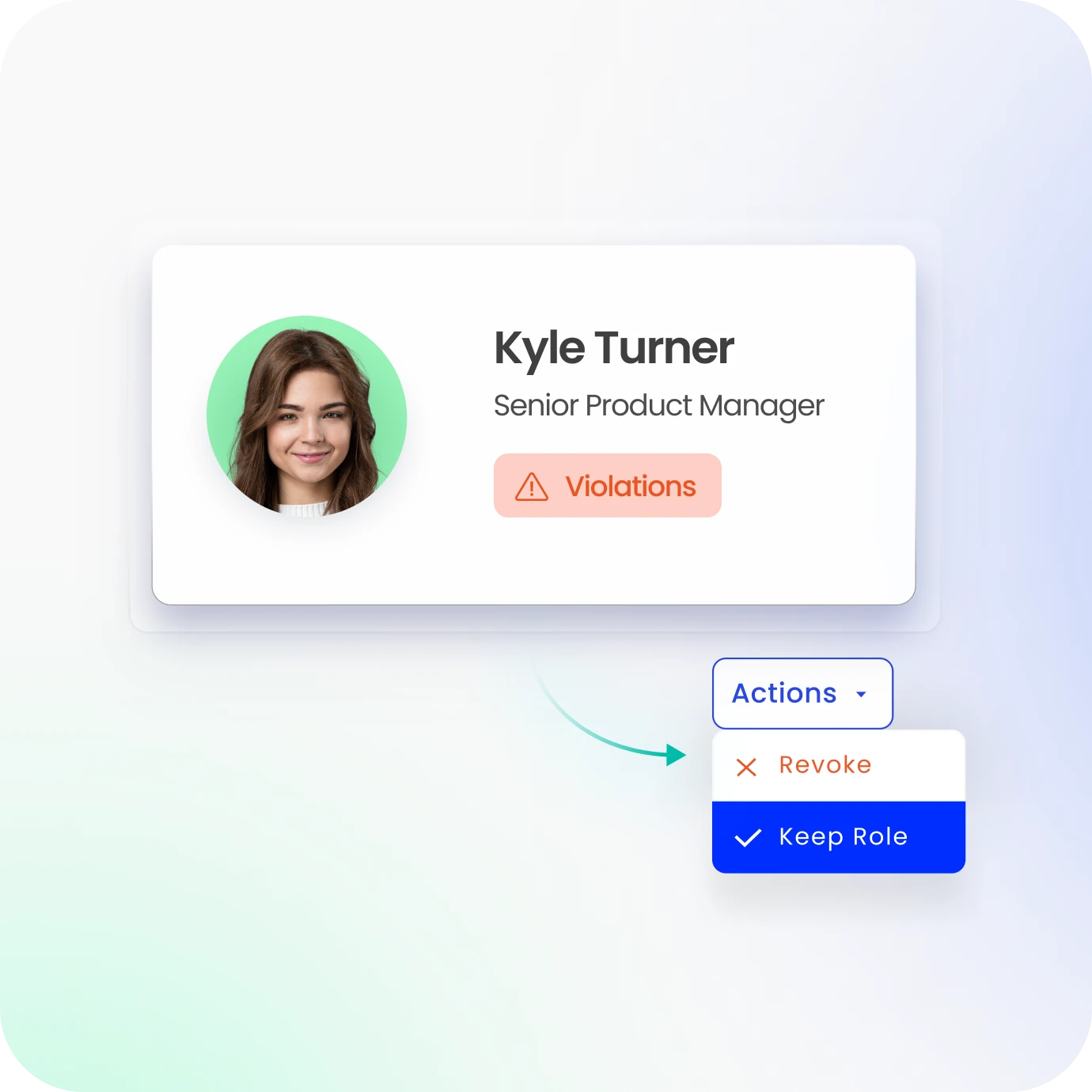
Simplify and Govern Access Certifications
Automate periodic and event-driven access reviews across critical financial systems.
Route certifications to business and risk owners with full access context visibility.
Use risk insights to flag toxic or excessive entitlements for faster decision-making.
Enforce Segregation of Duties Controls
Detect and prevent conflicting access combinations before provisioning occurs.
Continuously monitor SoD violations across users, roles, and entitlements in systems.
Reduce fraud risks by enforcing separation across critical financial operations.
Manage Roles and Entitlements at Scale
Define and manage roles aligned to job functions across banking environments.
Discover and map entitlements across systems for complete access visibility.
Simplify access assignment using role models to reduce manual provisioning effort.
Govern Privileged and High-Risk Access
Apply governance controls to admin and sensitive access across hybrid systems.
Enable just-in-time access and stricter policies for critical financial entitlements.
Continuously monitor privileged usage to detect misuse and reduce exposure risk.

Unify Identity Governance Across Financial Ecosystems
Govern identities across core banking, trading, SaaS, and legacy applications.
Apply consistent governance policies across employees, vendors, and partners.
Centralize governance with streamlined onboarding for applications and systems.
Stay Audit-Ready with Continuous Identity Intelligence
Generate audit-ready reports aligned to financial compliance requirements in minutes.
Track every identity and access change with complete lifecycle traceability.
Provide dashboards and analytics to identify gaps and strengthen governance posture.

Drive measurable value with Identity Confluence
Download the ROI Report
90%
Faster access review cycles
85%
Reduced orphaned accounts
3-5x
faster audit readiness
Why Identity Confluence Is Different
1.
Policy-First Architecture
Access policies are directly aligned to regulatory frameworks, keeping financial compliance continuously in check.

2.
Regulator-Ready by Design
Every access change is logged, validated, and exportable for audit defense without manual reconciliation.

3.
Unified Financial IT Governance
Consistent identity controls across core banking, trading, cloud, SaaS, and partner systems from a centralized framework.



