
Accelerate Technology Innovation with Secure Identity Governance
Secure users, applications, and systems while enabling fast product development and seamless access across cloud environments.
Trusted by



Identity Complexity Slows Innovation and Growth
Tech teams manage users, applications, and machine identities. Manual provisioning, fragmented access controls, and poor visibility increases complexity and slows development.
See it in Action →
Accelerate Growth with Unified Identity Governance
Manage identities, entitlements, and access across systems
Automate identity lifecycle and access workflows
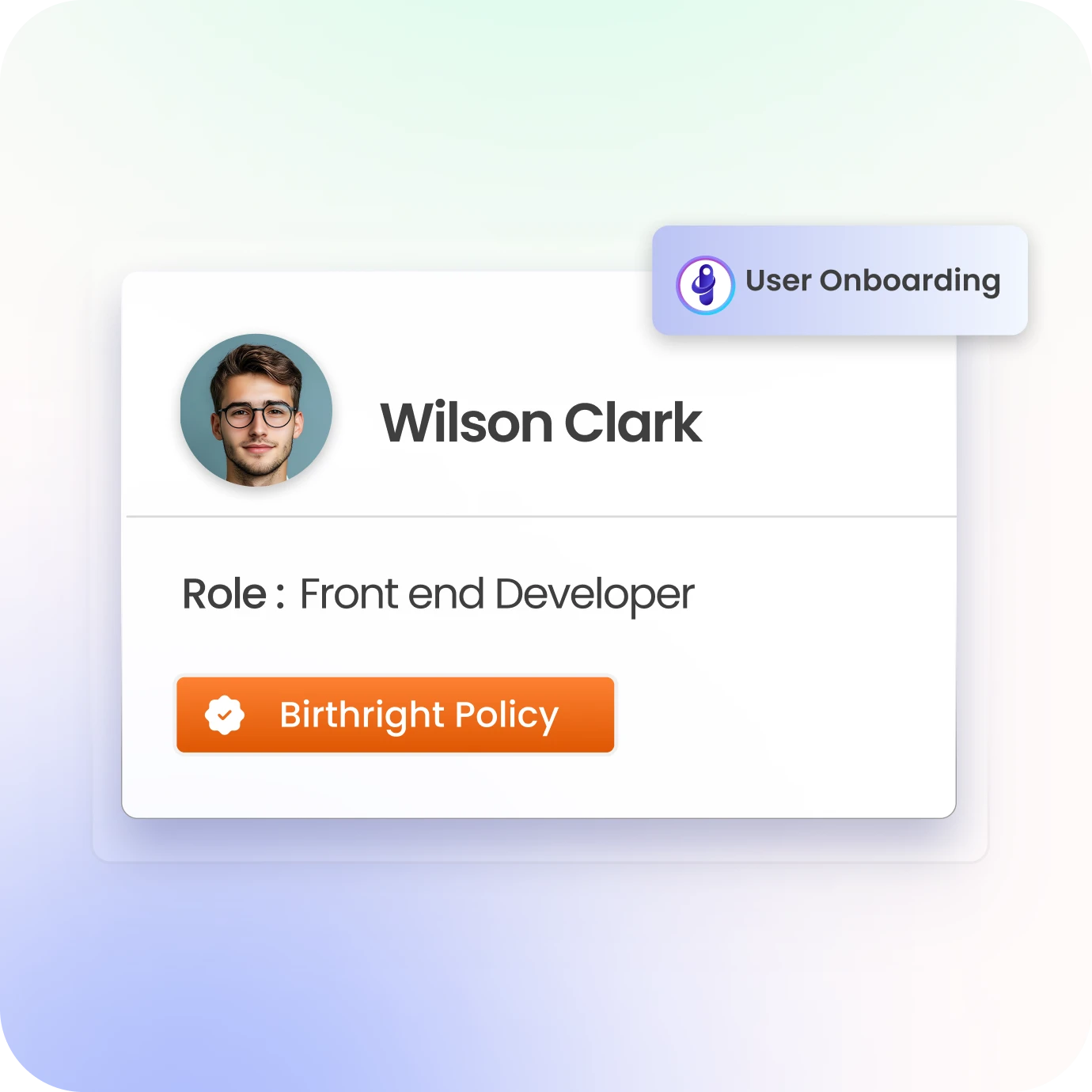
Accelerate onboarding and secure product access
Enforce access policies without slowing development
Enable scalable, cloud-first identity governance
Identity Governance Capabilities for Technology Innovation
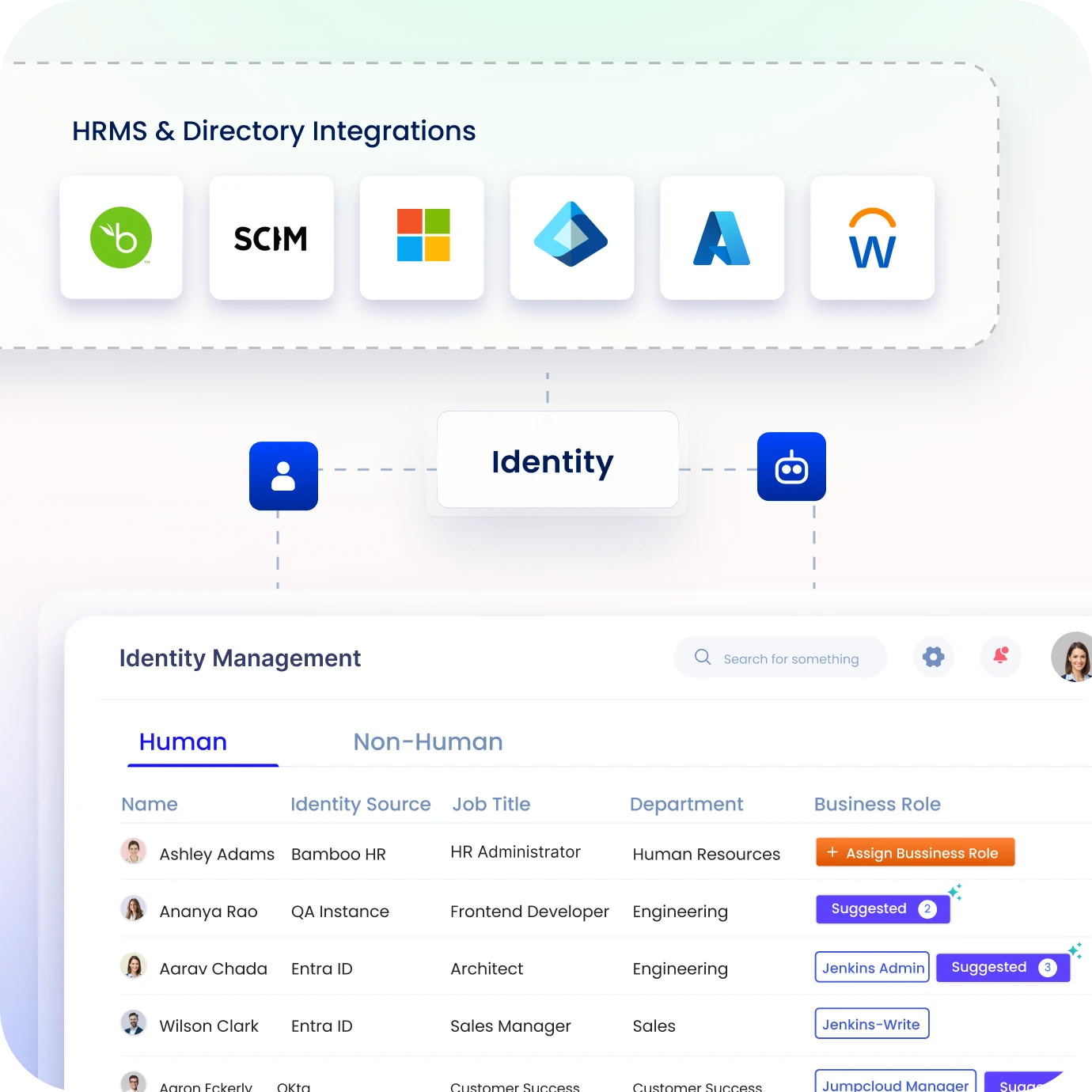
Access Visibility Across Users & Applications
Discover workforce, customer, and system identities across environments.
Maintain centralized visibility across cloud, apps, infrastructure, and entitlements.
Improve control and reduce identity-related complexity.
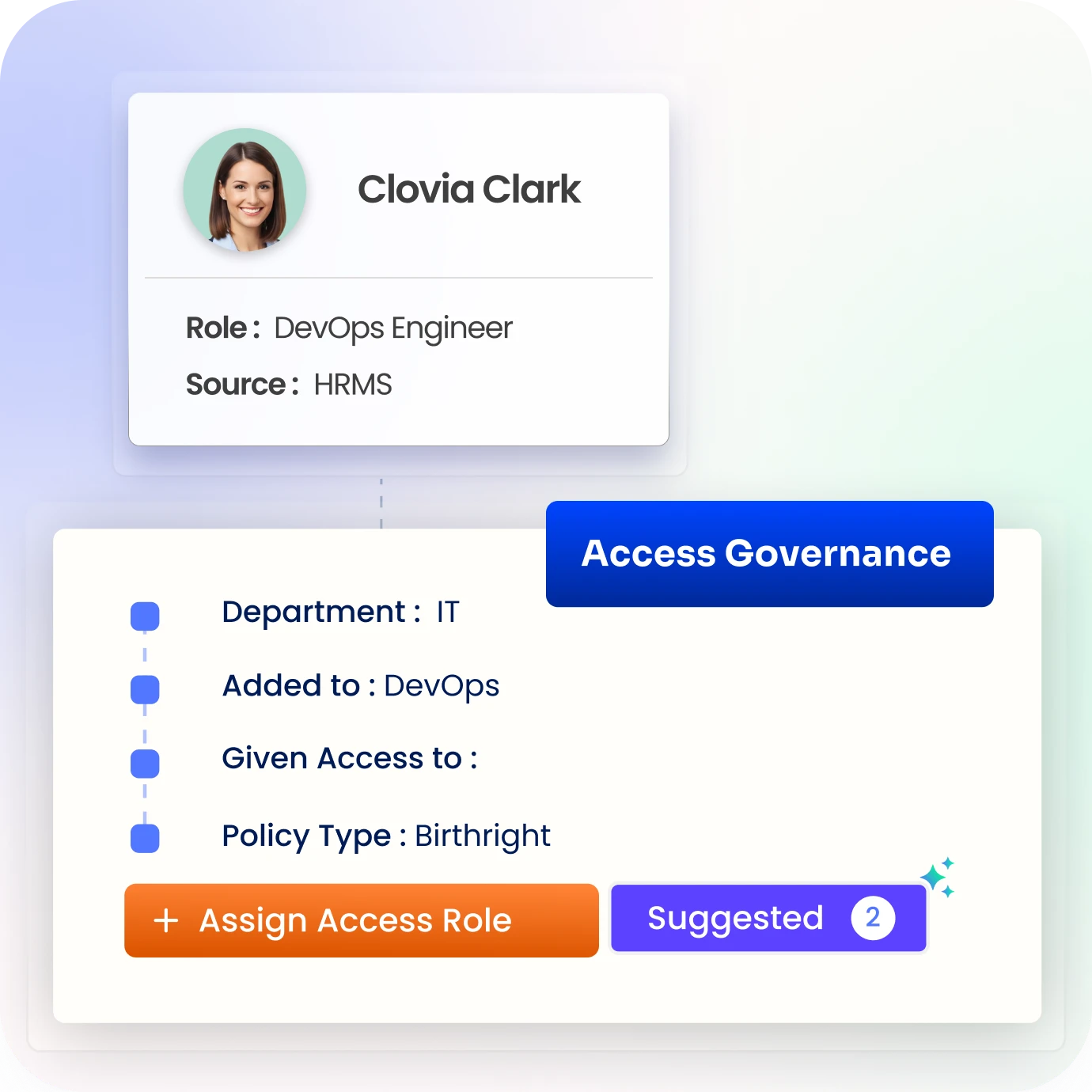
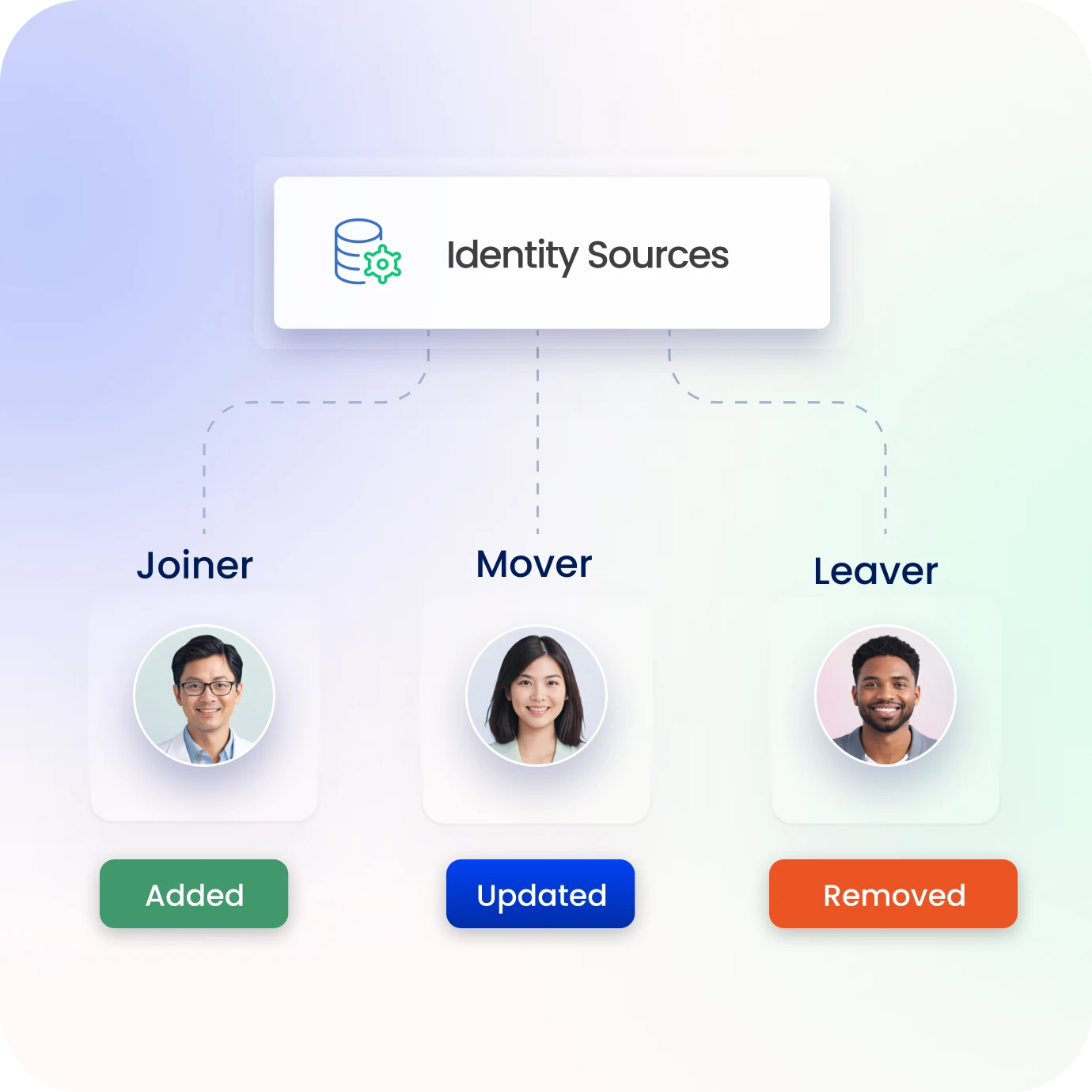
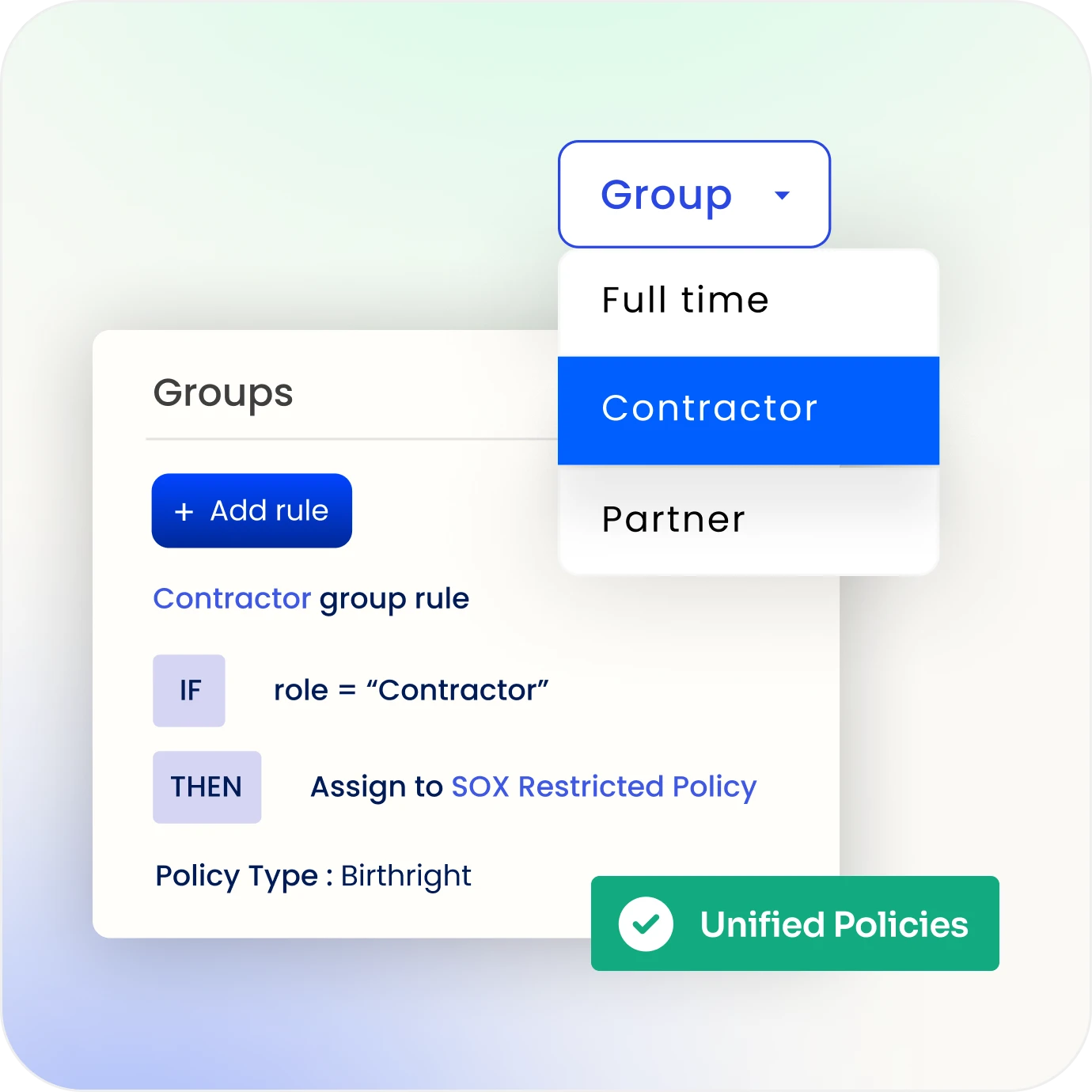
Identity Lifecycle Automation for Faster Development
Identity Confluence automates onboarding, access, and lifecycle changes.
Update access and entitlements dynamically as users and roles evolve.
Reduce manual work and accelerate product and IT operations.
Secure Authentication & Access Controls
Protect access with strong authentication, policy controls, & least privilege enforcement.
Enable secure login across applications and platforms.
Reduce unauthorized access and identity-related risk.
Scalable Identity Governance for Cloud Environments
Manage identity across cloud, SaaS, and hybrid environments.
Support rapid growth without increasing operational overhead.
Ensure consistent access policies and governance across systems.
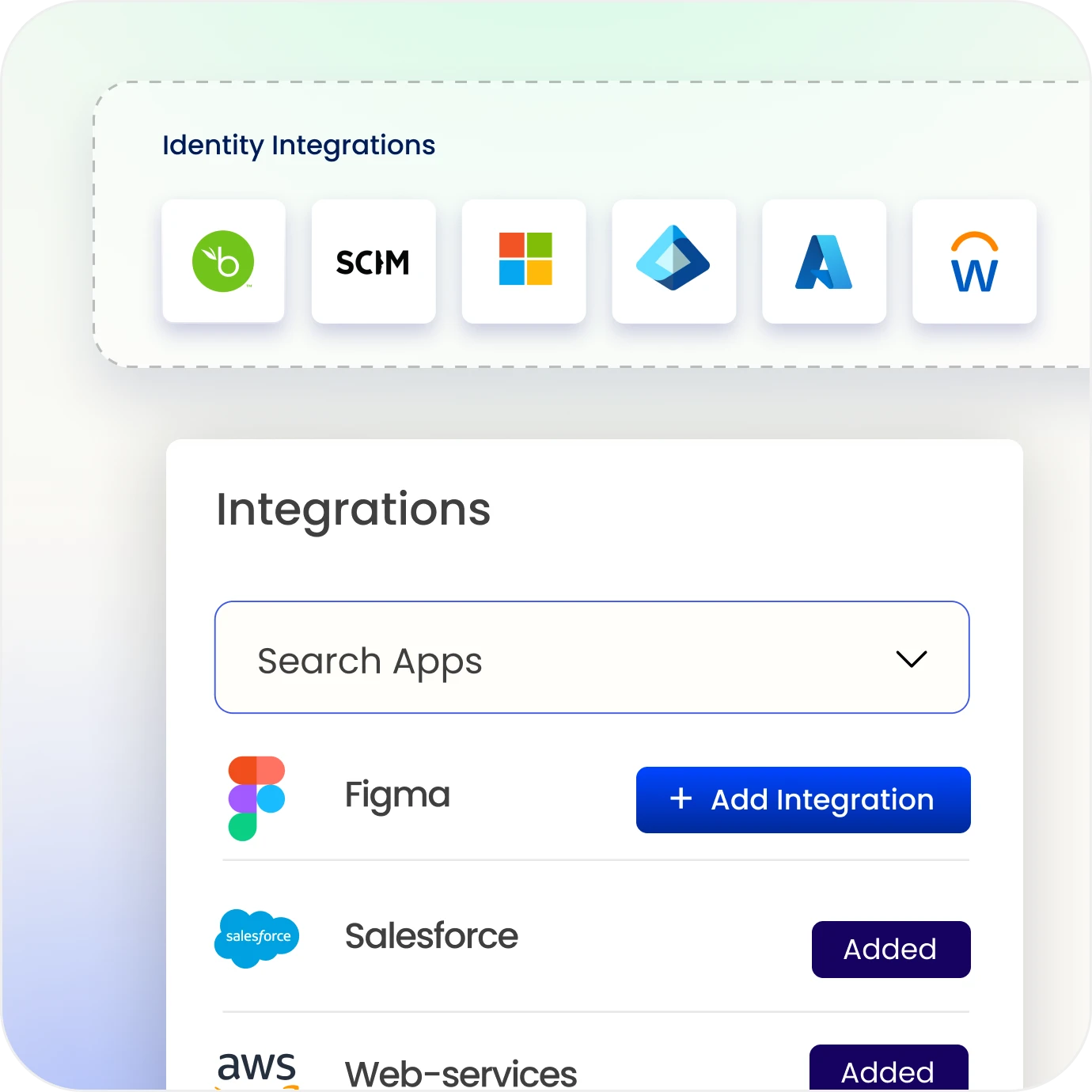
Developer-Friendly Identity Integration
Integrate identity, access, and entitlements across applications and APIs easily.
Enable teams to build secure products without complexity.
Accelerate development while maintaining security controls.
Drive measurable value with Identity Confluence
Download the ROI report
3-5x
ROI
within first 12 months
80%
Faster product onboarding
86%
Reduced operational complexity
Why Teams Choose Identity Confluence?
1.
Unified Identity Platform
Manage users, applications, identities, and entitlements from a centralized platform to reduce complexity and improve visibility.

2.
Automation-Driven Efficiency
Automate identity lifecycle, access provisioning, and workflows to reduce manual effort and accelerate product and IT operations.

3.
Scalable Identity Architecture
Support cloud-first growth and rapid expansion with consistent access policies and governance across environments.



