
Identity Governance That Gives CISOs Real Control Over Risk
Automate identity lifecycle, enforce least privilege, run intelligent certifications, and maintain full visibility to reduce enterprise risk.
Trusted by



Weak Identity Governance is Increasing Enterprise Risk
CISOs manage thousands of human & NHIs across all systems. Without centralized governance, privilege creep grows, certifications stay manual, SoD violations go unseen, and compliance becomes costly.
See How it Works →

Turn Identity Security Into a Strategic Control Layer
Gain full visibility into every identity, entitlement and access path
Enforce least privilege and policy-driven access across every identity
Automate identity lifecycle to eliminate manual provisioning and delays
Run intelligent, risk-based certifications with SoD conflict detection
Maintain continuous compliance with real-time audit trails and evidence
Enterprise Identity Governance Built for CISO Priorities
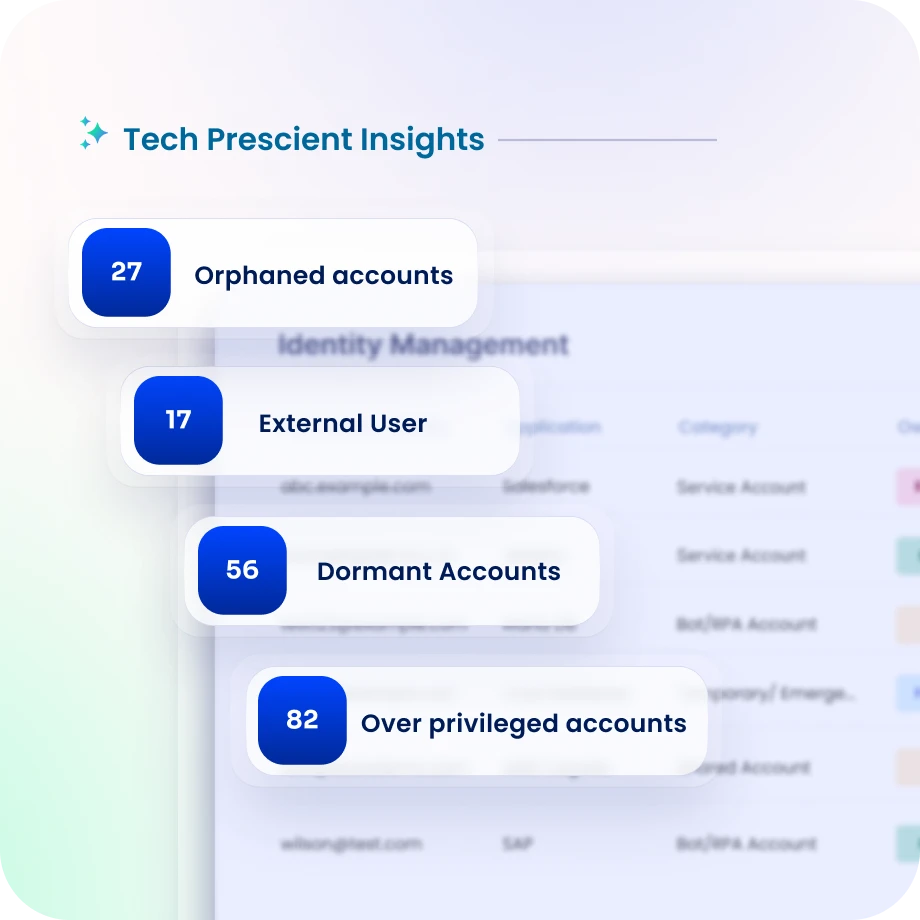
Complete Identity Visibility for Risk Oversight
Discover workforce, contractor, and non-human identities across all enterprise systems.
Maintain real-time visibility into entitlements, ownership, and access paths.
Identity Confluence detects unusual or unauthorized access patterns before they escalate.
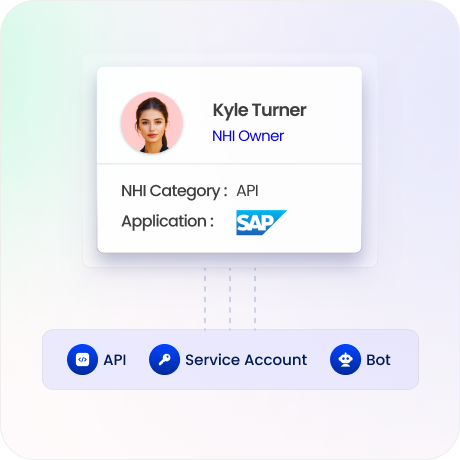
Ownership and Accountability Across Every Identity
Automatically assign and track business owners for every identity and entitlement.
Receive alerts on unassigned or stale ownership to maintain governance accountability.
Maintain accountability across departments, teams, and enterprise systems.

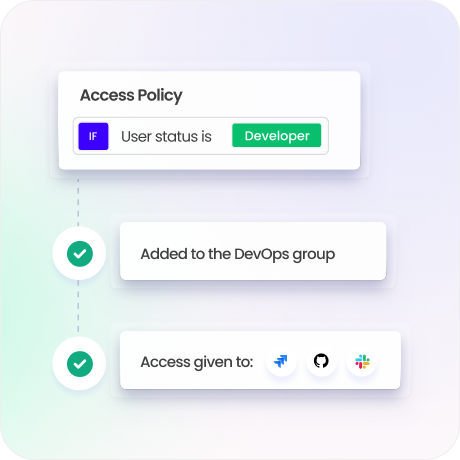
Least Privilege Enforcement at Scale
Enforce least-privilege policies using RBAC, ABAC, and dynamic rules.
Remove excessive permissions and reduce identity-related attack surfaces.
Minimize insider threats and credential misuse across the enterprise.
Privileged Access Security for Critical Systems
Secure administrative and high-risk access across infrastructure and applications.
Maintain visibility into privileged entitlements and usage patterns.
Reduce lateral movement risk and privilege escalation opportunities.
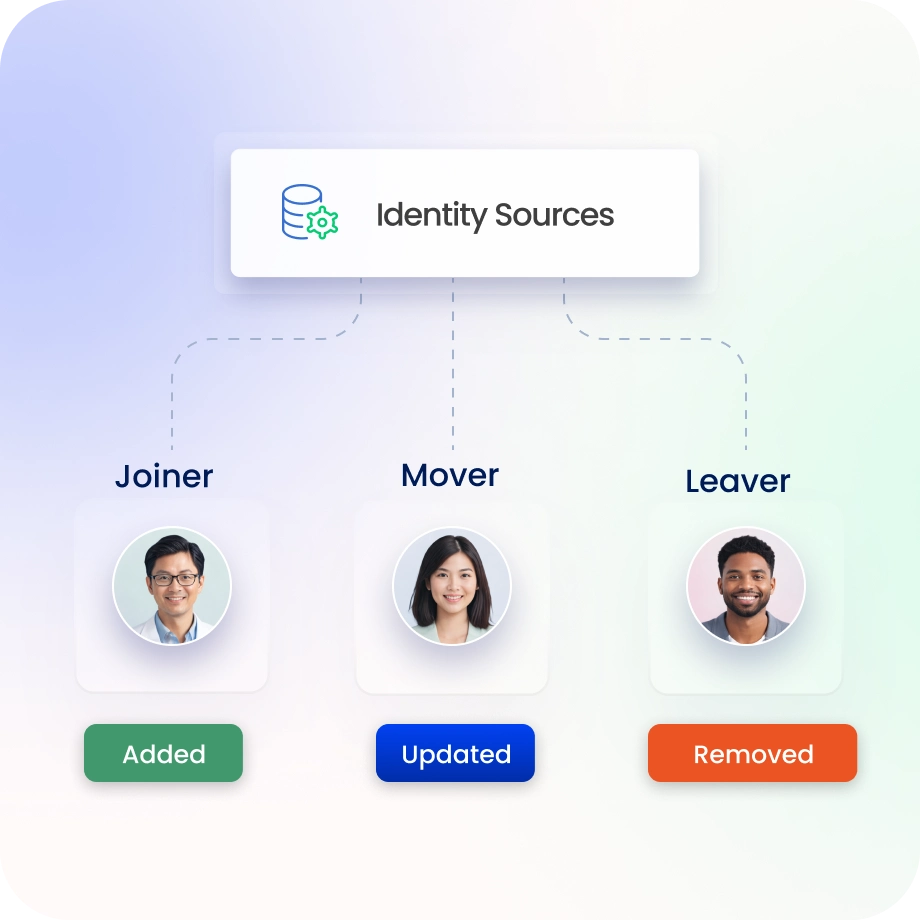
Automated Identity Lifecycle Controls
Automate onboarding, role changes, and offboarding with policy-driven workflows.
Ensure access updates automatically as roles and responsibilities evolve.
Eliminate manual provisioning delays and orphaned accounts.
Continuous Compliance and Audit Readiness
Track certifications, policies, and SoD controls in real time.
Generate audit-ready evidence aligned to ISO 27001, SOC 2, NIST, and GDPR.
Simplify compliance reporting and reduce audit preparation effort.

Drive measurable value with Identity Confluence
Download the ROI Report
100%
visibility across all human & non-human identities
Zero
orphaned identities across the enterprise
3-5x
ROI
within the first year
Why Teams Choose Identity Confluence
1.
Unified Identity Visibility
Get a centralized view of workforce, contractor, and machine identities across your entire enterprise.

2.
Policy-Driven Security
Automate policy enforcement with built-in SoD conflict detection and remediation.

3.
Continuous Risk Reduction
Use AI-driven insights, automated certifications, and real-time evidence for proactive security.



