Strengthen Compliance and Reduce Risk with Identity Governance
Gain full visibility into access, enforce policy-driven controls, and maintain continuous audit readiness with automated identity governance across all systems.
Trusted by



Lack of Visibility Increases Compliance Risk
Compliance teams lack visibility into access decisions & supporting evidence. Manual reviews, incomplete records, & inconsistent documentation make it difficult to justify access, increasing compliance risk.
See It in Action →

Turn Identity into a Control Layer for Compliance
Gain complete visibility into identities, entitlements, and access paths
Enforce policies automatically with SoD controls and least-privilege access
Automate access reviews and certifications with audit-ready traceability
Detect and remediate risks early before they impact compliance
Maintain continuous audit readiness across all systems and environments
Controls for Continuous Compliance and Audit Readiness
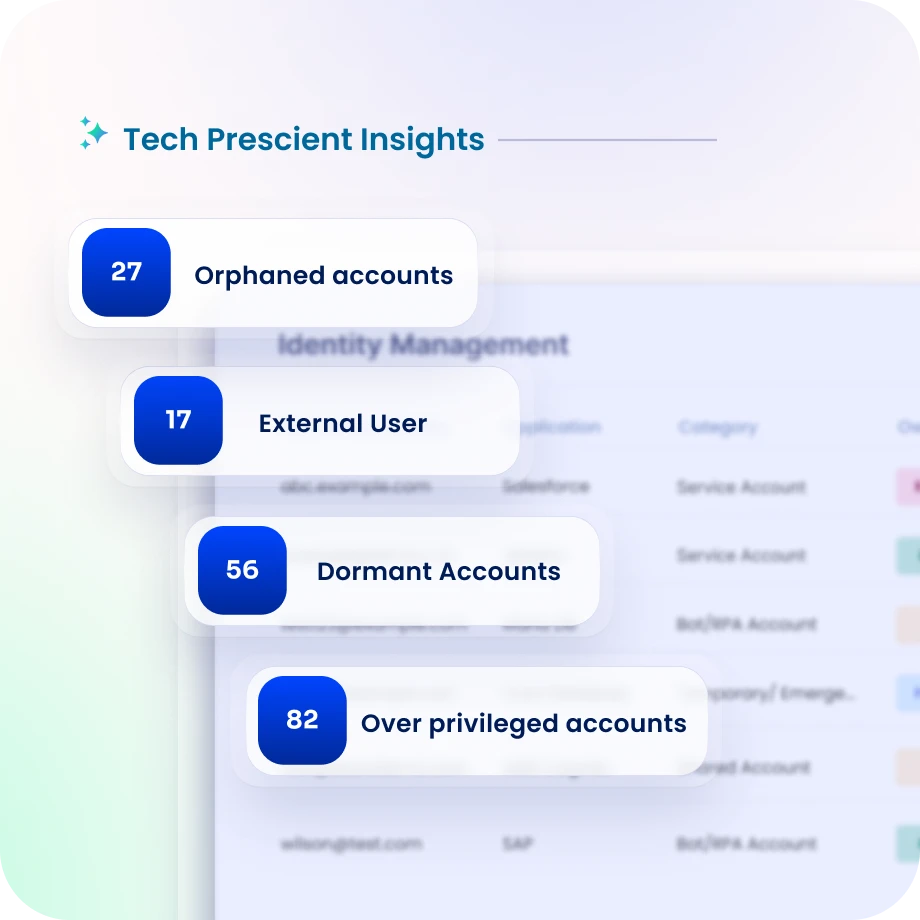
Gain Visibility for Compliance Monitoring
Discover workforce, contractor, and external identities across environments.
Maintain a unified view of applications, entitlements, and sensitive systems.
Detect policy violations and unusual access patterns early.
Enforce Policy-Driven Access Governance
Define and enforce access policies across all systems and identity types.
Prevent violations with automated SoD controls and risk-based access rules.
Ensure consistent enforcement of compliance standards across environments.
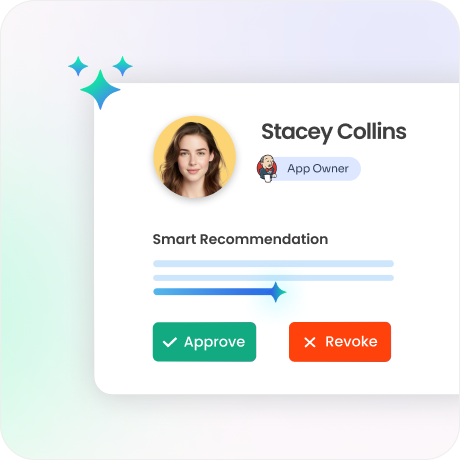
Automate Access Reviews & Certifications
Identity Confluence Automate certification campaigns with intelligent recommendations.
Improve accuracy and reduce manual review effort significantly.
Maintain audit-ready validation records at all times.
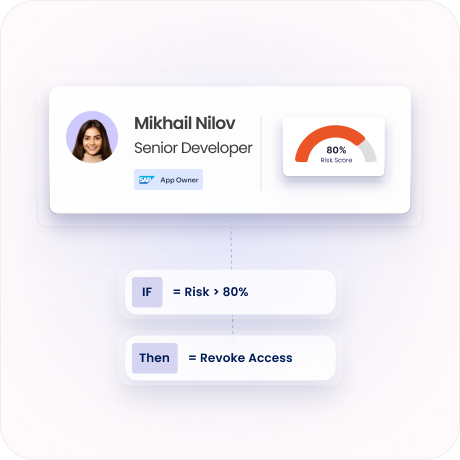
Detect and Reduce Identity Risk Exposure
Identify entitlement misuse, access risks, and anomalous behavior early.
Continuously assess identity posture across systems and applications.
Trigger automated remediation to reduce risk exposure.
Enforce Least Privilege and JIT Access
Enforce least privilege across users, applications, and systems.
Grant time-bound access using Just-in-Time controls instead of standing privileges.
Reduce exposure from excessive and unnecessary access.

Continuous Compliance and Audit Readiness
Track certifications, audit logs, access decisions, and policy enforcement centrally.
Support SOX, ISO 27001, GDPR, HIPAA, and global compliance frameworks.
Maintain complete audit-ready evidence with full access history.

Drive measurable value with Identity Confluence
Download the ROI Report
90%
automated certifications
85%
faster audit readiness
75%
reduced compliance risk
Why Teams Choose Identity Confluence
1.
Unified Compliance Visibility
Get a centralized view of identities, entitlements, and access policies to improve audit oversight.

2.
Policy-Driven Governance
Automate policy enforcement with built-in SoD controls and least-privilege access.

3.
Continuous Audit Readiness
Maintain real-time visibility into access decisions, certifications, and compliance evidence.



