
Secure DevOps Pipelines Without Slowing Deployments
Enable DevOps teams to build, deploy, and scale securely across pipelines, cloud and applications.
Trusted by



Manual Access Slows DevOps and Increases Risk
DevOps teams manage access across pipelines, cloud, and workloads. Manual provisioning, static credentials, and poor visibility increase risk and slow deployments.
See It in Action →
Secure and Automate Identity Across DevOps Workflows
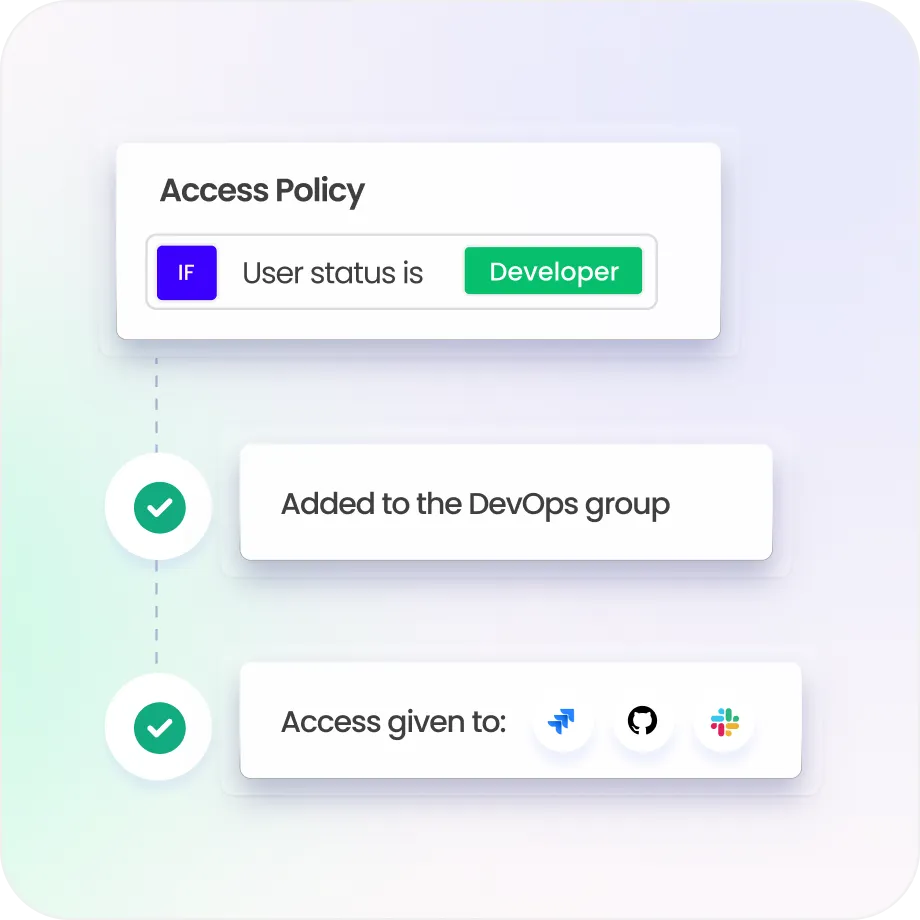
Automate identity lifecycle across CI/CD pipelines and environments
Enforce least privilege and policy-based access for every identity type
Replace static credentials with governed, time-bound access controls
Detect identity risks and anomalous activity across pipelines in real time
Enable fast, secure deployments with governed access controls
Identity Controls Built for DevOps Speed and Security
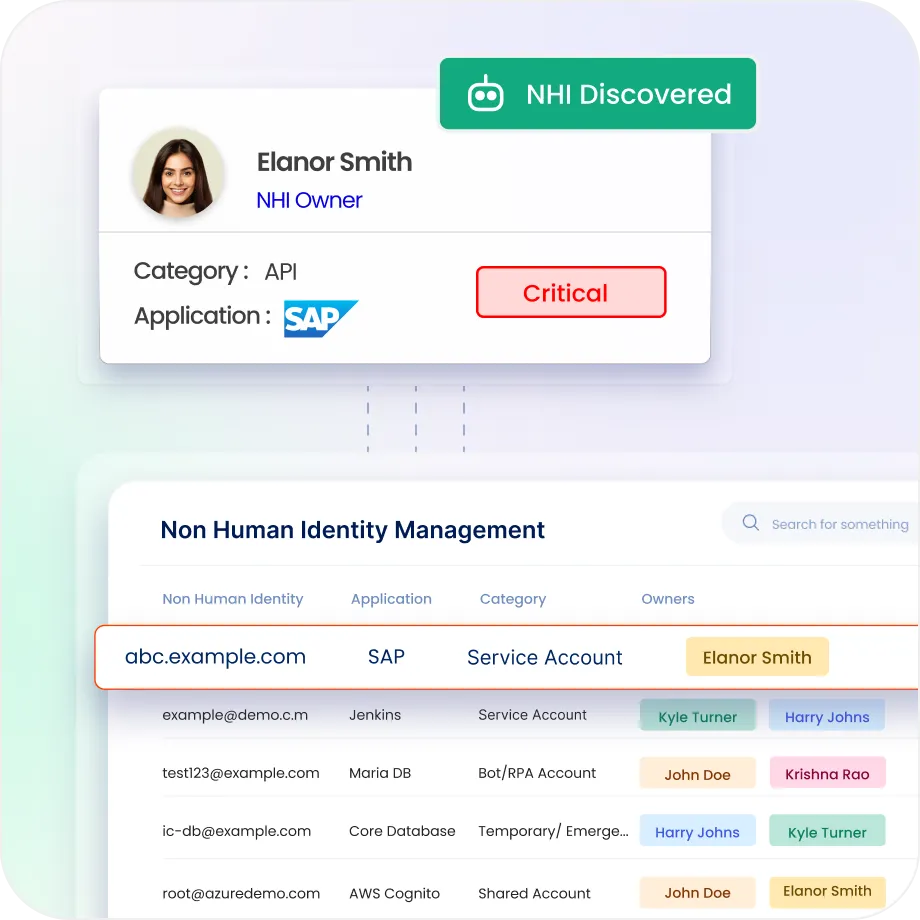
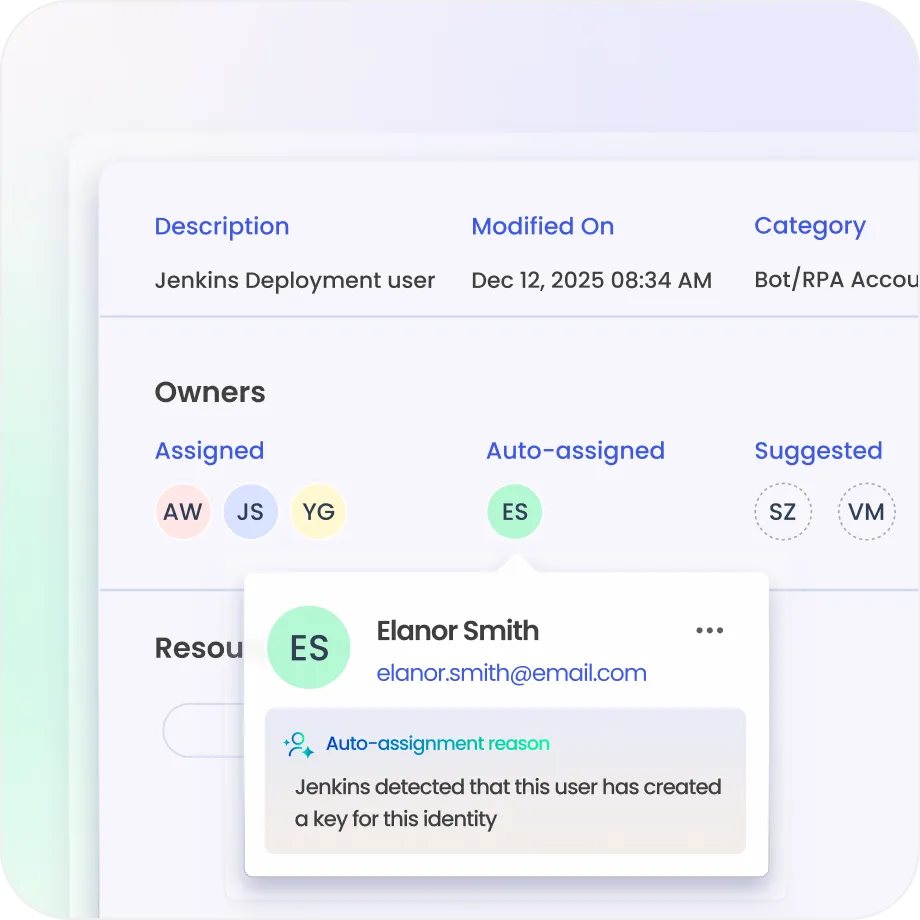
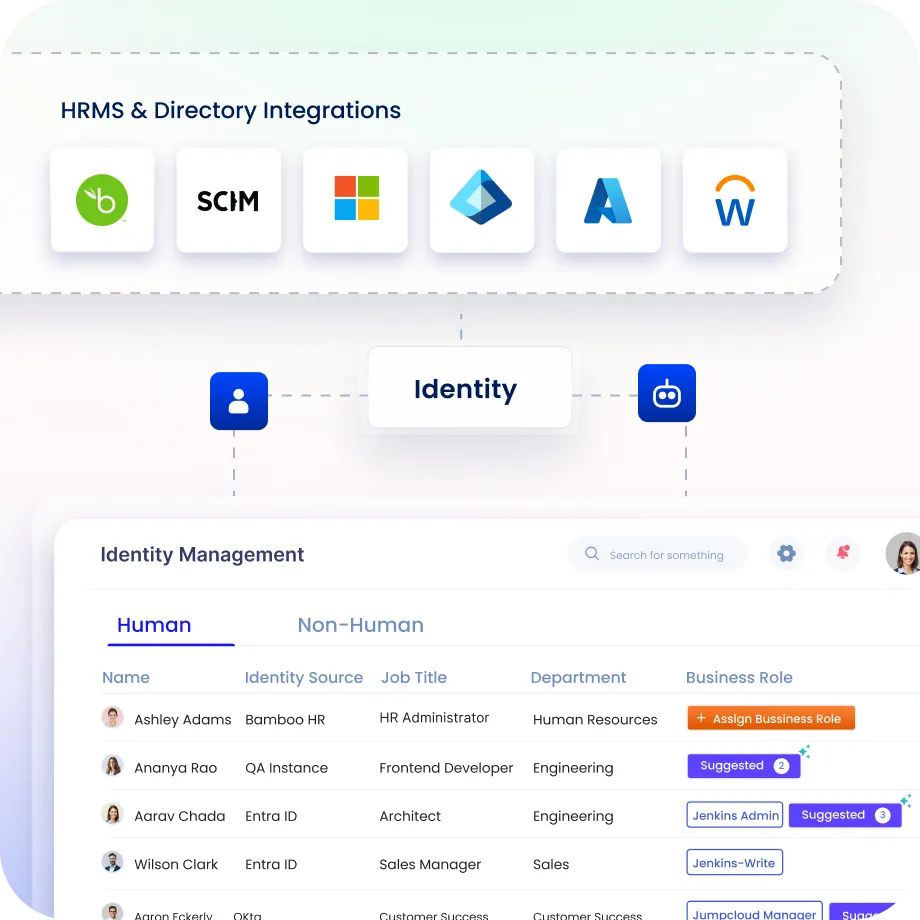
See Every DevOps Identity
Discover developers, workloads, and machine identities across systems.
Maintain visibility across pipelines, cloud, infrastructure, and entitlements.
Identify hidden identities, tokens, and access risks early.
Secure Secrets and Privileged Access
Protect credentials, API keys, and privileged access centrally.
Control access to repositories, pipelines, infrastructure, and sensitive entitlements.
Reduce risk of credential leakage and misuse.
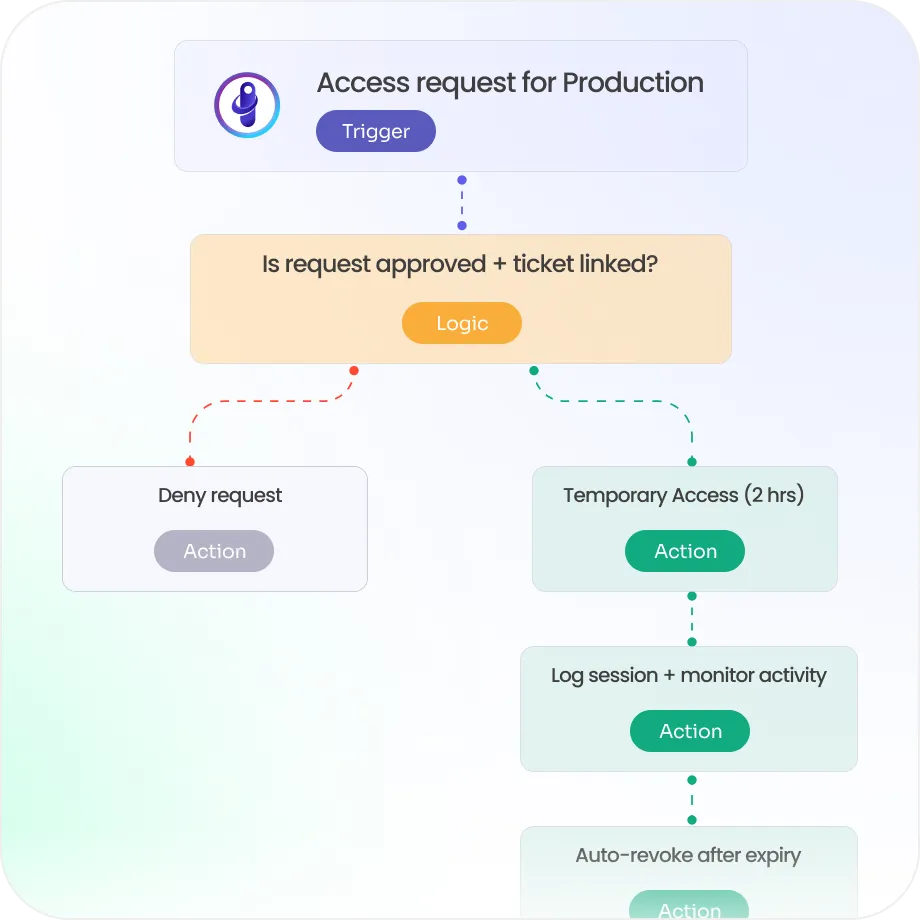
Enforce Least Privilege and JIT Access
Grant time-bound access using Just-in-Time controls instead of standing access.
Eliminate standing access across pipelines and infrastructure.
Reduce risk while enabling fast deployments.

Automate Identity Across CI/CD Workflows
Identity Confluence automates access across pipelines and environments.
Provision, adjust, and revoke access dynamically across deployment lifecycles.
Reduce manual approvals and accelerate release cycles.
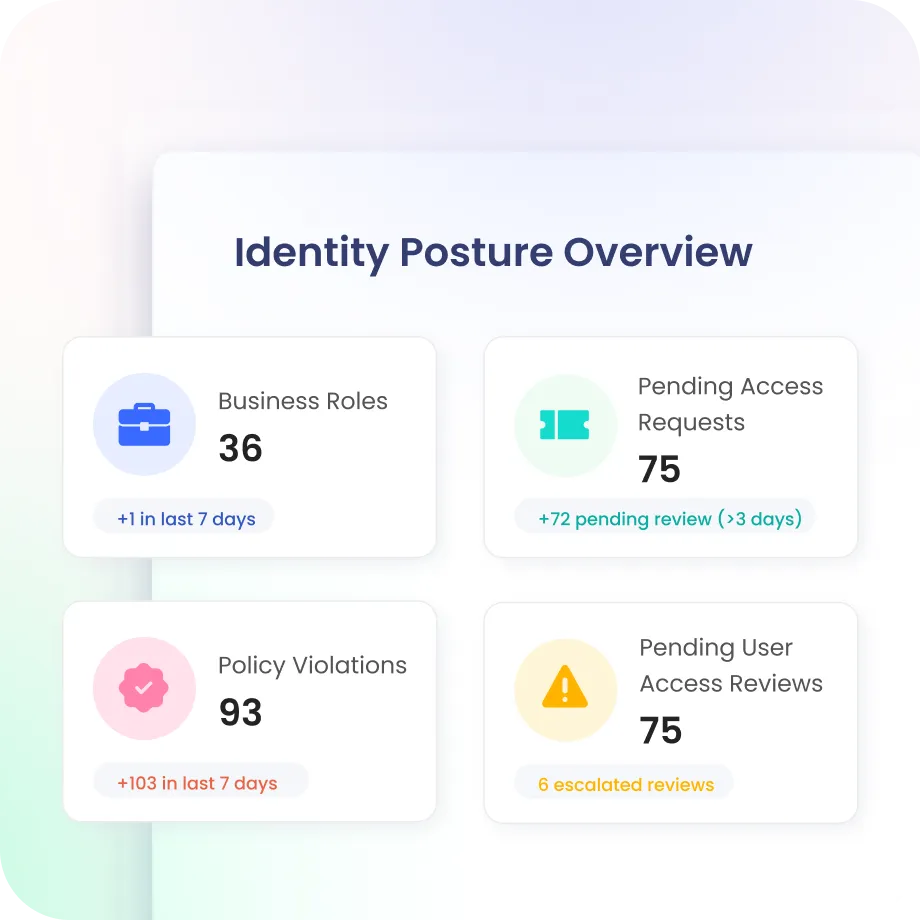
Detect and Reduce DevOps Identity Risk
Continuously assess identity posture across pipelines, workloads, and systems.
Detect anomalies, risky access, and policy violations early.
Trigger automated remediation across pipelines and infrastructure.
Govern Cloud, Containers, and IaC
Manage identity, access, and entitlements across cloud, containers, and IaC environments.
Support Kubernetes, APIs, and dynamic infrastructure.
Scale identity controls as systems and deployments grow.
Drive measurable value with Identity Confluence
Download the ROI Report
80%
Faster secure deployments
87%
Reduced credential exposure
90%
Automated access workflows
Why Teams Choose Identity Confluence
1.
Pipeline-Native Identity Control
Secure and govern access across CI/CD pipelines, cloud, and infrastructure without slowing development workflows.

2.
Automated and Ephemeral Access
Enforce least privilege with Just-in-Time access and dynamic lifecycle controls for developers and workloads.

3.
Unified Identity for DevOps Environments
Govern human, non-human, and machine identities with centralized visibility, policies, and control across environments.



