
Be Audit-Ready at all Times, Without Manual Effort
Automate audit evidence, enforce access controls, and maintain continuous compliance with AI-driven identity governance across every system and identity.
Trusted by



Manual Audit Processes Increase Risk and Delay Compliance
Fragmented identity data across systems makes it difficult to track access & controls. Teams spend up to 40% of audit time collecting evidence manually, leading to delays, errors, & gaps in compliance.
Identity Governance That Enables Real-Time Audit Readiness
Automate identity lifecycle changes from HR systems and directories
Continuously validate access across Active Directory, Entra ID, and apps
Generate audit evidence on demand with full traceability
Enforce least privilege and SoD policies across all access points
Maintain compliance across all systems, from SaaS to on-prem
End-to-End Identity Governance for IT Auditors
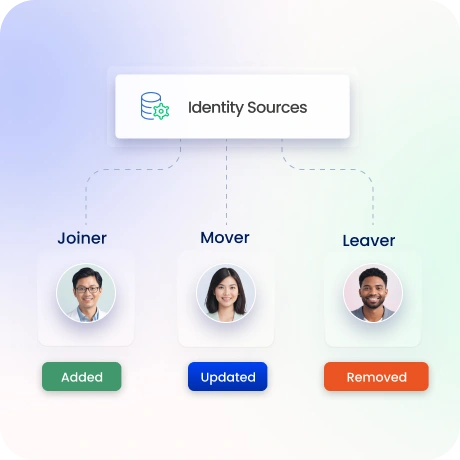
Automate Identity Lifecycle Governance (JML)
Automate JML lifecycle using HR systems as authoritative identity source
Propagate identity updates across directories and applications automatically.
Eliminate orphaned accounts with consistent deprovisioning.
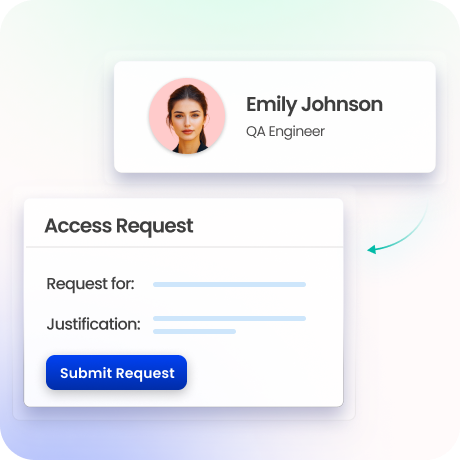
Access Requests & Approval Workflows
Enable self-service access requests with policy-based approval workflows.
Route approvals dynamically based on risk, roles, and entitlement context.
Maintain full traceability of every request for audit validation.
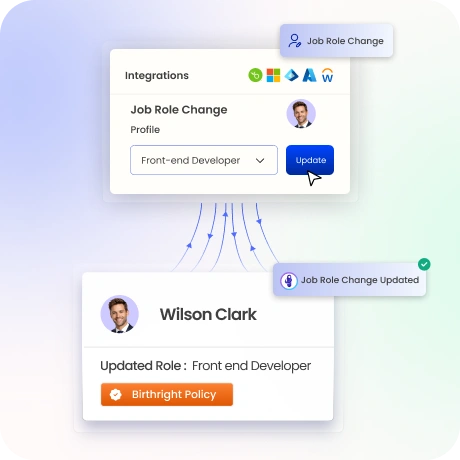
Role-Based Access & Entitlement Governance
Define and manage RBAC roles aligned to job responsibilities.
Centralize entitlement governance across systems and applications.
Simplify access control with role engineering and mapping.
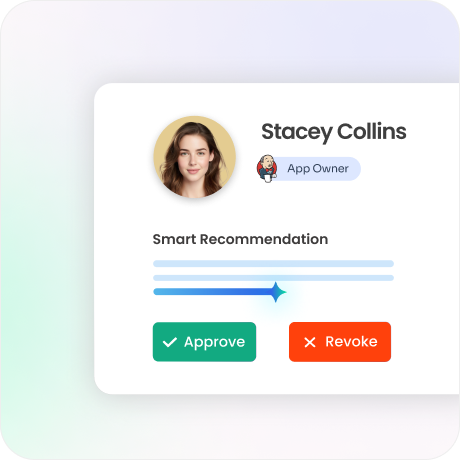
Intelligent Access Certifications & Reviews
Automate access reviews with risk-based certification campaigns.
Prioritize high-risk users and entitlements for audit focus.
Provide contextual insights for accurate validation decisions.
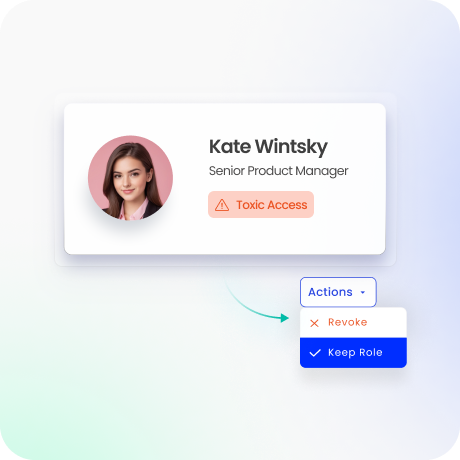
Segregation of Duties (SoD) Controls
Detect and prevent toxic access combinations using predefined policies.
Continuously monitor violations across systems and identities.
Reduce fraud risk and audit findings with preventive controls.
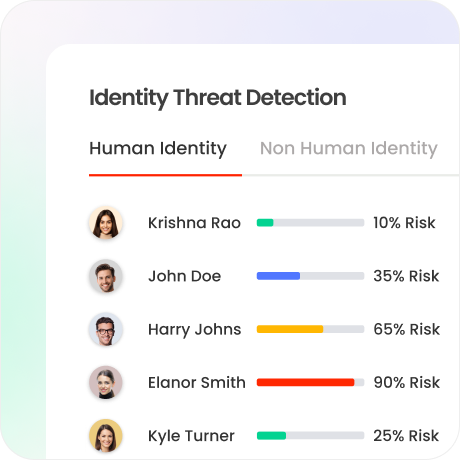
Policy Enforcement & Risk Analysis
Enforce least privilege with dynamic, policy-based controls.
Apply risk scoring across identities, roles, and entitlements.
Detect anomalies and policy violations in real time.
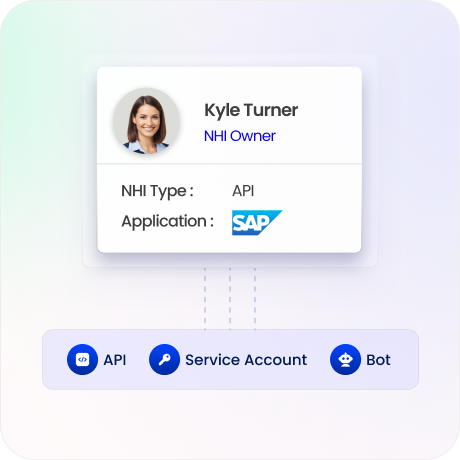
Privileged & Non-Human Identity Governance
Extend governance to admin accounts, service accounts, APIs, and bots.
Apply lifecycle and certification controls to high-risk identities.
Reduce audit gaps from unmanaged privileged access.
Continuous Audit Readiness & Reporting
Generate audit evidence instantly with full traceability.
Automate compliance reporting across SOX, ISO, GDPR, HIPAA, and SOC 2.
Provide auditors with on-demand, framework-aligned reports.

Drive measurable value with Identity Confluence
Download the ROI Report
90%
less manual audit effort
85%
faster audit evidence generation
3-5x
ROI within the first year
Why Teams Choose Identity Confluence
1.
Audit-Centric Identity Governance
Align identity controls, certifications, and audit workflows for faster validation and reduced audit complexity

2.
Continuous Compliance by Design
Real-time monitoring, automated evidence, and policy enforcement ensure audit readiness at all times

3.
Unified Identity Visibility
Gain a centralized view of identities, access, and policies across all applications and environments



