
Stop Identity Threats Before They Become Breaches
Gain full visibility across human and non-human identities, enforce least privilege, and reduce identity-driven attack paths with intelligent, Zero Trust identity governance.
Trusted by



Identity Gaps Are Expanding Your Attack Surface
Manual processes, fragmented visibility, and unmanaged non-human identities expand the attack surface, delay threat response, and increase exposure to insider threats and breaches.
See It in Action →

Reduce Identity Risk with Continuous, Intelligent Governance
Automate identity lifecycle to eliminate orphaned accounts and manual gaps
Gain unified visibility across human, machine, and privileged identities
Detect identity threats in real time with intelligent analytics
Enforce least privilege and Zero Trust with policy-driven controls
Maintain continuous compliance with automated governance and reporting
End-to-End Identity Governance for Enterprise Security
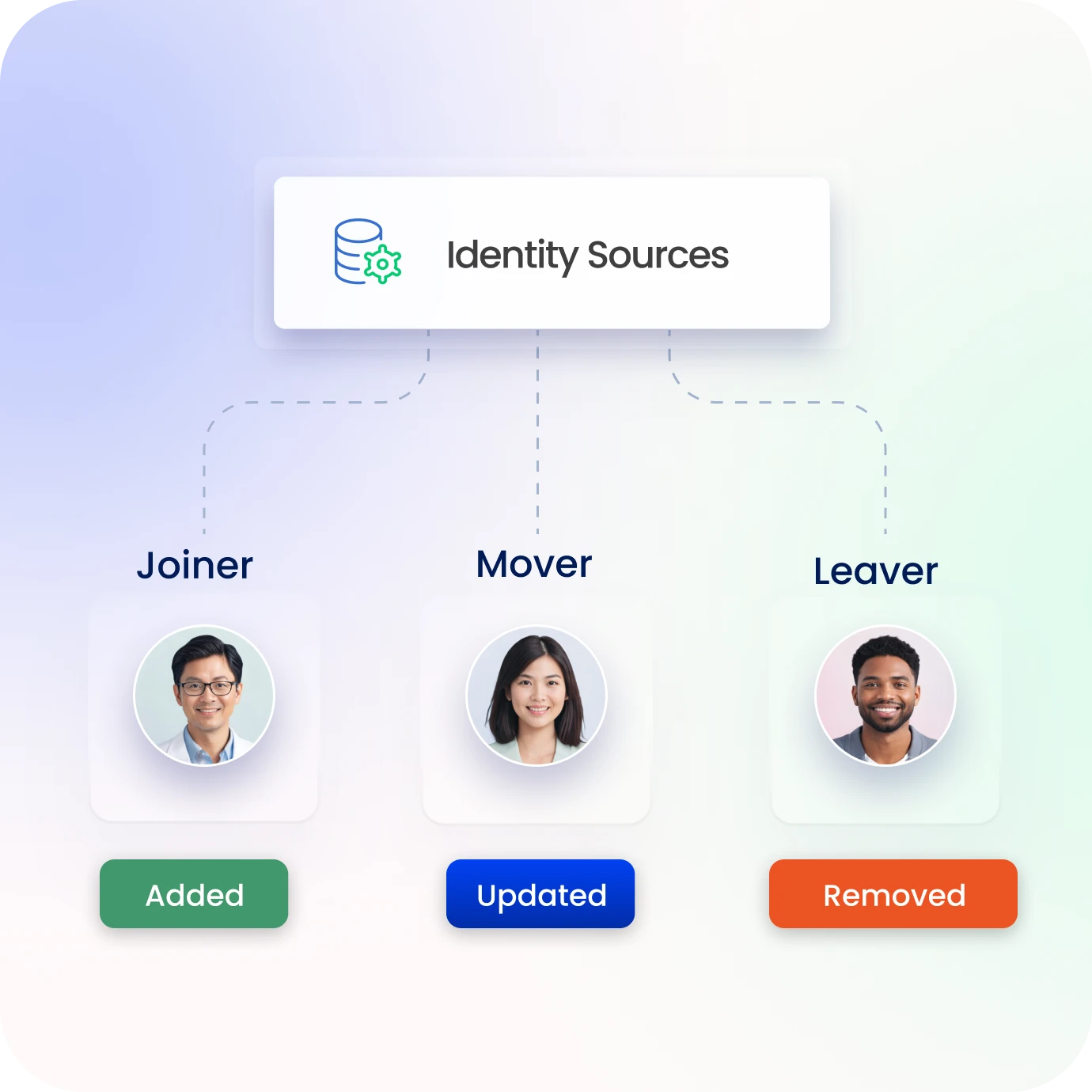
Automate Identity Lifecycle and Provisioning
Automate onboarding, role changes, and offboarding across systems.
Ensure instant provisioning and revocation to eliminate delays and orphaned access.
Maintain accurate, policy-driven identity controls with minimal manual effort.
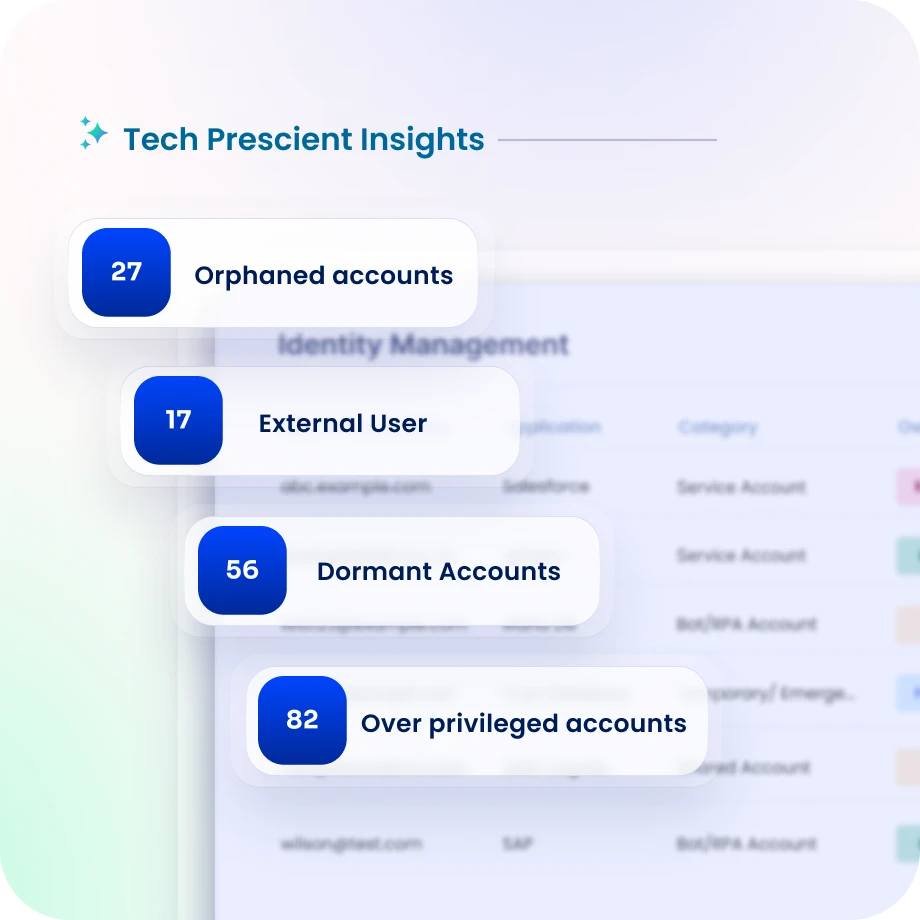
Unified Visibility Across All Identities
Discover and govern human, non-human, and privileged identities across environments.
Centralize identity relationships across applications, cloud, and infrastructure.
Gain a single, risk-aware view of identity access and exposure.
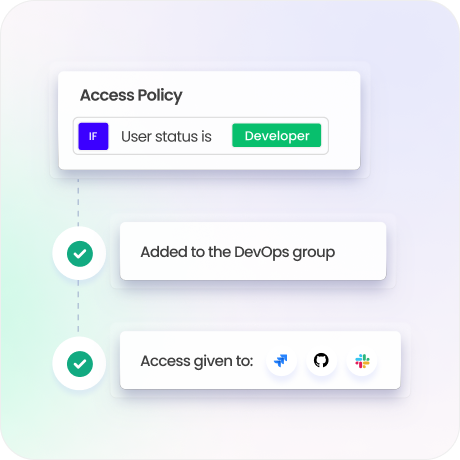
Least Privilege & Policy Enforcement
Apply RBAC, ABAC, and policy-based controls aligned with Zero Trust principles.
Prevent excessive permissions and enforce entitlement governance.
Eliminate SoD conflicts and high-risk access combinations.
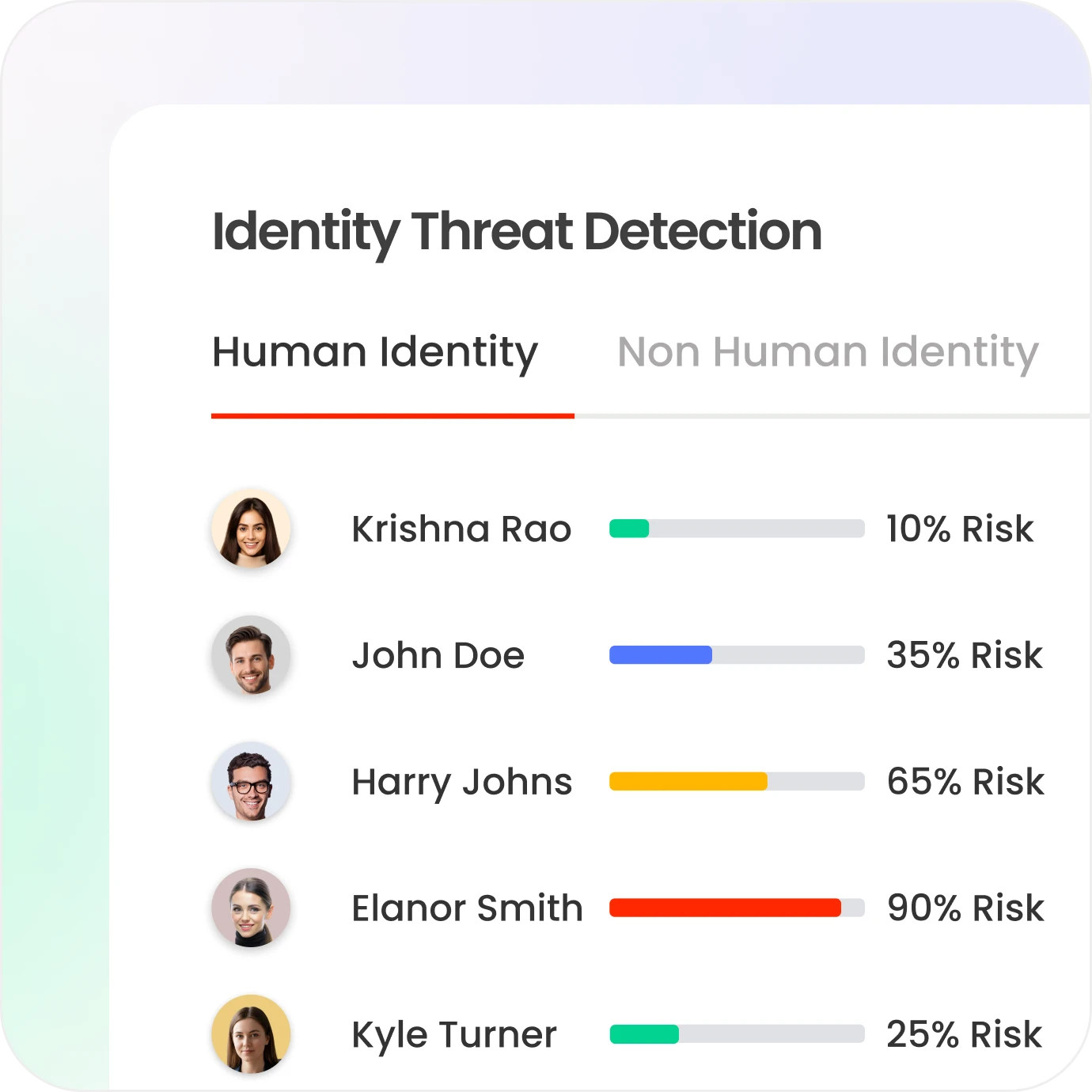
Identity Threat Detection & Response
Detect unusual access patterns and high-risk identity behavior in real time.
Identify compromised credentials and potential attack paths early.
Strengthen defense against insider threats and external attacks.
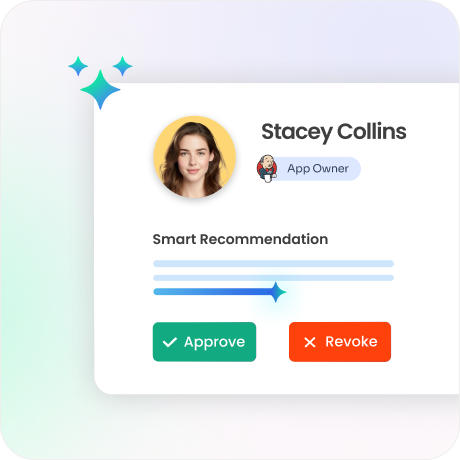
Access Reviews and Compliance Automation
Automate access certifications with risk-based recommendations.
Generate real-time audit trails and compliance reports.
Maintain continuous audit readiness without manual effort.
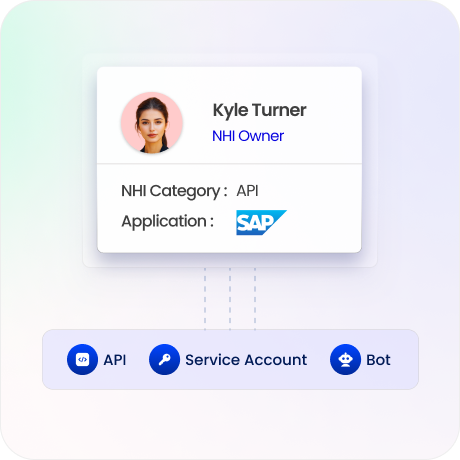
Privileged & Non-Human Identity Security
Govern service accounts, APIs, bots, and machine identities with full lifecycle control.
Secure privileged access across critical systems and infrastructure.
Reduce risk from unmanaged identities and permission sprawl.
Strengthen security posture, reduce risk, and improve response with intelligent identity governance.
Calculate Your ROI
83%
fewer identity-based attacks
90%
faster threat response
3x
faster identity provisioning
Why Tech Prescient Is Different
1.
Security-First Design
Built to detect and prevent identity-based threats, not just support audits.

2.
Unified Identity Control
Govern all identities, policies, and access decisions from a single platform.

3.
Intelligent Risk Insights
Continuously analyze identity behavior to detect threats and prioritize action.



