Identity Confluence
Evidence Center
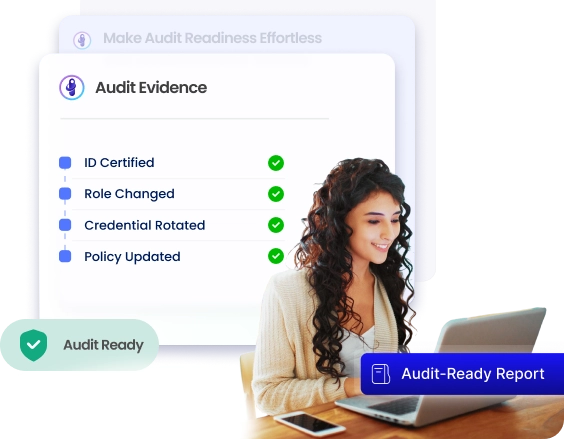
Make Audit Readiness Effortless with Unified Evidence Visibility
Every access decision, lifecycle event, and policy change is captured automatically, correlated, validated, and ready for any auditor before they ask the first question.
Trusted by



Manual Evidence Collection Slows Audits and Increases Risk
Audit teams spend weeks chasing records across disconnected systems, reconciling access manually, and patching gaps that should never have existed. By then, the risk is already documented.
See It in Action →

Automate Audit Evidence and Ensure Continuous Compliance
Continuously capture and correlate identity activity across every system.
Generate audit-ready evidence aligned to policy automatically.
Maintain complete traceability of every access decision and change.
Monitor identity behavior in real time to detect compliance gaps early.
Deliver instant audit reports without a single manual preparation step.
Key Capabilities for End-to-End Evidence Visibility
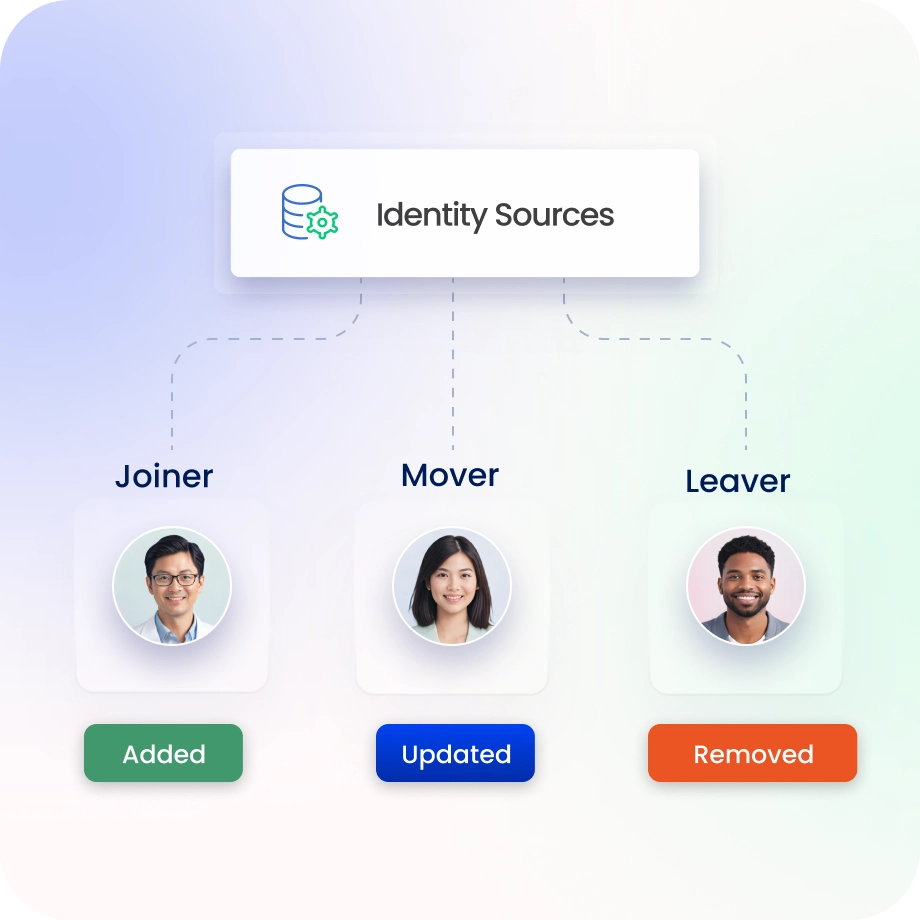
Full Lifecycle Audit Visibility
Track identity events across joiner, mover, and leaver lifecycle stages.
Capture all changes with continuous, validated audit-ready evidence.
Ensure complete traceability across users, roles, and access changes.
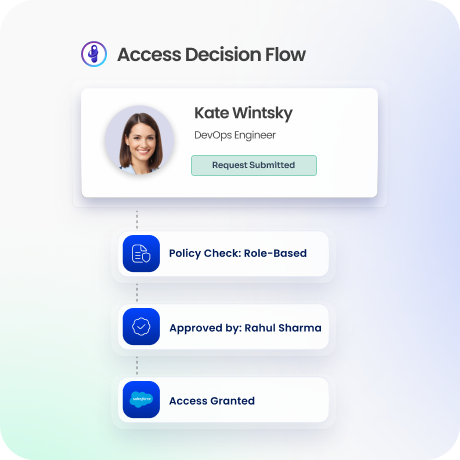
Traceable, Explainable Access Decisions
Track how access is granted, modified, and revoked across systems.
Understand who approved access and the reason behind each decision.
Approvals, provisioning actions, and policies link into a single traceable audit trail.
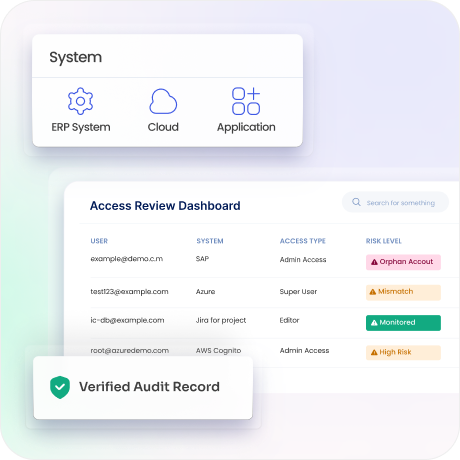
Access Review Evidence, Always Complete
Reviewer decisions, certification outcomes, and periodic review records are captured with full context.
Proof of every review cycle exists before the auditor requests it.
Excessive access and certification gaps surface during the cycle.

Accurate Evidence through Reconciliation
Identity data reconciles continuously across every connected system.
Orphaned accounts, mismatched entitlements, and data gaps are identified and flagged before they become audit findings.
Evidence stays accurate because the underlying data is continuously validated.
JIT Access Tracked as Verifiable Evidence
Every JIT access grant is tracked from approval through expiry, with a complete, timestamped trail.
Temporary access decisions become permanent, verifiable audit evidence.
Auditors see exactly what was granted, when, and for how long.

Real-Time Posture and Compliance Visibility
A unified view of identity risk, policy compliance, and access exposure.
SPM signals assess audit readiness in real time and surface gaps.
Pre-built reports aligned to SOX, GDPR, DPDPA, ISO 27001, and SOC 2 ready in one click.

Drive measurable value with Identity Confluence
Download the ROI Report
85%
Fewer orphan accounts
80%
Faster access reviews
90%
Reduced audit findings
Why Teams Choose Identity Confluence
1.
Unified Evidence Visibility
Capture identity activity and decisions across systems in one auditable evidence layer.

2.
Policy-Driven Control
Apply consistent policy checks across lifecycle, reviews, and temporary access events.

3.
Continuous Risk Reduction
Detect evidence gaps early and continuously prove compliance without manual reconciliation.



