Identity Confluence
Identity Threat Detection Response
Detect and Stop Identity Threats Before They Cause Damage
Most security tools see the anomaly. None of them know what access that identity actually holds. Identity Confluence adds the context that turns a detection into a decision.
Trusted by



Identity Threats Go Undetected Until It Is Too Late
Traditional security tools detect anomalies but lack identity context. Without visibility into access, organizations struggle to understand risk, respond effectively, & prevent recurring threats.
See How We Fix This →
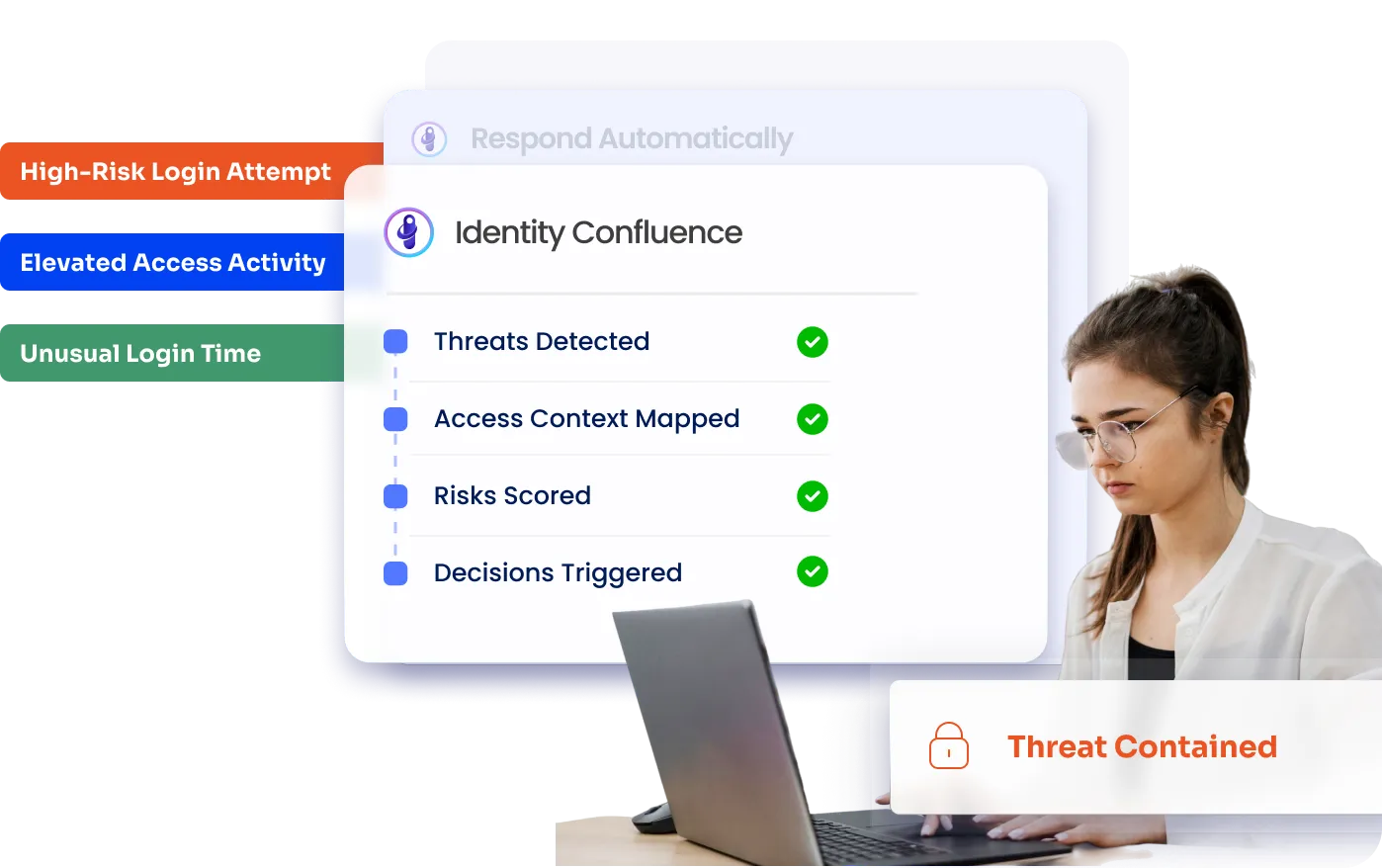
Detect Identity Threats in Context and Respond Automatically
Detect threats based on identity, access, and behavior context
Identify excessive or risky access that increases exposure
Automate response actions to contain and reduce threats
Link threat detection to identity governance decisions
Continuously reduce identity risk across systems
Identity-Aware Threat Detection with Automated Response
Detect Identity Threats with Access Context
Analyze behavior alongside roles, entitlements, and access patterns
Identify anomalies that deviate from expected identity activity
Detect threats that traditional tools miss due to a lack of identity context
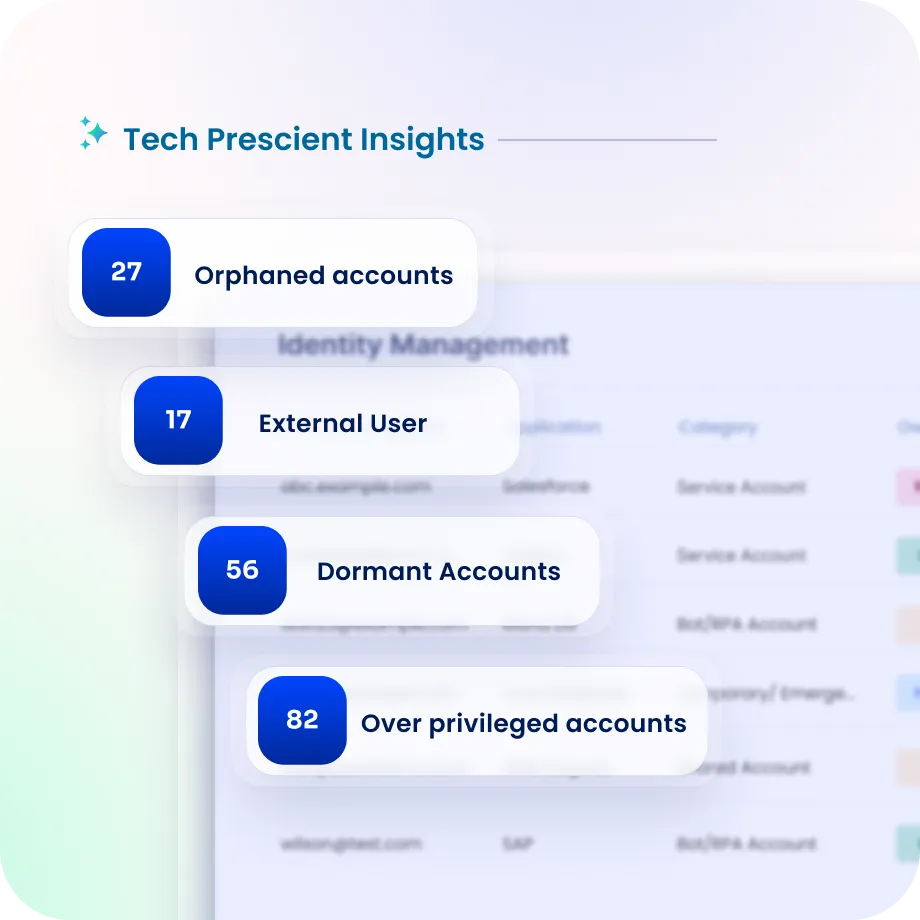
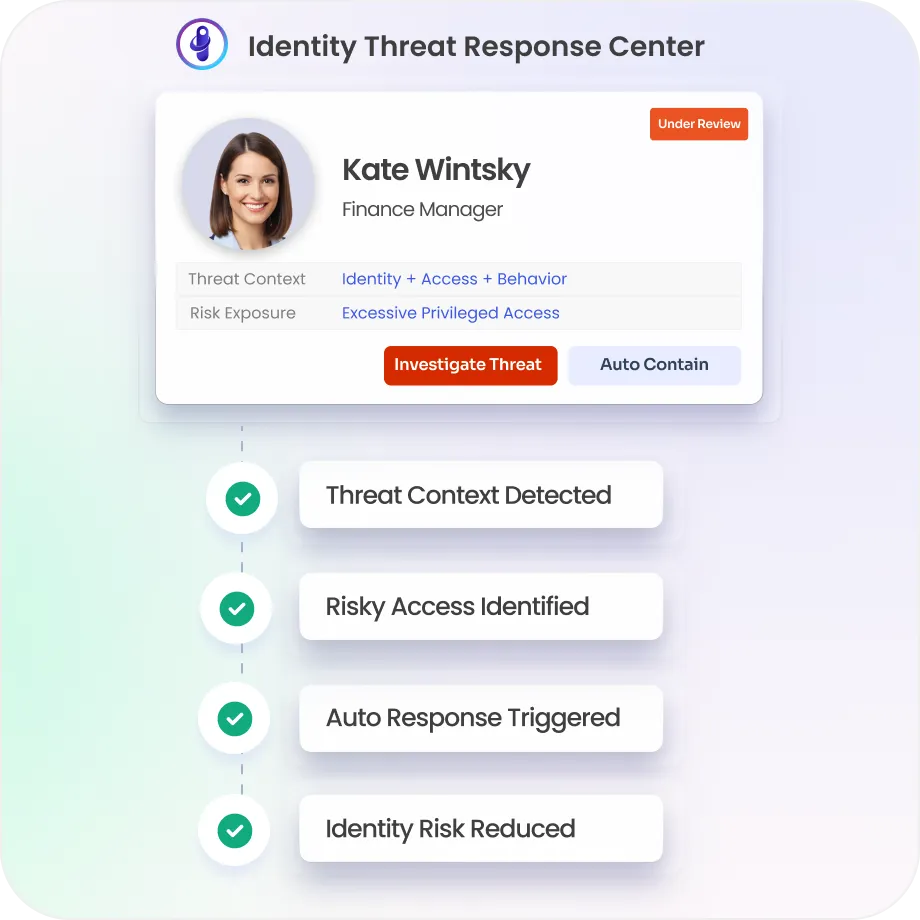
Surface Risky Access and Attack Exposure
Identify over-privileged accounts that expand the attack surface
Highlight access that can enable lateral movement and misuse
Surface identity risks before they escalate into security incidents

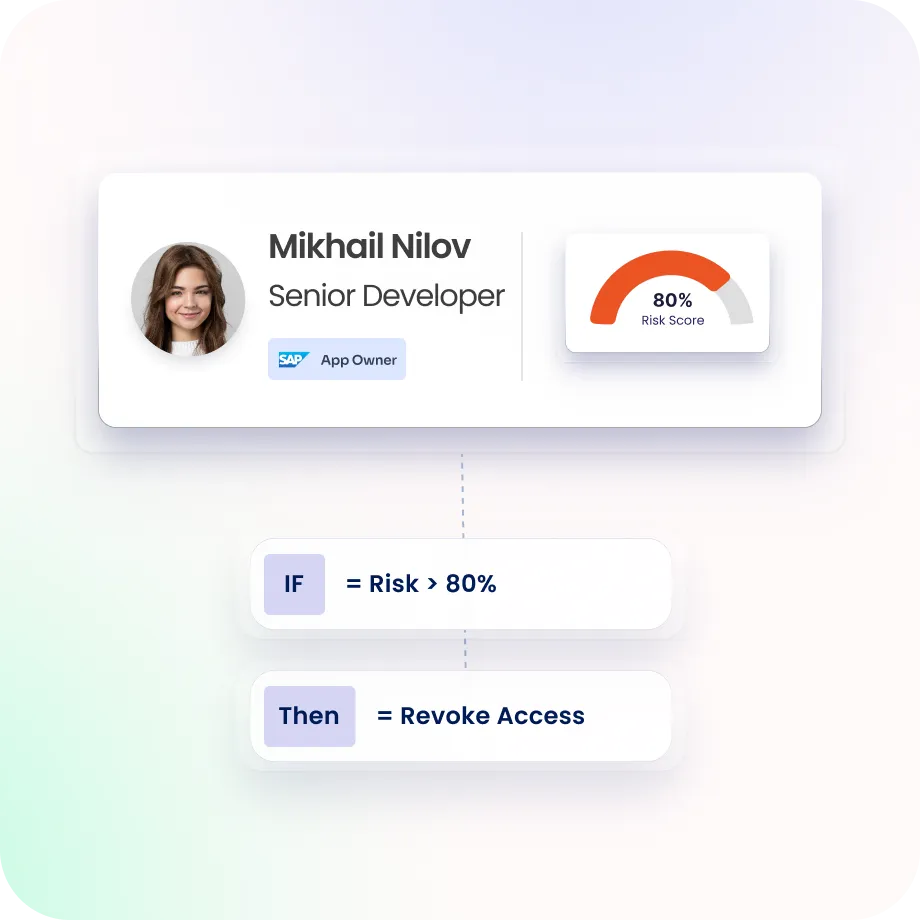
Automate Response and Containment Actions
Trigger automated actions such as access revocation or restriction
Contain threats immediately without manual intervention
Reduce response time and limit potential impact
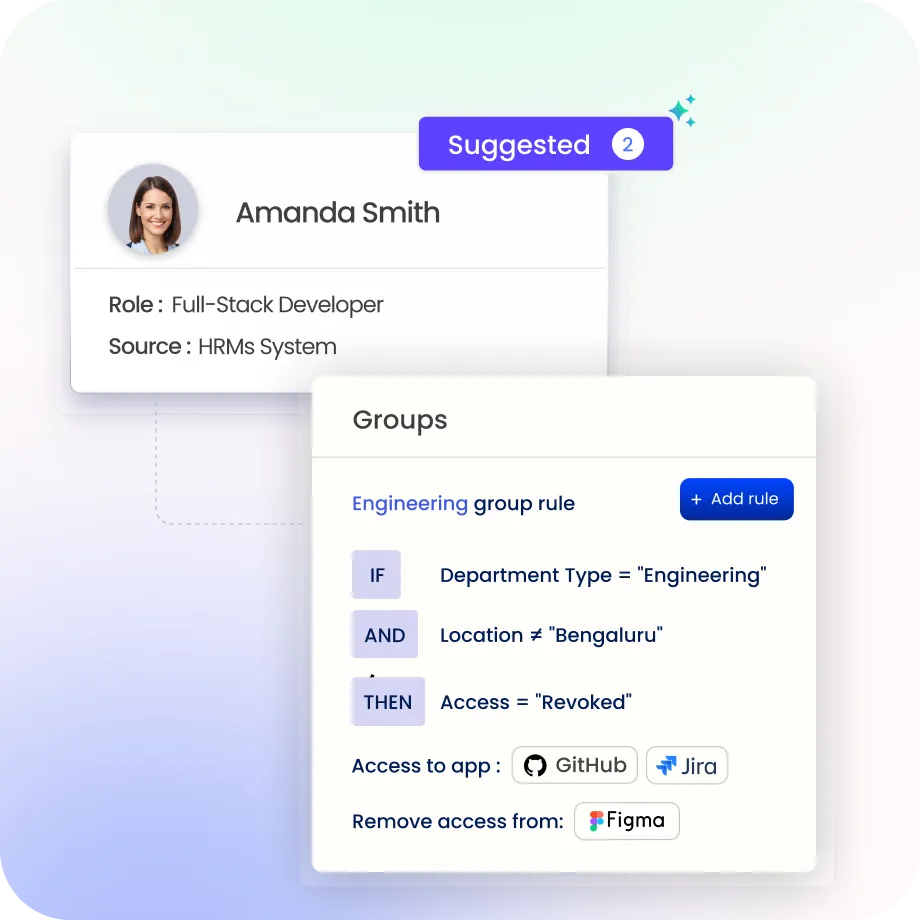
Correct Root Causes with Governance Controls
Align response actions with identity policies and governance rules
Remove excessive or misaligned access contributing to risk
Ensure threats are resolved at the source, not just contained
Maintain Continuous Visibility & Audit Evidence
Monitor identity risk signals and access changes in real time
Track detected threats, actions taken, and outcomes centrally
Maintain audit-ready records for investigations and compliance

Why Teams Choose Identity Confluence
1.
One platform across IT and OT
Identity Confluence brings workforce, contractor, and machine identities across IT, OT, SCADA, ICS, and cloud into a single platform, so you’re not stitching together tools or leaving gaps in operational environments.

2.
Built for regulations from day one
Standards like NERC CIP, SOX, NIS2, IEC 62443, and SEC cybersecurity rules are already mapped in, so every access change is logged, traceable, and ready when auditors ask.

3.
Close the gaps before they become risks
Continuous risk scoring, anomaly detection, and visibility into non human identities like service accounts and API keys help you catch issues early instead of reacting after the fact.
Drive measurable value with Identity Confluence
Download the ROI Report
90%
reduction in manual reviews
10x
faster onboarding and offboarding
80%
less access management overhead



