
Identity Governance Across Critical Energy Infrastructure
IT, OT, SCADA, and cloud converge. So do their identity risks. Enforce least privilege, automate access governance, and maintain continuous compliance from onboarding to offboarding.
Trusted by



Unmanaged Identities Increase Risk Across Energy Infrastructure
As IT, OT, SCADA, ICS, and cloud access converge, unmanaged identities create toxic access combinations, compliance violations, and the kind of operational disruption energy simply cannot afford.
See It in Action →
From Scattered Access to Governed Energy Operations
Enforce access controls aligned to NERC CIP, SOX, NIS2, and IEC 62443
Automate access certifications across on-prem, hybrid, and cloud systems
Monitor workforce, contractor, and privileged access in real time
Block SoD conflicts before access is ever granted
Generate audit-ready evidence automatically with every identity change
Discover, Govern, and Secure Every Energy Identity
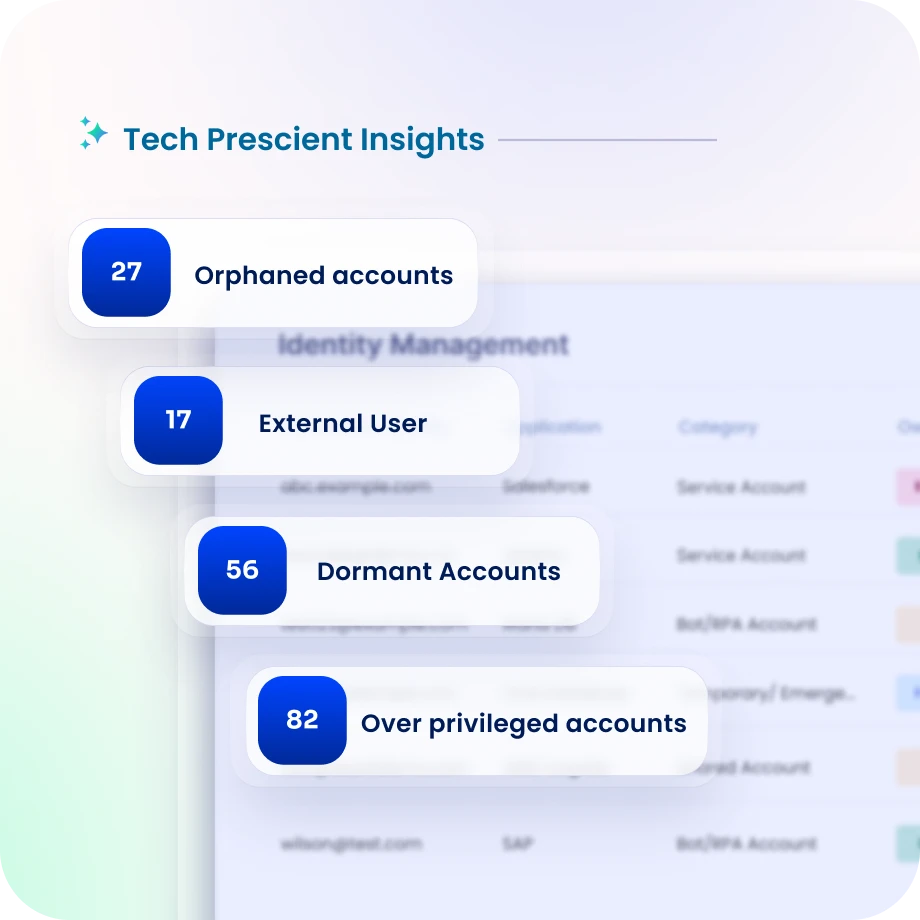
See Every Identity Across Every System
Discover workforce, contractor, machine, and service account identities across SCADA, ICS, ERP, IoT, and cloud systems.
Maintain a unified view of access across plants, control rooms, substations, and field operations.
Orphaned accounts, unauthorized entitlements, and unusual access patterns surface before an auditor or attacker finds them first.
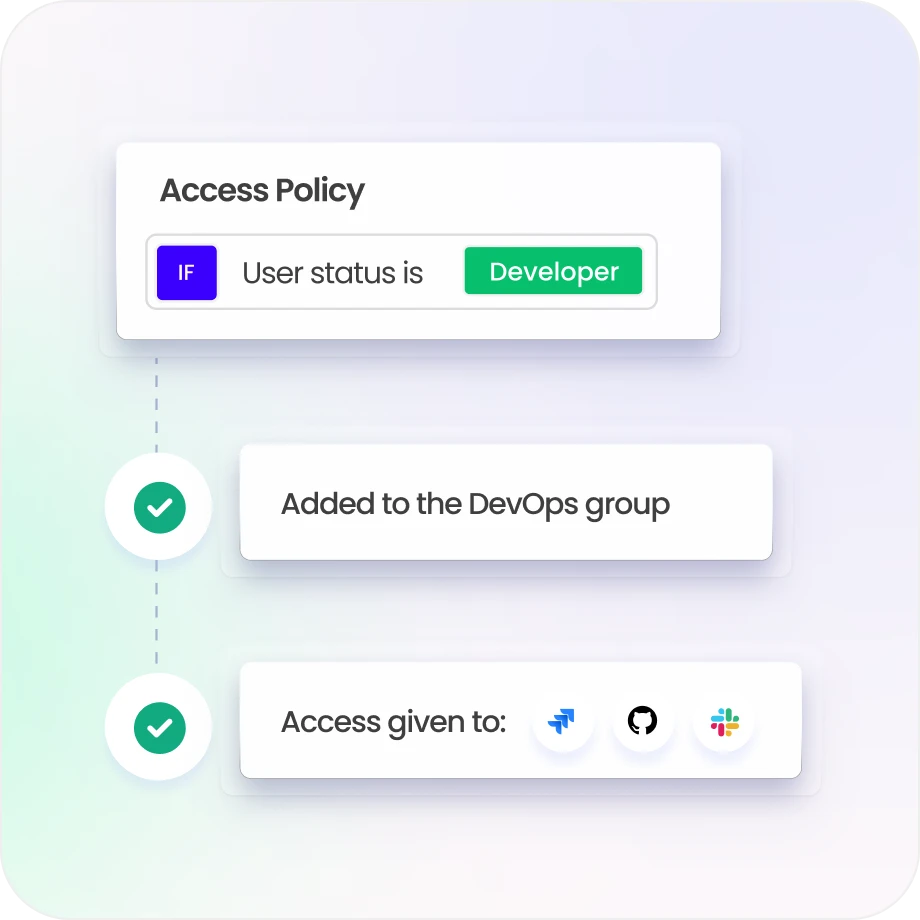
Enforce Least Privilege and Privileged Access Across IT and OT
Apply role- and attribute-based policies aligned to operational roles, plant functions, and facility zones.
Monitor privileged accounts, detect segregation-of-duties conflicts, and govern shared account usage with individual accountability.
Reduce ransomware and privilege escalation risk with dynamic controls, minimal standing privileges, and full audit trails.
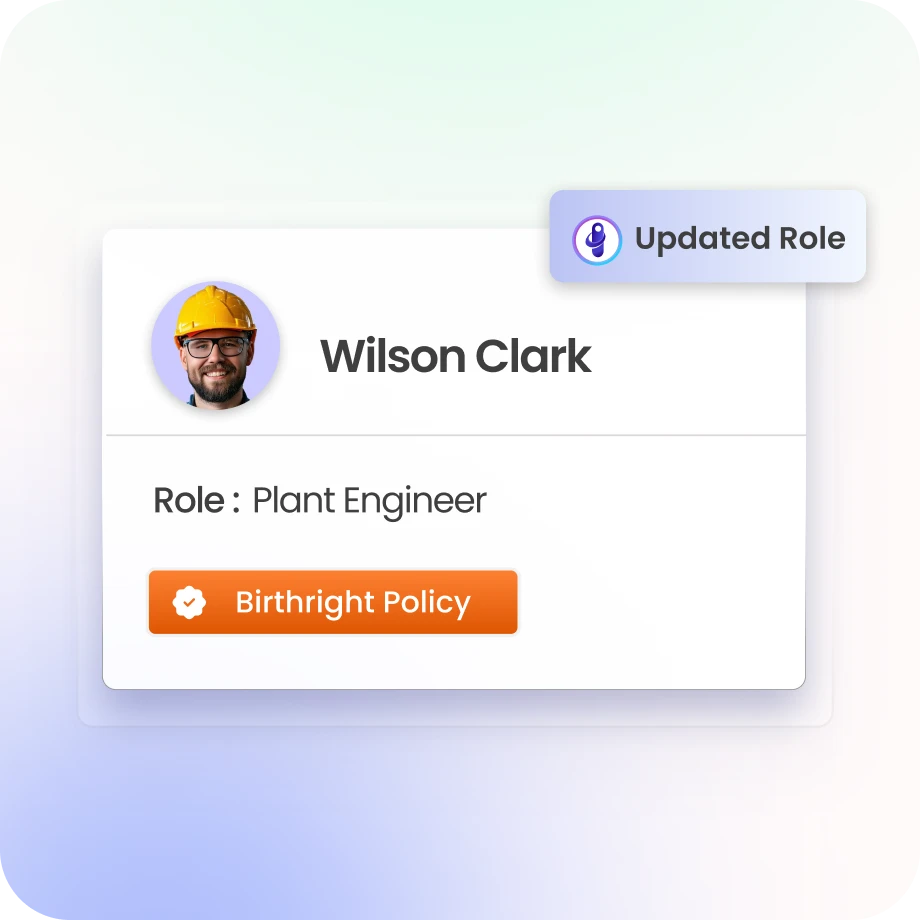
Automate the Full Identity Lifecycle
Automate onboarding, transfers, and terminations across HR, plant, and field systems.
Revoke access immediately upon termination to meet NERC CIP-004 R5 standards.
Field contractors, third-party vendors, and managed service providers get policy-based, time-bound access that revokes automatically when contracts end.
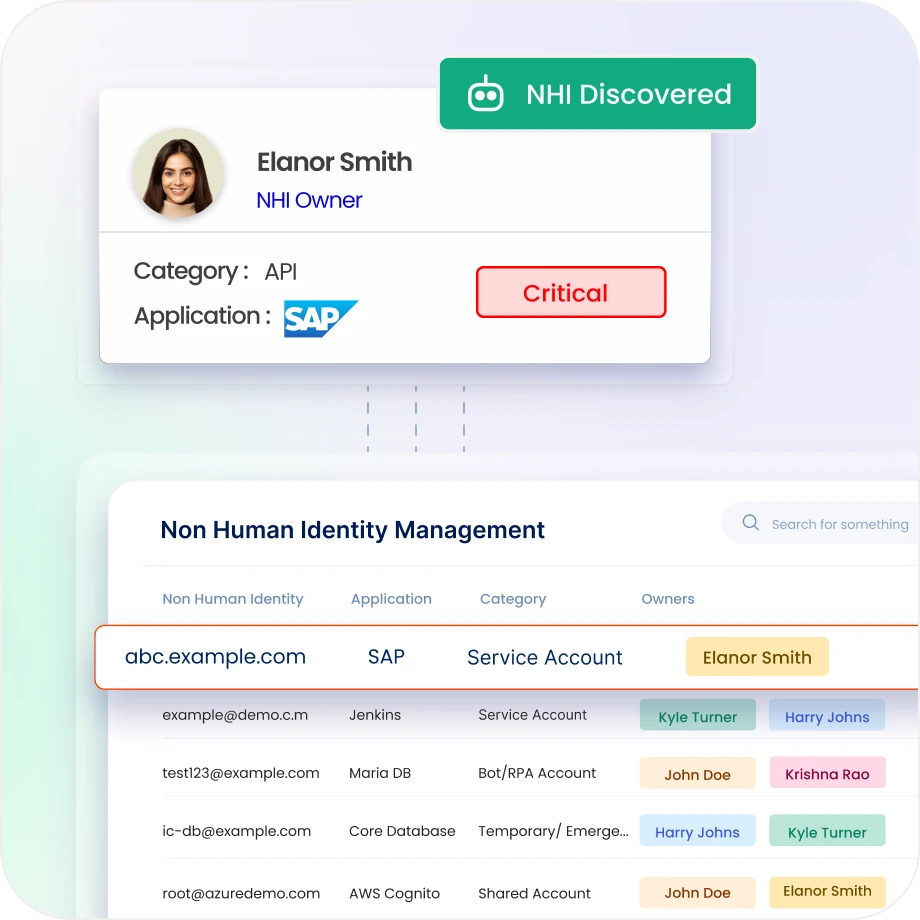
Govern Every Contractor, Vendor, and Non-Human Identity
Monitor and record external access across the supply chain, partner ecosystem, and managed service providers.
Govern service accounts, API keys, automation credentials, and machine identities across OT and cloud environments.
Enforce lifecycle policies for non-human identities: ownership assignment, rotation schedules, and expiry enforcement.
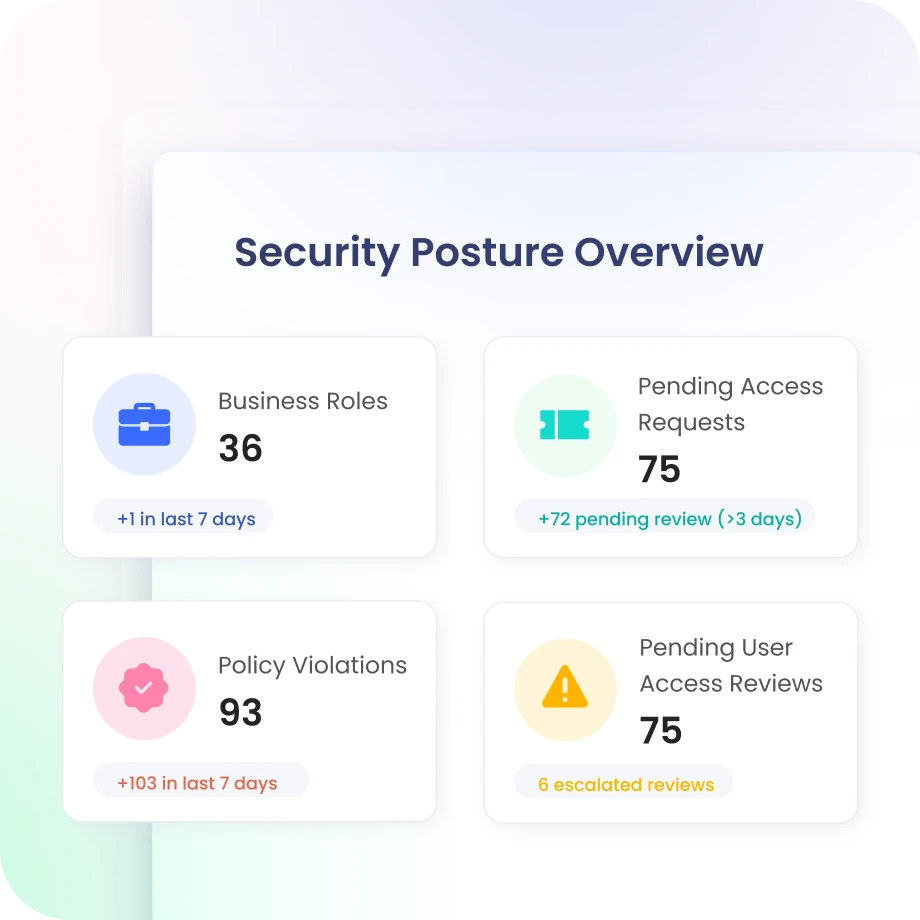
Adaptive Risk and Identity Security Posture Management
Score identity risk continuously and flag anomalous entitlements across IT, OT, and IoT environments.
Surface MFA gaps, dormant accounts, toxic access combinations, shadow admin exposure, and SoD conflicts before they become audit findings.
Prioritize remediation based on risk severity and route actions through existing ITSM workflows.

Drive measurable value with Identity Confluence
Download the ROI Report
60%
reduction in manual reviews
10x
faster onboarding and offboarding
80%
less access management overhead
Why Teams Choose Identity Confluence
1.
One platform across IT and OT
Identity Confluence brings workforce, contractor, and machine identities across IT, OT, SCADA, ICS, and cloud into a single platform, so you’re not stitching together tools or leaving gaps in operational environments.

2.
Built for regulations from day one
Standards like NERC CIP, SOX, NIS2, IEC 62443, and SEC cybersecurity rules are already mapped in, so every access change is logged, traceable, and ready when auditors ask.

3.
Close the gaps before they become risks
Continuous risk scoring, anomaly detection, and visibility into non human identities like service accounts and API keys help you catch issues early instead of reacting after the fact.



