Identity Confluence
Manual Access Requests
Automate Access Requests with Modern Identity Governance
Email chains, spreadsheet trackers, and manual approval chases don't scale, and they leave no audit trail. Replace all of it with policy-driven workflows that just work.
Trusted by



Manual Access Requests Create Risk & Compliance Gaps
Access requests land in inboxes. Approvals happen in Slack. Provisioning waits on someone's calendar. By the time access is granted, it's either late, excessive, or completely undocumented.
See It in Action →
Govern Manual Access Requests with Smart Automation
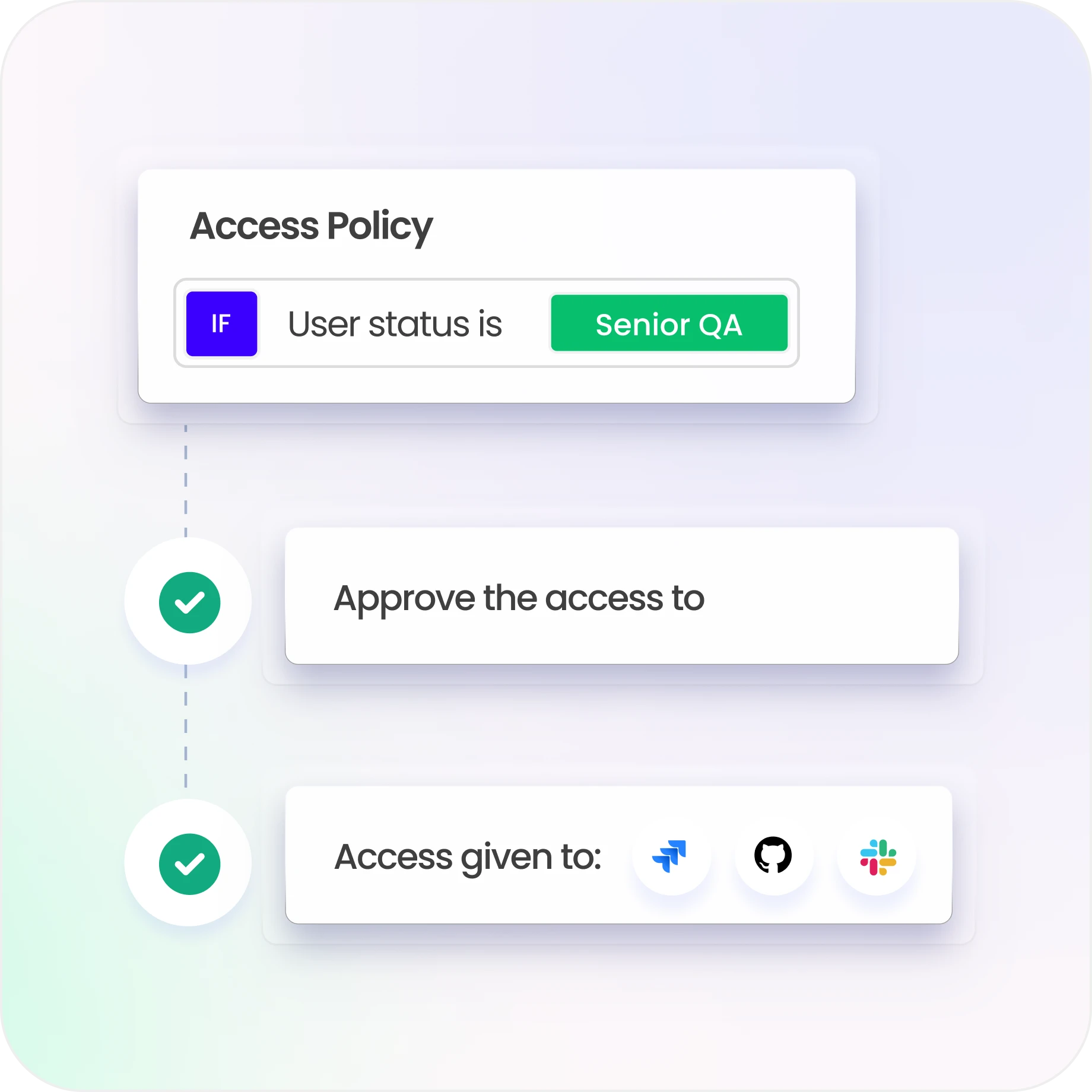
Automate requests with policy-based workflows and approvals
Enable self-service access with built-in governance controls
Route approvals dynamically by role, risk, and ownership, automatically
Enforce least privilege using RBAC and policy-driven access models
Track every request, approval, and provisioning action with a full audit trail
Everything You Need for Continuous Compliance
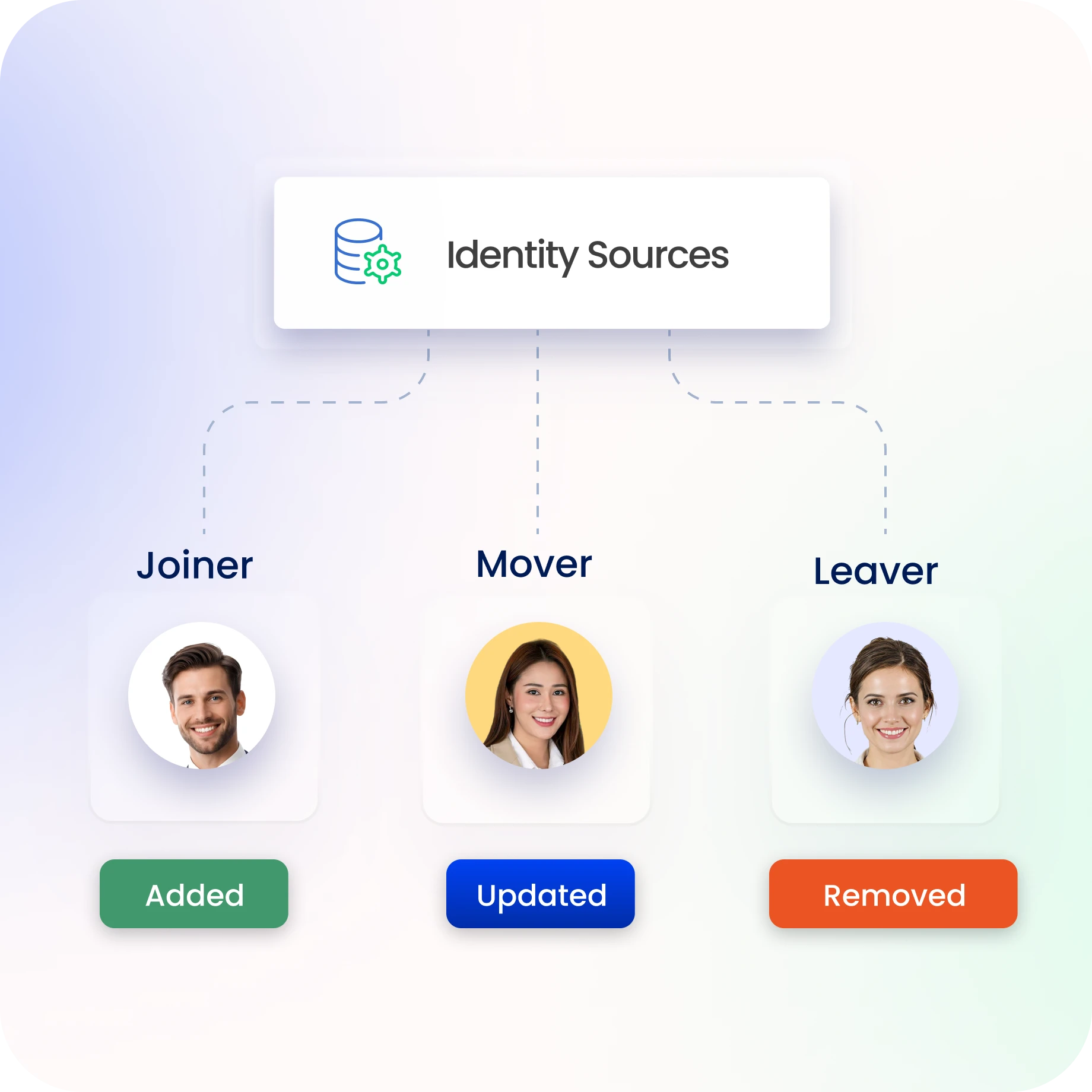
Align Access to the Lifecycle Automatically
Every joiner, mover, and leaver event triggers the right access change automatically
Ensure access aligns with roles across all identity lifecycle stages.
Employees, contractors, and non-human identities governed consistently under the same lifecycle rules.
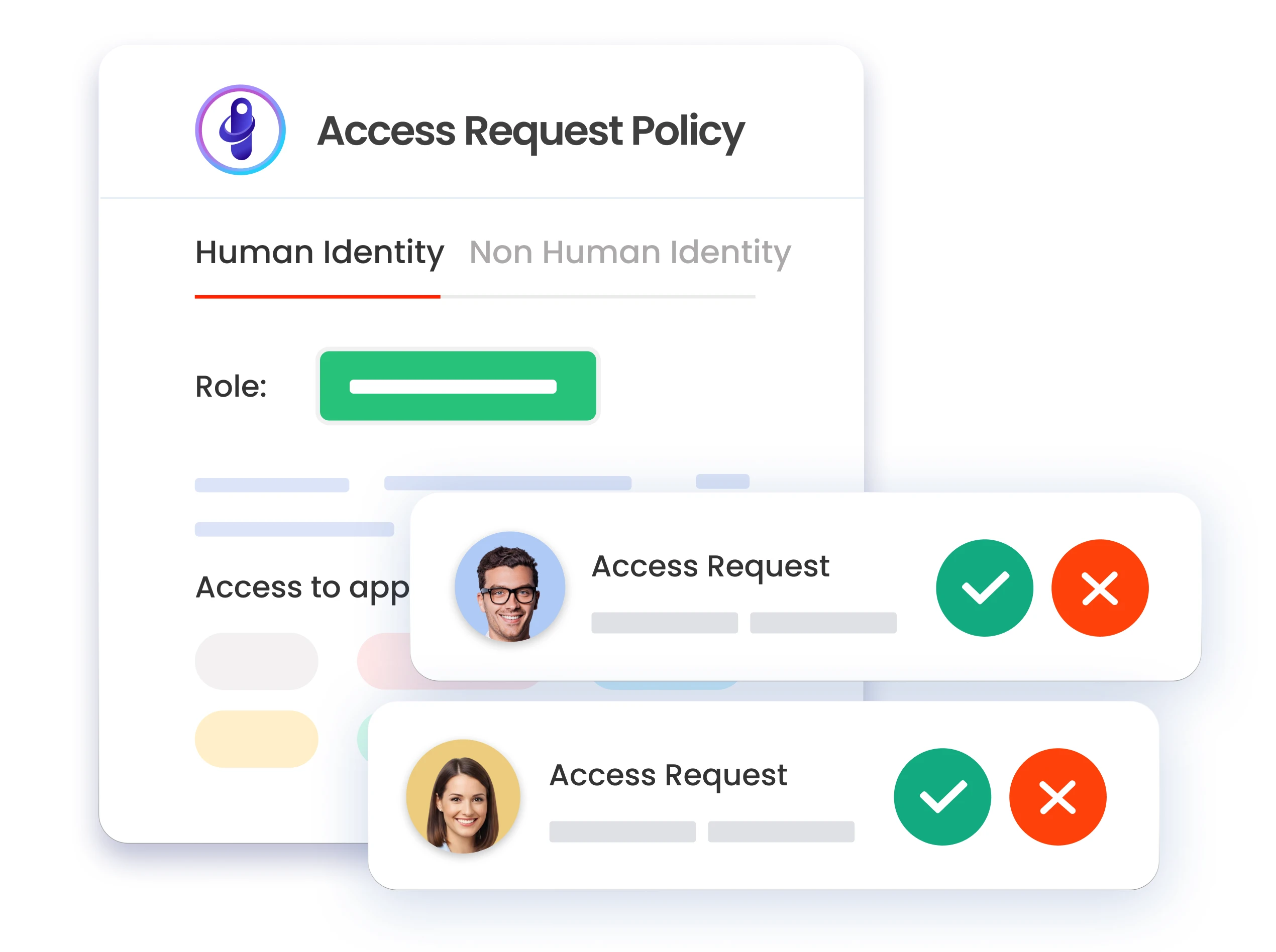
Enable Fast Access Requests and Approvals
Enable governed access requests through a centralized portal.
Route approvals dynamically based on role, risk, and ownership.
Leverage smart access workflows to automate routing and reduce manual intervention.
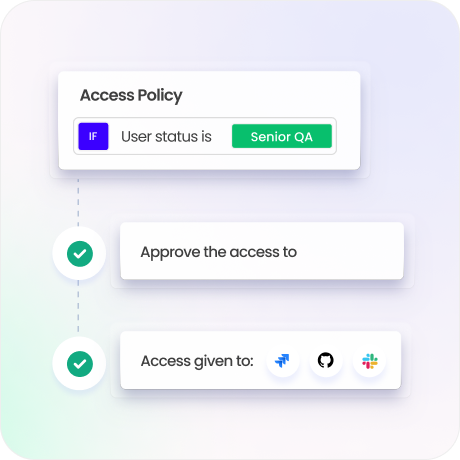
Enforce Least Privilege at Every Request
Role and attribute-based access controls enforce least privilege at the point of every request
Policy-driven access models mean nobody gets more than they need, and nobody gets it without the right approval chain.
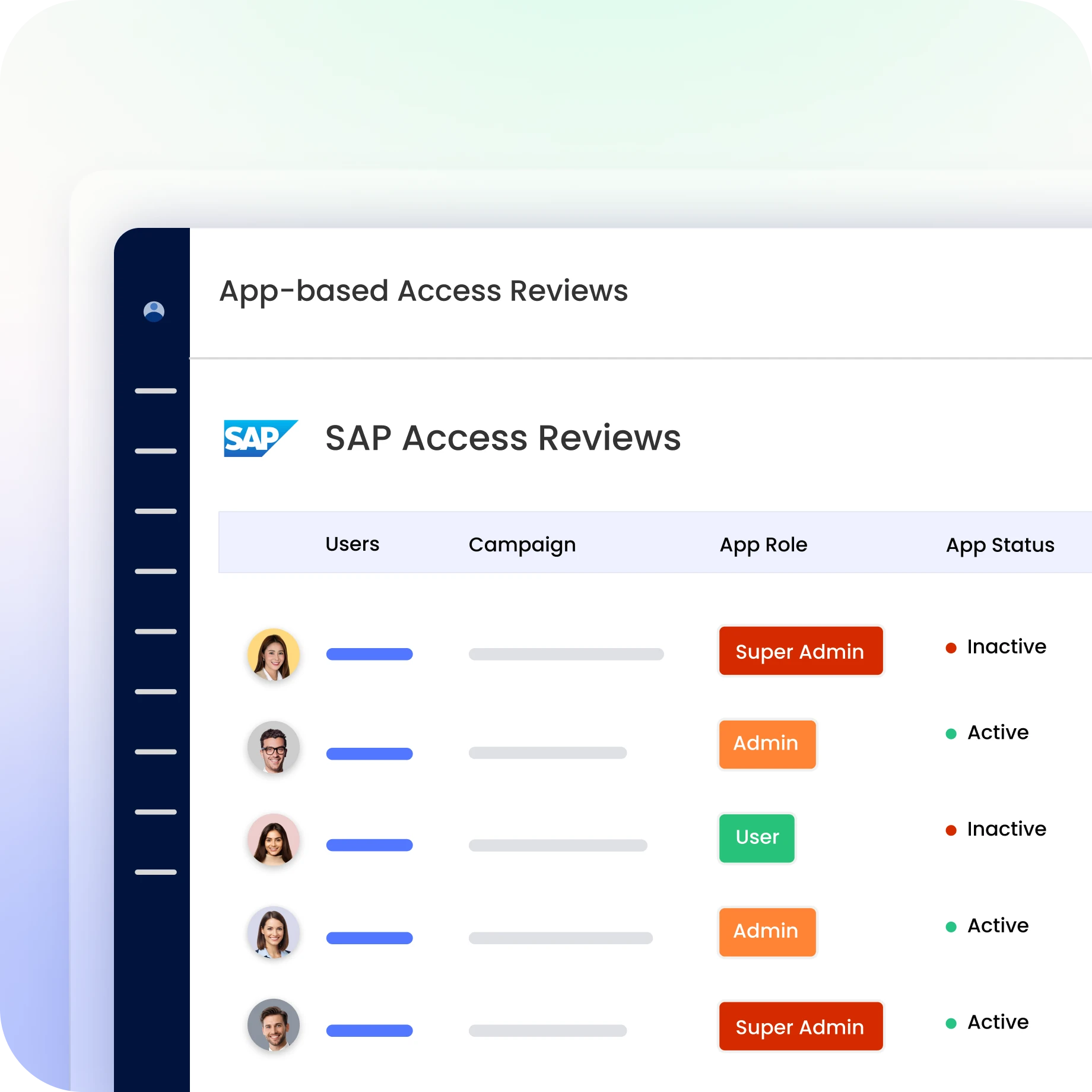
Continuously Validate What Was Approved
Conduct scheduled access reviews with risk-based prioritization.
Enable managers to validate or revoke unnecessary access.
Use reconciliation insights to detect mismatches between what's approved and what's provisioned.

Provision Across Systems Automatically
Approved access provisions instantly across every connected system.
Role changes and exits trigger immediate access adjustment and revocation.
250+ pre-built connectors and continuous identity synchronisation.

Ensure Audit Readiness and Risk Visibility
Every request, approval, and provisioning action generates a complete, timestamped audit trail.
Pre-built compliance reports for SOC 2, GDPR, DPDPA, SOX, ISO 27001 and more.
Risk visibility centralised in one place means compliance decisions are based on evidence.

Drive measurable value with Identity Confluence
Download the ROI Report
90%
Faster provisioning
85%
Fewer identity risks
83%
Faster audit readiness
Why Teams Choose Identity Confluence
1.
Context-Aware Reviews
Reviewers get real risk signals, usage insights, and entitlement clarity, not just names in a spreadsheet.

2.
Risk-Based Automation
Prioritize high-risk access automatically and reduce reviewer fatigue with intelligent workflows.

3.
Audit-Ready Evidence, Instantly
Generate complete audit trails and compliance reports instantly, no manual evidence collection.



