Identity Confluence
Role Mining
Turn Access Complexity into Intelligent Role-Based Governance
Role sprawl doesn't happen because people are careless. It happens because building accurate roles manually is nearly impossible. Identity Confluence changes that permanently.
Trusted by



Unmanaged Roles Create Access Risks and Audit Challenges
Manually built roles drift from reality the moment they ship. Redundant roles accumulate. Access exceeds what anyone needs. And when auditors ask why a user has certain access, nobody can explain it.
See It in Action →

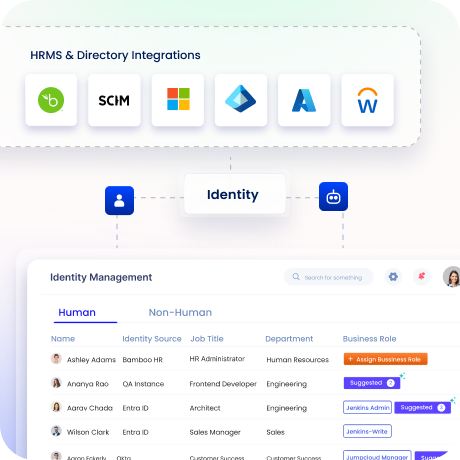
Transform Access Data into Governed Role Intelligence
Discover access patterns across identities and entitlements automatically
Generate optimised roles aligned with real job functions
Eliminate redundant roles and reduce entitlement sprawl at the root
Enforce least-privilege through role-based and policy governance
Continuously refine roles as your organisation changes
Role Mining Built for End-to-End Identity Governance
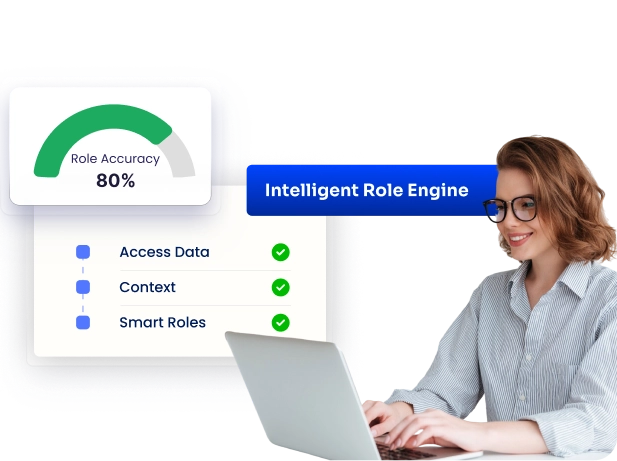
Discover Role Intelligence from Access Patterns
Analyze identities, entitlements, and usage patterns to uncover role candidates.
Use data-driven role mining to replace assumptions with accurate role models.
Leverage risk signals and behavioural insights to prioritize high-impact role optimisation.
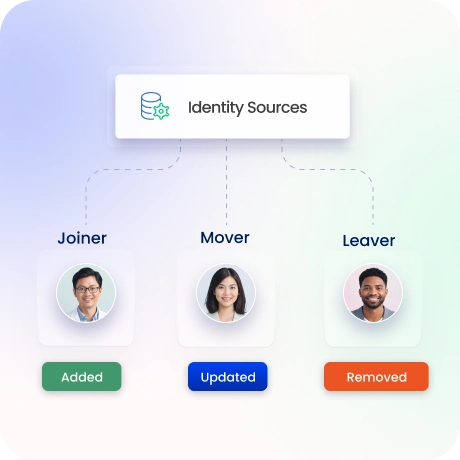
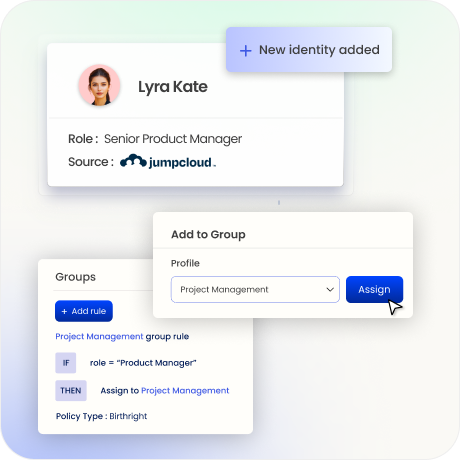
Align Roles with Identity Lifecycle
Integrate role mining directly with joiner, mover, and leaver processes, so access is always aligned to the current role.
New hires receive appropriate access automatically based on optimised roles.
Accelerate onboarding with AI-driven role assignment aligned to lifecycle events.
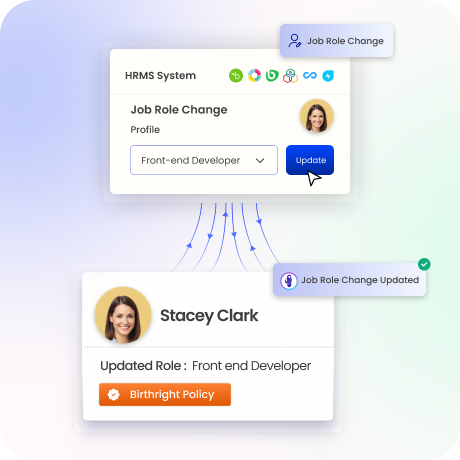
Automate Provisioning with Role-Based Access
Connect mined roles to automated provisioning and deprovisioning workflows.
Access is granted or revoked based on lifecycle events.
Enable seamless role-to-access orchestration through smart access workflows.
Enforce Least-Privilege with Role & Policy Controls
Apply RBAC and policy-based access controls across roles and entitlements.
Continuously validate access against least-privilege principles.
Detect risky access patterns and prevent violations using integrated risk insights.
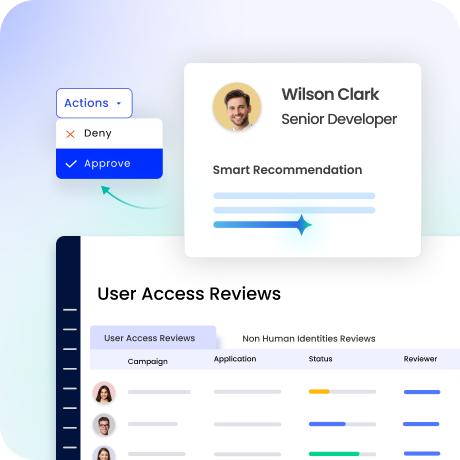
Continuously Optimize and Certify Role Access
Support periodic access reviews with role-level visibility.
Enable faster, more accurate certifications with contextual insights.
Incorporate risk-based recommendations to reduce review fatigue and improve decision accuracy.
Ensure Audit-Ready and Accurate Role Governance
Complete audit trails of every role creation, change, and assignment, automatically.
Continuously reconcile roles and entitlements to eliminate inconsistencies and duplicates.
Centralize audit evidence and leverage unified data integration for complete visibility.

Drive measurable value with Identity Confluence
Calculate Your ROI
90%
Reduction in manual role effort
85%
Faster access alignment
3-5x
ROI
within 12 months
Why Teams Choose Identity Confluence
1.
AI-Driven Role Intelligence
Most role mining tools generate candidate roles that need weeks of manual validation before they're usable. Identity Confluence builds roles from actual access patterns and behavioural data.

2.
Built for Unified Identity Governance
Role mining isn't a separate step that feeds into governance later. In Identity Confluence, mined roles connect directly to lifecycle automation, access reviews, and policy enforcement.

3.
Continuous Governance and Optimization
Most role models are built once and ignored until they're too broken to use. Identity Confluence continuously refines mined roles as your organisation changes so access stays aligned to reality.

GET A PERSONALIZED DEMO


