Identity Confluence
Universal Application Sync Framework
One Framework to Connect, Sync, and Govern Every Application
Automate identity sync across HR systems, IDPs, SaaS apps, databases, and on-prem infrastructure with 200+ pre-built connectors and zero custom code.
Trusted by



Every Disconnected App Is a Governance Blind Spot
Your IGA platform is only as good as what it can see. Every app it cannot reach means orphaned accounts nobody reviews, access nobody revokes, and audit evidence nobody can find.
See It in Action →
One Sync Engine. Every Application. Continuous Governance
Connect 250+ apps via pre-built, API-first, or custom connectors.
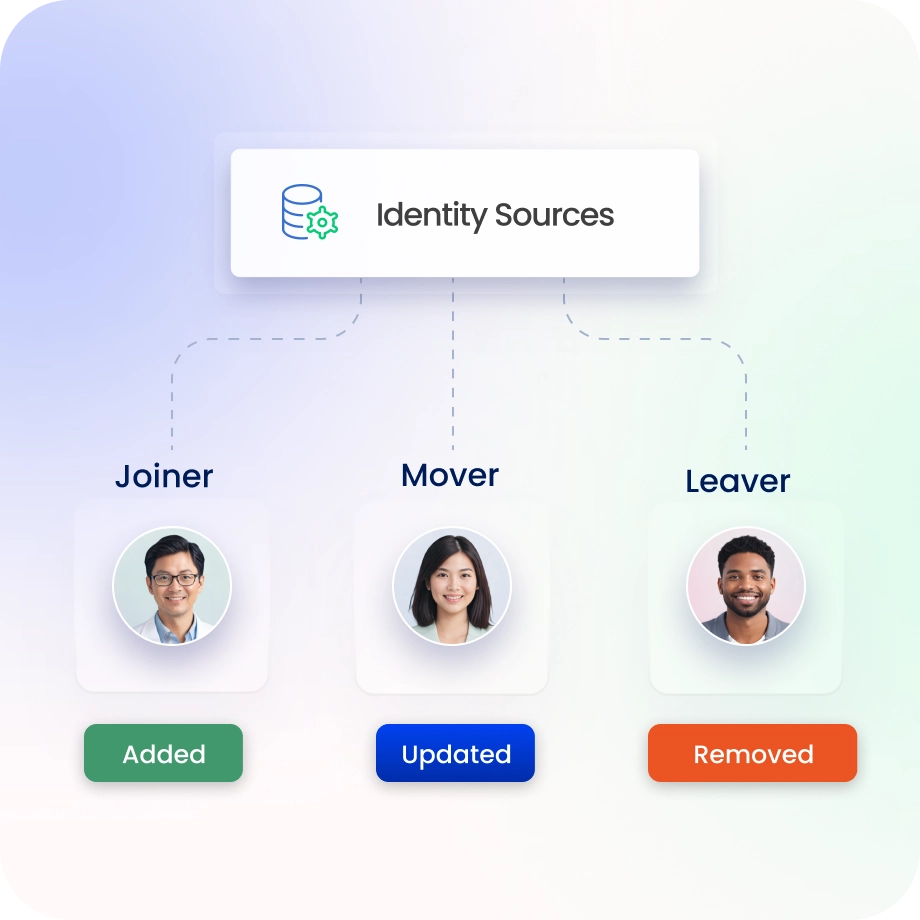
Trigger joiner, mover, and leaver workflows the moment an HR event fires.
Surface orphaned accounts and permission drift through continuous reconciliation.
Sync identity data across every system in real time.
Capture audit evidence automatically for every event.
Every Identity Capability. One Unified Platform.
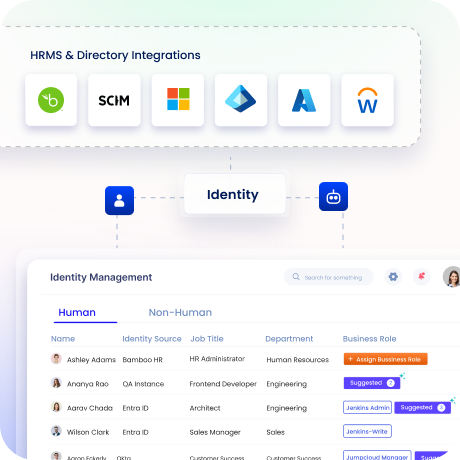
Unified Identity Inventory
Every real user, service accounts, APIs, bots, mapped into one source of truth.
Orphaned accounts, shadow identities, and ungoverned access surface the moment they form.
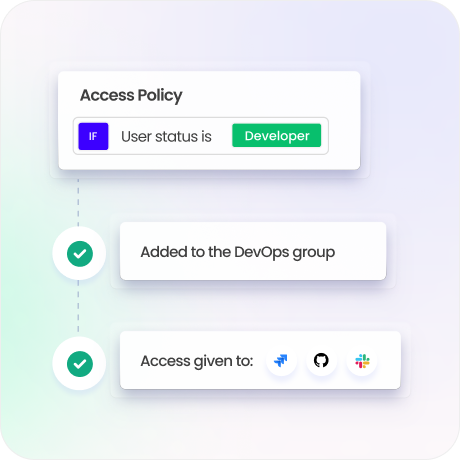
Centralised Policy Engine
Define least-privilege policies once, then enforce them across every connected app without rewriting a single rule.
Eliminate conflicting rules across siloed tools with a single governance layer.
Simulate and validate policy changes before deploying to production.
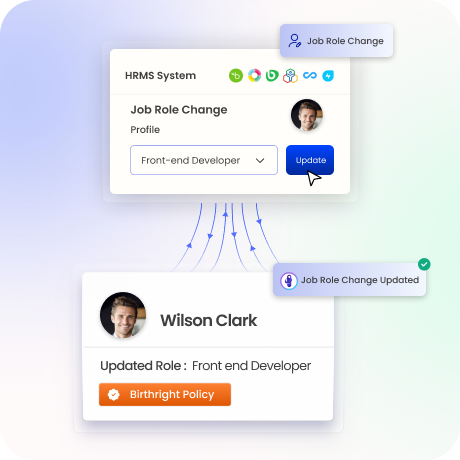
Automated Identity Lifecycle
HR-event-triggered provisioning and deprovisioning across all connected systems.
Joiner, mover, and leaver workflows execute in minutes, not days.
Zero orphaned accounts. Zero residual access after termination.
Compliance and Evidence Center
Access certifications, reconciliation, and policy violation detection from one platform.
Pre-configured reports for SOC 2, DPDPA, ISO 27001, SOX, HIPAA, GDPR, and more.
Continuous audit trails that replace manual evidence assembly across multiple tools.

250+ Pre-Built Connectors
Native integration with Okta, Entra ID, Workday, SAP SuccessFactors, ServiceNow, and more.
Replaces bespoke point-to-point integrations with a governed, auditable sync framework.
Custom connector framework for disconnected and legacy applications not in the catalog.

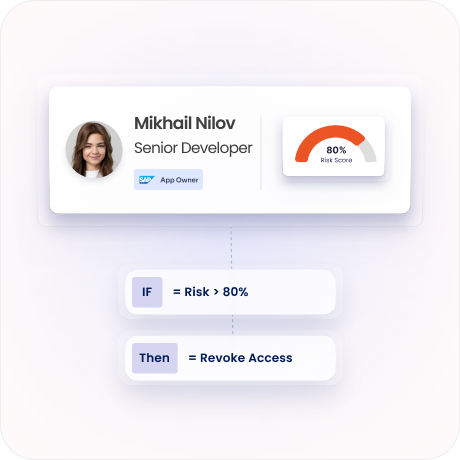
AI-Driven Identity Risk Analytics
Risk scoring and anomaly detection across your entire consolidated identity data set.
Surface over-privileged accounts, stale access, and policy drift before they become incidents.
Context-rich signals that no single-point tool can produce in isolation.
Drive measurable value with Identity Confluence
Download the ROI Report
30-min
onboarding achieved
100%
audit evidence captured
3-5x
ROI
within a year
Why Teams Choose Identity Confluence
1.
Unified Identity Inventory
Purpose-built on one data model and one policy engine, not acquired tools stitched together.

2.
Govern every identity type
Human users, contractors, service accounts, bots, and API credentials governed under the same platform, the same policies, and the same audit trail.

3.
No rip and replace required
API-first architecture and 250+ pre-built connectors integrate into your existing stack. Deploy alongside what you already run, expand coverage incrementally.



