Simplify Access Reviews and Eliminate Certification Fatigue
Hundreds of rows. No context. No time. That's how rubber-stamp approvals happen. Replace manual certifications with risk and context based reviews that focus effort where it counts.
Trusted by



Access Reviews Are Repetitive, Manual, and Prone to Error
Reviewers get hundreds of decisions with no context and no time, so they approve everything. Fatigue does not just slow certifications down, it makes them meaningless.
See It in Action →
Modernize Access Certifications with Risk-Based Governance
Automate access certifications across identities, roles, and systems
Surface high-risk access first so reviewers see what actually matters
Deliver context-aware recommendations for accurate decisions
Enforce least privilege automatically through policy-driven controls
Continuously validate access so reviews reflect reality, not snapshots
Advanced IGA Features to Eliminate Access Review Fatigue
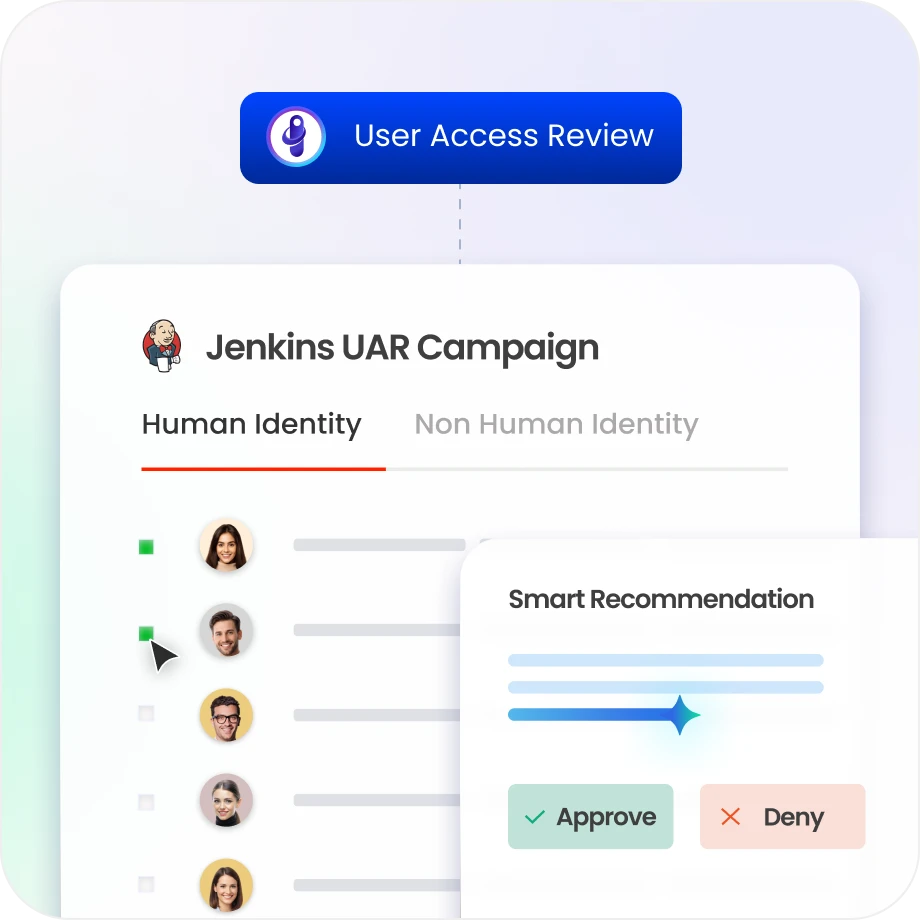
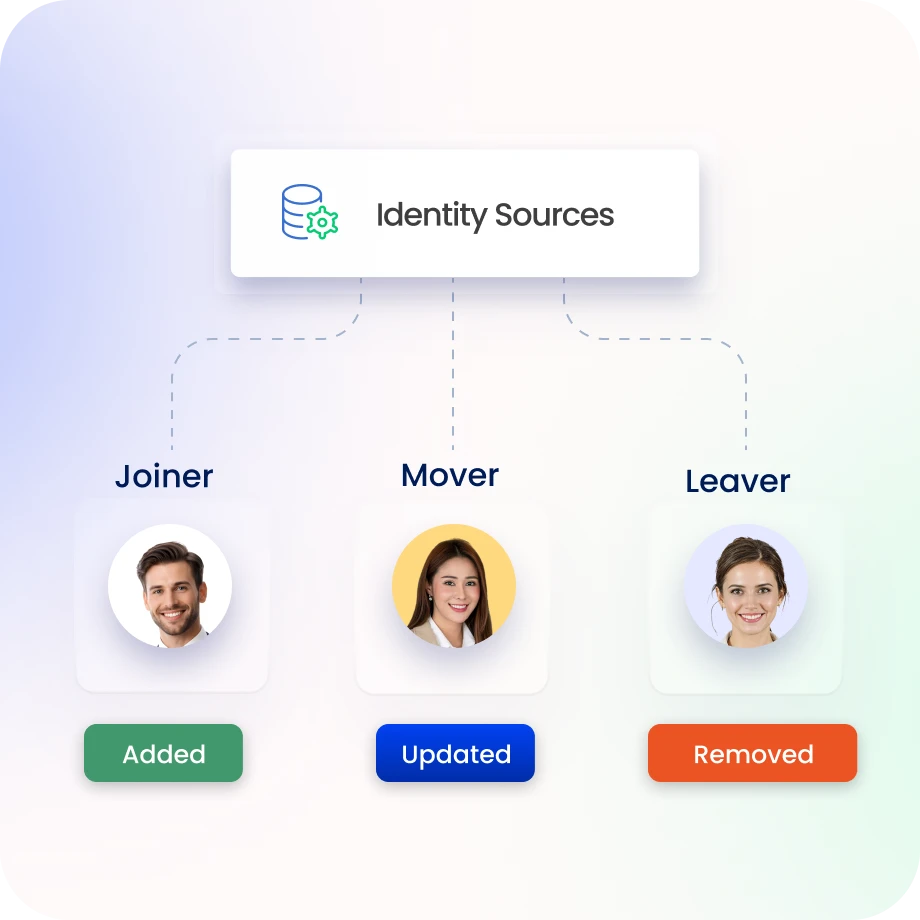
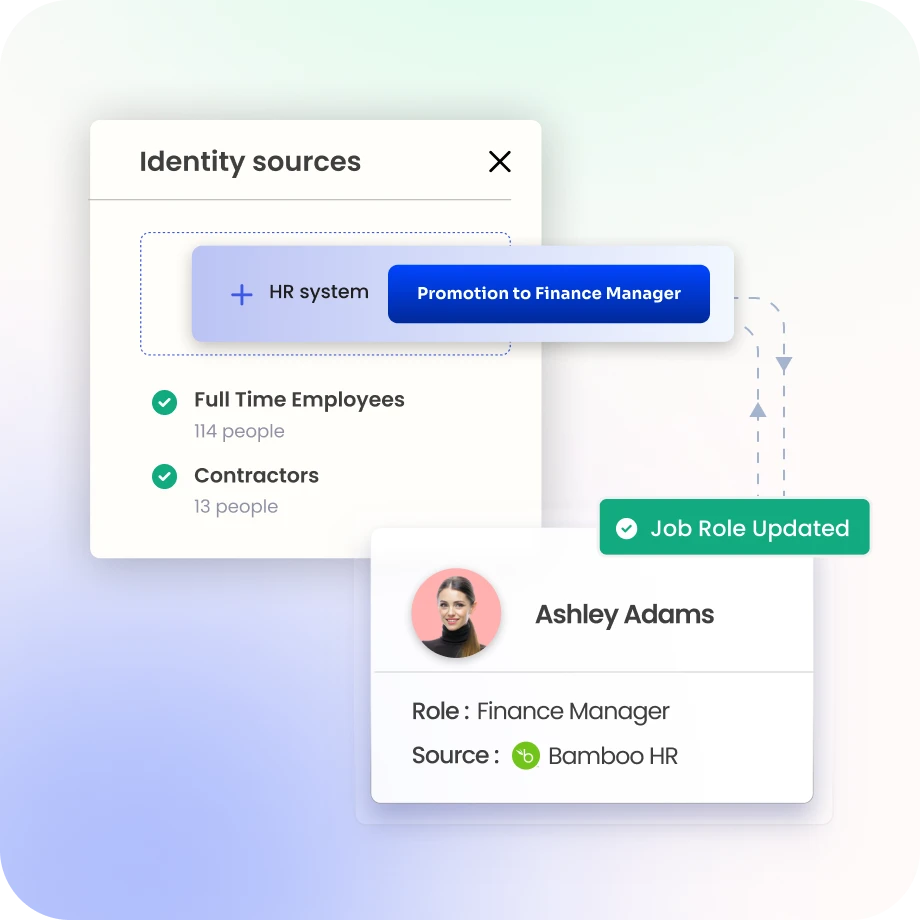
Automate Lifecycle-Triggered Reviews
Onboarding, role changes, and offboarding trigger access reviews automatically, with no manual scheduling.
Ensure access evolves with user roles and responsibilities.
Trigger access reviews automatically during lifecycle events and policy changes.
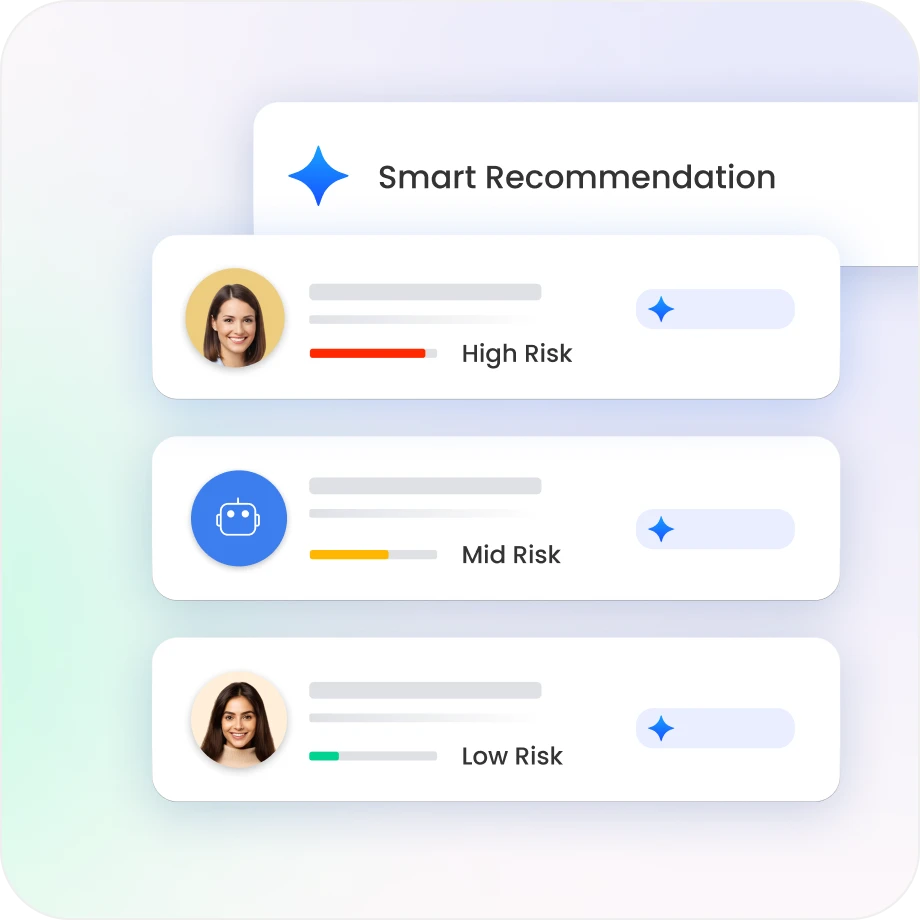
Cut Review Volume with Risk Prioritisation
High-risk users, roles, and entitlements surface to the top. Everything else stays out of the way.
Reviewers stop wading through hundreds of low-risk rows to find the three that matter.
Risk signals dynamically re-rank certifications as the threat landscape shifts.
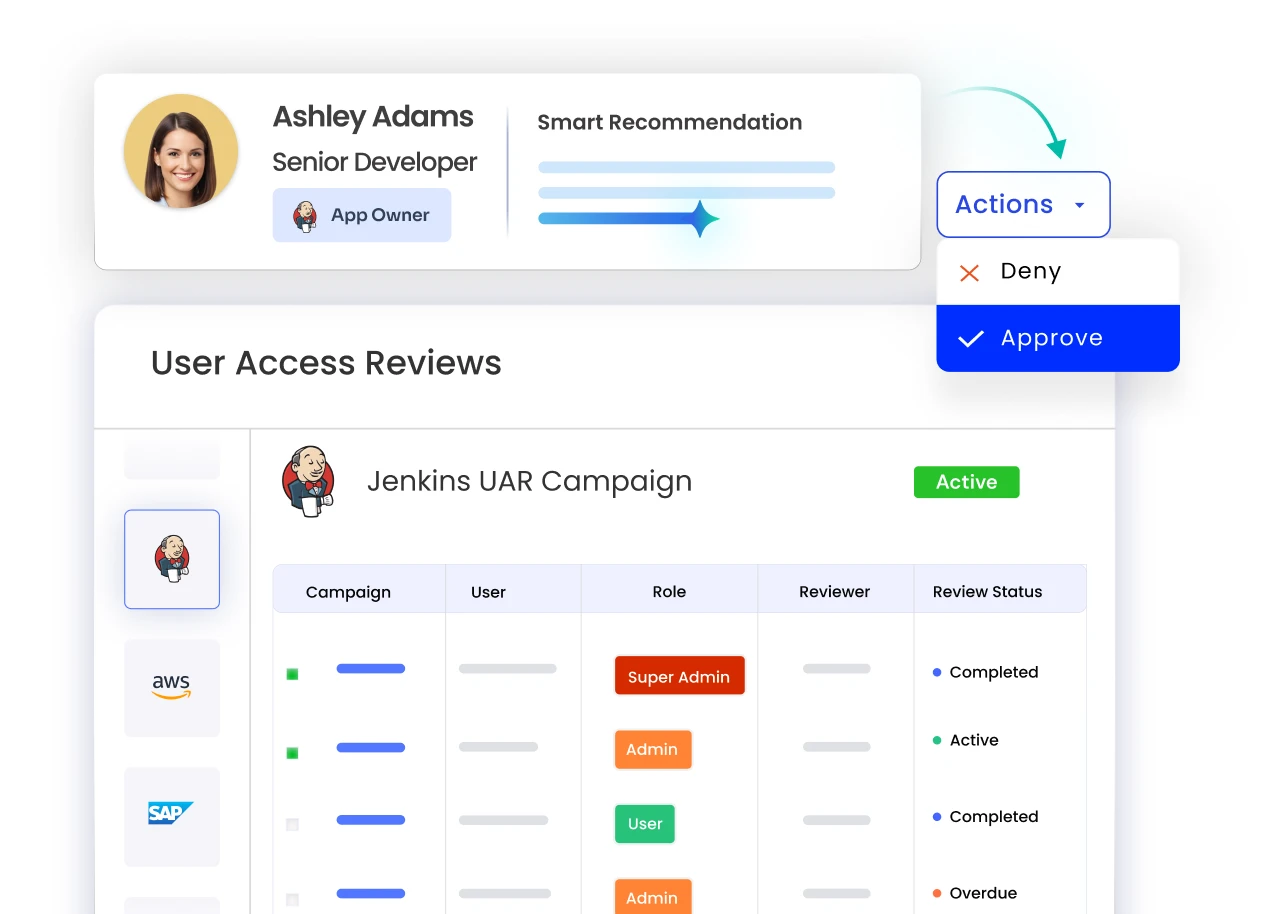
Enable Faster Decisions with Contextual Insights
Access history, last-used date, risk score, and entitlement source are all visible before a reviewer clicks anything.
Informed decisions replace instinct. Accurate revocations replace rubber stamps.
Identity behaviour context means reviewers catch anomalies that a blank approval form would miss entirely.

Simplify Governance with Roles and Entitlements
Define roles with mapped entitlements so certifications review access in logical groups, not individual rows.
Role-based review models cut the decision count without cutting coverage.
Continuous reconciliation keeps roles and entitlements aligned.
Prevent Risk with Policy Enforcement
Enforce governance policies across identities and access
SoD conflicts surface and get blocked during the review, before they become an audit finding.
Policy checks and access analytics run in the background.
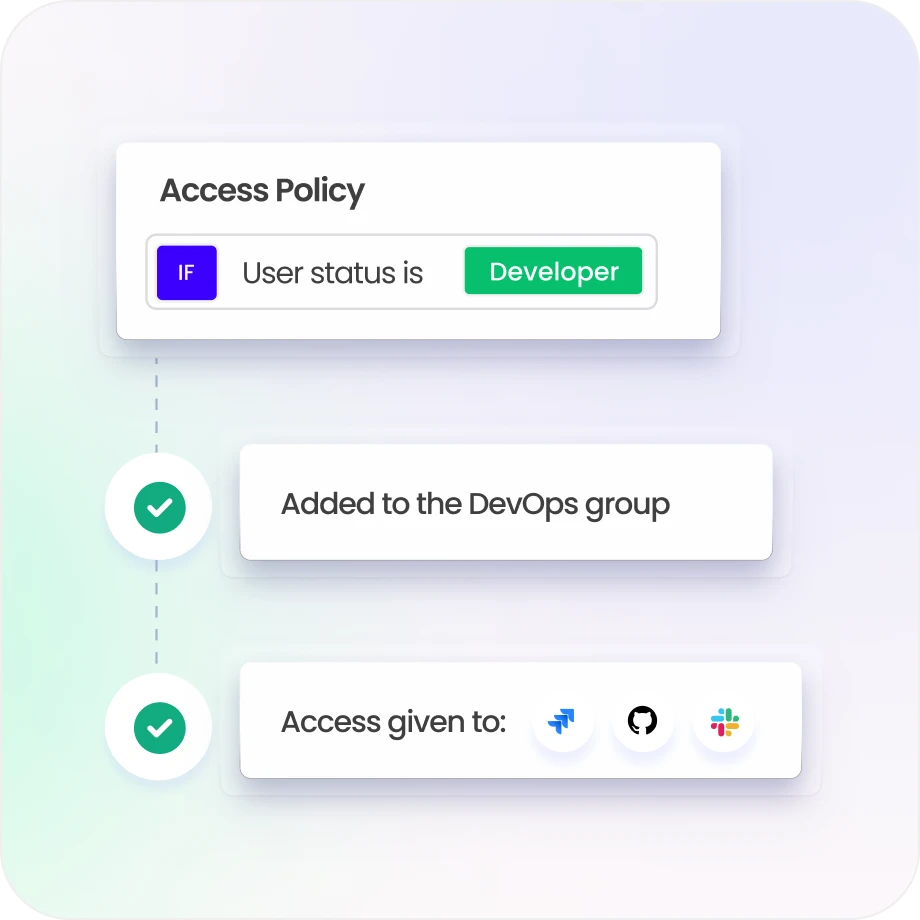
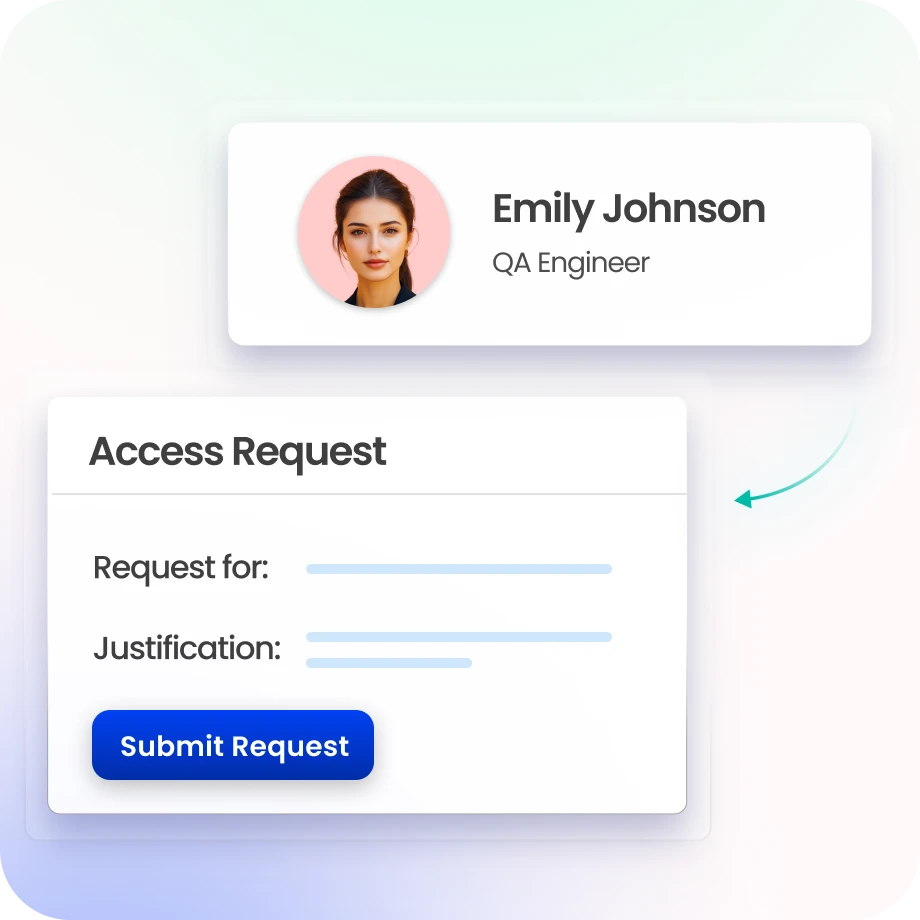
Streamline Requests with Smart Approvals
Enable self-service access requests with approval workflows.
Route requests based on role, risk, and ownership.
Automate approvals using smart workflows and policy-based routing.
Ensure Compliance with Audit-Ready Reporting
Generate audit-ready reports with complete timestamped trails.
Full visibility into every access decision and change, centralised in one dashboard.
Pre-built reports for SOC 2, ISO 27001, SOX, HIPAA, and GDPR.

Drive measurable value with Identity Confluence
Download the ROI Report
88%
reduction in review fatigue
86%
faster certification decisions
3-5x
ROI
within 12 months
Why Teams Choose Identity Confluence
1.
Built around the reviewer
Most IGA tools generate certifications. Identity Confluence generates certifications that are actually completable, with risk prioritisation and auto-completion.

2.
Context-Driven Governance Intelligence
Usage data, risk scores, and identity behaviour signals mean reviewers make decisions based on evidence.

3.
Unified Governance Across All Identities
Workforce accounts and non-human identities all certified under one governance model, with consistent policy enforcement and a single audit trail.

GET A PERSONALIZED DEMO


