Eliminate Excess Access Before It Becomes a Breach
Access piles up quietly through role changes, forgotten approvals, and permissions nobody revoked. Continuously enforce least privilege before over-provisioning becomes your next incident.
Trusted by



Permission Creep Is Expanding Your Attack Surface
Nobody grants excess access on purpose. It accumulates role by role, approval by approval, until over-privileged accounts are everywhere and nobody knows who has what.
See It in Action →
Enforce Least Privilege with Smart Identity Governance
Find and fix over-provisioned users, roles, and entitlements now
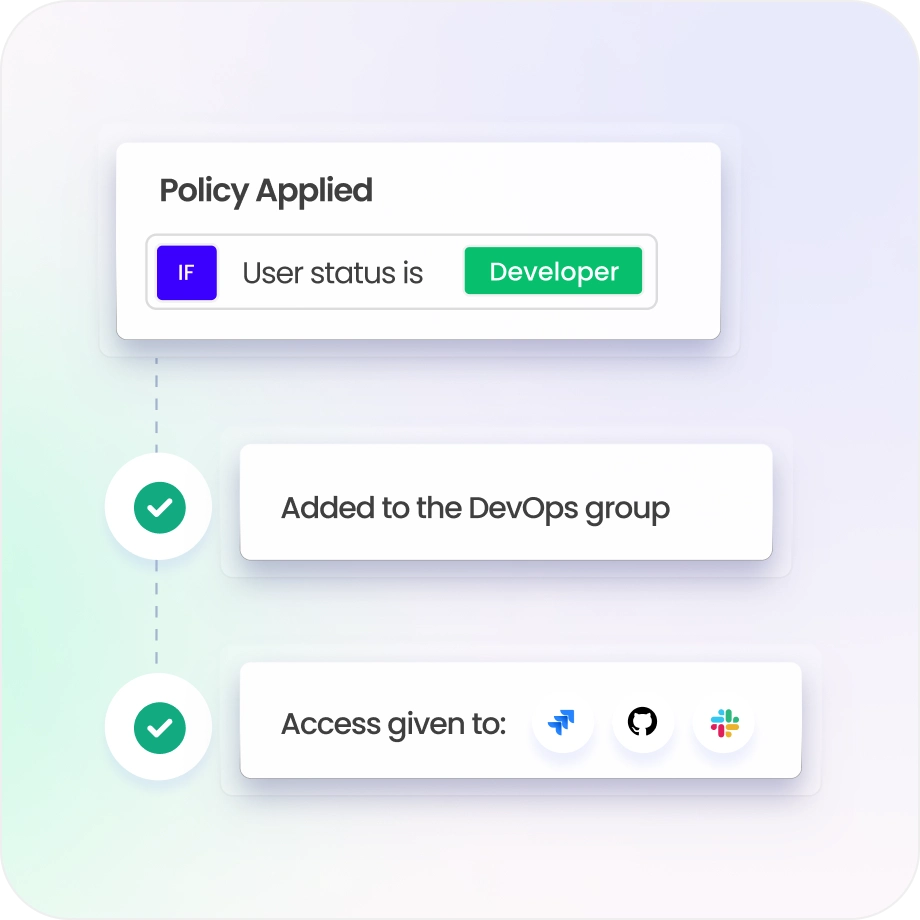
Enforce least privilege with role-based and policy-driven governance
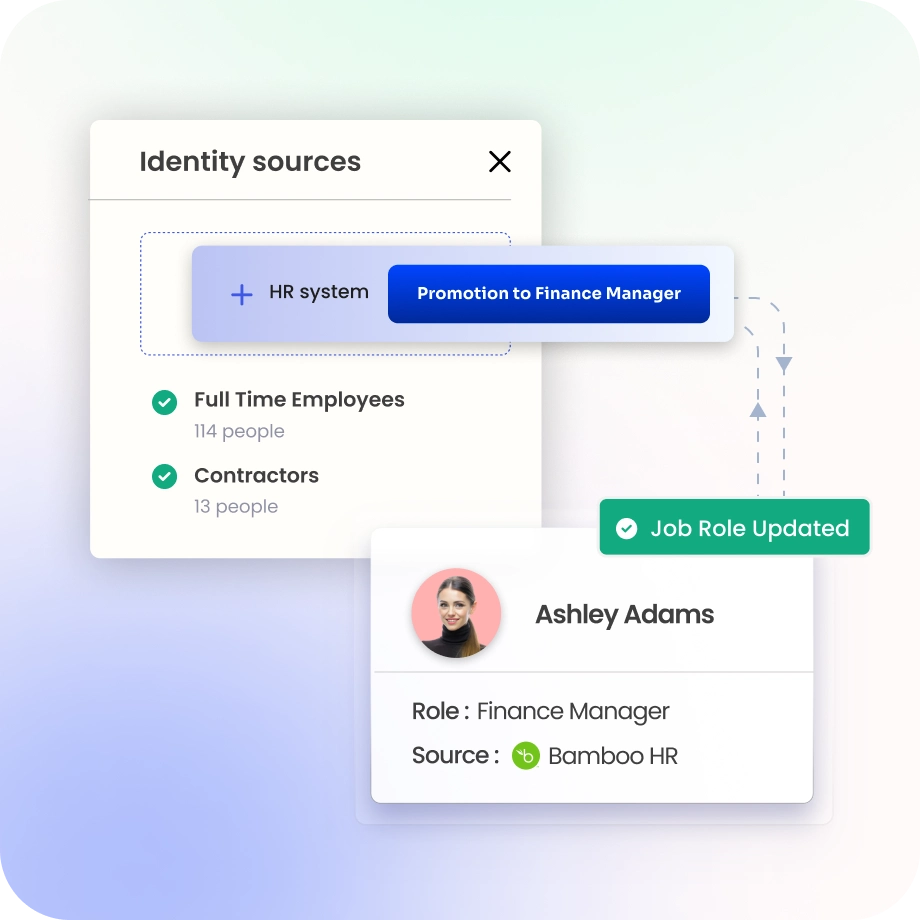
Automate lifecycle changes so access never outlasts its purpose
Detect high-risk access with context-aware, real-time intelligence
Control every identity type, including workforce, service accounts, and APIs.
Continuous Identity Governance for Least-Privilege Access
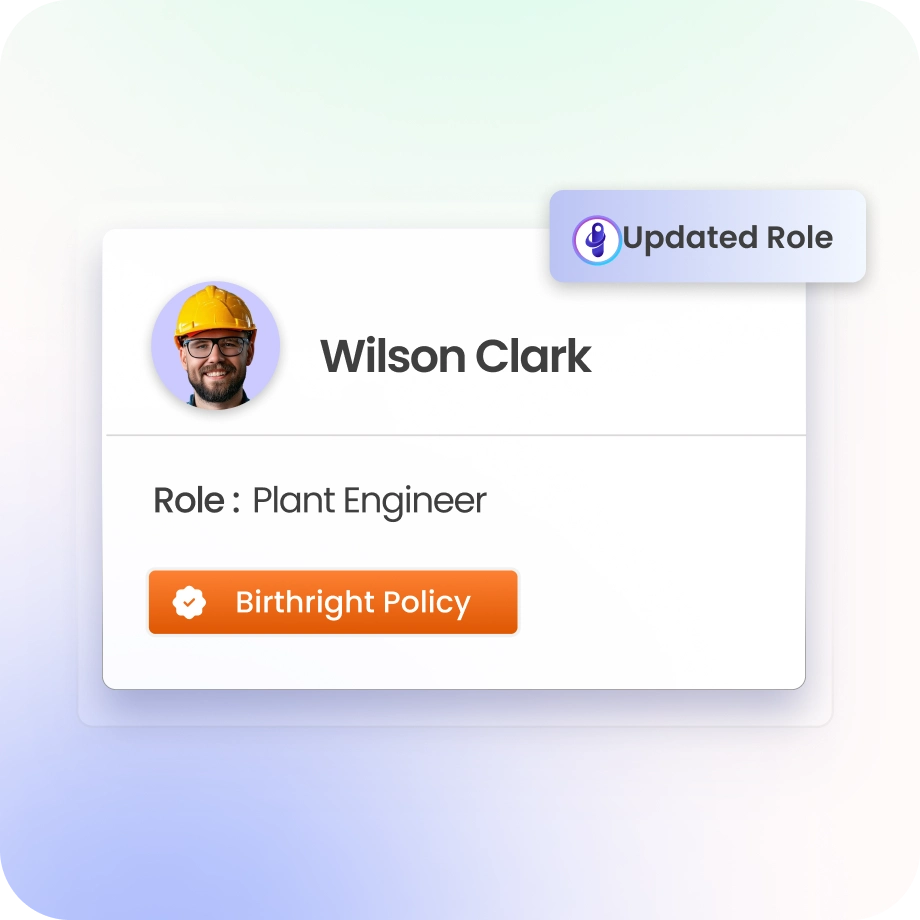
Prevent Access Accumulation
Continuously align entitlements with current roles so permission buildup stops before it starts.
Eliminate outdated access automatically the moment responsibilities change.
Eliminate Over-Provisioning
Enforce least privilege using role and policy-based access controls.
Every access request follows governance and approval rules, with no exceptions or workarounds.
Continuously validate permissions so entitlement drift never quietly becomes a breach vector.
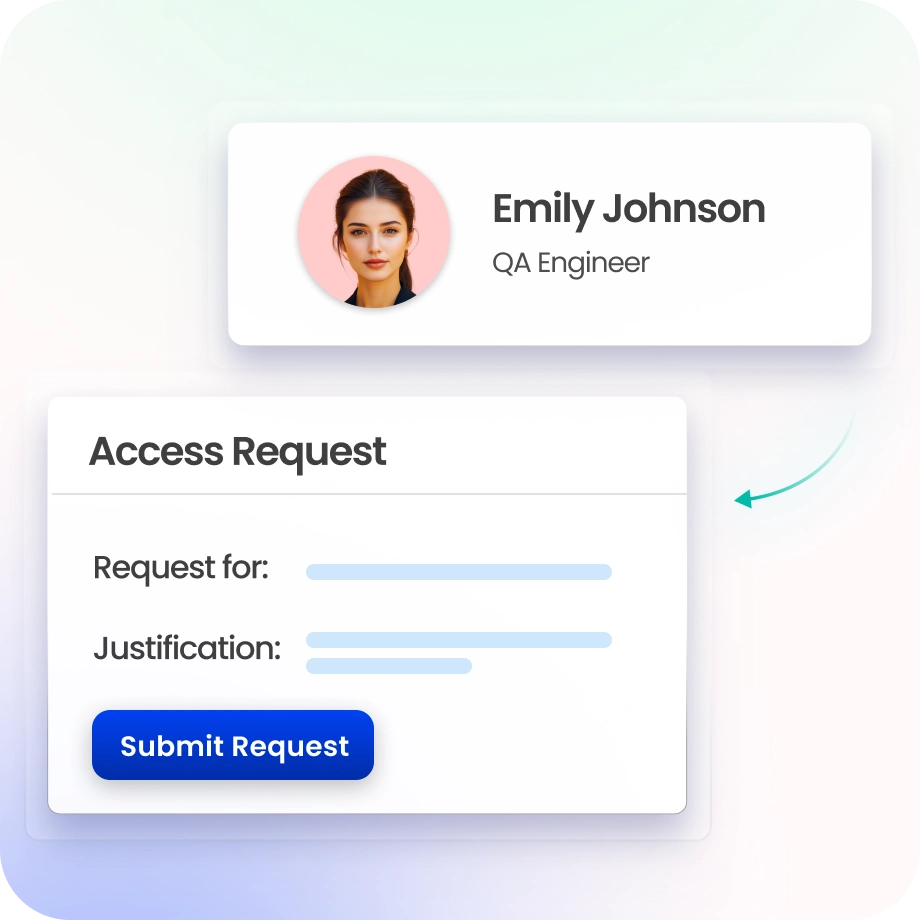
Control Access Request Workflows
Self-service access requests with policy-based approvals deliver speed without compromising control.
Role, risk, and policy validation runs at every step, not just at the point of approval.
Smart workflows send requests to the right approver based on context, not a static list.
Govern Roles and Entitlements
Model roles against real business functions and map entitlements to enforce least privilege access.
Discover and govern access rights across human and non-human identities.
Reduce entitlement sprawl so fewer permissions per identity mean a smaller blast radius when things go wrong.

Validate Access with Risk-Based Reviews
Risk-based access reviews surface what matters, so managers see scores, usage data, and access sources.
Auto-completion handles low-risk, uncontested access so reviewers focus on what actually needs a decision.
Reduce review fatigue without reducing coverage. Better outcomes in a fraction of the time.

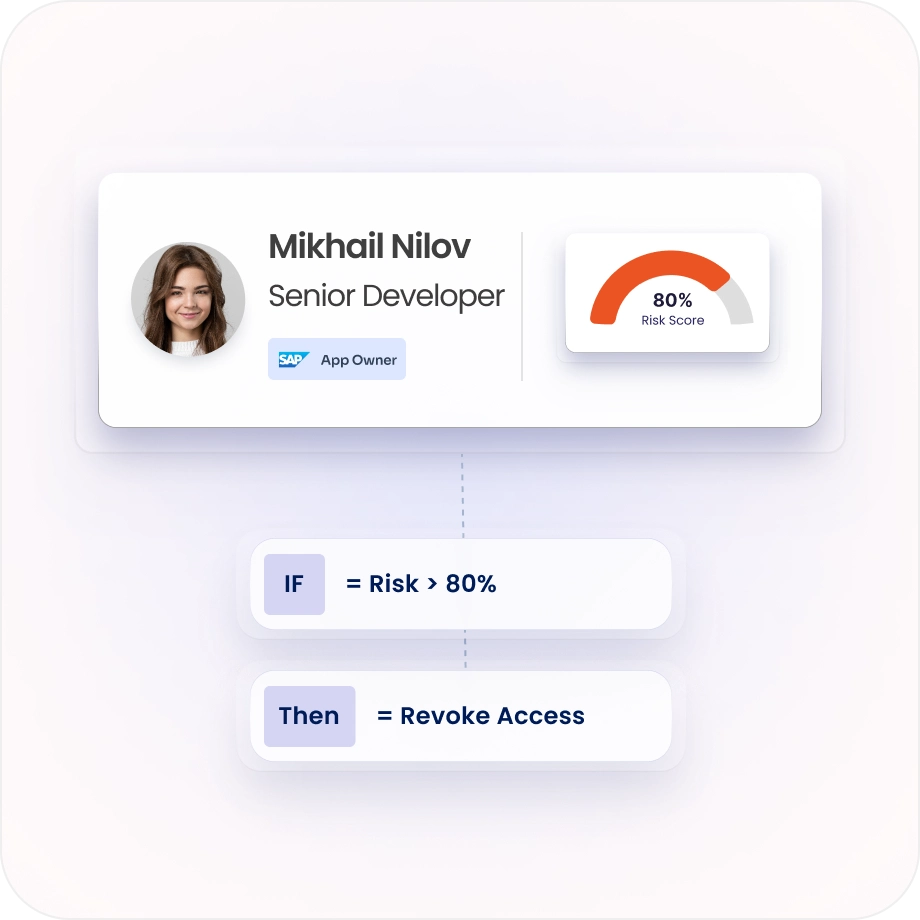
Detect Risk with Policy Intelligence
Continuously enforce least-privilege policies across every connected system, not just at review time.
Risk scoring and context-aware insights surface anomalous access patterns before they escalate.
ISPM signals identify over-privileged access in real time so remediation happens fast, not after the fact.
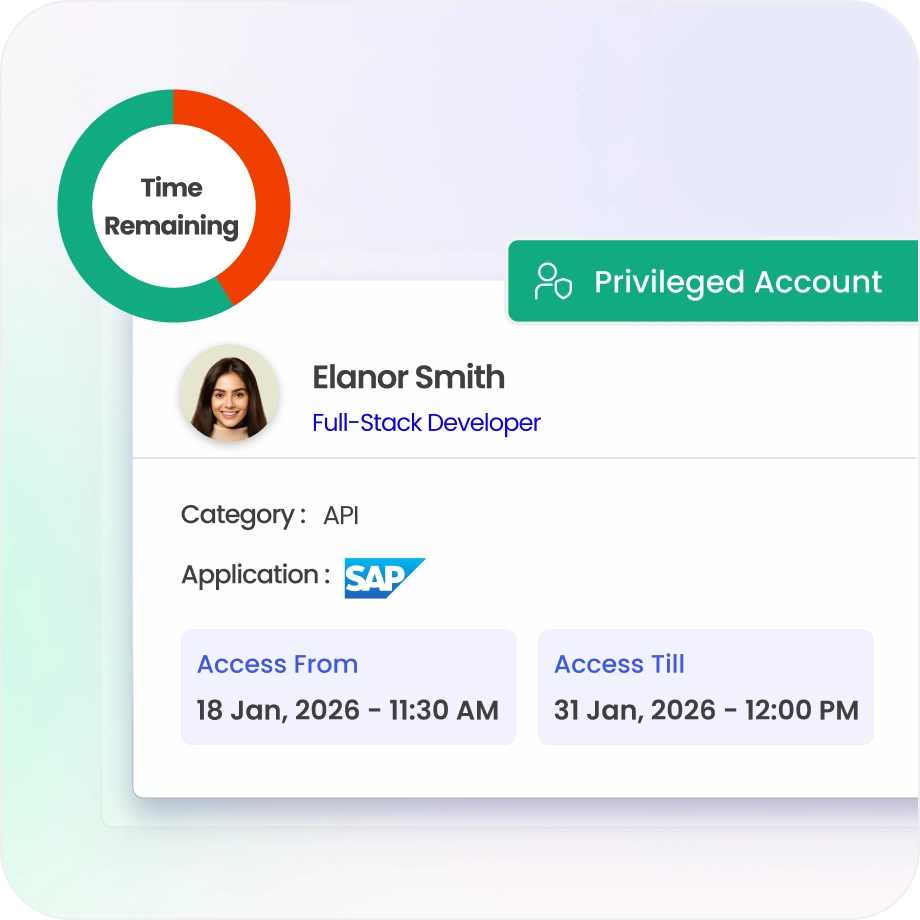
Minimise Privileged Access Risk
Apply stronger governance to privileged and high-risk accounts, the ones attackers target first.
Enforce controlled, policy-driven permissions to limit excessive administrative access across your environment.
JIT access eliminates standing privileges so elevation is temporary, logged, and revocable.
Accelerate Compliance Readiness
Every access decision and lifecycle event generates a real-time audit trail automatically.
Pre-built compliance evidence for SOX, GDPR, DPDP, ISO 27001, and SOC 2 is ready in one click.
With advanced Evidence Center audit preparation drops from weeks to hours. The evidence is always current, never retrospective.

Drive measurable value with Identity Confluence
Download the ROI Report
92%
Reduction in excess permissions
88%
Faster access remediation
3-5x
ROI
within 12 months
Why Teams Choose Identity Confluence
1.
Built for Continuous Access Governance
Most governance tools catch excessive permissions during quarterly reviews. Identity Confluence catches them the moment they form and acts before your next review cycle even starts.

2.
Intelligent, not just automated
Context-aware insights and risk scoring mean reviewers focus on over-privileged access that actually matters, not rubber-stamping hundreds of rows nobody has reviewed in months.

3.
Unified Governance Across All Identity Types
Enforce consistent policy across workforce identities, and non-human identities, with 250+ pre-built integrations to connect your full stack.



