Every Machine Identity. Visible. Governed. Secured.
Service accounts, API keys, bots, and workload identities are multiplying faster than anyone is governing them. See everyone. Own every one. Control every one.
Trusted by



NHI Sprawl Is Your Largest Identity Blind Spot
Machine identities outnumber humans 45 to 1. Most have no owner, no review cycle, and no expiry. When a service account gets compromised, nobody notices until the damage is done.
See How We Fix This →
Discover, Own, and Control Every Non-Human Identity.
Auto-discover every service account, API key, bot, and workload identity
Assign human ownership to every NHI so no identity goes unclaimed.
Apply least-privilege policies and enforce credential expiry across all NHI types
Run certification campaigns for NHIs alongside your human access reviews
Generate audit-ready evidence for every machine identity lifecycle event
Non-Human Identities Governed Like Every Other Identity
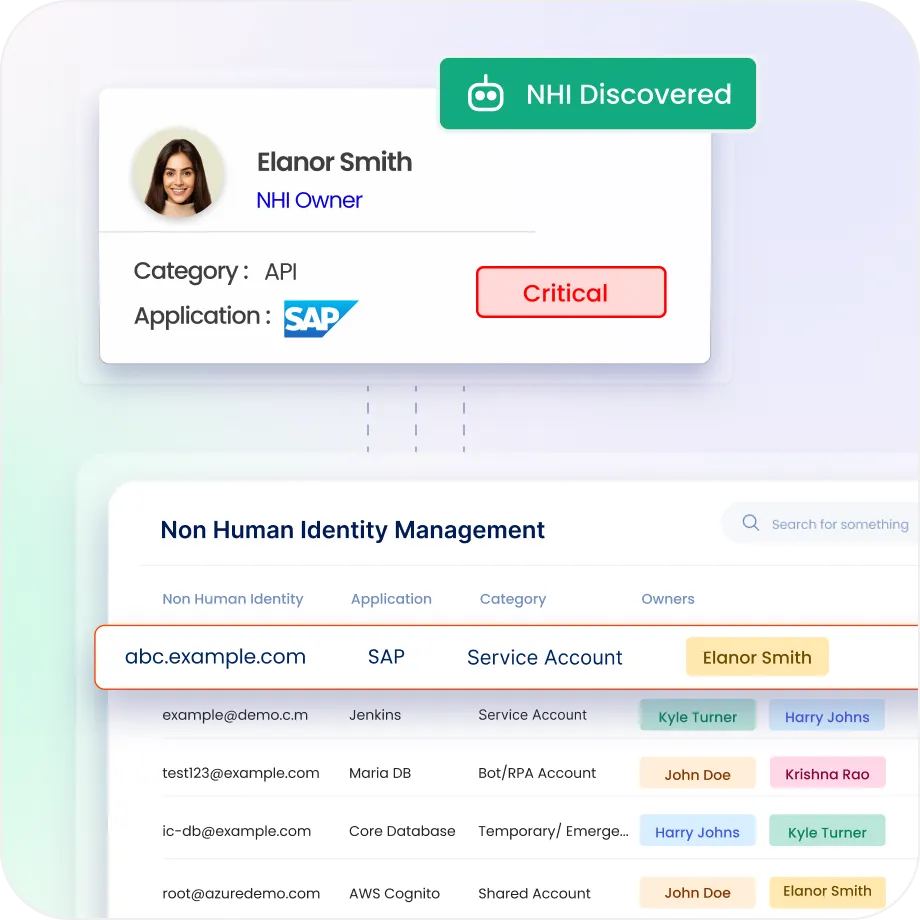
Automated NHI Discovery
Scan every connected identity source to surface non-human identities, including the ones nobody catalogued.
Classify NHIs by type, risk level, and activity status, and take a specific governance action.
Map human ownership to every non-human identity. Flag anything with no assigned owner.
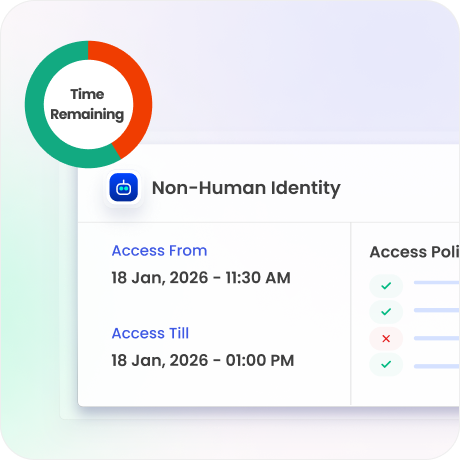
Govern the Full NHI Lifecycle
Automate the full NHI lifecycle from provisioning and access assignment through to revocation.
Define risk-based rotation policies at intervals and send automated reminders to owners without forced revocation that breaks systems.
Automatically transfer NHI ownership to a pre-configured successor when an owner exits.
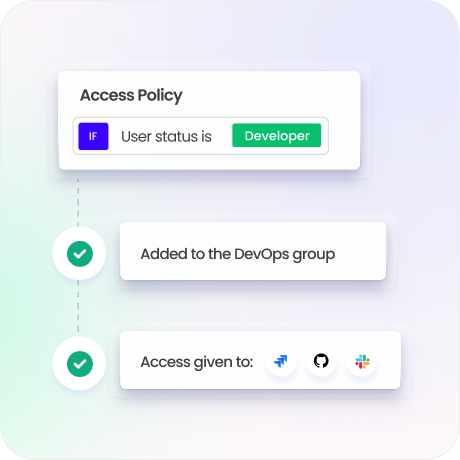
Policy-Based Access Control
Apply least-privilege policies to every NHI ensuring service accounts access only what they need.
Define and enforce usage policies specific to each NHI type
Privilege sprawl triggers an alert the moment NHI permissions exceed defined policy thresholds.
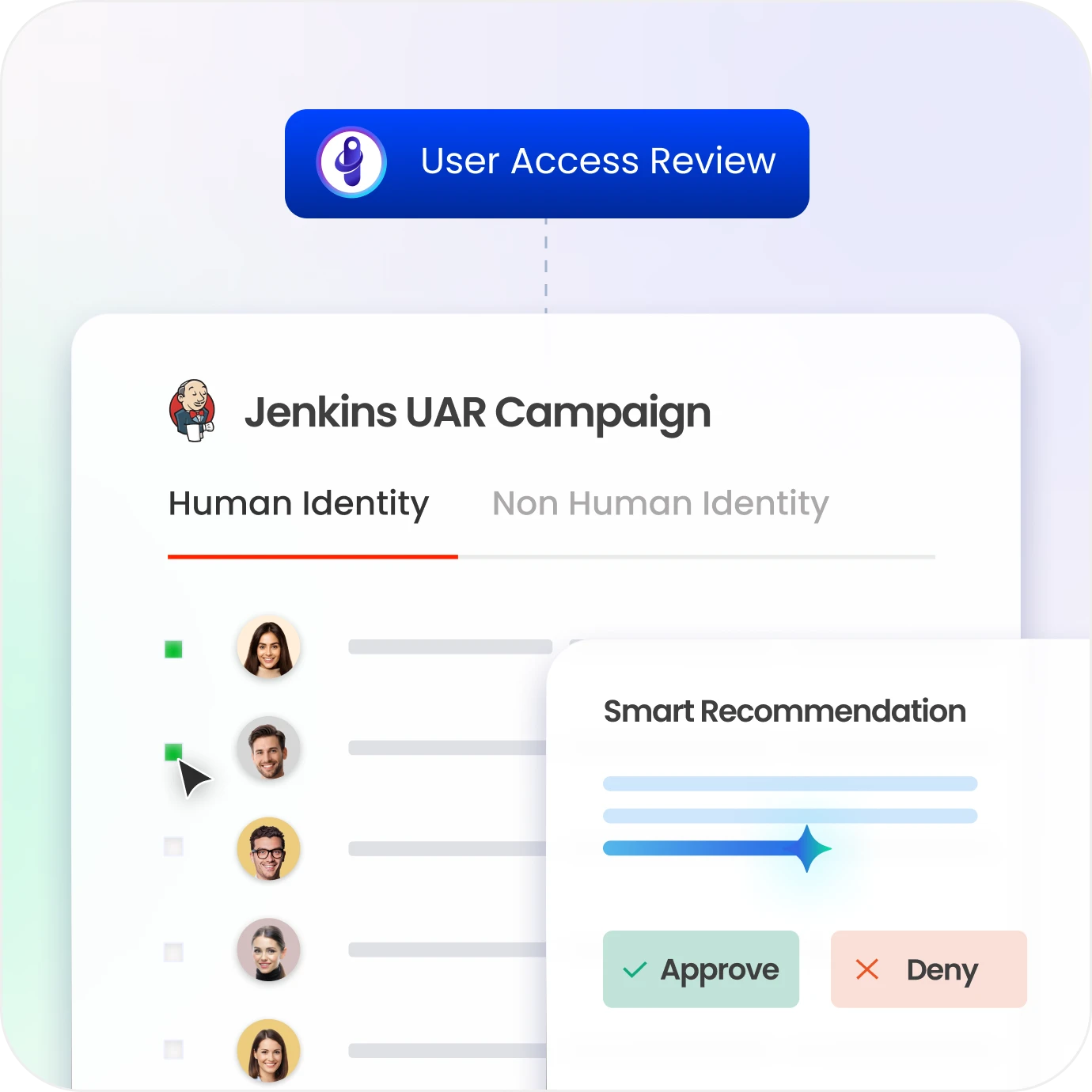
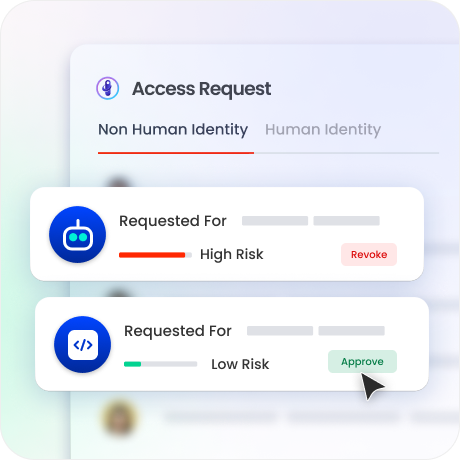
Certify NHI Access Like Human Access
Run certification campaigns for non-human identities using the same workflows applied to human access.
Route review requests to assigned NHI owners with context on permissions, usage, and risk scores.
Auto-revoke access for NHIs that fail certification or remain unreviewed past defined deadlines.
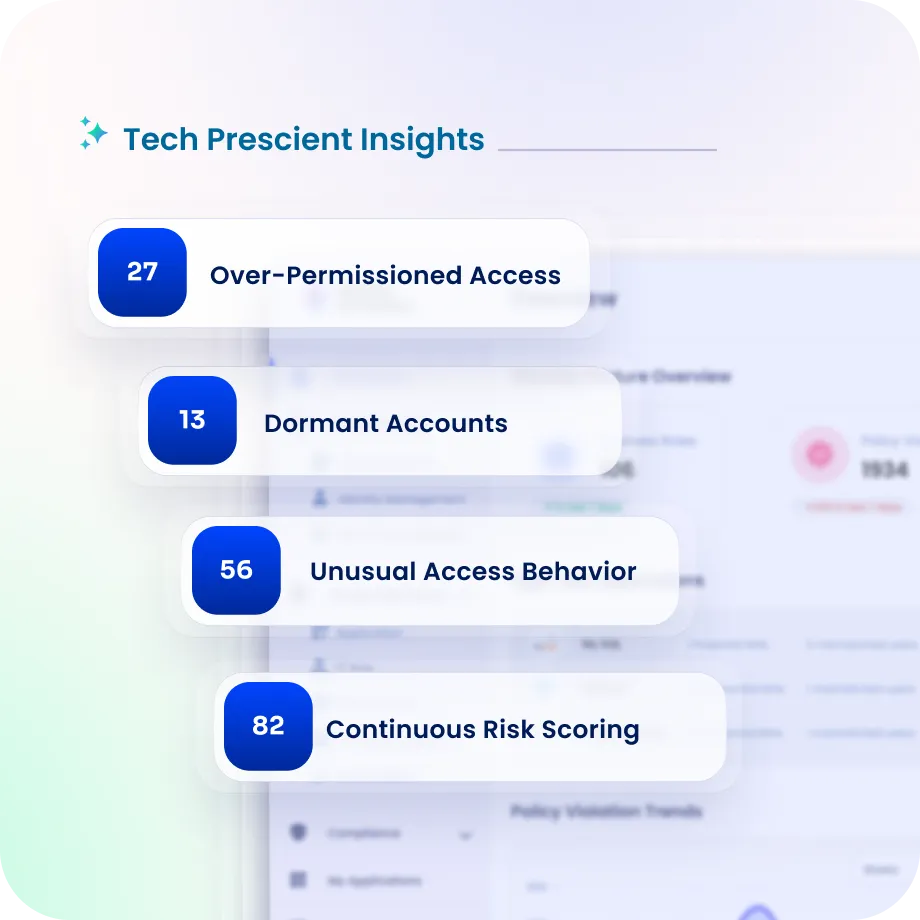
Detect Risk Before It Becomes a Breach
Every NHIs is scored by risk using analysis of permission scope, credential age, and access patterns.
Over-permissioned accounts, dormant service accounts, and identities with unusual behaviour surface in real time.
Security teams get a continuous NHI posture dashboard, not a quarterly spreadsheet that is already out of date.
Prove NHI Governance to Auditors
Maintain complete audit trails for every NHI action - creation, permission changes,rotation and revocation.
Generate compliance-ready reports mapped to SOX, SOC 2, GDPR, and HIPAA with pre-built templates.
Demonstrate that non-human identities receive the same governance rigour as human accounts.

Drive measurable value with Identity Confluence
Download the ROI Report
100%
NHI visibility from day one
Zero
orphaned machine identities
Unified
governed inventory for every NHI
Why Teams Choose Identity Confluence
1.
One platform, humans and machines
Most IGA platforms were built for workforce identities. Non-human identities were added later or ignored entirely. Identity Confluence governs both under the same policies, workflows, and audit trails from the start.

2.
Lifecycle automation that doesn't break systems
Policy-driven rotation and deprovisioning replace manual processes, but with configurable intervals and owner reminders

3.
Built for the environments NHIs actually live in
API-first with 200+ pre-built connectors and flexible deployment across cloud and on-prem. AWS, Azure, GCP, and every major identity provider.



