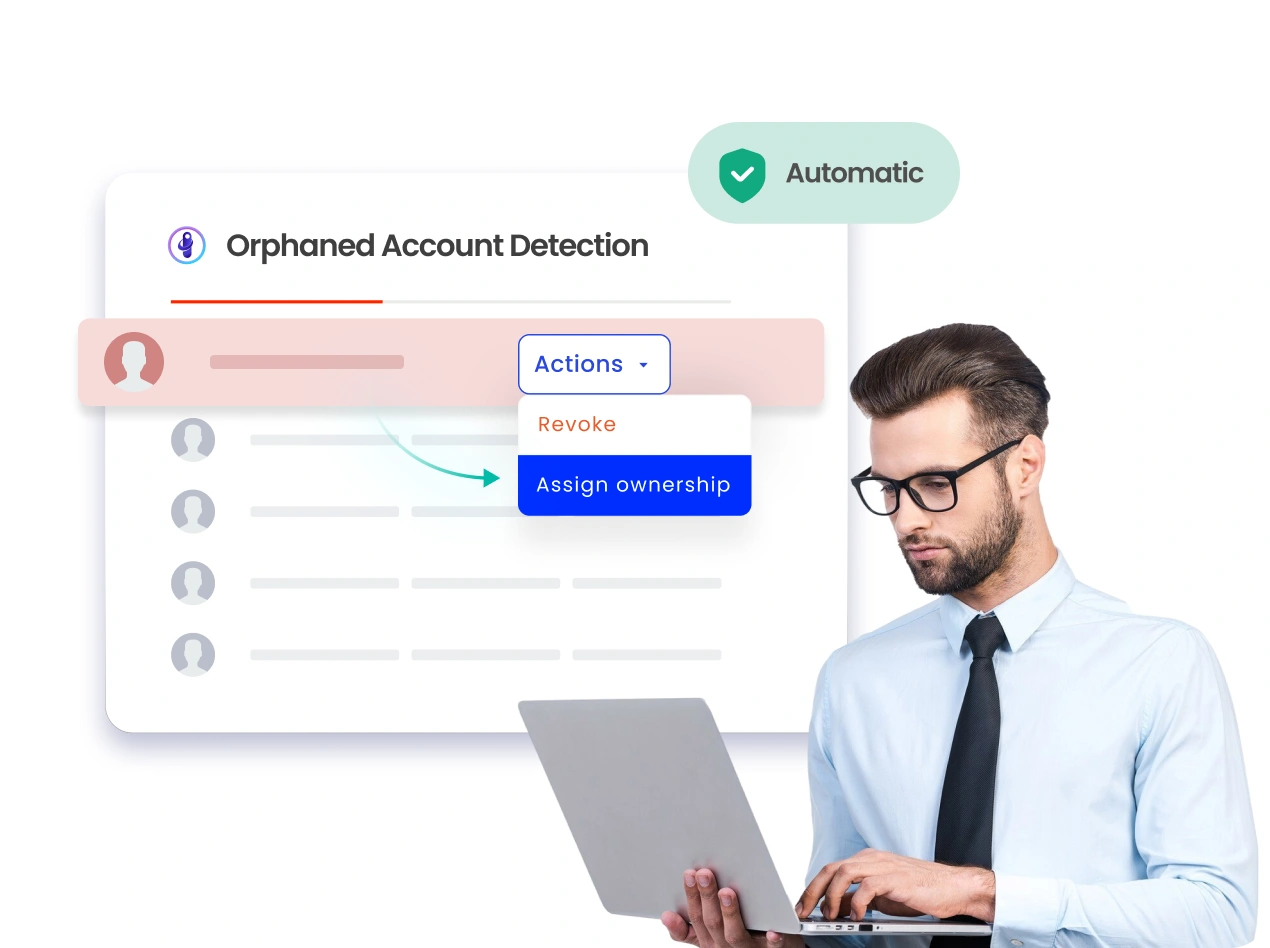
The Accounts Nobody Owns Are Your Biggest Security Risk
Orphaned accounts pile up every time someone leaves, changes roles, or a project ends. Automatically find them, assign ownership, and eliminate them, before attackers do.
Trusted by



You Can't Secure What You Can't See
Every departure, every role change, every failed project leaves accounts behind. No one owns them. No one reviews them. But they still have access, and that access is active.
See It in Action →
Eliminate Orphaned Accounts with Intelligent Governance
Surface every unowned, inactive, and unlinked account automatically
Govern identities with lifecycle controls from onboarding to offboarding
Deprovision access the moment it becomes unowned, no manual step needed
Certify ownership continuously, not just at audit time
See every identity, role, and entitlement in one place, always real-time
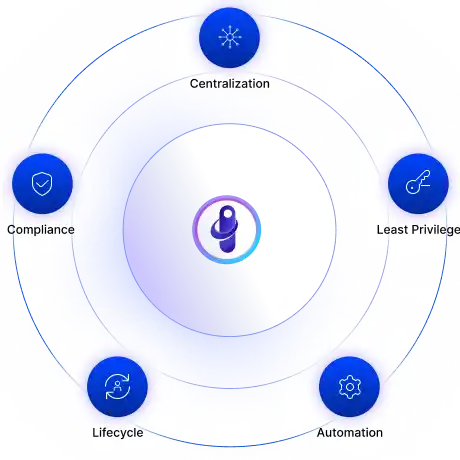
Eight ways Identity Confluence eliminates orphaned accounts
Stop Orphans Before They Form
Automate joiner, mover, and leaver workflows so no account outlives its owner.
Every role change triggers a review. Every departure triggers removal.
No manual steps. No accounts left behind.
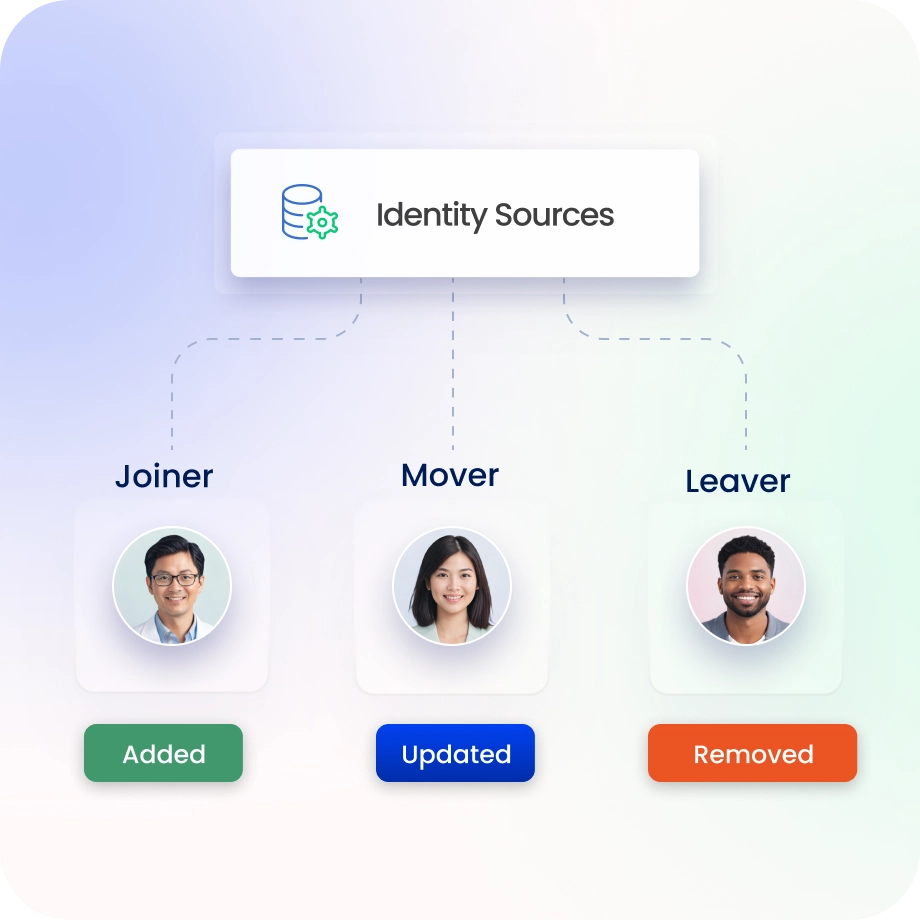
Remove Access the Moment It's Unowned
Lifecycle events such as terminations, transfers, and project closures trigger instant deprovisioning.
Policy rules enforce removal across HR systems, directories, and every connected application.
Orphaned accounts don't survive long enough to become a problem.
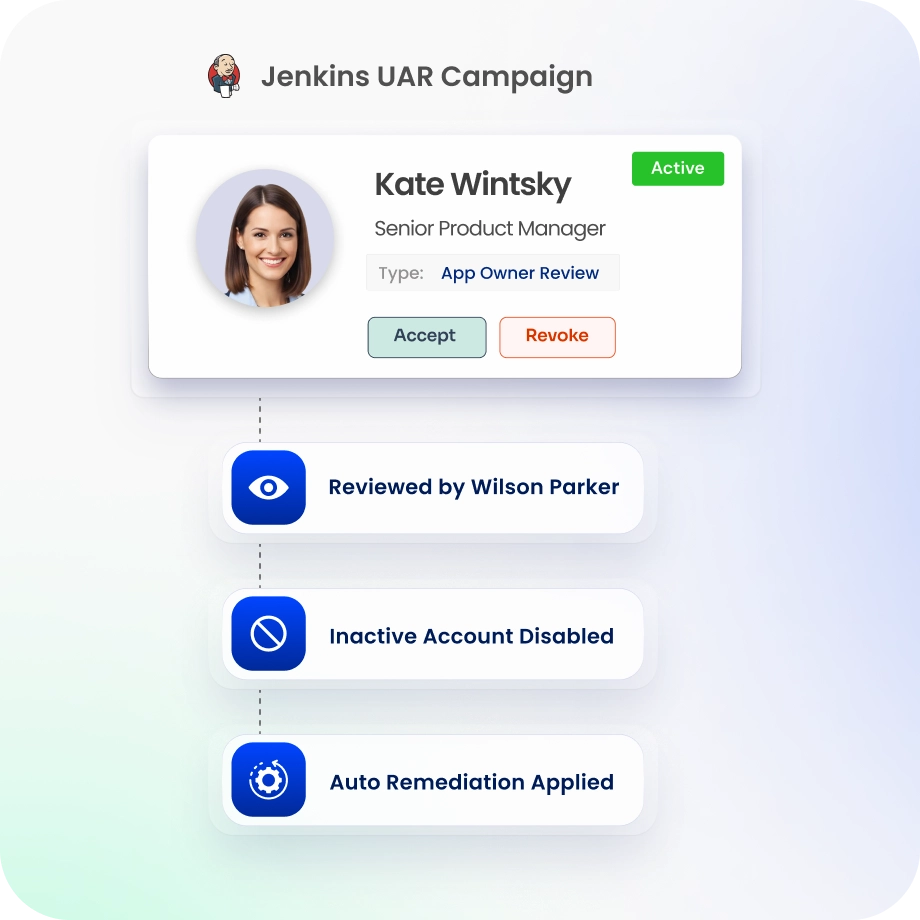
Certify Every Owner, Every Cycle
Scheduled reviews surface every account with missing, disputed, or outdated ownership.
Managers see risk scores, last-used dates, and access sources, not just a name and a checkbox.
Improve accuracy with context-aware insights and risk indicators.

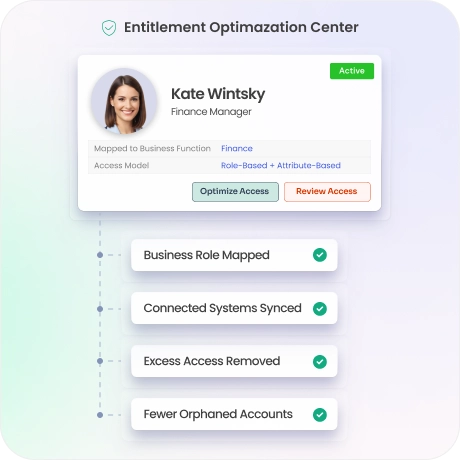
Cut Entitlement Sprawl at the Root
Model roles against actual business functions using role-based and attribute-based controls.
Discover entitlements across every connected system, then right-size them.
Fewer entitlements per identity means fewer orphaned accounts when people leave.
Block Risky Access Combinations
Dynamic policy controls enforce least privilege across every access request and role assignment.
Segregation of Duties (SoD) enforcement catches conflicting access before it's granted.
Orphaned accounts with policy violations are identified immediately, not just during your next audit.

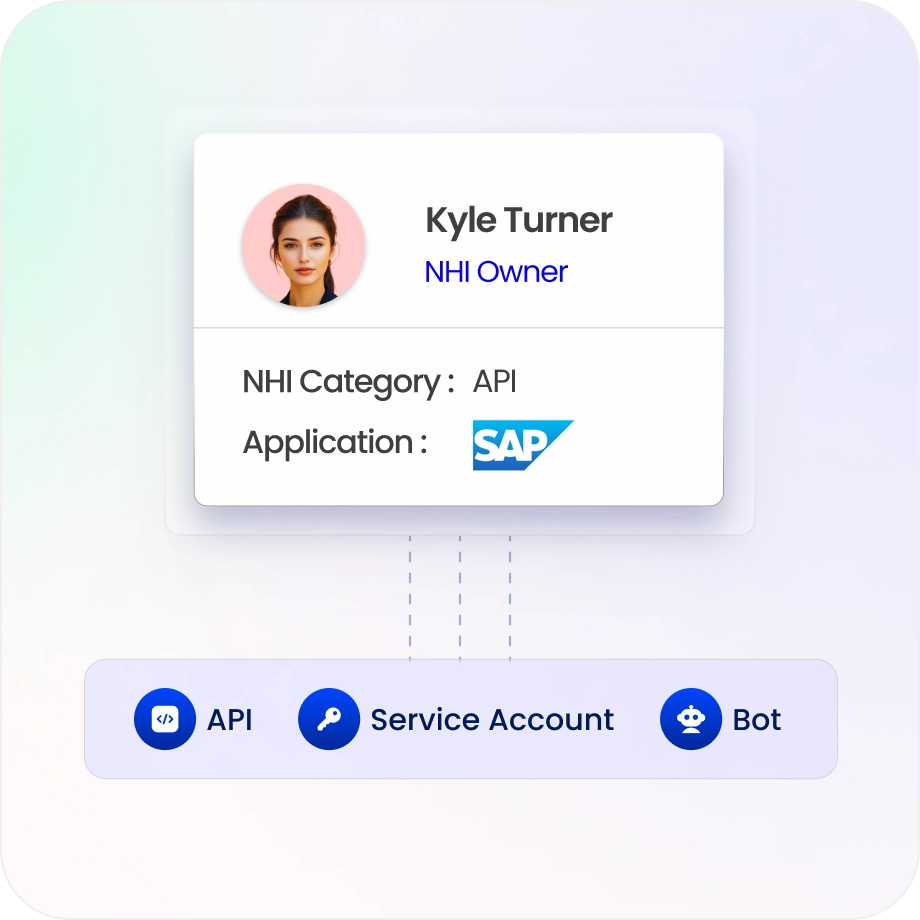
Govern Non-Human Identity Lifecycle
Service accounts, APIs, bots, and cloud IAM roles can become orphaned just as easily as human accounts, and often carry far more privilege.
Ensure accountability and ownership for non-human access cloud and DevOps environments.
Auto-discover non-human identities from AWS, Azure, and GCP. Map every one to an accountable owner.
Rotate credentials, enforce policies, and eliminate unmanaged machine identities before they're exploited.
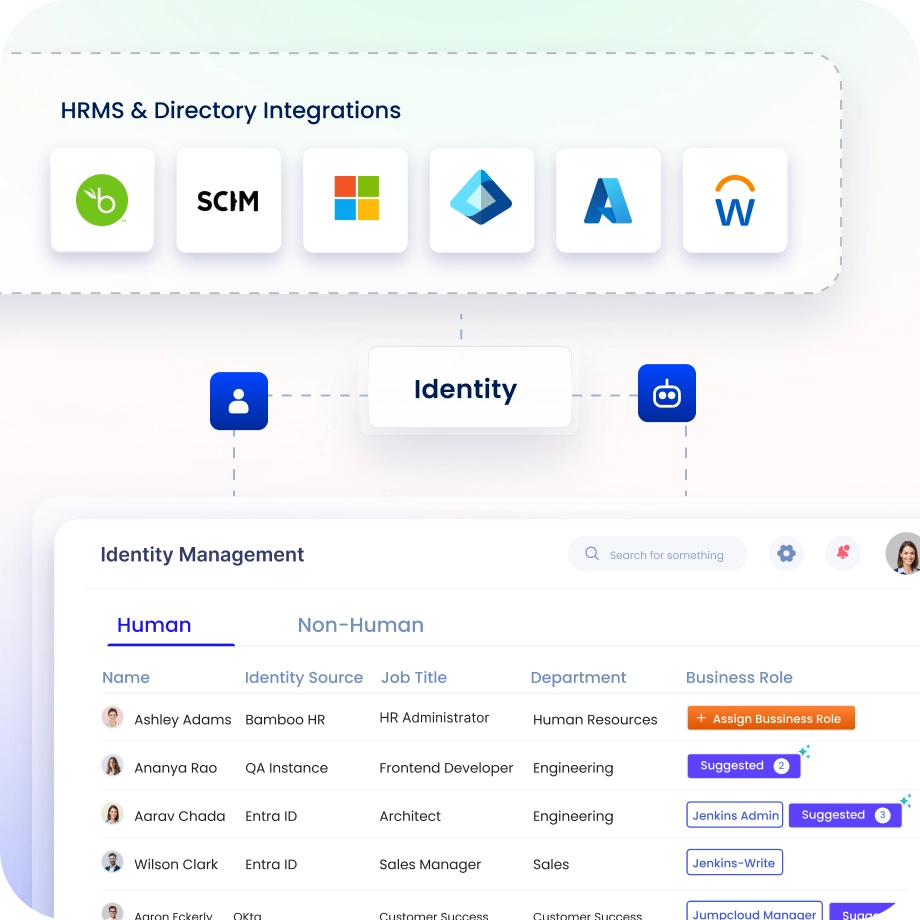
Reconcile Identities Continuously
Continuously reconcile every identities against HR records, directories, and application data in real time.
Accounts with no matching identity, whether duplicate, unlinked, or unknown, are flagged immediately.
Connect across 250+ pre-built integrations so nothing falls through the cracks.
Stay Audit-Ready, Always
Every access decision, lifecycle event, and deprovisioning action generates an automatic audit trail.
Pre-built reports for SOC 2, ISO 27001, SOX, HIPAA, and GDPR are ready in one click, not three weeks.
No scrambling before an audit. Evidence is always up to date.

Drive measurable value with Identity Confluence
Download the ROI Report
91%
Reduction in account sprawls
86%
Faster cleanup cycles
5x
ROI
within 12 months
Why Teams Choose Identity Confluence
1.
Built for Complete Identity Governance
Most tools find orphaned accounts during quarterly reviews. Identity Confluence finds them the moment they form and removes them before the next review even starts.

2.
Human and machine identities, one platform
Workforce accounts, service accounts, APIs, and bots are governed under the same lifecycle rules, with the same ownership accountability and the same audit trail..

3.
Governance that works without a full-time admin
Risk scoring, usage context, and ISPM signals mean reviewers focus on what matters, not rubber-stamping.



