Govern Every App Your Employees Actually Use
Employees do not wait for IT approval, they find a tool that works and sign up. Discover every unsanctioned app, assess its risk, and govern it before an auditor or attacker does.
Trusted by



Shadow IT Is a Governance Gap, Not an IT Problem
Employees use apps IT never approved. Access is granted outside any policy. No audit trail exists. By the time you find out, sensitive data has already left the building.
See It in Action →

Discover, Govern, and Control Every App in Use.
Surface every unsanctioned app accessing your identity environment
Score every shadow app against your governance and risk policies
Extend access controls to cover sanctioned and ungoverned apps alike
Run certifications on shadow apps exactly like governed applications
Generate audit evidence across every app, approved or not.
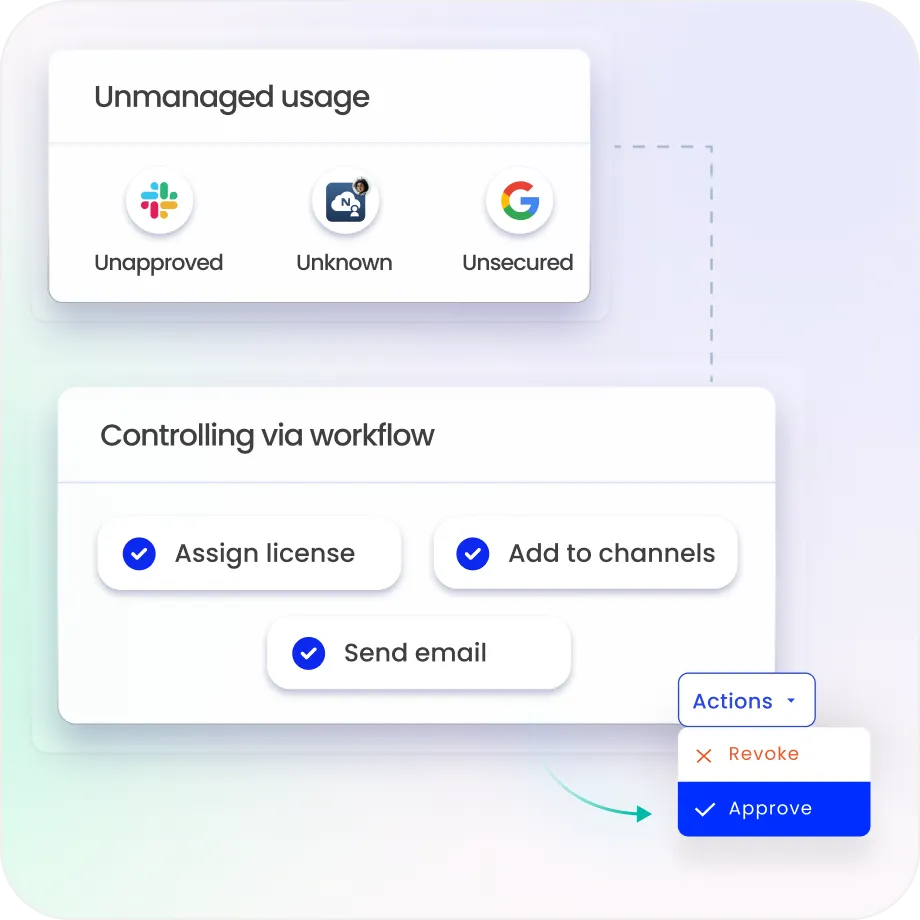
Shadow IT Governed Like Every Other Application
Surface Every Shadow App
Automatically discover unsanctioned apps connecting to your identity environment through OAuth, SSO bypass, or API integration.
Build a complete inventory of every application in use
Every app that interacts with your identities shows up.
Score Risk Before It Becomes Exposure
Every discovered application is scored against configurable governance criteria.
Authentication strength, data access scope, compliance certification status, high-risk apps surface immediately.
Remediation is prioritised by risk level, usage volume, and data sensitivity.
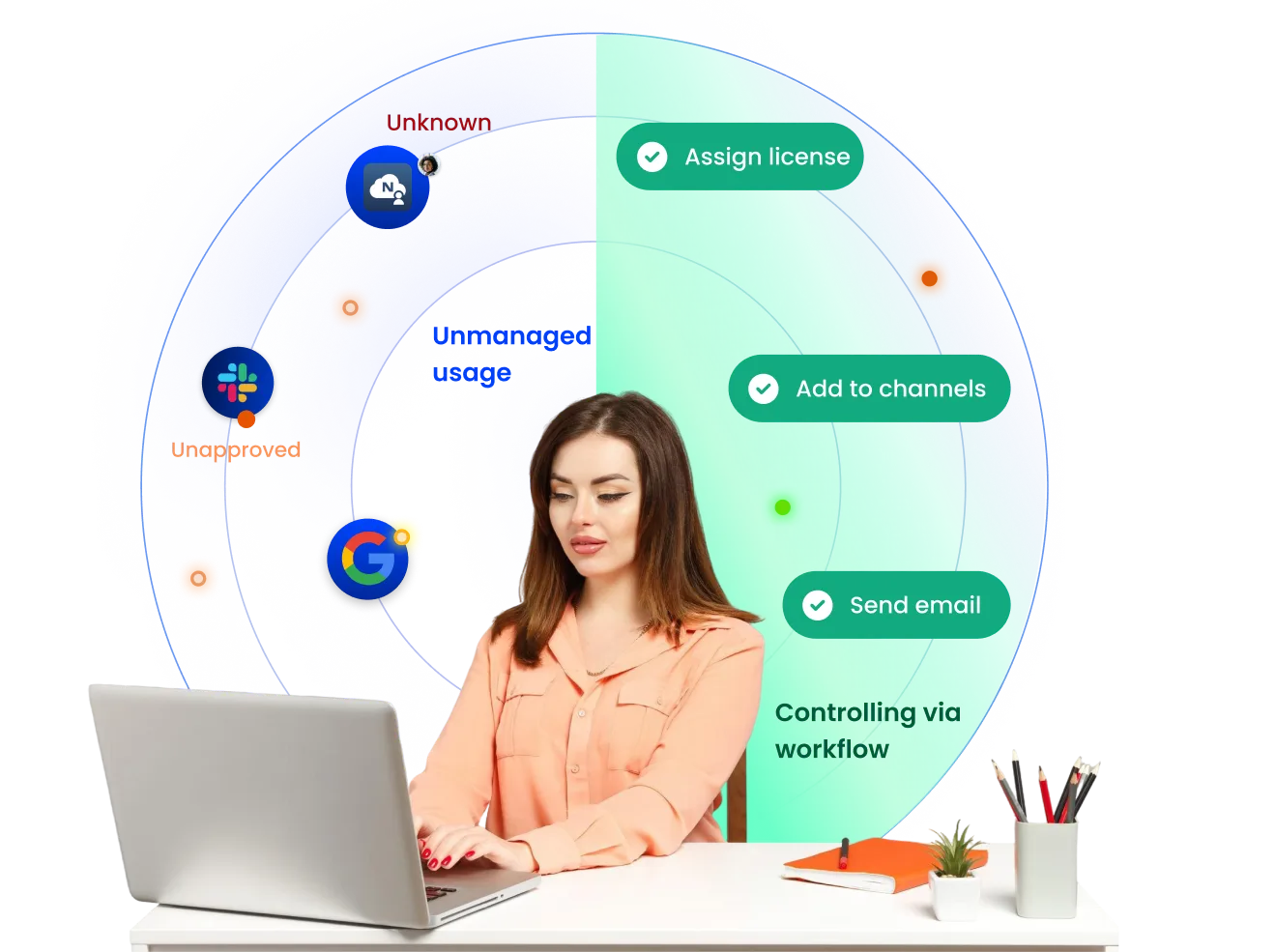
Extend Policy to Ungoverned Apps
Existing role and attribute-based policies extend to cover shadow applications
Enforce access controls, usage limits, and approval requirements on apps that never went through procurement.
Policy violations flag in real time. Audit findings get caught before the auditor does.
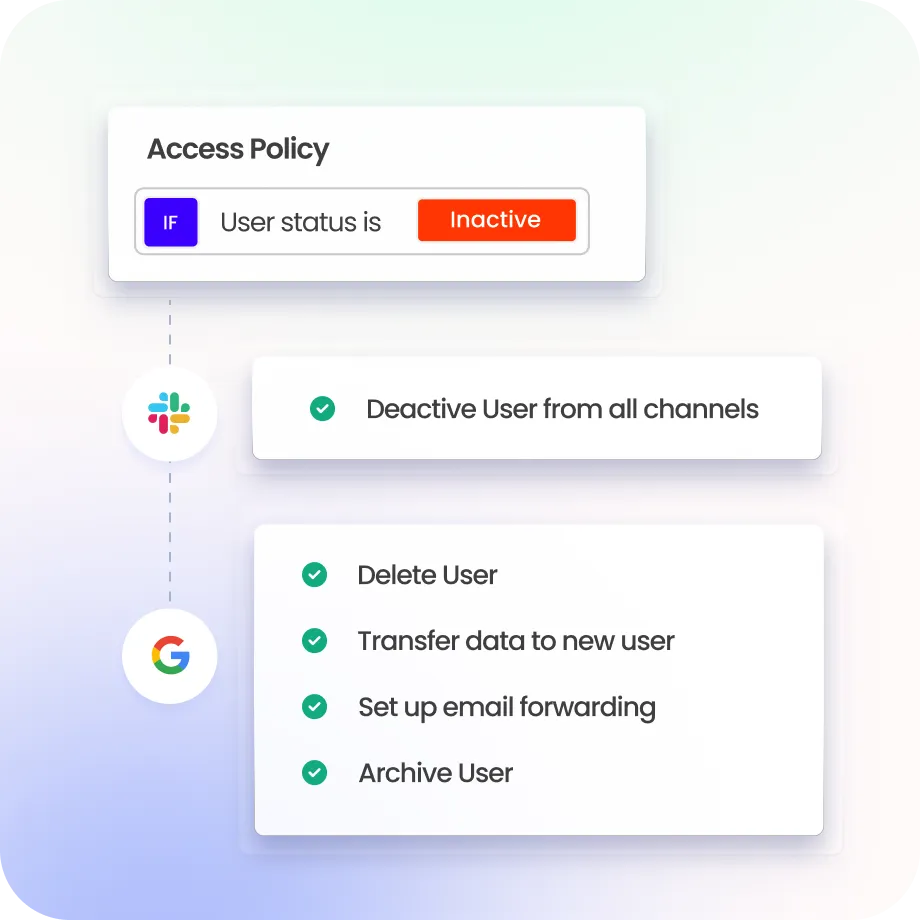
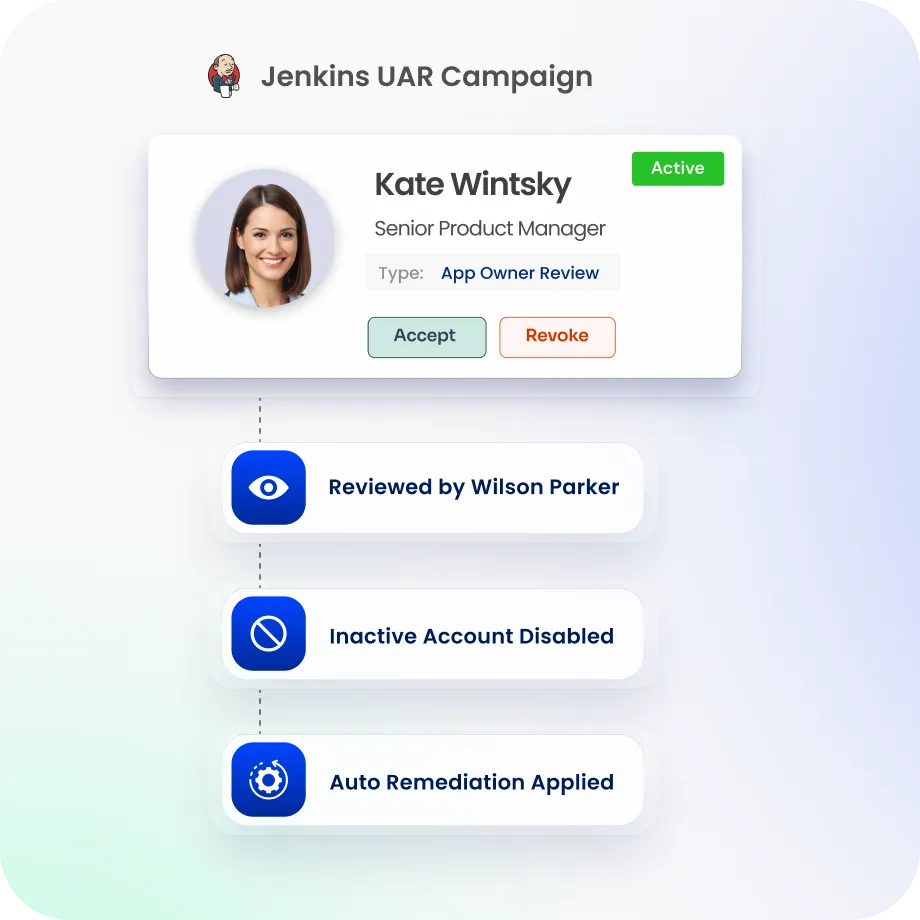
Certify Shadow App Access Too
Certification campaigns run across shadow applications and governed systems, with the same workflow and reviewer experience.
Reviewers see usage context, risk scores, and access history per entitlement before they decide anything.
Every approval or revocation generates a timestamped audit trail.
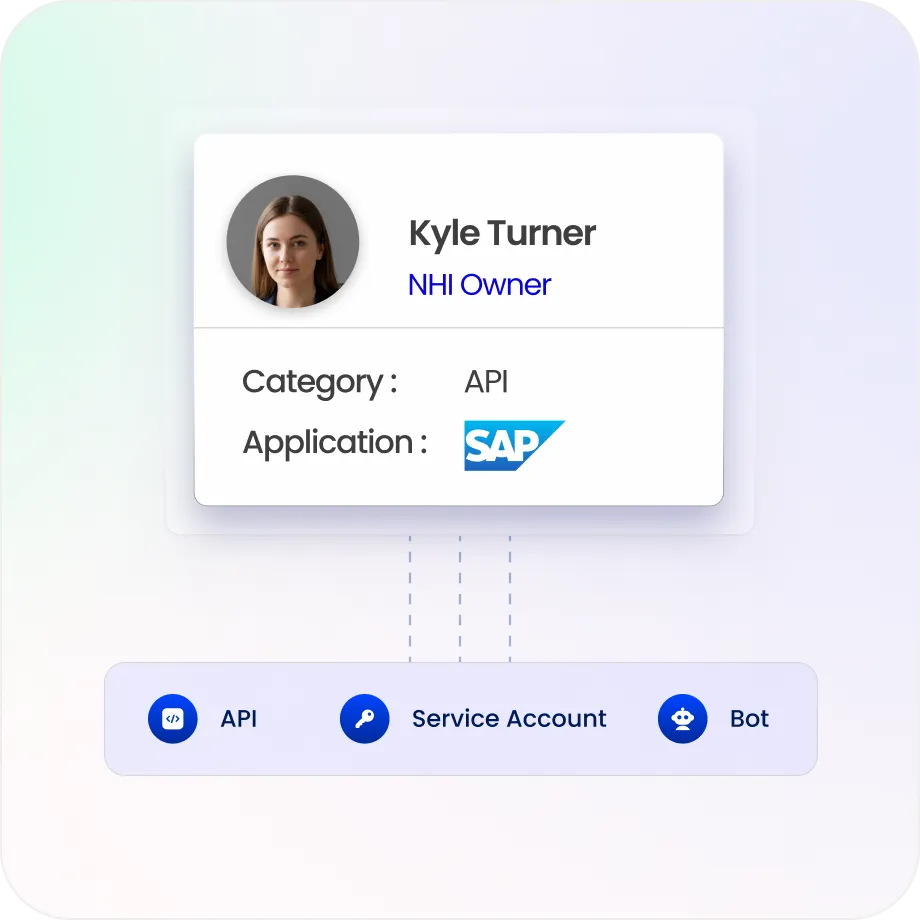
Revoke Access When People Leave
Shadow app access revokes automatically when employees exit or change roles
Orphaned accounts in unmanaged applications surface through continuous reconciliation and get cleaned up.
Legacy and disconnected apps can still be brought into access reviews without a native connector.
Centralise Compliance Evidence
Shadow app access decisions land in the Evidence Center alongside every governed system
Pre-built compliance reports cover SOX, GDPR, HIPAA, ISO 27001, and more, ready before the auditor asks.

Drive measurable value with Identity Confluence
Download the ROI Report
100%
app access governed
3-5x
ROI
within 12 months
99%
shadow IT risk reduction from day one.
Why Teams Choose Identity Confluence
1.
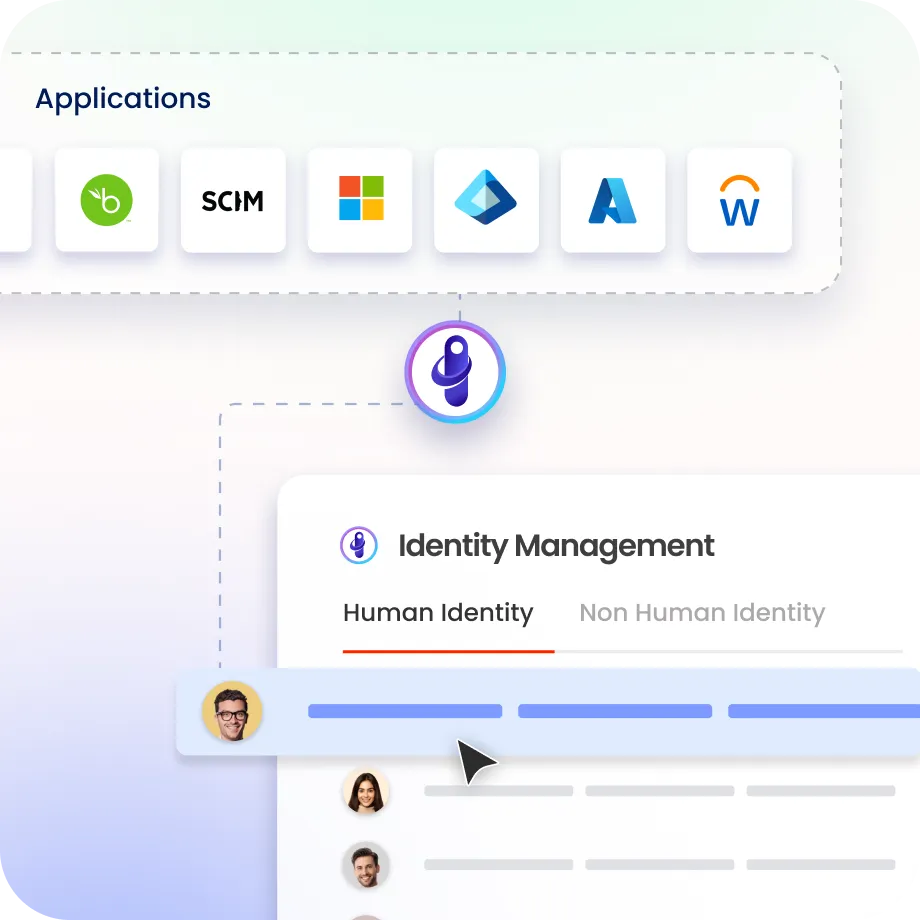
Identity-first discovery
Most tools find shadow IT through network traffic analysis. Identity Confluence finds it through identity signals. The moment a user connects an unsanctioned app, it's visible.

2.
Governed every shadow app
250+ pre-built connectors onboard shadow apps into governed lifecycle management rapidly.

3.
One platform, every application
Shadow apps and sanctioned systems governed under the same policies, the same certification workflows, and the same audit trail.

GET A PERSONALIZED DEMO


