Govern Disconnected Applications Without a Connector
Bring legacy systems, internal tools, and ungoverned apps into your governance framework without a direct integration or API connection.
On this page
See Tech Prescient in Action
Automate access, reduce risk, and stay audit-ready
Last Updated date: April 14, 2026
Your identity governance platform can only control what it can see. Most platforms are built around direct integrations: API connectors, SCIM endpoints, and pre-built adapters that pull account data in real time and push provisioning decisions back out. That model works well for modern SaaS applications.
It breaks down the moment you look at the rest of your portfolio.
Every enterprise runs applications that resist connection entirely. A disconnected application is any system that cannot be integrated with your IGA platform through an API, connector, or SCIM endpoint but still holds user access that requires governance. Legacy applications where the underlying database is locked. Internal tools built by teams that no longer exist. Departmental software purchased without IT involvement that ships with zero API documentation. These applications hold real user access and appear in no access certification workflow, no offboarding automation, and no governance process of any kind.
Auditors do not accept "we don't have an integration for that" as an answer. SOX, HIPAA, and GDPR apply to every application holding sensitive data, regardless of whether your IGA platform can reach it or not.
TL;DR
The integration gap is real: A significant portion of enterprise application portfolios sits outside IGA coverage, holding access that auditors will ask about.
Governance without a live connection: Identity Confluence brings disconnected application governance into its framework using CSV-based user lists and a defined access schema. No API required.
Three capabilities unlock immediately: Access request workflows, user access review automation, and offboarding automation run identically to connected applications the moment a user list is in place.
Honest about its limits: Identity Confluence cannot enforce access changes in disconnected applications. Fulfillment depends on the application owner acting on the raised ticket. The ticket and its full history remain on record as a defensible audit trail.
Accuracy requires maintenance: The governed user list must be refreshed manually. If access changes occur directly inside the application, the governance baseline drifts.
Which Applications Fall Outside IGA Governance?
Applications that fall outside automated IGA governance are typically the ones your platform cannot integrate with through connectors, APIs, or agents, like older ERP systems, on-premise tools, and departmental software built without interoperability in mind. Every IGA deployment draws a coverage line. On one side sit connected applications with live integrations and automated provisioning. On the other side are applications with limited or no integration capability, where governance depends on manual processes and periodic data updates rather than continuous automated control.
Legacy and heavily customized platforms with limited integration support. Industry-specific applications built for function, not interoperability. On-premise tools where identity integration was never a design priority. The access within these systems is real and frequently overlooked. A finance analyst may retain access to a legacy reporting system; a contractor was granted admin rights two years ago and never removed them. A former employee's credentials were never explicitly revoked because no joiner-mover-leaver automation ever reached that system.
Unmanaged access in applications that your platform cannot see is not a theoretical risk. It is your current state.
When your compliance team runs a user access review campaign, these applications are rarely under consistent, automated governance control, creating an audit gap, or managed through manual workflows such as spreadsheets and email approvals that lack standardization and defensible audit trails.
Why Does Traditional IGA Miss Disconnected Applications?
Identity Governance Platforms are fundamentally built around connectors. The architecture assumes that governance follows integration: connect an application, reconcile its accounts, automate provisioning decisions, and enforce lifecycle events. That architecture has limited support for applications that cannot be connected.
The typical response is often exclusion. Remove them from the automated governance scope and manage them manually. Pragmatic, but it creates a structural compliance gap that grows as unreviewed access accumulates inside weakly governed or disconnected systems.
Some organizations attempt manual provisioning workflows using spreadsheets maintained outside the platform. The problem is not effort; it is isolation. That spreadsheet sits outside the centralized audit trail for legacy applications, is often not version-controlled, and is disconnected from your governance platform. When an auditor asks for access certification workflow evidence, a spreadsheet does not carry the same weight as a certified review record inside your IGA platform.
The gap is not a process problem. It is an architectural one.
How Identity Confluence Governs Disconnected Applications
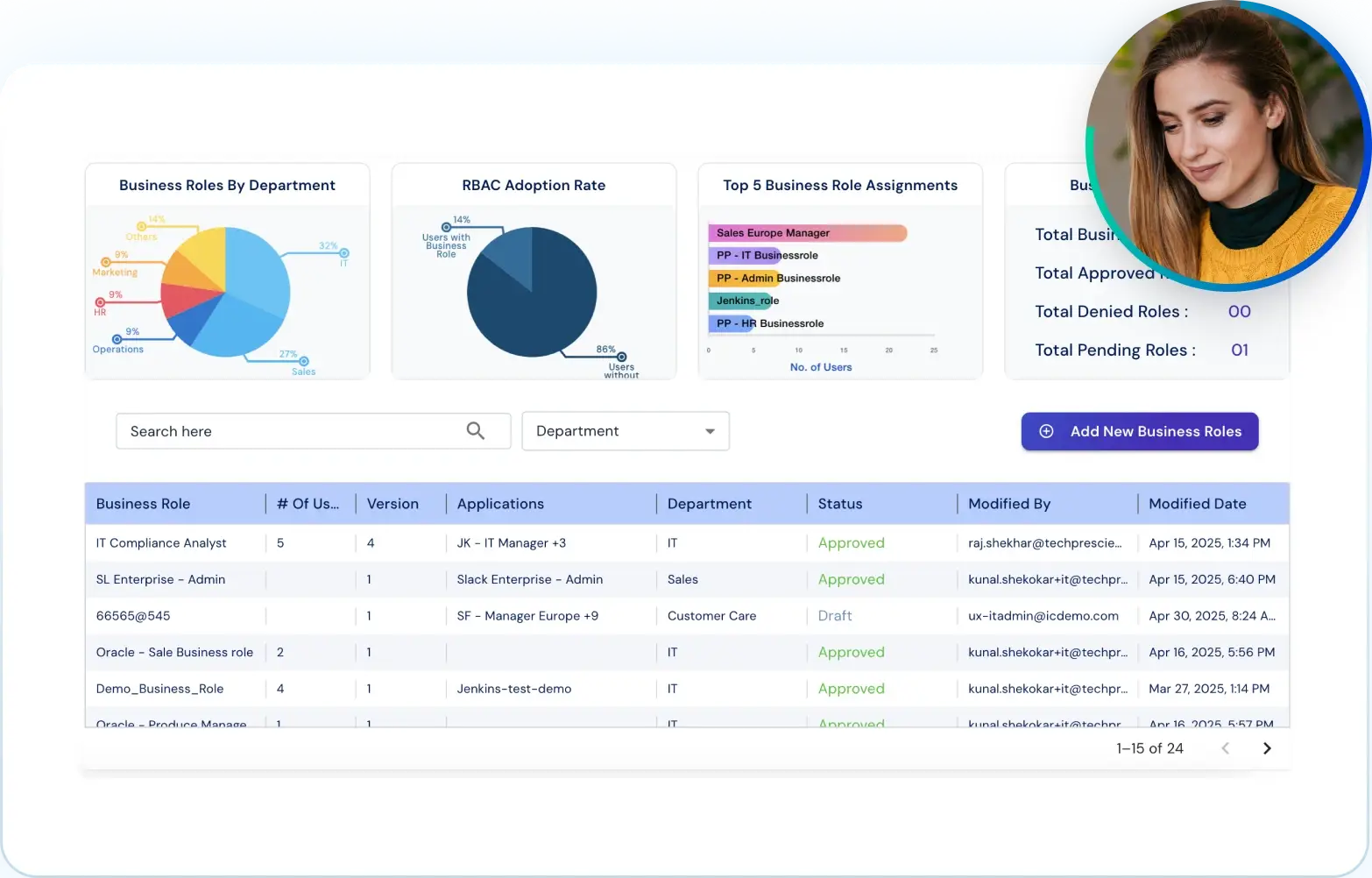
Tech Prescient's Identity Confluence, a next-gen IGA platform, introduces a disconnected application governance model that does not require a live system connection. Any application is registered inside the governance framework, and every workflow available to a connected application becomes available immediately.
The mechanism is transparent. Identity Confluence creates a governed record of the application and a structured user list with a defined access schema and runs its standard governance workflows against that record.
Key Capabilities
Governance-First Onboarding: Any application can be onboarded in Identity Confluence regardless of its integration capability. A governance record is established from the moment of onboarding.
CSV-Based User List Management: Account data is collected from the source system and uploaded as a structured CSV file. This serves as the authoritative record of who holds access. It must be refreshed manually when access changes occur directly within the application.
Access Schema Definition: Permission levels are defined and then captured during onboarding, enabling a downstream access certification workflow with the vocabulary it needs to produce meaningful reviewer decisions, rather than mechanical approvals.
User Access Review Automation on Parity: Once a user list is established, disconnected applications are included in user access review campaigns on the same cadence as connected applications.
Automated Ticket Creation: Every access change, whether a new request or an access revocation workflow, generates an automated ticket inside Identity Confluence. Timestamped, assigned to the application owner, and tracked through to closure.
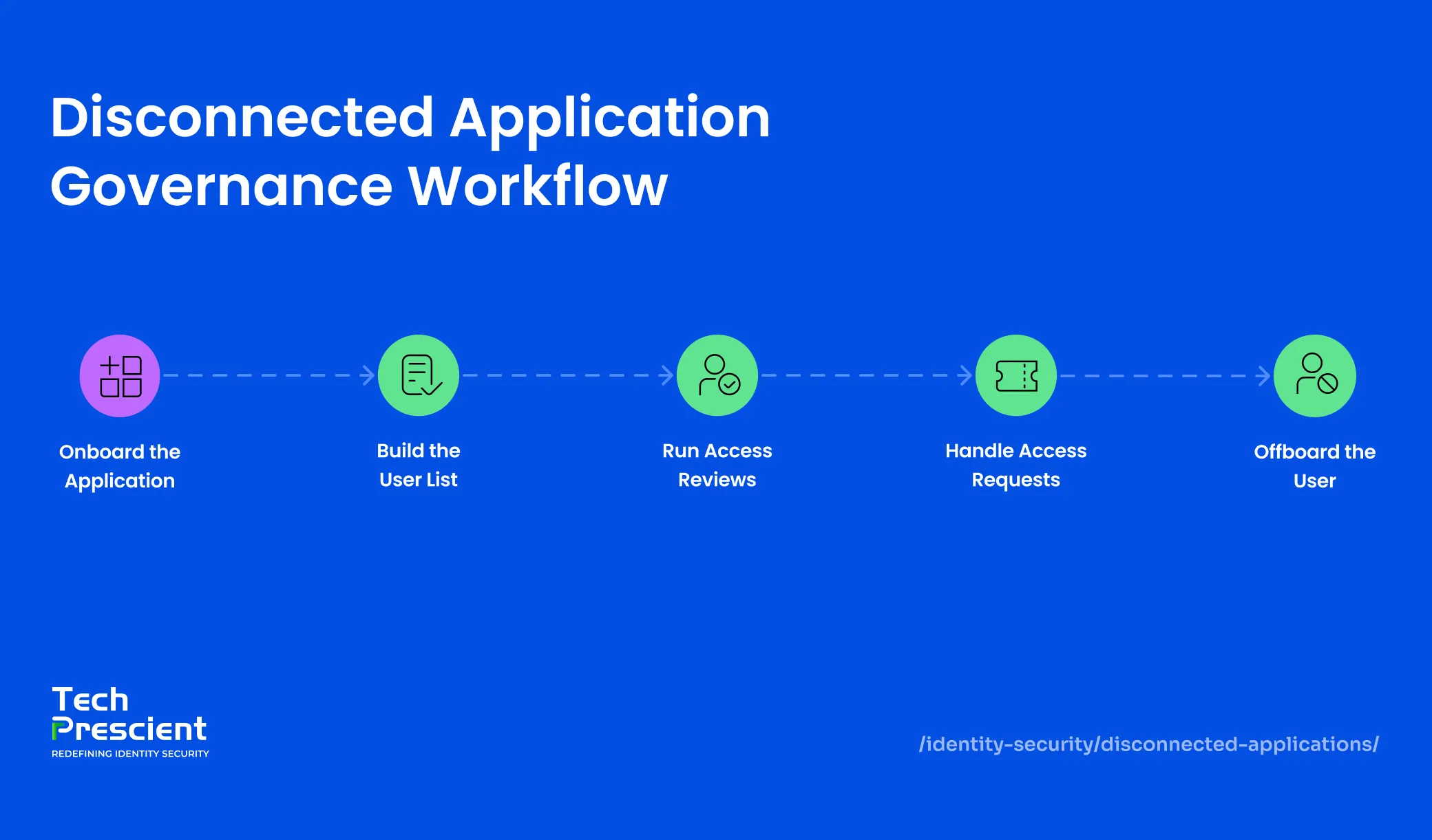
Step 1 - Onboard the Application
Onboard the application in Identity Confluence and assign an application owner: the person or team responsible for fulfilling access changes manually. Define the access schema by documenting the permission levels the application supports.
| Access Level | Description |
|---|---|
| Read Only | View data, no modification capability |
| Standard User | Full feature access within limited assigned scope |
| Administrator | Full access, including user management |
The schema definition is a one-time setup step. It gives every downstream workflow, from access certification to revocation decisions, the permission vocabulary every downstream workflow needs to make accurate, reviewer-driven decisions rather than blanket approvals. If the application's permission structure changes after onboarding, the schema must be updated before the next UAR cycle runs. An outdated schema means reviewers are certifying access levels that no longer reflect the application's actual model.
Step 2 - Build the User List
Collect the current account list from the application by exporting from the admin console, extracting it from available reports, or using any available method, and upload it to Identity Confluence as a CSV file, mapped to the defined schema.
The result is a governed user list: every identity with access to the application, their assigned permission level, and the date the record was established.
Application Insight:
If your application admin console does not support a clean export, start with whatever data exists, even a partial list. An incomplete, governed record is more defensible than no record. Flag the gaps explicitly in Identity Confluence so reviewers know which accounts could not be verified at the time of upload.
Step 3 - Run User Access Review Automation
With a user list in place, the application enters the user access review automation cycle in the same way as connected applications. Reviewers receive certification tasks, see the user list mapped to access schema levels, and make decisions through the same interface they use for every other application. Certify confirms continued access. Revoke triggers the access revocation workflow and generates an automated ticket assigned to the application owner for manual removal.
The review record is fully exportable. Every certify-and-revoke decision is timestamped, reviewer-attributed, and retrievable on demand.
Step 4 - Access Request Workflow
When someone needs access to a disconnected application, the request flows through Identity Confluence's standard access request workflow. The ticket is created automatically, routed for approval based on defined rules, and, once approved, assigned to the application owner for manual fulfillment.
Every request is visible. Every approval is documented. Every change is on record. The access request workflow operates identically regardless of whether the system behind it can execute changes automatically.
Step 5 - Offboarding and Access Revocation
When a user leaves, and the offboarding event is triggered, Identity Confluence automatically raises a revocation ticket for every disconnected application that the user holds access to. No manual checklist. No dependency on institutional memory.
This is where the model's constraint matters most. Identity Confluence cannot enforce access removal in a disconnected application. Actual removal depends on the application owner acting on the ticket. What Identity Confluence guarantees is that the access revocation workflow is triggered automatically, the ticket is assigned, its status is visible, and the full record is maintained throughout the offboarding automation process.
For auditors reviewing an offboarding event, the question is not only whether access was removed. It is whether the removal was initiated, tracked, and documented.
Note:
An open revocation ticket with no closure date is an audit liability, not an audit record. Build a simple process alongside Identity Confluence: define what closure looks like, require the application owner to confirm removal in writing when marking the ticket complete, and review all open revocation tickets before any scheduled audit. The platform creates the record. The process makes it defensible.
What Changes After You Onboard Disconnected Applications
Before: Access certification workflows skip legacy applications entirely. Offboarding automation never reaches them. Auditors receive a spreadsheet that nobody fully trusts.
After: Every disconnected application has a governed user list, a defined access schema, and a documented owner. User access review automation runs on the same cadence as connected systems. Offboarding automation raises revocation tickets the moment a user exits.
Maintaining Governance Accuracy Over Time
Onboarding a disconnected application is the foundation, not the finish line.
The governed user list must stay current. If the application owner grants or removes access directly inside the system without updating the Identity Confluence record, the disconnected application governance baseline drifts. Your next user access review automation cycle will certify access that no longer reflects reality. A refresh cadence, monthly or triggered by any access change event, is the discipline that keeps the governance record accurate.
The access schema requires the same attention. Any change to the application's permission structure must be reflected in Identity Confluence before the next access certification workflow runs. Reviewing against an outdated schema produces certifications that do not accurately map to the application's actual access model.
Ready to Close the Gap?
Every access request workflow, approval, and access revocation workflow is documented. Every decision is retrievable. What was initiated is on record. What remains open is visible.
This is not about simulating integration where none exists. It is about extending governance discipline to every application that holds access, regardless of whether your platform can reach it directly. The applications without connectors carry the same compliance obligations as the ones with them.
Identity Confluence was built to govern the full application portfolio, not just the portion that supports modern APIs.