What Is Identity Governance Framework: Guide For 2026
Learn what an identity governance framework is, its key components, benefits, and how to implement an IGA framework for compliance and security in 2026.
On this page
See Tech Prescient in Action
Automate access, reduce risk, and stay audit-ready
Last Updated date: April 10, 2026
An Identity Governance Framework is a structured model that defines how organizations manage enterprise identities and access governance policies across systems and applications.
It combines policies, processes, and technologies, such as role-based access control (RBAC), access certifications, segregation of duties (SoD), and identity lifecycle management, to ensure the right users have the right level of access at the right time.
In 2026, as enterprises adopt cloud-first architectures, hybrid work models, and third-party SaaS platforms, identity has become the primary security perimeter. According to Verizon’s Data Breach Investigations Report, over 60% of breaches involve compromised or misused credentials, making identity governance a business-critical priority, not just an IT function.
This guide explains what an Identity Governance Framework is, how it differs from IAM, its key components, business benefits, and how to implement an effective IGA framework that scales with modern enterprise needs.

Key Takeaways:
- Identity governance controls access risk in cloud-first, distributed environments.
- IAM enables access; identity governance validates and governs it over time.
- Effective IGA relies on policy-driven automation and continuous oversight.
- Mature IGA reduces audit friction while improving compliance and efficiency.
- Enterprise IGA platforms differentiate through risk awareness, audit readiness, and scale.
What Is an Identity Governance Framework?
An Identity Governance Framework is a policy-driven blueprint that defines how organizations manage identities, govern access rights, and maintain compliance across applications, systems, and environments.
Identity Governance and Administration (IGA) is a structured set of standards that helps enterprises manage user identities, enforce access policies, and maintain compliance. But when we are referring to an Identity Governance Framework, we are talking about a strategic blueprint that guides how those governance policies are implemented across an organization.
So, what is an Identity Governance Framework in simple terms?
Consider a financial institution that stores sensitive customer and transaction data across internal systems and third-party SaaS platforms. Finance teams require access to this data to perform their roles, while departments such as marketing or human resources should not have visibility into it. An Identity Governance Framework enables the organization to define and enforce RBAC policies that grant access strictly based on role and business need. This reduces the risk of unauthorized access, limits insider exposure, and supports compliance with regulatory obligations.
With an appropriate Identity Governance Framework in place, XYZ Bank can implement role-based access control (RBAC) policies that allow only finance team members to access these systems nothing more, nothing less. This approach eliminates unauthorized access, reduces the risk of insider threats, and ensures compliance with regulatory standards like GDPR and SOX.
Now, you might ask: “Isn’t this what Identity and Access Management (IAM) does?” It's a valid question. While IAM handles the ‘who logs in’ part, IGA goes deeper governing why they have access, what level of access they have, and whether that access is still valid.
The 5 Pillars of an Identity Governance Framework
An effective Identity Governance Framework is built on five foundational pillars that collectively govern the full identity lifecycle, from onboarding through access changes to offboarding.
Identity Lifecycle Management
Defines how digital identities are created, updated, and removed as users join, move within, or leave the organization. This ensures access aligns with current roles and employment status at all times.
Access Governance
Establishes and enforces who should have access to which resources, based on role-based access control (RBAC), segregation of duties (SoD), and business context.
Continuous Access Reviews
Requires periodic validation of user access through certifications and audits to confirm that entitlements remain appropriate, necessary, and compliant.
Risk and Compliance Intelligence
Identifies and prioritizes risky access patterns while supporting regulatory and internal compliance requirements through reporting, monitoring, and evidence generation.
Automation and Orchestration
Ensures governance policies are applied consistently and at scale by automating access decisions, enforcement actions, and workflows across systems and environments.
Pro Tip
Most organizations fail at identity governance not because of missing tools, but because these pillars operate in silos instead of as a single lifecycle.
Why Identity Governance Matters in Modern Enterprises (2026)
In 2026, identity governance is essential due to cloud sprawl, insider risk, and regulatory pressure, helping organizations prevent excessive access and maintain continuous compliance.This leads to a dangerous phenomenon known as cloud sprawl, where identities and permissions multiply across disconnected systems creating the perfect opportunity for attackers.
As organizations continue to expand their use of cloud services, hybrid work models, and third-party integrations, access environments have become increasingly fragmented. Identities, roles, and permissions proliferate across disconnected systems, making it difficult to maintain consistent oversight. Without governance, this sprawl creates persistent exposure through excessive, outdated, or poorly justified access.
Identity Risk Alert:
Dormant accounts, over-provisioned SaaS access, and unmanaged third-party identities are among the top causes of identity-related breaches today.
Identity governance isn’t just about security it’s about resilience and accountability. With increasing pressure from regulations like GDPR, HIPAA, and SOX, organizations must prove they have tight control over user provisioning and deprovisioning, access certification, and segregation of duties (SoD).
A well-implemented identity governance and administration (IGA) framework enables organizations to:
- Prevent excessive or outdated access
- Enforce role-based access control (RBAC)
- Meet evolving compliance and audit demands
- Reduce the risk of data breaches by addressing identity-related vulnerabilities
In 2026, identity governance solutions are no longer optional they're essential for sustaining trust, ensuring agility, and maintaining competitive edge.
Not sure where to start? Get the 90-day plan
A step-by-step roadmap to gain visibility, control access, and reduce identity risk.
Identity Governance vs. Identity & Access Management (IAM)
Identity and access management (IAM) controls how users authenticate and gain access to systems. Identity governance ensures that access is appropriate, justified, and continuously reviewed throughout the identity lifecycle.
Although the terms are often used interchangeably, identity governance and IAM serve distinct, and complementary, functions within an enterprise security architecture.
| Aspect | Identity Governance (IGA) | Identity and Access Management (IAM) |
|---|---|---|
| Core Focus | Governance, policy enforcement, lifecycle management | Authentication and authorization |
| Scope | Monitors who should have access and why | Manages who can access systems |
| Functions | Access reviews, role assignments, access recertification, compliance tracking | Login management, password policies, session handling |
| Lifecycle Coverage | End-to-end user lifecycle: provisioning, modification, deprovisioning | Mainly login and real-time access control |
| Use Case | Ensuring least-privilege access across systems | Verifying user credentials and granting access |
| Governance Layer | Strategic—aligns with compliance and audit standards | Operational focused on system access enforcement |
A practical way to distinguish the two is by intent. IAM determines whether a user can access a system at a given moment. Identity governance determines whether that access should exist at all, and whether it remains appropriate as roles, responsibilities, or employment status change.
When implemented together, IAM and identity governance form a complete access control model. IAM enforces access decisions, while identity governance defines, validates, and governs those decisions over time across the enterprise.
6 Key Components of an Identity Governance Framework
An Identity Governance Framework typically includes lifecycle management, RBAC, segregation of duties, access reviews, audit reporting, and risk analytics. These components ensure users receive the right access while maintaining compliance and minimizing security risks.
An effective Identity Governance Framework consists of several foundational components that help organizations manage digital identities, enforce access policies, and maintain regulatory compliance. These elements ensure that every identity is governed consistently across its entire lifecycle, minimizing risk and supporting business operations securely.
Identity Lifecycle Management
Identity lifecycle management forms the foundation of any IGA framework. It covers every stage of a user’s journey within an organization, including onboarding, role transitions, and offboarding. The goal is to ensure that access is provisioned promptly, adjusted as roles evolve, and revoked when it is no longer needed.
Automating user provisioning and de-provisioning helps eliminate the risk of unauthorized access and reduces administrative overhead. This not only strengthens security but also ensures that access rights always align with business needs.
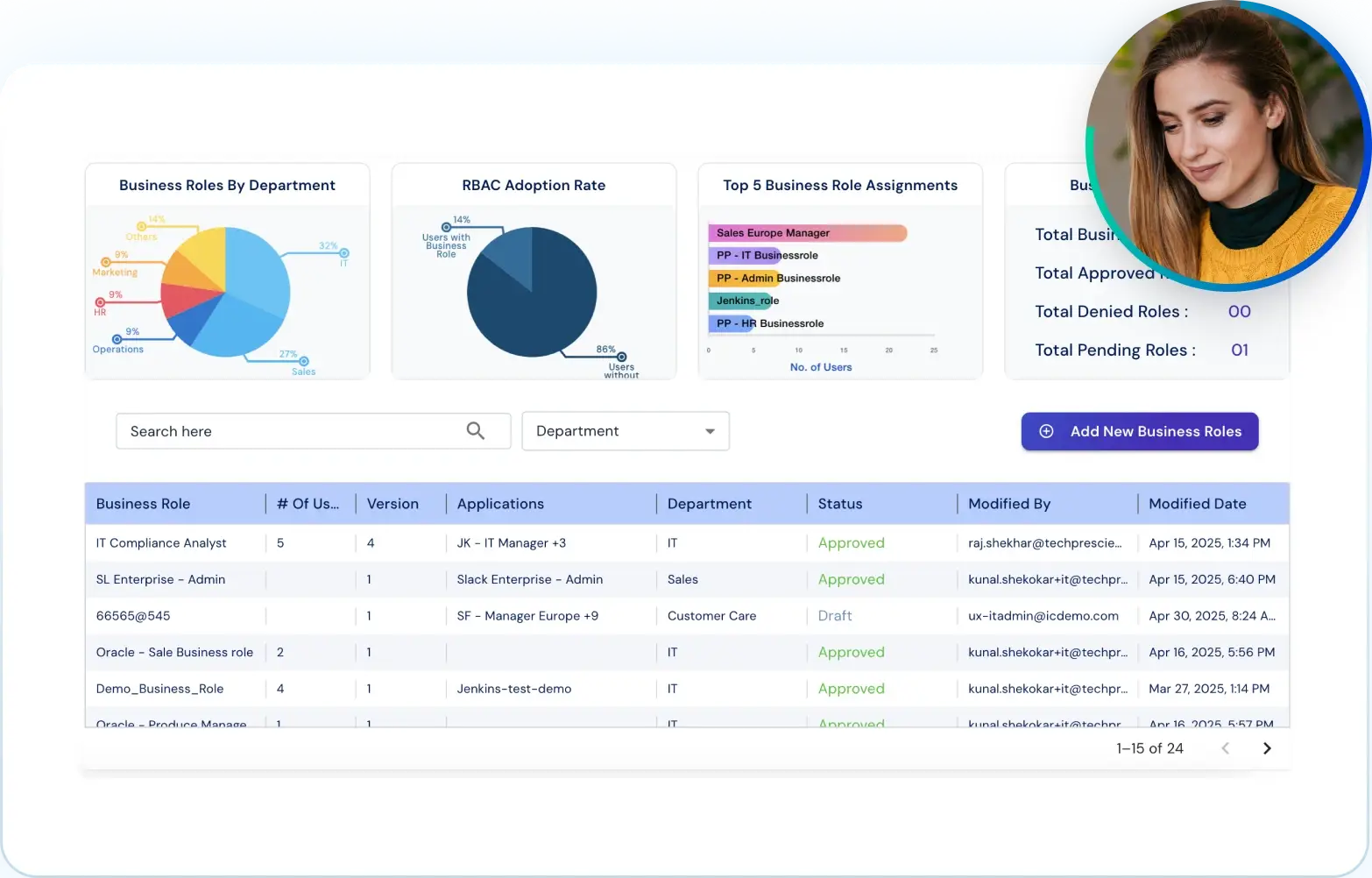
Role-Based Access Control (RBAC)
Role-based access control, or RBAC, allows organizations to grant access permissions based on job roles rather than individual requests. This streamlines the process of assigning and managing access and helps enforce the principle of least privilege across departments.
By using RBAC as part of an identity governance solution, businesses can prevent privilege creep, reduce manual errors, and improve scalability across teams and systems.
Segregation of Duties (SoD)
Segregation of duties is essential for mitigating internal threats and ensuring proper checks and balances. It ensures that no individual has enough control to execute conflicting functions, such as both initiating and approving a financial transaction.
Incorporating SoD policies into your Identity Governance Framework strengthens compliance posture, reduces fraud risk, and enhances transparency within business operations.
Access Review and Certification
Access reviews and certifications help verify that users have the correct level of access based on their roles. This process involves reviewing and validating access rights on a regular basis to eliminate excessive or outdated permissions.
Automated access reviews are a core capability of identity governance tools. They help identify risks early, enforce access policies, and ensure that access entitlements remain aligned with business and compliance requirements.
Audit and Compliance
Audit and compliance capabilities are crucial in highly regulated industries. Your identity governance solution should provide a clear record of who accessed what, when, and why, along with policy enforcement and violation alerts.
Complete audit trails and real-time reporting make it easier to demonstrate compliance with frameworks like GDPR, HIPAA, and SOX. They also improve incident response and build trust with stakeholders.
Risk Analytics
Risk analytics adds a predictive layer to identity governance. It allows organizations to monitor user behavior, identify anomalies, and respond to threats proactively.
By integrating risk scoring and behavior analysis, organizations can focus on high-risk access patterns and take timely corrective action. This enhances security across the identity lifecycle and supports a more adaptive access governance strategy.

3 Business Benefits of Implementing an IGA Framework
An Identity Governance Framework improves security, simplifies compliance, and increases operational efficiency through automation and policy-driven access control.
Implementing an Identity Governance Framework offers more than just security. It strengthens compliance, boosts operational efficiency, and ensures access is always aligned with business needs. Let’s break down the top three benefits.
Improved Security
An IGA framework continuously monitors and adjusts access based on user roles and their behavior. Through automated access reviews, RBAC, and identity lifecycle management, it is ensured that users only have access to what they need. This reduces the risk of unauthorized access, insider threats, and credential misuse, making your organization far less vulnerable to breaches.
Regulatory Compliance
Identity governance solutions help enforce policies such as least privilege and segregation of duties, aligning with regulations like GDPR, HIPAA, and SOX. They also maintain audit-ready logs and reports, making compliance easier and reducing the risk of fines during regulatory audits.
Operational Efficiency
Automation is a key outcome of identity governance. By standardizing and automating provisioning, access changes, and deprovisioning, organizations reduce manual intervention and operational overhead.
This leads to faster onboarding and role changes, fewer access-related errors, and consistent policy enforcement at scale, without increasing administrative burden on IT teams.
Not sure where to start? Get the 90-day plan
A step-by-step roadmap to gain visibility, control access, and reduce identity risk.
How to Implement an Identity Governance Framework
Implementation of an Identity Governance Framework requires a blend of policy, technology, and collaboration. Let us have a look at five essential steps to get started.
Understand Business Requirements
Start by aligning your identity governance goals with overall business objectives. Identify key systems, critical data, user roles, and compliance mandates specific to your industry.
This step ensures your IGA framework is tailored as per your organization’s risk profile, operational needs, and regulatory responsibilities, whether you're in finance, healthcare, or a SaaS-driven enterprise.
Define Access Policies
Establish access policies based on role-based access control (RBAC) and the principle of least privilege. Clearly define who should have access to what, under what conditions, and for how long. Include rules around user provisioning and deprovisioning, segregation of duties (SoD), and access certification to prevent excessive or conflicting privileges.
Choose IGA Tools
Select the right identity governance tools that offer centralized visibility, policy enforcement, automated access reviews, and reporting capabilities. Modern tools should integrate easily with your existing identity and access management (IAM) infrastructure, support compliance tracking, and offer built-in workflows for access governance.
Pro Tip
Don’t evaluate IGA tools only on features. Prioritize visibility, audit readiness, and how easily the tool integrates with HR and IAM systems.
Automate with Workflows
Automation is essential for enforcing policies consistently at scale. Implement workflows to handle routine access events such as role changes, approvals, certifications, and access revocation.
Automated workflows reduce manual effort, improve response times, and limit the risk of errors that can introduce access gaps.
Review and Optimize Regularly
Identity governance isn’t a one-time effort. Conduct regular audits, access reviews, and policy evaluations to ensure continued alignment with business changes and evolving compliance standards. Track metrics, assess risk scores through risk analytics, and update your framework as needed to maintain a strong security posture.
Not sure where to start? Get the 90-day plan
A step-by-step roadmap to gain visibility, control access, and reduce identity risk.
H2: Best Practices for Identity Governance
Best practices for identity governance include executive sponsorship, Zero Trust adoption, access recertification, just-in-time access, and automation.
To establish a robust and scalable Identity Governance Framework, organizations must go beyond basic implementation. A combination of leadership support, smart access models, and automation helps ensure long-term success in managing digital identities and access.
Executive Sponsorship
Every effective Identity Governance solution needs support from executive leadership. Gaining buy-in ensures the initiative receives proper funding, visibility, and collaboration across departments. Leadership backing also reinforces the importance of identity governance as a core component of enterprise security and compliance.
Zero Trust
Adopting a Zero Trust approach strengthens identity and access governance by removing any assumption of trust. Every user, device, and system is continuously validated before access is granted. When aligned with your IGA framework, Zero Trust ensures strict access controls and better protection against insider threats and credential misuse.
Access Recertification
Access recertification involves periodic review of user entitlements to ensure they still align with job roles. This step helps prevent privilege creep and supports policies like segregation of duties (SoD). With automated access reviews, teams can quickly identify and revoke outdated or unnecessary permissions to stay audit-ready and secure.
Just-in-Time Access
Just-in-time access provides temporary access to resources only when needed. It eliminates standing privileges and limits access exposure to a predefined duration. This model supports least privilege access, reduces risk, and helps manage sensitive data more securely within the Identity Governance Framework.
Automation
Automation improves accuracy and efficiency across identity governance processes. It simplifies tasks like user provisioning, access requests, deprovisioning, and policy enforcement. By leveraging identity governance tools with built-in workflows and analytics, teams can streamline operations and reduce the burden of manual oversight.
Why Our IGA Solution Stands Out Among Leading Tools
Leading identity governance solutions differentiate themselves through automation, risk-aware controls, seamless integrations, and audit-first design.
In an ever-expanding market of cybersecurity solutions and identity governance tools, what sets a solution apart is not just featured checklists but how well it aligns with real-world needs, adapts to business change, and scales with confidence. That’s where our IGA framework at Tech Prescient excels.
The platform is built to address the challenges modern enterprises face, including distributed cloud environments, complex compliance obligations, and dynamic role structures. Its architecture prioritizes governance integrity, operational consistency, and scalability.
Here’s why our identity governance solution goes beyond the ordinary:
Unified Identity Lifecycle Management
Centralized lifecycle governance automates provisioning and deprovisioning across systems while maintaining policy alignment as users join, move, or leave the organization.
Risk-Aware Governance
Embedded risk analytics identify high-risk access patterns and entitlement anomalies, enabling organizations to prioritize remediation based on exposure rather than volume alone.
Zero Trust–Aligned Architecture
The platform supports least-privilege and just-in-time access models, enabling continuous access evaluation without relying on standing privileges.
Seamless Integrations
Native integration with IAM, HR, IT service management, and compliance systems enables consistent governance enforcement without disrupting existing operational workflows.
Audit-First Design
Access certifications, reporting, and audit trails are built into core workflows, providing traceable evidence to support regulatory and internal audit requirements.
Built for Scale
The platform is designed to operate consistently across environments ranging from hundreds to tens of thousands of identities, without compromising governance control or visibility.
Why Choose Tech Prescient IGA
Organizations evaluating identity governance platforms require more than feature comparisons. They require consistent policy enforcement, risk-aware access controls, and the ability to operate at enterprise scale.
Tech Prescient’s identity governance and administration (IGA) platform is designed for organizations that require structured access governance, audit-ready controls, and scalable automation across complex environments.
FAQs
The purpose of an identity governance framework is to ensure users have appropriate access to systems based on policies, roles, and compliance requirements, reducing security risk and supporting audits.
Industries such as finance, healthcare, government, manufacturing, and large enterprises benefit most due to strict compliance needs and sensitive data access.
Yes. Modern identity governance tools automate access reviews, provisioning, policy enforcement, and compliance reporting to reduce errors and improve efficiency.